Embed presentation
Download as PDF, PPTX


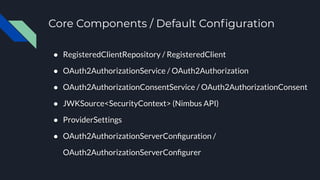
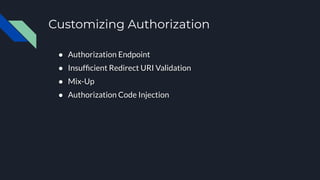
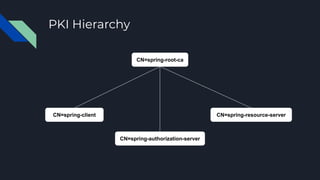
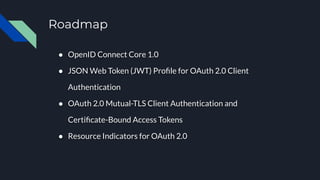

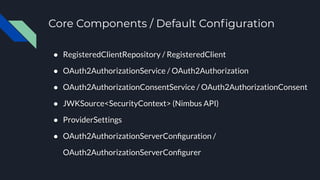
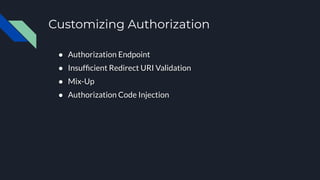
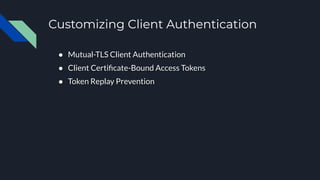
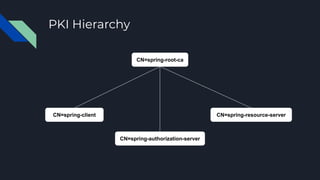
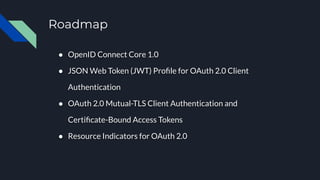
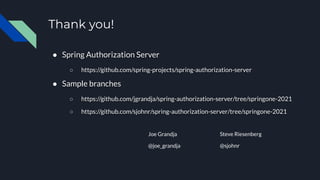
This document outlines the essentials of getting started with the Spring Authorization Server, detailing various security standards like OAuth 2.1 and OpenID Connect. It describes core components, default configurations, and methods for customizing both authorization and client authentication. Additionally, it includes links to sample branches and a roadmap for future developments.