Embed presentation
Downloaded 16 times

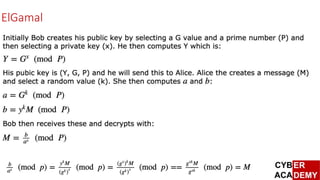

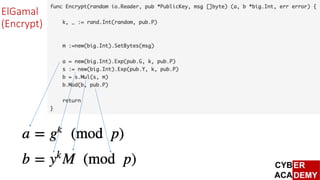
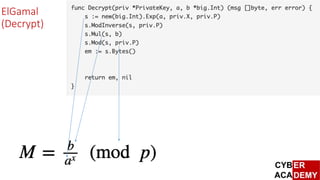
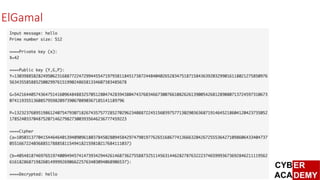

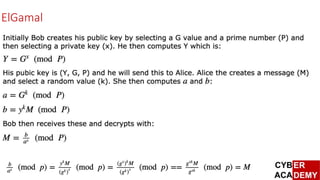
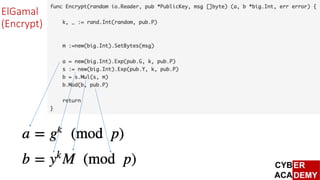
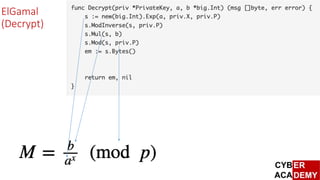
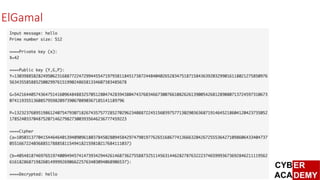
The document discusses the ElGamal public key encryption algorithm. It explains that ElGamal uses discrete logarithms to generate a public and private key during key generation. The public key is used to encrypt messages while the private key is used for decryption. The document was written by Prof. Bill Buchanan and provides a link to further information about ElGamal encryption on asecuritysite.com.