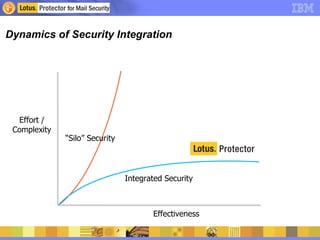
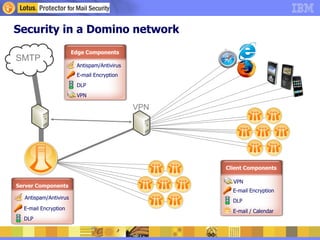
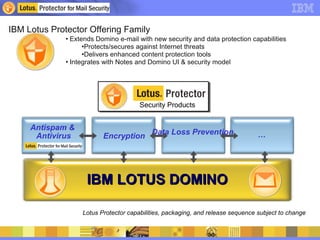
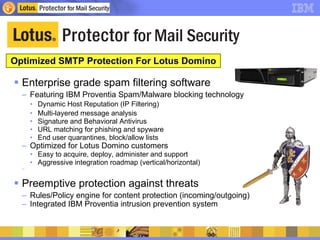
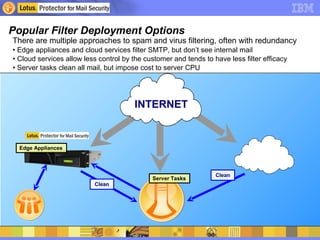
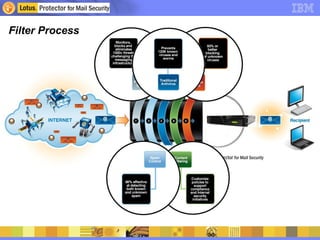
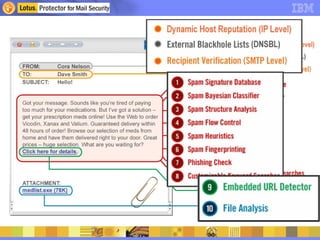
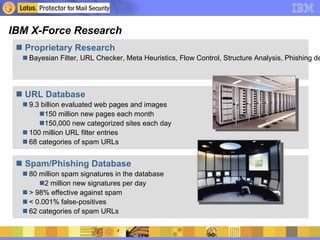
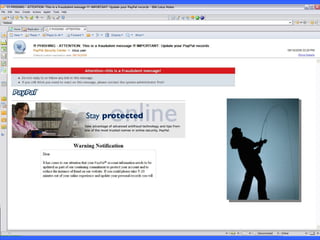
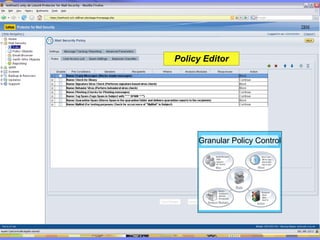
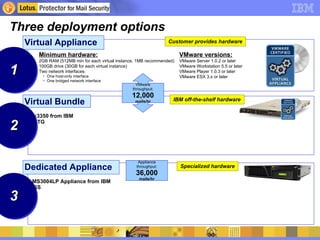
Lotus Domino provides robust email security capabilities including strong password authentication and encryption. As email threats like spam, phishing and malware have increased, comprising up to 90% of email traffic, integrated email security solutions are needed. IBM Lotus Protector extends Domino's security with antispam, antivirus, encryption, data loss prevention and other tools to protect against modern threats while maintaining Domino's access controls and policies. It offers deployment options including virtual appliances, dedicated hardware, and integration with existing Domino infrastructure.