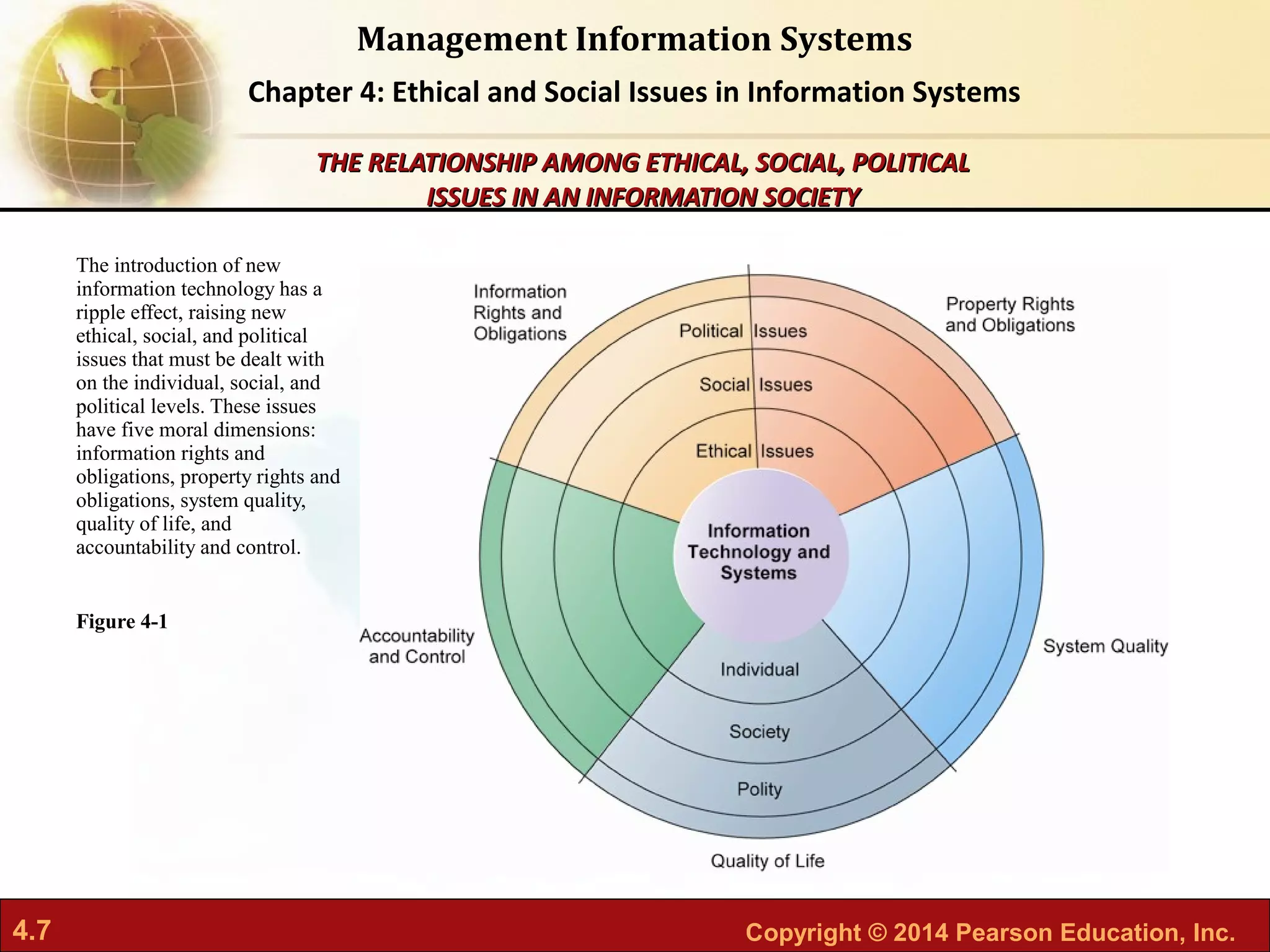
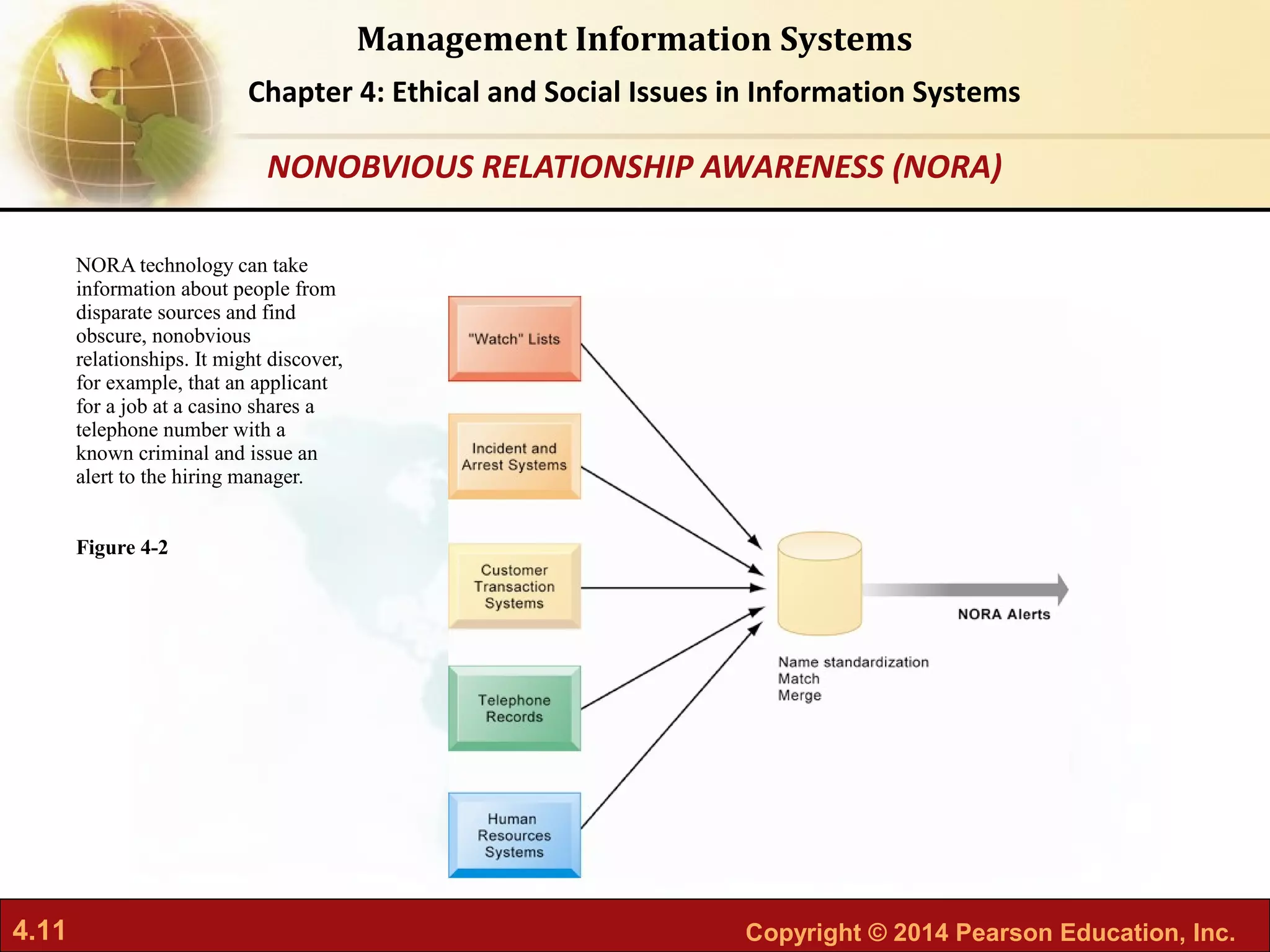
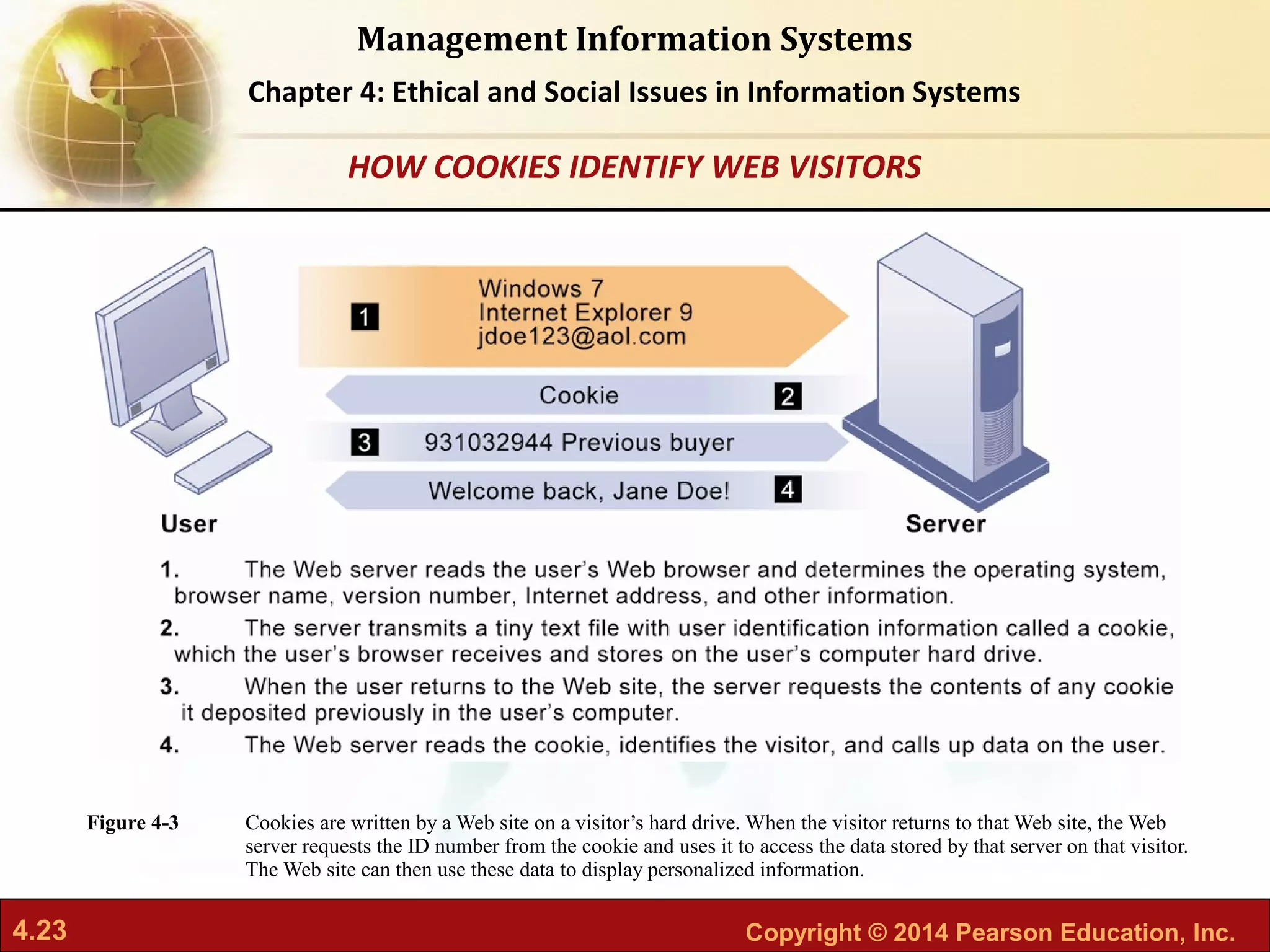
The document discusses ethical and social issues in information systems, focusing on privacy, intellectual property rights, and the implications of technology on society. It outlines key principles for ethical decision-making, the impact of information systems on individual rights, and provides a framework for ethical analysis. It also addresses contemporary challenges, such as behavioral targeting, data mining, and the balance of power in the digital age.