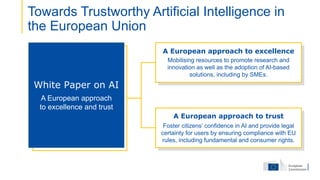
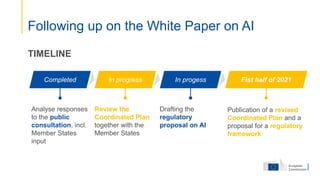
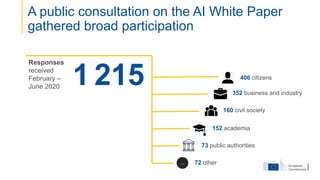
This document outlines the agenda for an international conference on quantum computing, artificial intelligence, and related topics. The conference will feature several keynote speakers and panels discussing various applications and policy issues. Topics include the European Commission's work on AI, practical applications of quantum computing in medicine, the impact of AI and computing power on healthcare, and perspectives on quantum computing from various governments and companies. The document provides names, titles, and affiliations for multiple speakers as well as summaries of some of their planned presentations.