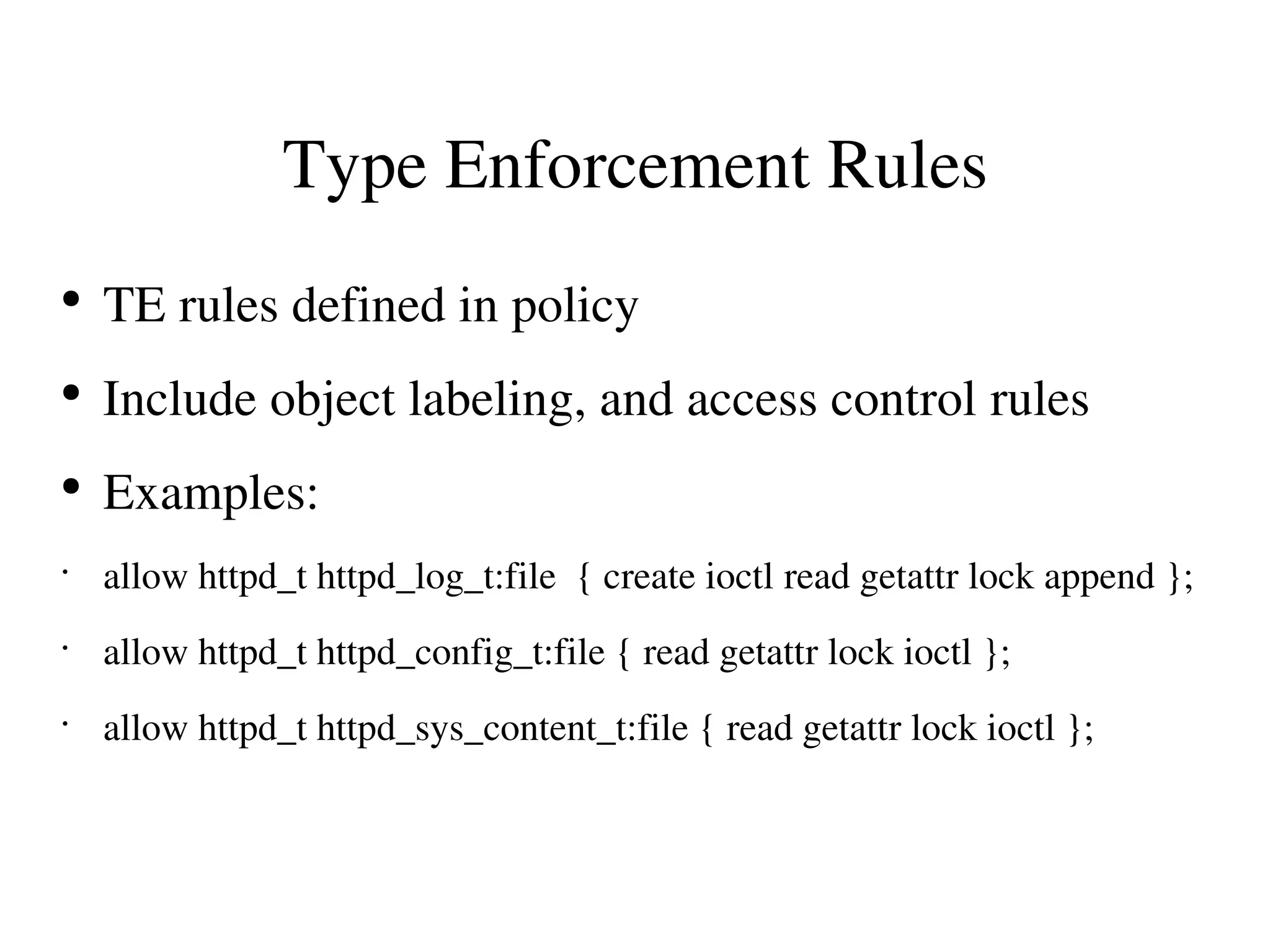
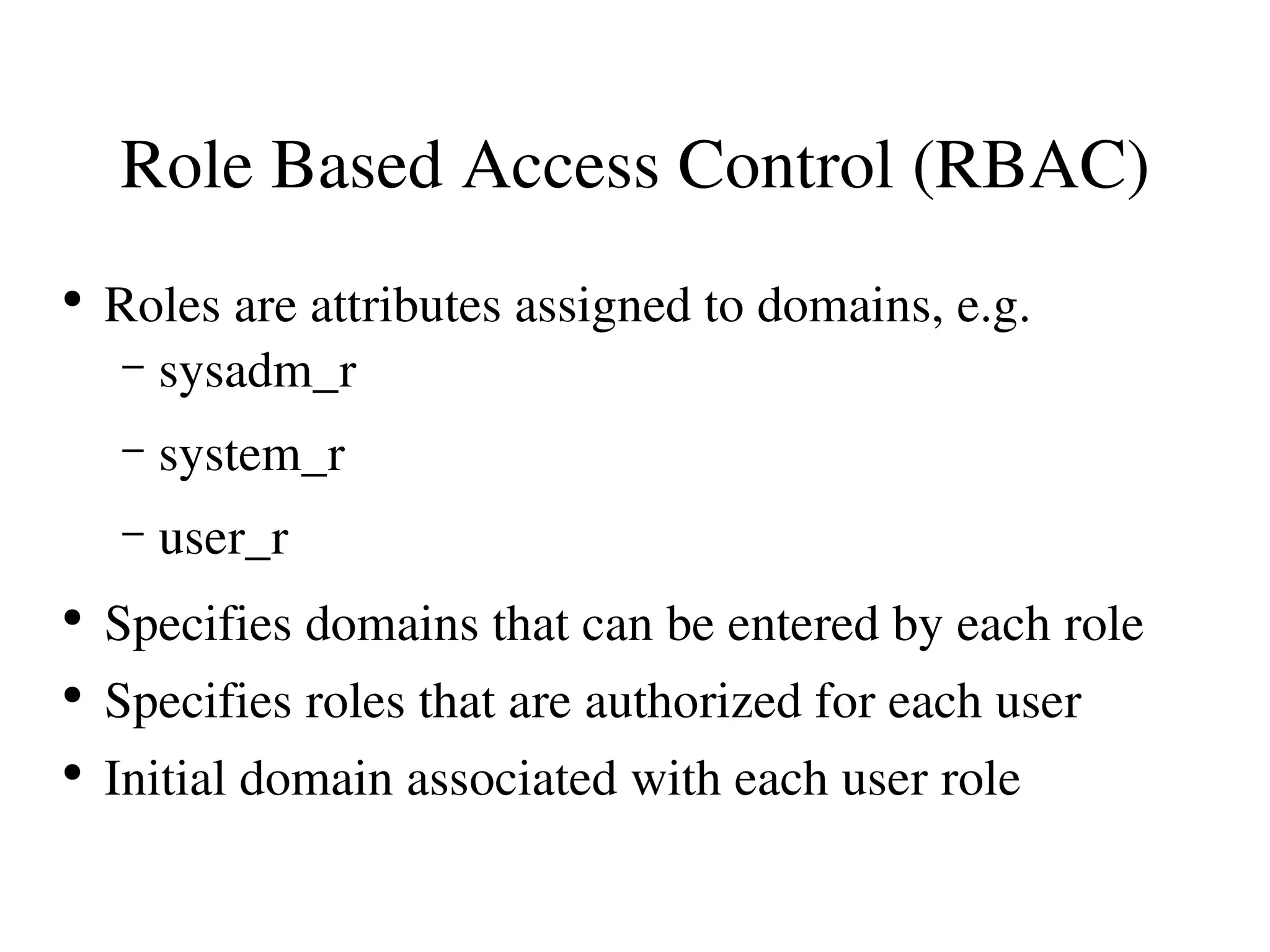
This document provides an overview of NSA Security Enhanced Linux (SELinux). SELinux implements mandatory access control (MAC) to provide fine-grained access control and confinement of processes. It uses type enforcement (TE) and role-based access control (RBAC) models to define types for objects and domains for processes. TE rules in the SELinux policy specify which domains can access which object types. SELinux has been merged into the Linux kernel and adopted by several distributions to enhance security for network-facing services. Current development focuses on multi-level security and a reference policy, with future work on tools, policies, and additional applications.