Fundamentals for Stronger Cloud Security2.pdf
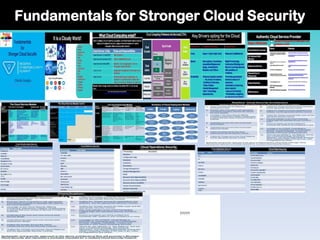
- 1. Fundamentals for Stronger Cloud Security
- 2. Fundamentals for Stronger Cloud Security Chinatu Uzuegbu CCISO, CISSP, CISM, CISA, CEH,……
- 3. https://www.linkedin.co m/in/chinatu-uzuegbu- 67593119/ https://de.slideshare.net /Chinatu Chinatu Uzuegbu CCISO, CISSP, CISM, CISA, CEH, ……….. Chinatu Uzuegbu is The Managing Cyber SecurityConsultant with RoseTech CyberCrime Solutions Limited(RoseTech). RoseTech is a Cyber Security firm runningwith the vision of assisting Entities to proactively Combat Cyber Crimes, proffering Cyber Security solutions and facilitating Cyber Security workshops. Her concern about the rate of frauds and abuses emanating with Technology gave birth to RoseTech. The Founding Past Presidentof (ISC)2 Nigeria Chapter from October 2018 to December 2021 and currentlyin the board of the Chapter's Directors. She is also a Member of the (ISC)2 Chapter Advisory Committee(CAC) ,running, with the vision of providing strategies to improve the governance and structure of (ISC)² Chapters and much more. She currently joined the (ISC)2 Security Congress Event Advisory Committee as a member. She is a Speaker,Mentor and a Global Ambassador with WomenTech Network, running with the Vision of mobilizingand empowering over 100,000 women in Technology and Cyber Security to develop and thrive in their career. She is also a Member of the Advisory board of VigiTrust,Ireland,runningwith a collaborative vision of sharing ideas and knowledge around the governance and best standards in Cyber Security as Technology evolves. Chinatu was in the Top 50 Women in Cyber Security Finalistby Cyber in Africa, 2020 accolade. Prior to RoseTech, she had acquired over 20 years wealth of experience as an IT Professional with some Financial Institutions and Manufacturing firms. She kicked off her career in Cyber Security in 2008 as a Cyber Security Analyst in one of the banks in Nigeria. Professionally, she is Certified Information Systems Security Professional (CISSP), Certified Chief Information Security Officer (CCISO), Certified Information Security Manager(CISM), Certified Information Systems Auditor(CISA), Certified Ethical Hacker(CEH) and other Information Technology related certifications. She is also an (ISC)2 Authorized Instructor with various Cyber Securitytraining Suites for Individualsand Corporate Organizations. Educationally, She has honorary doctorate with London Graduate School in collaboration with Common Wealth University as an established leader in the field of Information Technology and Cyber Security. She has MSc. in Information Systems Management(ISM)from University of Liverpool and BSc. in Computer Science/Mathematicsfrom University of Port Harcourt. She is a professional member in good standing with (ISC)2 and Other Information Security Bodies. She has attended both International and Local Conferences as a Speaker, Delegate or Volunteer. She is also a Mentor in both Information Technology and Cyber Securityas well as a Blog writer in same. She is available for Cyber Securityrelated Services. Kindlyrefer below for her publications:
- 4. It is a Cloudy World! •Dropbox •GItHub •Google Cloud •MS Azure •AWS •Alibaba •Gmail •Yahoo •Digital Ocean •IBM •Dell •Salesforce •Cloud Vendors •Facebook •Linkedin •Whatsapp •Snapchat
- 5. Fundamentals for Stronger Cloud Security • What Cloud Computing entails. • Key Business Drivers for Cloud Opt-in. • The Authentic Cloud Service Provider. • The Cloud Service Models. • The Cloud Deployment Models. • The Cloud Security Architecture. • Terminologies in each Cloud Computing Module. • Conclusion: Promoting a Stronger Cloud Security Posture. • ???????
- 6. What Cloud Computing entail? Cloud Computing is a an act of granting a perpetually, convenient on-demand network access to a shared pool of configurable resources, rapidly provisioned and released with minimal management effort or service provider interaction. Cloud Service Entity Roles and Responsibilities Cloud Service Provider(CSP) Data Processor Cloud Service Customer(CSC) Data Controller/Data Owner Cloud Service Broker(CSB) Mediator, Service Aggregator, Service Arbitrager, Identity Provider Cloud Auditor Independent Validation for Conformance to standards Cloud Carrier Interconnectivity and transportation of services from one Service Provider to the other or from Service Provider to Customer. Networks, Servers, Storage, Applications, Databases, Repositories, Platforms, Services and others Refer to Cloud Computing Reference Architecture(CCRA): https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication500-292.pdf
- 7. Cloud Computing Reference Architecture(CCRA) https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication500-292.pdf
- 8. Key Drivers opting for the Cloud (Outline your Business Needs) Business Case Traditional Environment Proposed Cloud Costs Capex + Opex (High Cost) Reduced Cost(Metered) Speed Interruptions, Downtimes, Acquisition/Deployment drags, Jurisdictional Disasters and Others Rapid Provisioning, Contractual Bindings and Service Level Agreements with penalties on violations Scalability •Reduced logistics burden: • the choice of vendors, • Conflicts of Interests, • Peak of Sales, •Assets Management •other Technology dependencies. •Promotes guaranteed minimum amount of resources. •Automatic provisioning when required. • resource thresholds. • Prioritization weighting
- 9. Authentic Cloud Service Provider Name Website CAIQ(Consensus Assessments Initiative Questionnaire) andCloud Control Matrix from CSA. https://cloudsecurityalliance.org/research/cloud-controls-matrix/ https://cloudsecurityalliance.org/blog/2020/10/16/what-is-the-cloud- controls-matrix-ccm/ CSA STAR(Security, Trust, and Assurance Registry ) https://cloudsecurityalliance.org/artifacts/star-level-1-security- questionnaire-caiq-v4/ SSAE18(SOC2 &SOC3) from AICPA https://kfinancial.com/what-you-need-to-know-about-ssae-18- reports/ ISO 31000 on Risk Management https://www.iso.org/iso-31000-risk-management.html ENISA(Cloud Risk Frameworks) Europian Union Agency for Cyber Security https://www.enisa.europa.eu/topics/cloud-and-big-data/cloud- security/enisa-cloud-computing-risk-assessment. https://www.clubcloudcomputing.com/top-8-cloud-security-risks- according-enisa/ Privacy Regulations on PII GDPR, HIPAA, GLBA, PIPEDA, NDPR , PCI-DSS and others FIPS-140(Cryptographic Modules) https://csrc.nist.gov/publications/detail/fips/140/2/final NIST 800-145(Cloud Computing) https://csrc.nist.gov/publications/detail/sp/800-145/final Broad Network Access On Demand Self- Service Measured Service Shared Pool of Resources Rapid Elasticity Multi-tenancy Basic Attributes Standard Frameworks for affirmation and attestation of CSP
- 10. The Cloud Service Models Service Model Description Advantages Disadvantages Potential Customer Infrastructure As a Service •CPU •RAM •Networks •Storage •Memory •Servers •Others •Reduced cost of Asset Ownership, pram location, IT personnel and others. •Pay As you Go. •FIPS-140 HSM Cryptographic Module. •Customer has the highest level of control around Patching, Operating Systems, Applications and Data. •Loss of total control around the physical environ and Data Center, hardware, networks and other infrastructures. •Manual Scaling IT Operations Platform As a Service •IaaS •The host •Operating System(OS) •Runtime Engines •Dev. environments •Programming Languages. •Databases •Others •IaaS but Customer has control only around the development environment, the applications running on it and the data being processed. •Auto-Scaling •Seamless BCDR • IaaS + •Challenge with Vendor Lock-in/Lock- out. •Software Developer •Database Administrator. Software As a Service •IaaS + PaaS •Applications •IaaS+PaaS but Customer has control only around the Data and the Software licensing of the Applications processing the customer’s data. •IaaS +PaaS + •Issues with Data disposal and destruction. • Data Analyst •Data Processor
- 11. The Cloud Service Models Cont’d Chart of responsibilities Responsibility On-Premise IaaS PaaS SaaS Data Applications Operating System Runtime Middle ware Virtualization Servers Storage Networking Physical Activity Customer Provider
- 12. The Cloud Deployment Models Model Description Advantages Disadvantages Customer Private Dedicated to the Customer and in some cases deployed on the premise of the customer. •Focused Control. •Mostly for top secret and highly regulated Subscribers. • Quite Expensive to deploy. •Accessing Data remotely could be difficult. •Regulatory Bodies. •Top Governing Bodies. •Military and other Forces. Public Publicly available to anyone that subscribes. It is also required for seamless BCDR, Test environments, file sharing and others. •Quite cheap and affordable. •High availability of data center pool of resources. •Virtualization •Agility for customers. •On-demand provisioning. •Outsourcing of enterprise IT infrastructures. •BCDR •Minimal control of Customers resources. •Subject to threats of Spoofing, Data tampering, repudiation, Information Disclosure, Denial of Service and escalation of Privilege. •Dropbox •Gmail •iCloud •Google Drive. •One Note •Yahoo •Facebook •OneDrive •Application Development. •Application Testing •File sharing •Email Hybrid A mix of one or two deployment models, mostly a mix of Private + Public Clouds or On Premise + Public Cloud. Usually applied during bursts of sales for outsourcing Rapid elasticity in Publc Cloud. •A good economical fix for periodic on high demand sales where another deployment Model is required to add to the existing model or on premise . • Issues of Inter-operability due to complicated technology. •Jumia + AWS •On Premise Production + Public Cloud Deployment. •Others Communi ty Mostly applied for subscribers with common goal for example an Alumni Class of a University, forum of all Cloud Security Pros. • Focused control. •Shared Computing Resources. •Multiple Organizaions •Identity Management and Authenti •Communities with shared goal. •Whatsapp groups •Fedrated Dentities
- 13. Summary of Cloud Deployment Models Public Supports All Users Software & Hardware testing Subscription App Dev & Testing File Sharing Private Single Org. Managed internally or by service provider More Expensive Tighter Security Better Privacy Hybrid Interconnected Infrastructure Enterprise, Private and Public Cloud Can scale rapidly Cloud Bursting Peak sales Community Shared Resources Multiple Orgs. Community of Works Example Universities Cloud Security Association
- 14. Resilient Cloud Security Architecture Resilient Cloud Security with ambience must start from the outset of adoption: 1 . Cloud Computing with the Reference Architecture in mind. 2 . Business Value Propositions with appropriate Cost Benefit analysis to ascertain the need for the Cloud adoption. 3 . Leverage on the Cloud Security Alliance Consensus Assessment Initiative Questionnaire to assure that your choice of Service Provider is authentic. 4 . Understand the pros and cons around each Service Model 5 . Understand the pros and cons around each Deployment Model. 6 . Outline the threats around the Cloud Infrastructures and the Security Controls. 7 . Outline the Threats around the Cloud Platforms and the appropriate Security Controls. 8. Outline the Threats around the Cloud Operations and the appropriate Security Controls. 9. Outline the Threats around the Applications and Software and the appropriate Security Controls. 10. Outline the Threats around the Data Layer and the appropriate Security Controls. 11. Pay close attention to the Cloud Computing Cutting edge with seamless security controls in mind. 12. Ensure processes are being audited and monitored with resilience and compliance in mind. 13. Leverage on the STRIDE Threat Model to ascertain an acceptable level of Confidentiality, Process Integrity, Availability , Privacy and Security in your Cloud computing Services. 14. Above all, pay attention to due diligence and due care, Contractual bindings, Service level Agreement and Shared Responsibility among the Cloud Computing Parties is the way to go, Laws, PII Regulations and others. Systematic and granular approach to the above architectural flow will promote a Stronger Cloud Security and represent a workable checklist for a resilient Cloud Security Posture.
- 15. Cloud Infrastructures Security (Networks, CPU, Storage, Servers, Memory, others Terminology Description Virtualization (Core) computer sharing its hardware resources with multiple digitally separated environments. Automation The Cloud leverages on (CI/CD) automated processes through APIs for orchestrating the resources around the Cloud tenants. Hypervisor Computer and memory sharing of its resources across multiple Virtual Machines. Threat(Hyperjacking) Virtual Machine The Virtual Instance in form of Software, such as OS for hosting other applications and software for sharing purposes. Threat(VM Host/Guest Escape, Tampering, Spoofing, Information Disclosure, escalation of priviledge, Repudiation) Management Plane The Cloud Interface applied for necessary administrations and configurations. Threat(Sprawl, Denial of Service) Multi-tenancy Posing as the most threatening aspect of Cloud Computing. Jurisdiction Very important to understand the jurisdiction or location the Cloud Provider’s hosting is domiciled. Reservations, Limits, shares Methods of sharing resources in the cloud: Guaranteed minimum, Maximum amount and Prioritization weighting) Isolation Processes and VMs should be logically isolated, a tenant must not know what goes on with the other. Threat(Inference and aggregations) Volume Storage The two types of storage in IaaS, Volume is more like the traditional drives and partitions . Object Storage Key Value and Flat files, Virtual Images Networks Sharing of Network infrastructures such as NAS, SDN, VPN, VPC, IPSec
- 16. Cloud Platforms Security (End Point, OS, Runtime, Databases, AppDevops and others Terminology Description Portability Seamless transfer of data and applications from one CSP to another or from Premise to CSP and vice versa. Threat(Vendor Lock-in/out). Do not use proprietary data format. Inter Operability Re-use or movement of resources from CSP or the other with seamless interaction and handshake in mind. Patches Patches should be orchestrated with risk mitigation in mind. (Threat: Geographical Boundaries and Time Zones) SIEM Security Information and Events Management should run with correlations and Aggregation of similar events(Threat: Dashboard sensitive info disclosure) Malwares Run Software and OS Updates and necessary Ant-Malwares with updated DATs. IAM Secure Provisioning and de-provisioning of access rights. Grant access based on Regulation, Governance, least privilege and need to know. Databases Data running on DBMS for storing and generating subset of info in various ways. Reversibility Seamless removal of customer data from the CSP’s platform. Dev. Environment Runtime Environment provisioned for coding and compiling software components. Structured Relational Database driven file layout, always necessary for seamless data portability and inter-operability. Unstructured Not with any structure or layout such as email file, documents and others. Data Format Always build your file format with standard ascii or xml format, do not use proprietary data format. Programming Lang For coding and Software developments, any coding language of your choice would be
- 17. Cloud Operations Security (BCDR, Incidents, Changes, Patches, Baselines, Uptime, others) Terminology Description Baselines Minimum Configuration on all systems applied as the standard requirement across platforms. Configuration Mgt Management of all Configuration Items leveraging on the CMDB. Standards Requirements mandated on the Platforms to run as baselines. Guidelines Non-mandatory instructions for seamless operations such as Manual of Operations and Instructions. Procedures Step-by-step approach to achieving a task, for example, keep the SIEM of a VM instance on during the maintenance of the VM. Change Management Ensure changes are controlled and approved by the change management board. Incident Management Incident response and sustain after incident is paramount. BCDR BCDR must be done annually with restoration and recovery of data in mind. Recovery Time Objective(RTO) The amount of time required to recover from a disaster as acceptable by your org. Recovery Point Objective(RPO) The amount of data, measured in time, required to recover from a disaster Recovery Service Level(RSL) The percentage of service required for recovery.
- 18. Cloud Applications Security (Sand boxing, SAST, DAST, SDLC, others) Terminology Security SDLC Security must apply from the inception: Data Gathering, Definition, Design, Test, deploy, maintain, monitor, dispose API Application Programming Interface leveraging on REST (representational State transfer) and SOAP(Simple Object access protocol) API Security is paramount. Data Format Structured layout with SOAP and REST in mind Sand-boxing Running of an untested code in an isolated area of the OS different from Production. App Virtualization Running an application on top of the Host OS through a Hypervisor. Penetration Testing Leverage on hacking tools to test based on defend-in=depth in mind. Static Application Software Testing Leverages on source and byte codes to test with knowledge of the system in mind. Dynamic Test on the stress, performance , runtime and memory without the
- 19. Cloud Data Security (Data Phases, Encryptions, DLP,DRM,IRM, Others) Terminology Security Data Creation(Create) Classification, labeling and re-creation of data. Data at Rest(Store) The security of data starts from the Storing stage of the data. The DLP should be deployed on the host System Data in Use(Use) Data in Use, The DLP should be deployed on Client System and Digital Signatures to prevent Repudiation. Data in Transit(share) The DLP should be deployed on the Network Perimeter and should strongly apply in the Share phase for egress monitoring. Data Archive Archival of data should run with data retrieval and Rention Policy in mind. Data Disposal Data should be disposed securely leveraging on Cryptographic erasure and crypto shredder. Deletion is not the way. Data Loss Prevention(DLP) Critical tool for egress monitoring, enforcement of policy and e- discovery and data collections. Data/Inf. Right Mgt.(IRM) DRM and IRM for protecting your Copyright or Intellectual properties such as your Publications, Consumer media and Applications from unauthorized usage or misuse. Data Encryption The process of converting readable text to cipher or unreadable format. Levarages on Symmetric and asymmetric types of
- 20. Threat Models in Cloud computing DREAD Model
- 21. Conclusion: Fundamentals of a Stronger Cloud Security To achieve a Measurable and desired Cloud Security Outcome: 1. Ensure you employ the cloud security concepts right from inception. 2. Review the Cloud Security checklist in the Cloud Security Architecture Slide. 3. Our goal is to achieve an acceptable level of Confidentiality, Integrity, Privacy, Security and availability between the CSC and CSP relationships. 4. Leverage on the Preventative, Detective, Deterrent, Compensative, Corrective, Recovery and Directive controls to counter the core threats in Cloud Computing, 5. Keep monitoring accordingly. 6. Above ALL, Pay attention to your DUE DILIGENCE and DUE CARE. 7. The cloud Service Customer is Liable to any legal bindings. 8. Outline your contract terms and Service Level Agreement and make them explicit and also note the shared responsibilities. STRONGER CLOUD SECURITY is ACHIEVABLE and MUST BE ONGOING.
- 22. ?????
- 23. Thank You