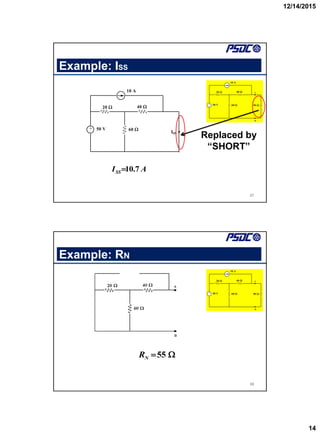
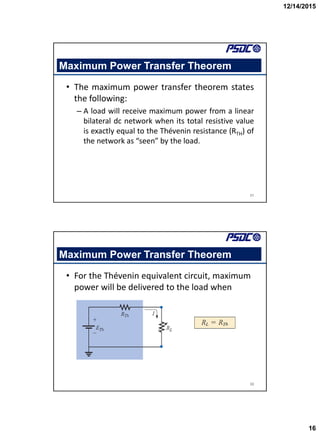
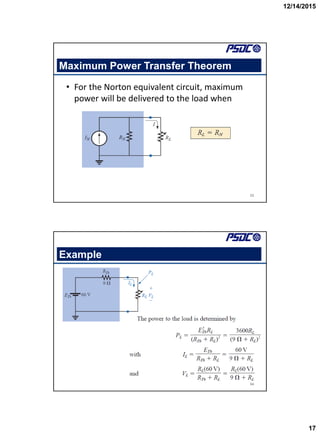
This document summarizes a lecture on advanced network theorems. The lecture covers Thevenin's theorem, Norton's theorem, and the maximum power transfer theorem. Examples are provided to demonstrate how to use these theorems to analyze circuits and calculate current and voltage values. The document concludes with a post-test question and homework assignment related to analyzing circuits using these network theorems.

![12/14/2015
7
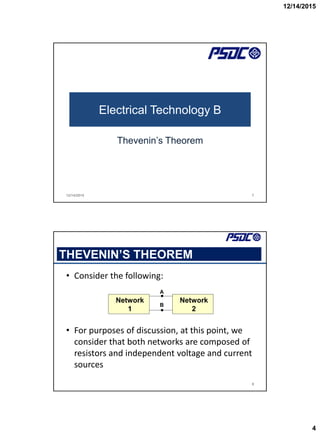
Thevenin Equivalent Resistance, RTH
• The total resistance across the terminals A and
B is called RTHEVENIN and shorten this to RTH.
• For the circuit shown above,
RTH = R4 // [ R3 + (R1 // R2) ]
13
R1
R2
R3
R4
A
B
Thevenin Equivalent Circuit
• We had obtained the VTH and RTH. Now, we can replace
Network 1 with the following network.
14
VTH
RTH
A
B
+
_
A
B
Network
2
VTH
RTH
+
_
](https://image.slidesharecdn.com/etblo1advancednetworktheoremspart2-221118161914-2a6be38d/85/ETB-LO1-Advanced-Network-Theorems-Part-2-pdf-7-320.jpg)



![12/14/2015
15
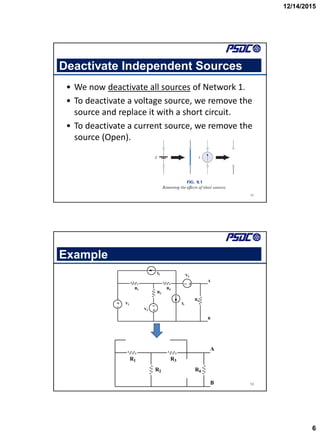
Example: Norton Equivalent Circuit
29
10.7 A 55 50
+
_
20
60
40
50
10 A
50 V
A
B
𝐴 = 𝜋𝑟2
𝑰𝟓𝟎𝛀 = [55/(55+50)]10.7 = 5.6 A
Electrical Technology B
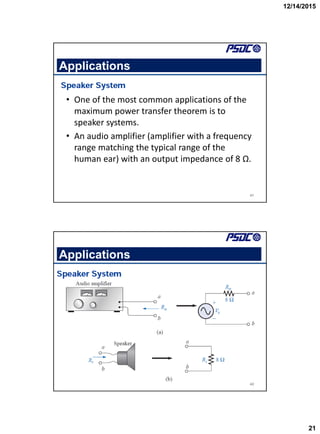
Maximum Power Transfer Theorem
12/14/2015 30](https://image.slidesharecdn.com/etblo1advancednetworktheoremspart2-221118161914-2a6be38d/85/ETB-LO1-Advanced-Network-Theorems-Part-2-pdf-15-320.jpg)


![12/14/2015
23
45
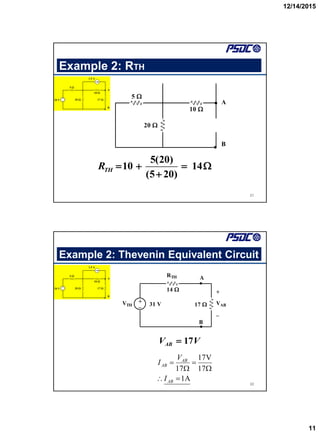
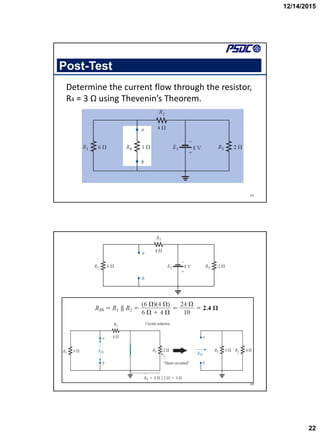
𝑰𝟑𝛀 = [4.8/(2.4 + 3)]
= 0.89 A
Homework
46
Find the Thevenin equivalent circuit for the
network in the shaded area .](https://image.slidesharecdn.com/etblo1advancednetworktheoremspart2-221118161914-2a6be38d/85/ETB-LO1-Advanced-Network-Theorems-Part-2-pdf-23-320.jpg)