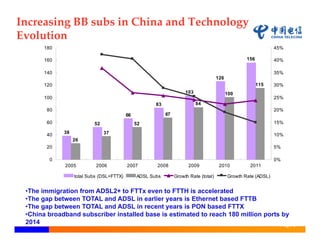
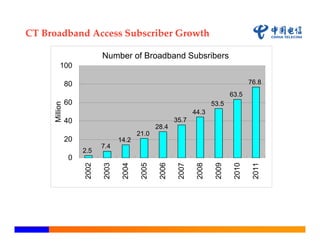
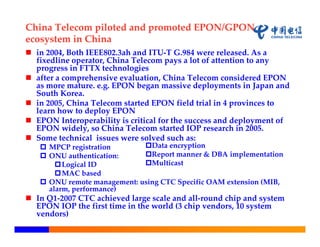
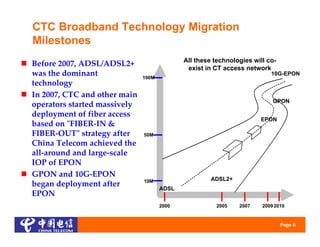
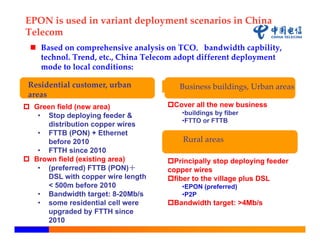
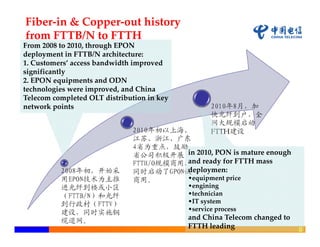
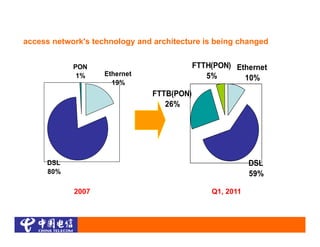
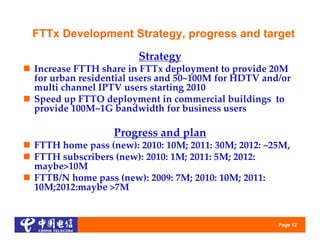
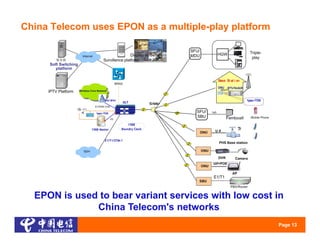
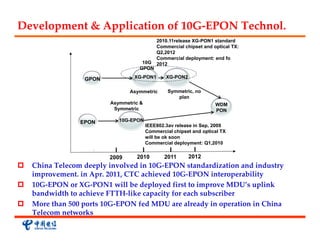
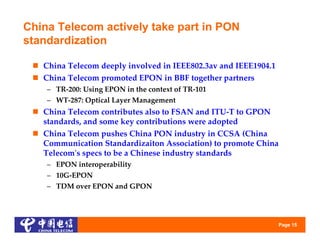
China Telecom has been migrating from ADSL to fiber technologies like EPON and GPON to meet increasing broadband subscriber and bandwidth demands, piloting EPON in 2005 and making it a core access technology due to its maturity and interoperability. They aim to accelerate FTTH deployment through projects like "Broadband China, Optical City" to reach 100 million FTTH homes by 2015 using EPON and GPON, while also starting rollout of 10G-EPON to improve bandwidth for multi-dwelling units.