We can estimate square roots in three ways:
1. To the nearest whole number by finding the square root of the nearest perfect square number
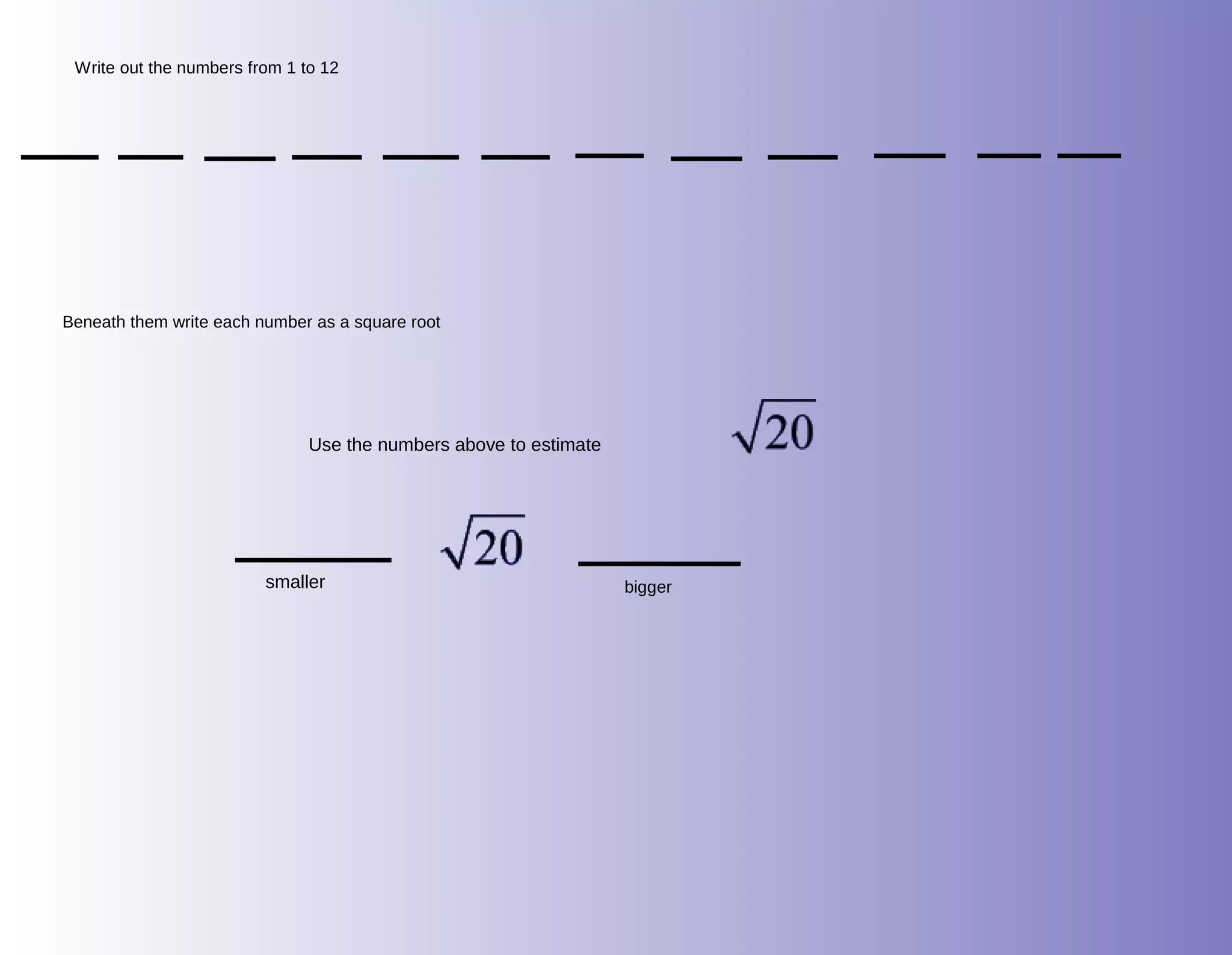
2. To the nearest tenth by considering numbers smaller and larger than the target number and rounding the calculator value
3. Using a calculator, which provides an estimate even for perfect squares if we round the answer