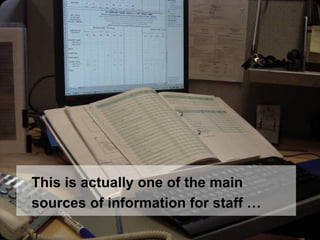
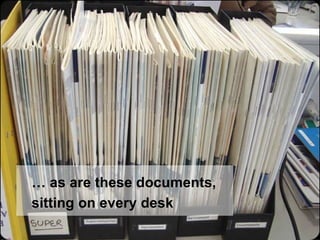
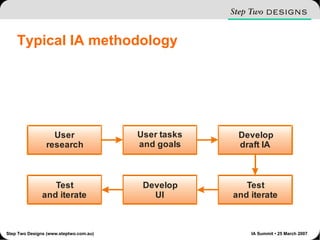
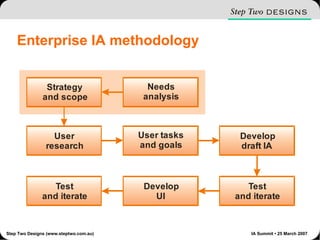
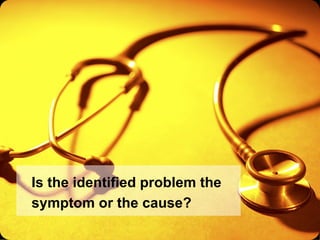
The document discusses the importance of understanding the real problems organizations face before designing solutions, emphasizing the need for ethnographic needs analysis. It argues that typical methodologies often overlook the complexities of organizational realities, and suggests starting the process two steps earlier. Additionally, it highlights the launch of global intranet innovation awards to recognize individual contributions within the field.




![Questions? James Robertson [email_address] Website: www.steptwo.com.au RSS feed: www.steptwo.com.au/columntwo/index.xml Visit our site for 150+ articles on intranets, usability, IA, content management and more](https://image.slidesharecdn.com/enterprise-ia-methodologies-starting-two-steps-earlier-3766/85/Enterprise-IA-methodologies-starting-two-steps-earlier-24-320.jpg)