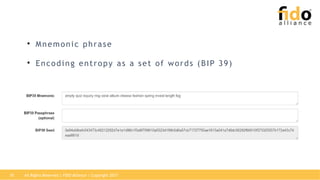
The document discusses the intersection of FIDO (Fast Identity Online) and blockchain technologies, emphasizing the need for strong cryptography to ensure trust and security in digital transactions. It highlights the importance of private keys for asset ownership in blockchain applications and the evolution of malware targeting these keys, necessitating new security devices for user validation. Additionally, it outlines the U2F (Universal 2nd Factor) authentication process and previews future collaboration opportunities within the realm of self-sovereign identity and cryptographic proofs.