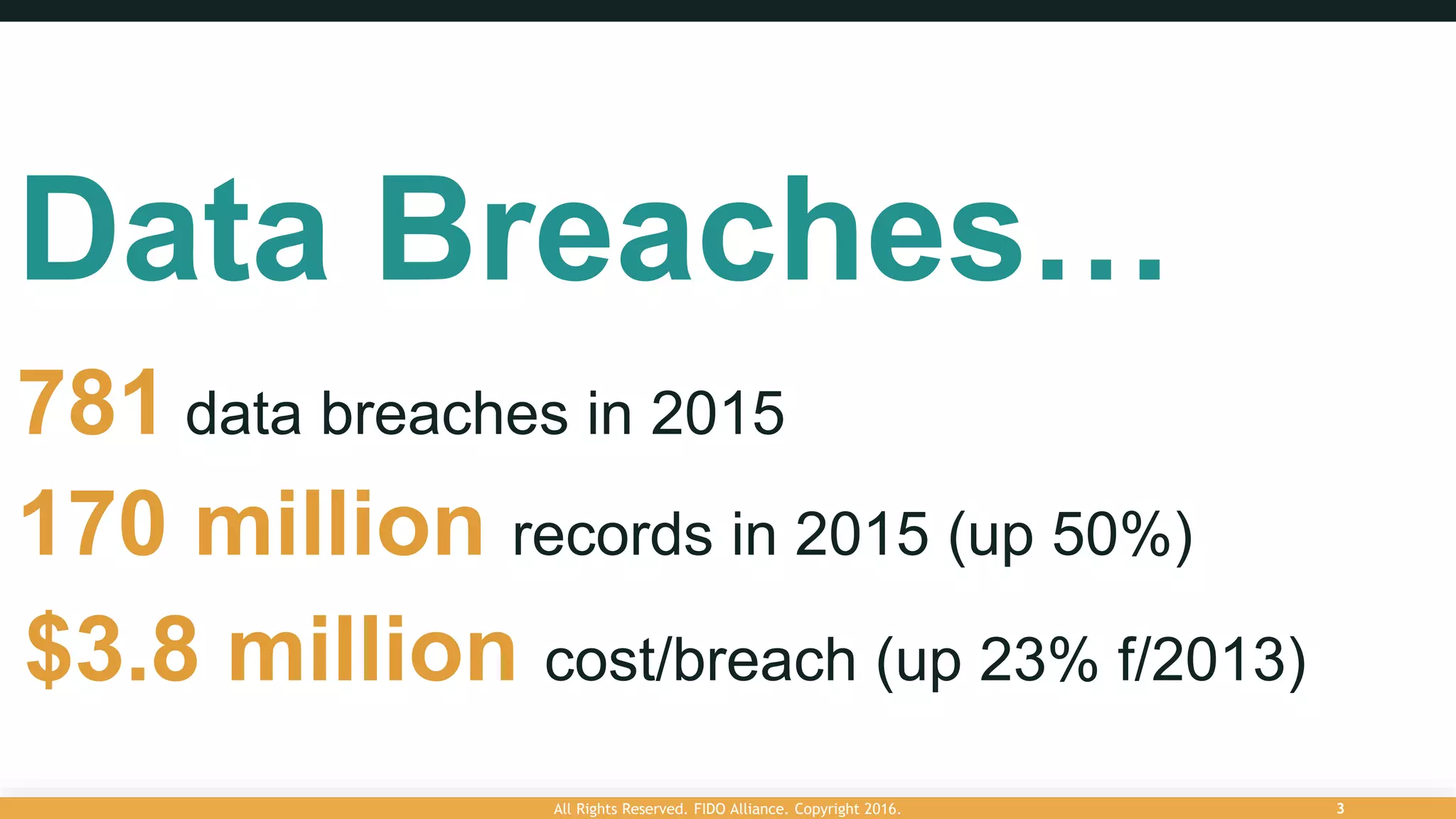
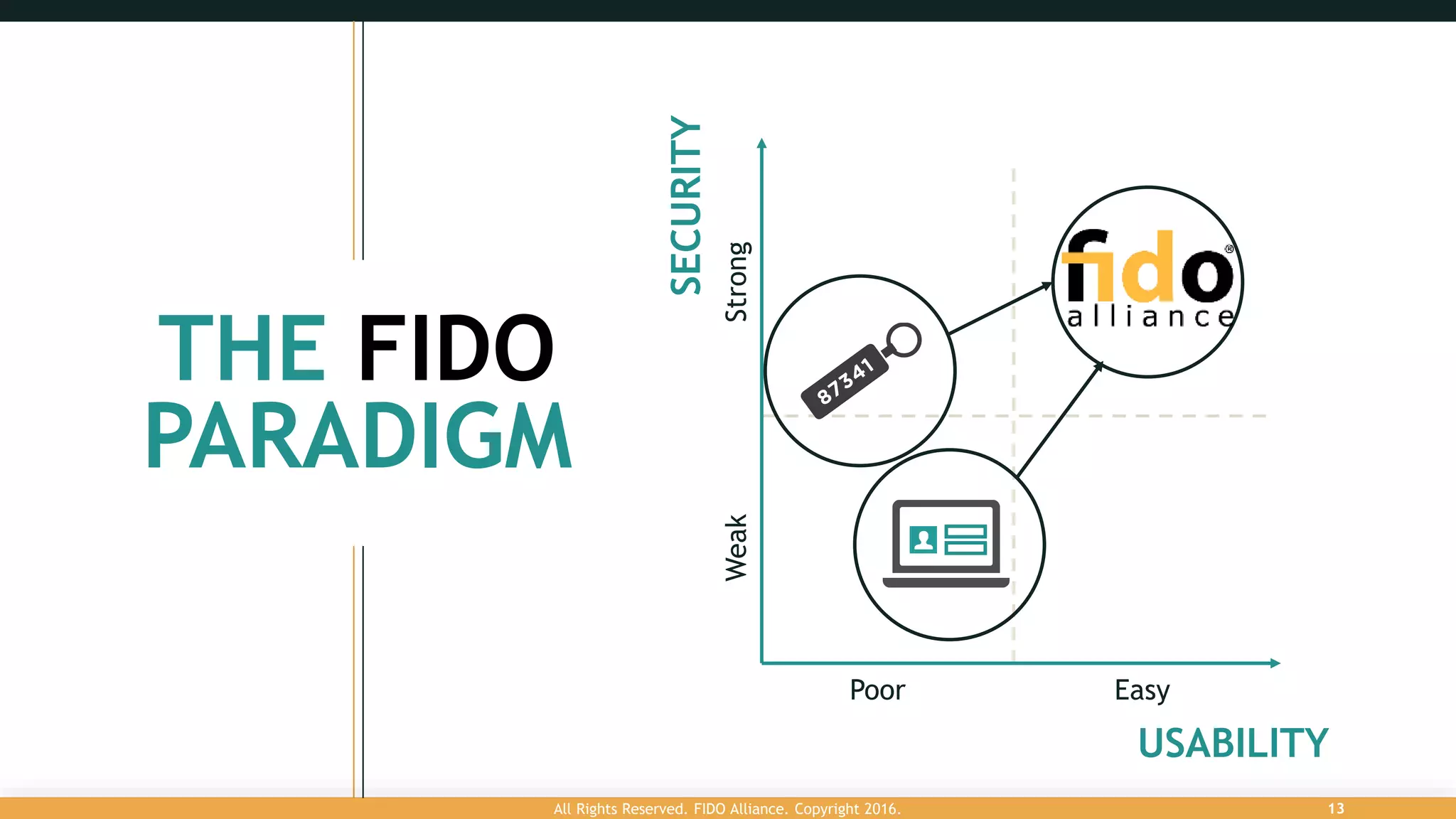
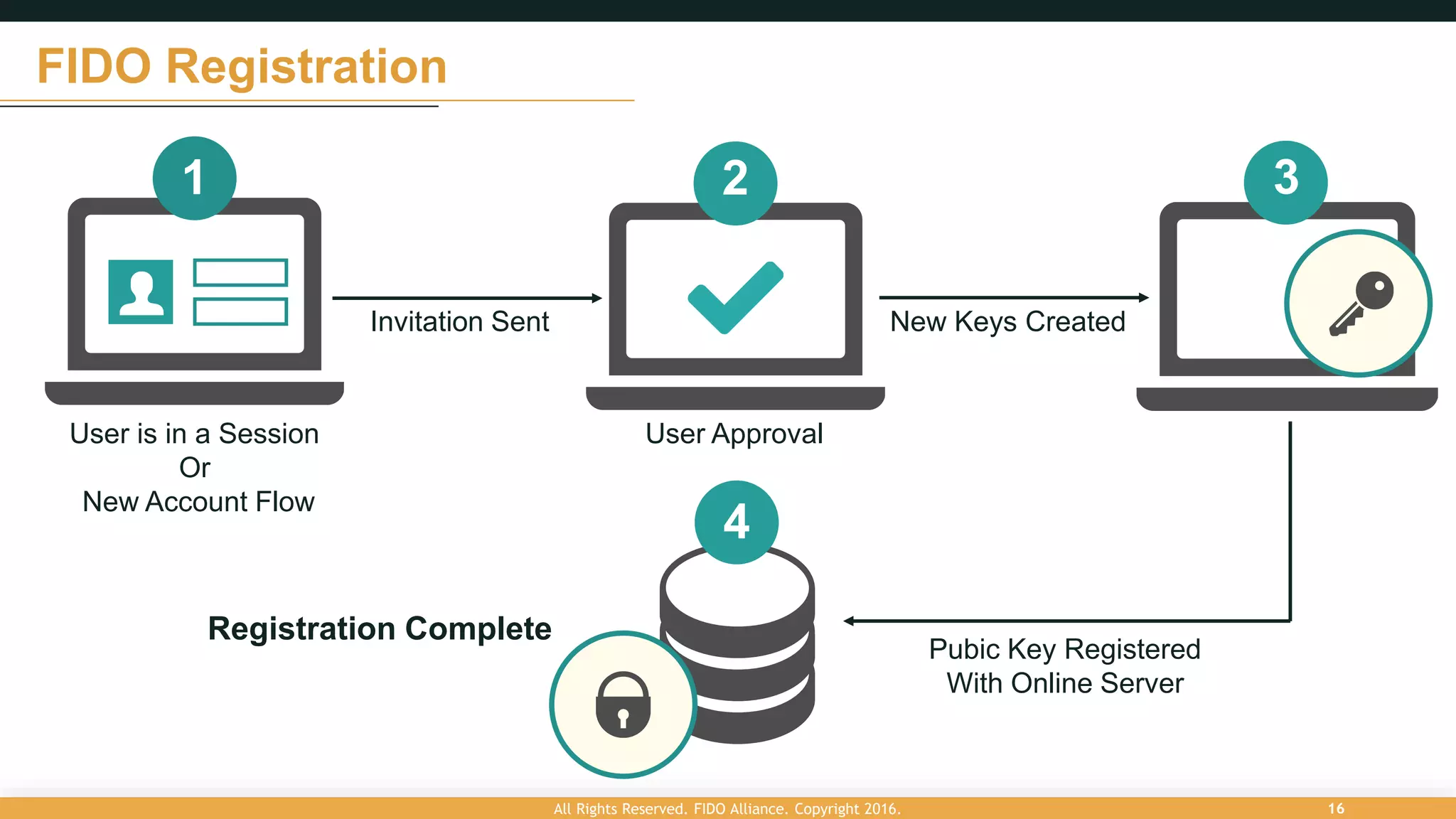
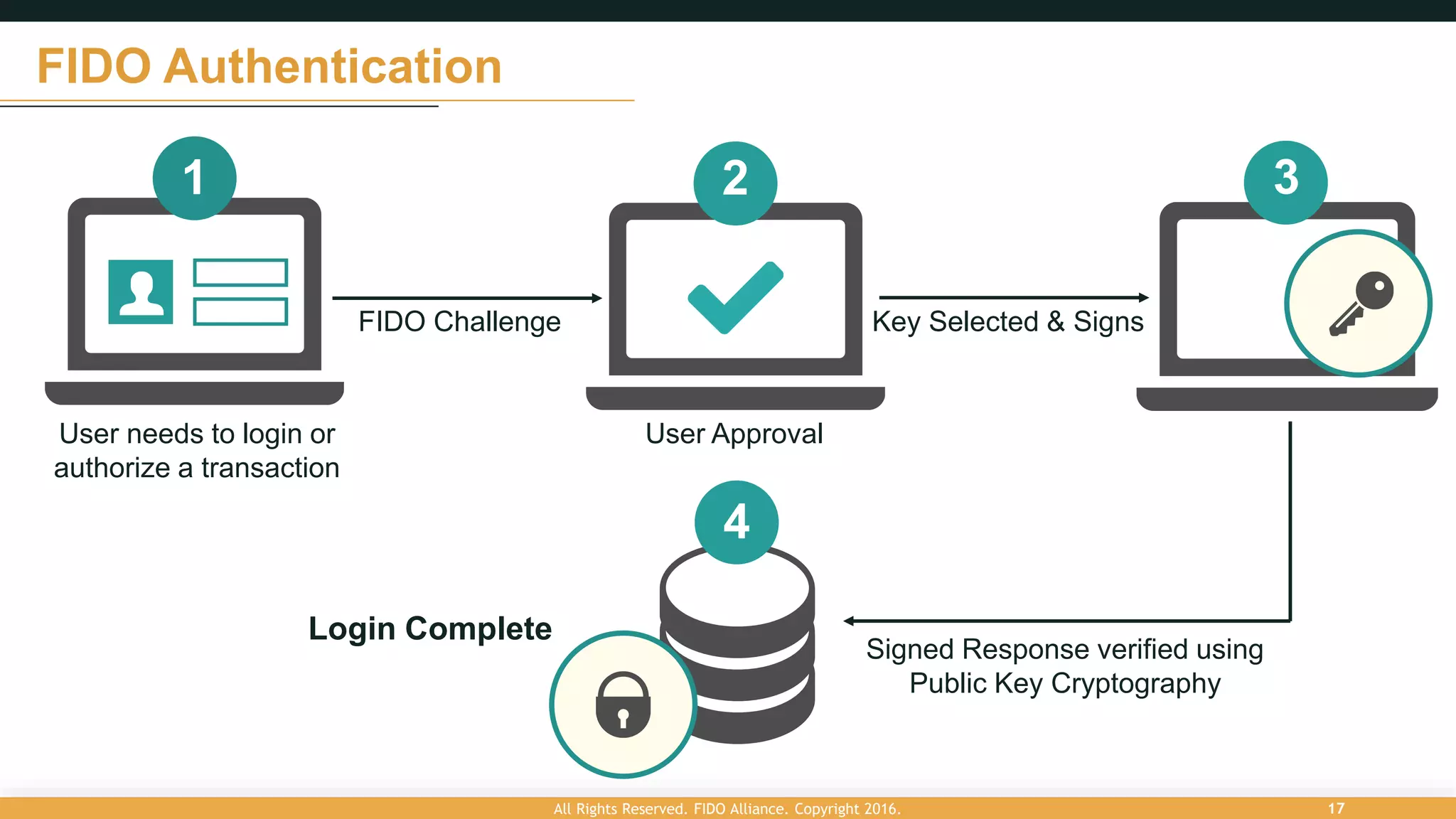
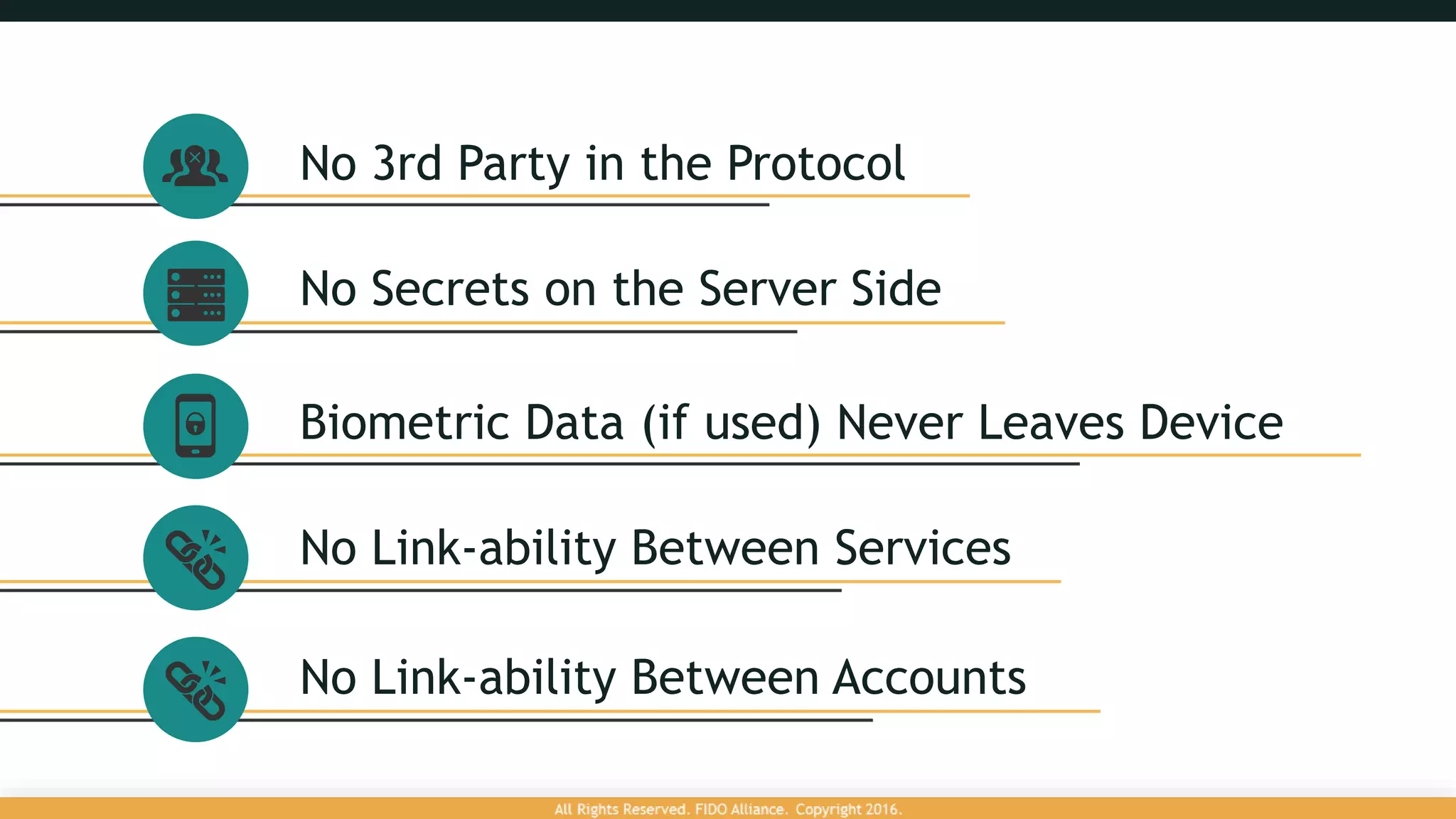
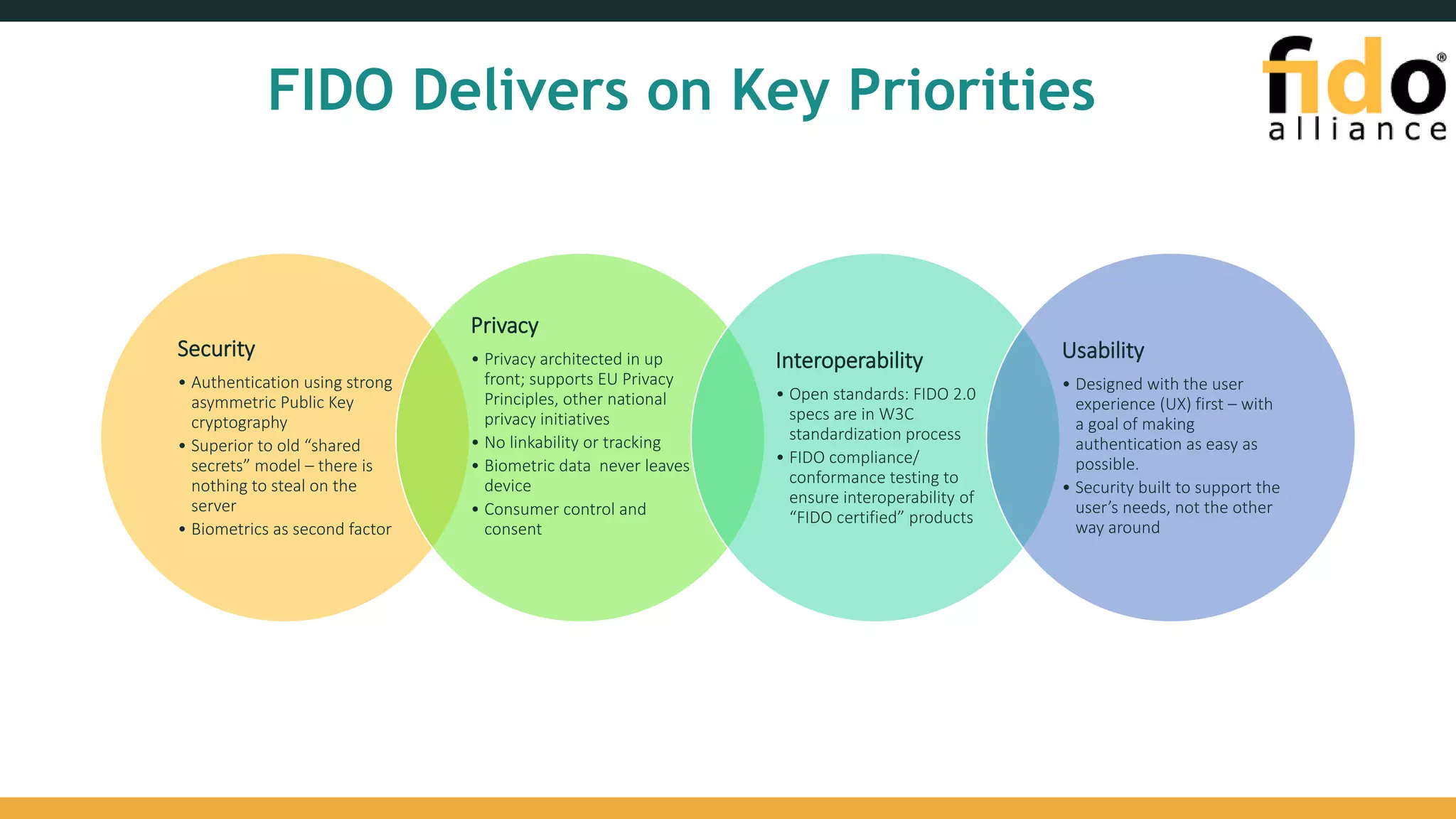
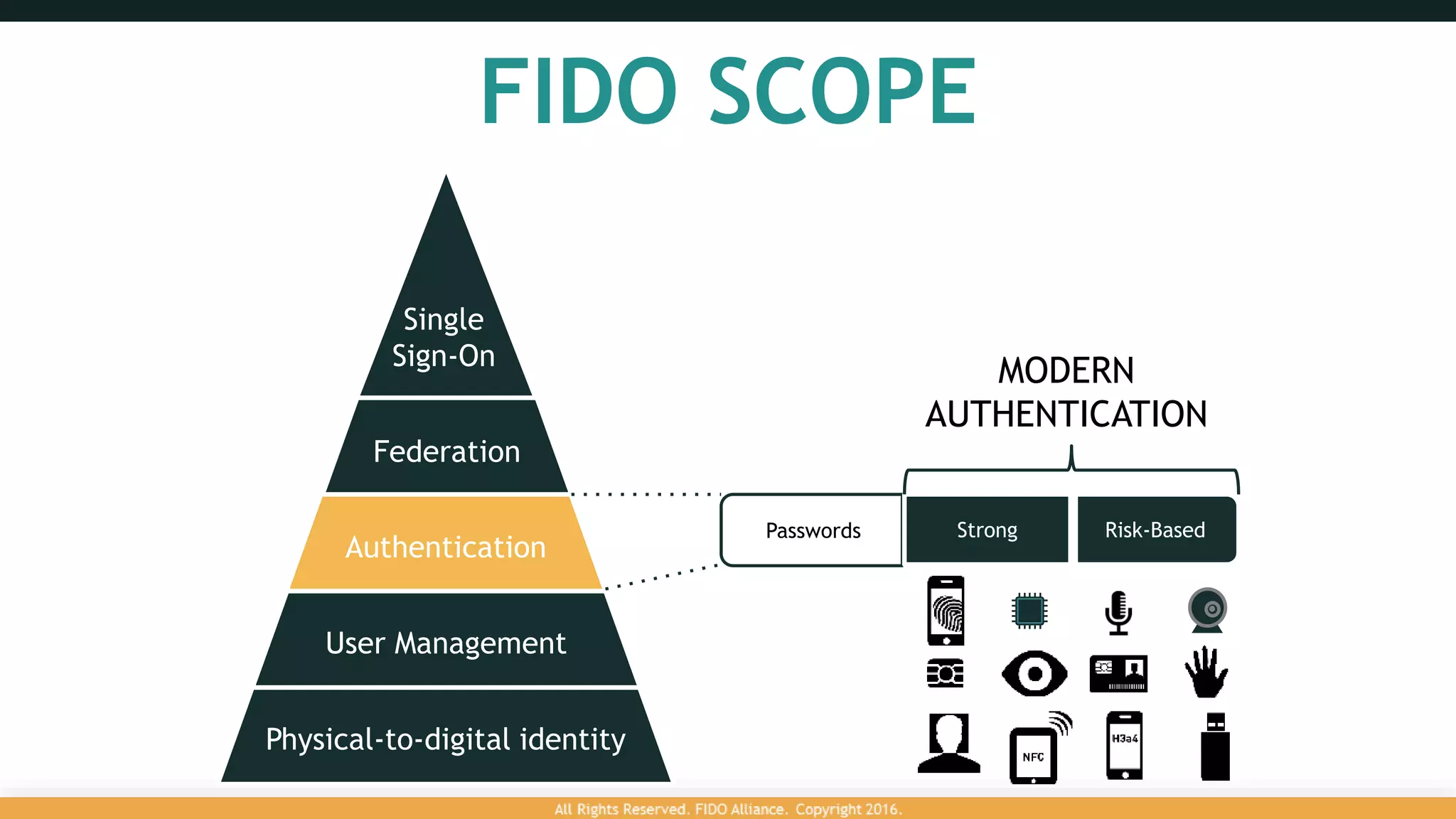
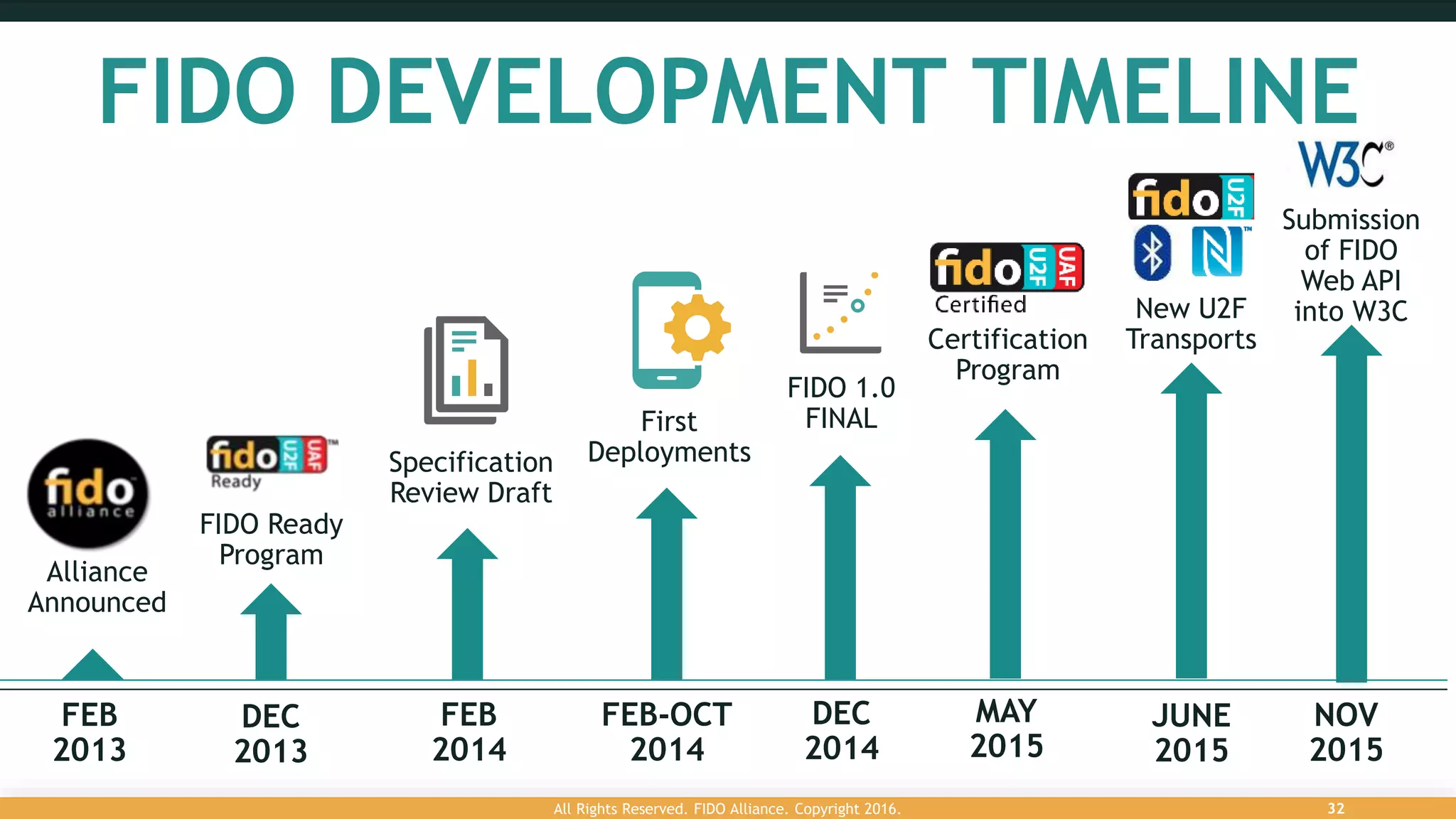
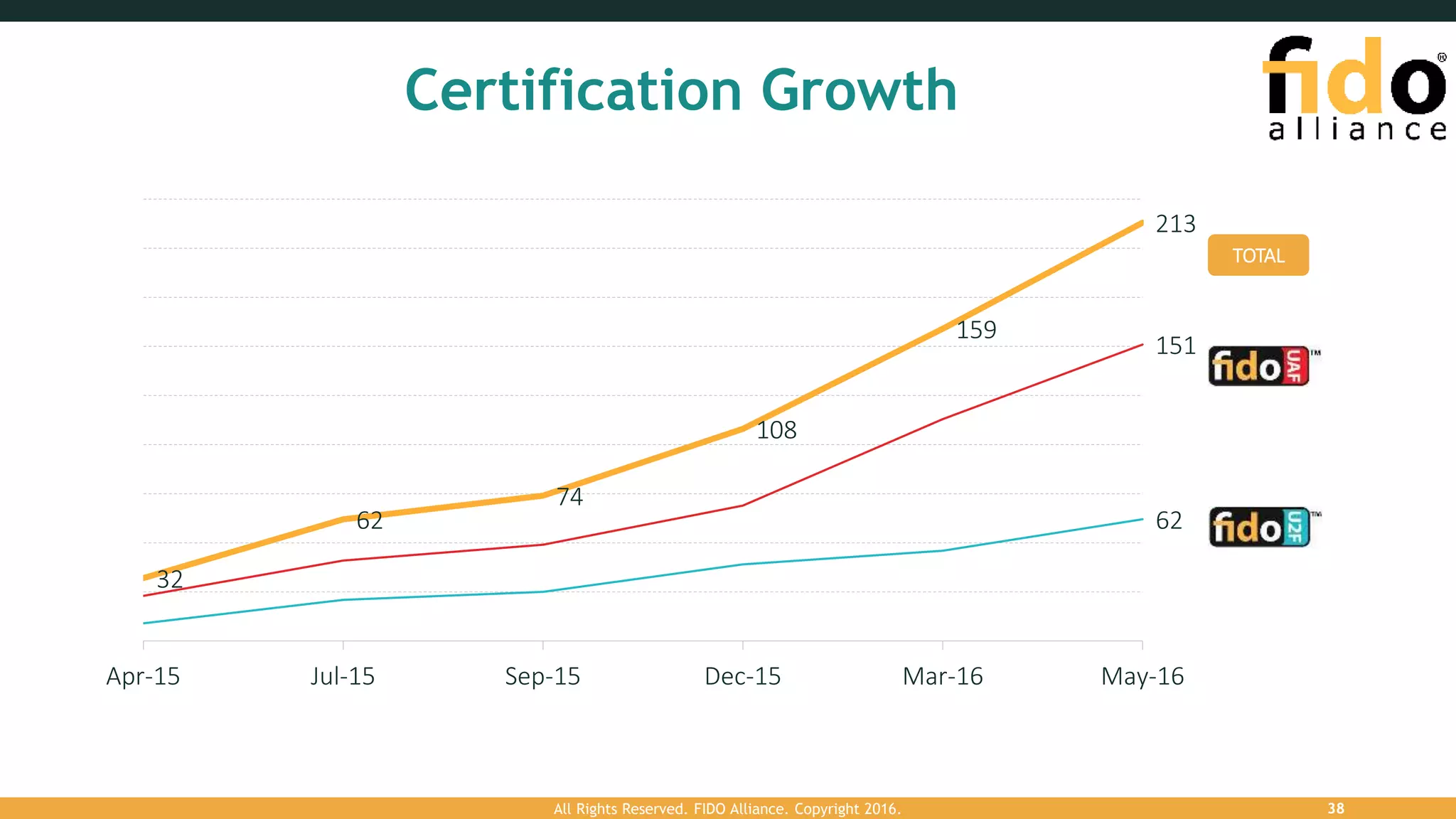
The FIDO Alliance addresses the growing problem of data breaches resulting from compromised credentials, promoting a new authentication model that utilizes public key cryptography instead of traditional passwords. This model enhances security, preserves user privacy, and improves user experience by eliminating shared secrets and minimizing data theft risks. With over 250 member organizations, the FIDO Alliance aims to establish open standards for secure online authentication and has seen significant adoption of its certified products in the market.