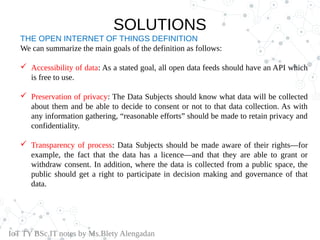
The document discusses the ethical implications of the Internet of Things (IoT), addressing issues of privacy, control, and environmental impact associated with connected devices. It highlights the dual nature of technology, which can both disrupt and enhance human life, and the importance of responsible data management. Additionally, it emphasizes the need for transparency, consent, and community involvement in the governance of IoT data to ensure ethical usage.