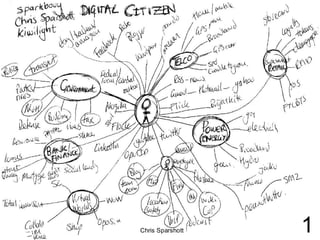
Future of Digital Profiles
- 1. Chris Sparshott 1
- 2. Profile 2.0 1. Basic Profile 5. Data 2. Activity Profile 2.0 4. Relationships 3. Participation Chris Sparshott 2
- 3. 1. Basic Profile Work Profile 5. Data 2. Activity Profile 2.0 4. Relationships 3. Participation Internet Profile 1. Basic Profile Profile 1. Basic Profile 5. Data Profile 2. Activity 2.0 5. Data Profile 2. Activity 2.0 2.0 4. Relationships 3. Participation 4. Relationships 3. Participation Private Profile Chris Sparshott 3
- 5. Who owns my profile? Chris Sparshott 5
- 6. Enterprise Outside Wall Knowledge Saas Knowledge blog spreadsheets spreadsheets experience wiki experience teamrooms skills teamrooms skills Social Web pub/sub wiki me documents network me documents applications crm share info IM applications crm share info IM 2.0 messaging email intranet web messgaing email intranet web Profile content notice-board projects tagging CV telephone VoIP UC content notice-board projects tagging CV telephone VoIP UC videos blogs webinar podcast videos blogs webinar podcast images SL animation learning images animation SL blog communities expert community learning communities expert share immersion mobiles API community share immersion mobiles API Chris Sparshott 6
- 7. Chris Sparshott 7
- 8. Chris Sparshott 8
- 9. Enterprise Outside Wall Knowledge Internet Saas Knowledge blog spreadsheets spreadsheets experience wiki experience teamrooms skills teamrooms Profile Social skills Work pub/sub wiki me documents network me documents applications crm share info IM applications crm share info IM Profile messaging email intranet web messgaing email intranet web content notice-board projects content notice-board projects tagging CV telephone VoIP UC tagging CV telephone VoIP UC videos blogs webinar podcast Private videos blogs webinar podcast images SL animation learning images animation SL blog communities expert community Profile expert learning communities share immersion mobiles API community share immersion mobiles API Chris Sparshott 9
- 10. Who owns my profile? Chris Sparshott 10
- 11. Authority To Access homomorphic Profile encryption Reputation 2.0 1. Basic Profile 5. Data 2. Activity Profile 2.0 4. Relationships Chris Sparshott 3. Participation 11
- 12. Who owns YOUR profile? 1. Basic Profile 5. Data 2. Activity Profile 2.0 4. Relationships 3. Participation 1. Basic Profile Profile 1. Basic Profile 5. Data 2. Activity Profile 2.0 5. Data Profile 2. Activity 2.0 4. Relationships 3. Participation 4. Relationships 3. Participation Chris Sparshott 12
- 13. Chris Sparshott http://chrissparshott.com 0064 (0)21 574 696 (Sparkbouy) sparkbouy@gmail.com Portfolio http://www.slideshare.net/sparkbouy/slideshows Blog http://chrissparshott.com IBM chris_sparshott@nz.ibm.com Chris Sparshott 13
