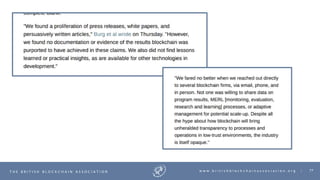
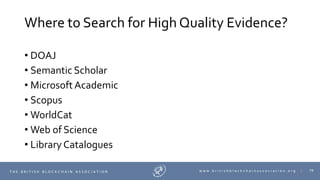
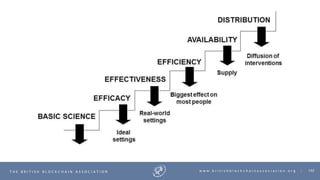
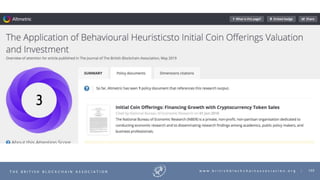
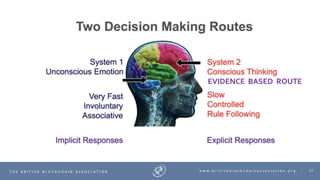
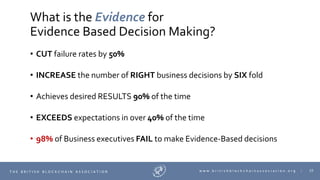
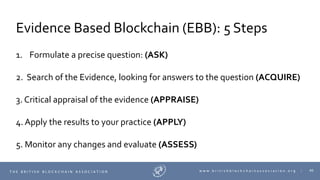
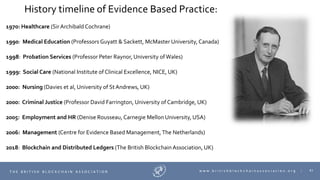
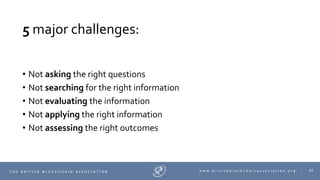
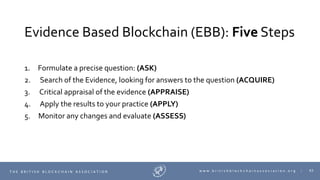
The document discusses the concept of evidence-based blockchain (EBB) and its significance in decision-making processes, emphasizing its potential to improve business outcomes by reducing failure rates and increasing the accuracy of decisions. It outlines a structured five-step process for adopting EBB, including formulating questions, searching for evidence, appraising that evidence, applying results, and assessing changes. Additionally, the document provides a historical perspective on the evolution of evidence-based practices across various fields leading up to its application in blockchain technology.

































![73T H E B R I T I S H B L O C K C H A I N A S S O C I A T I O N w w w . b r i t i s h b l o c k c h a i n a s s o c i a t i o n . o r g |
Question:
“..Compared to existing traditional database based [C]
infrastructure, does private permissioned blockchain [I] of
Hyperledger Fabric save time, reduce costs, improve food
integrity, and increase consumer satisfaction [O] in the tracking of
seafood [P] via the supply chain, based in India..”?](https://image.slidesharecdn.com/0301nassemisc2020keynote-200311201841/85/Keynote-Naseem-Naqvi-73-320.jpg)