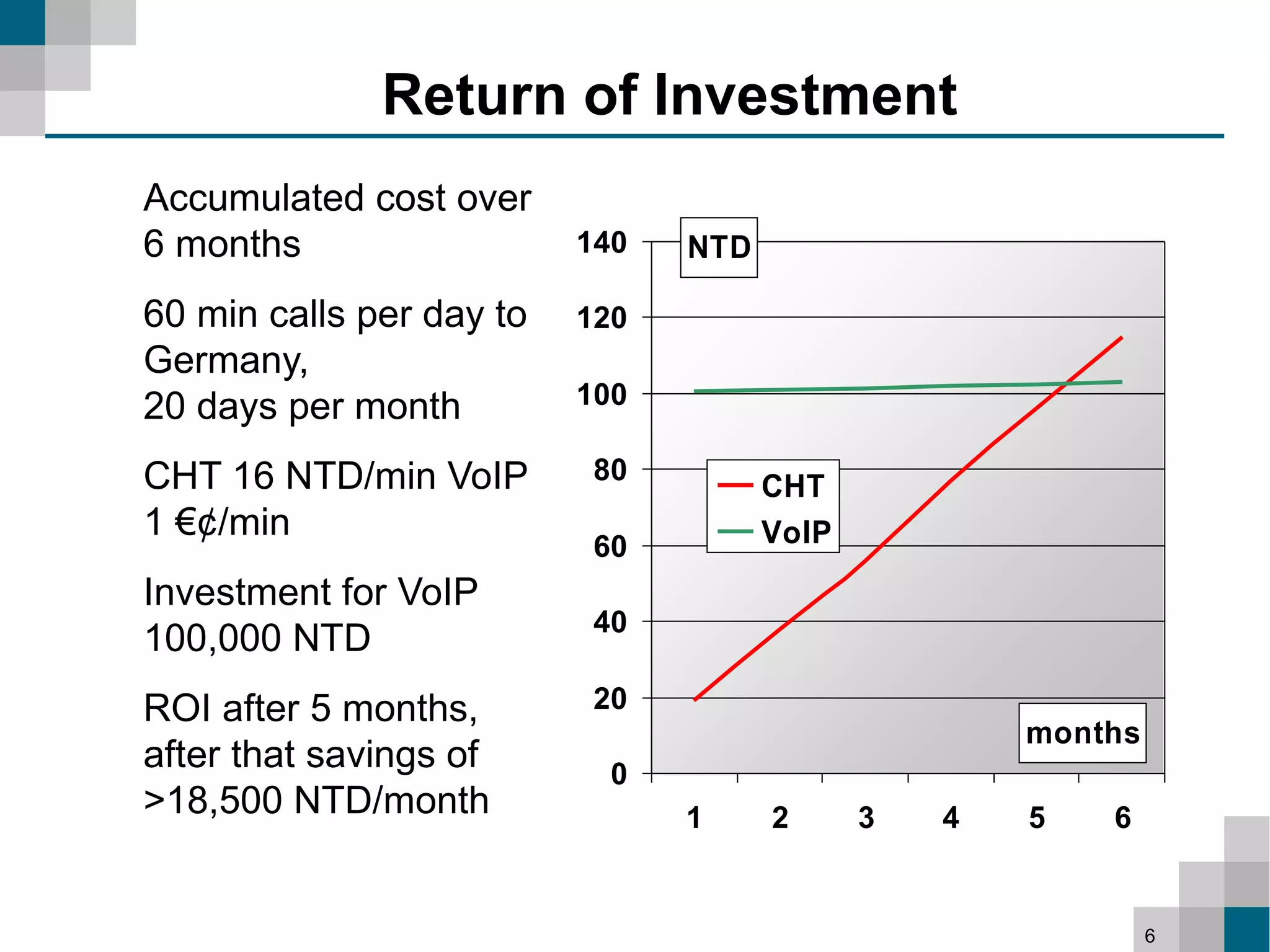
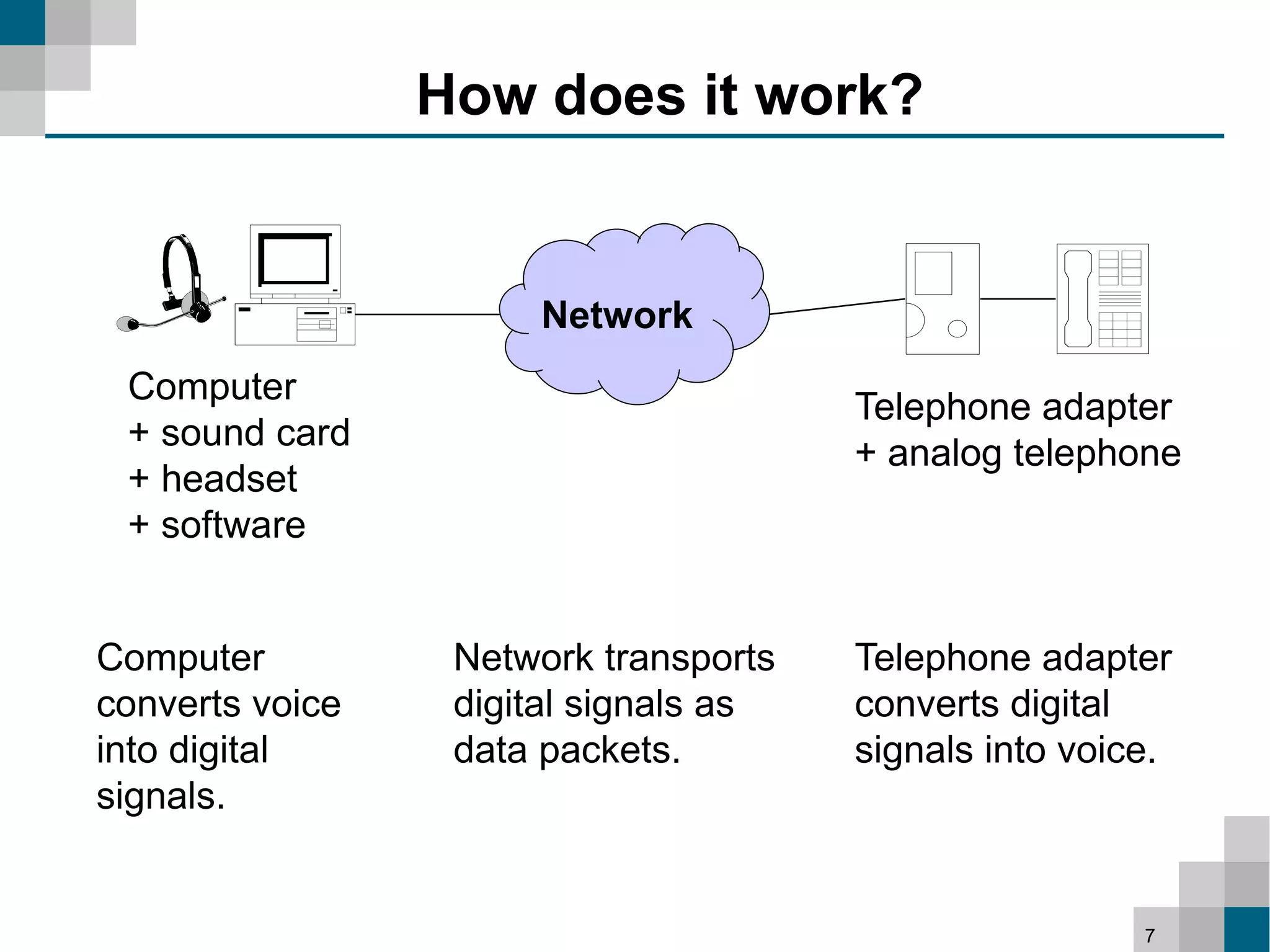
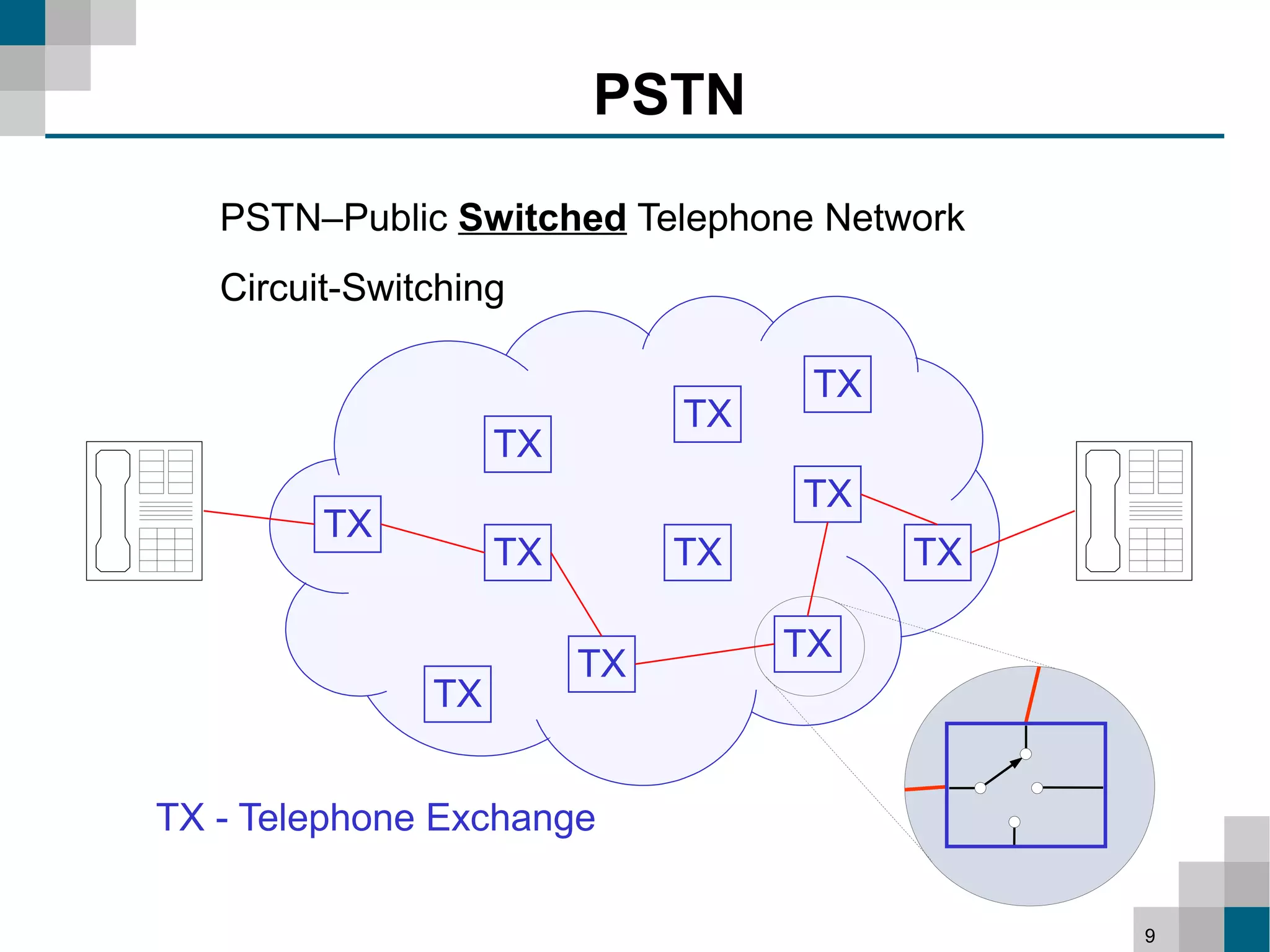
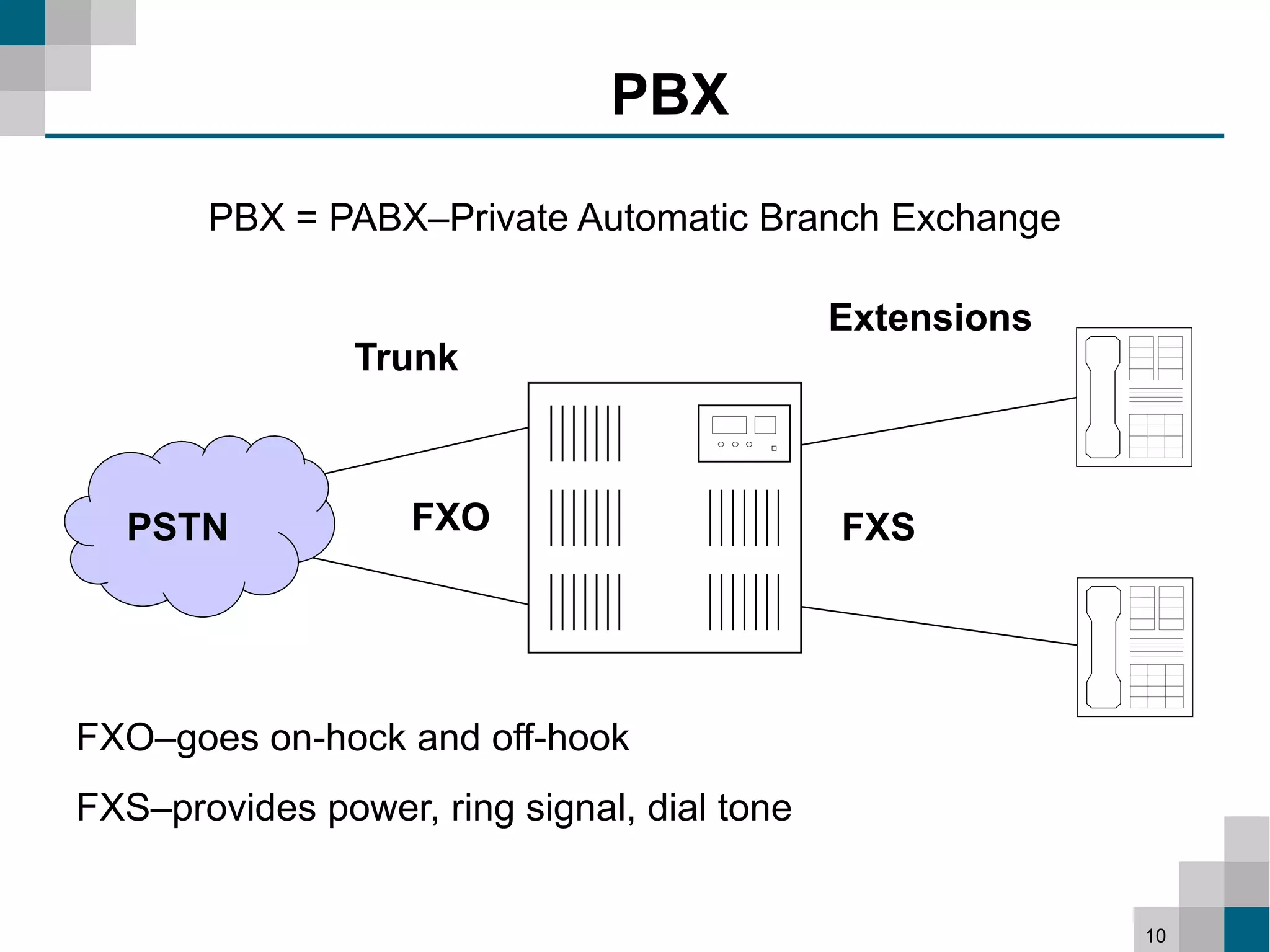
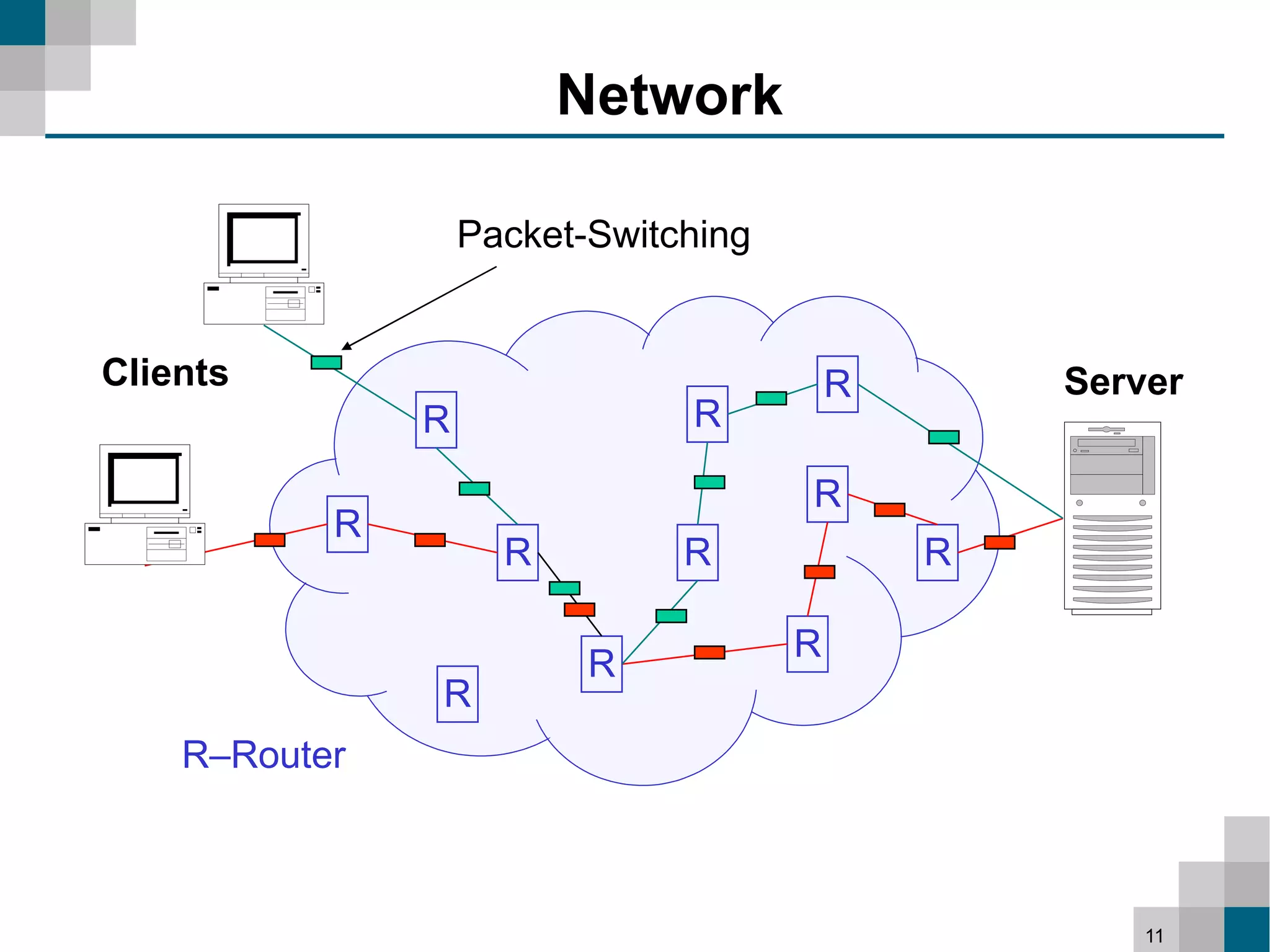
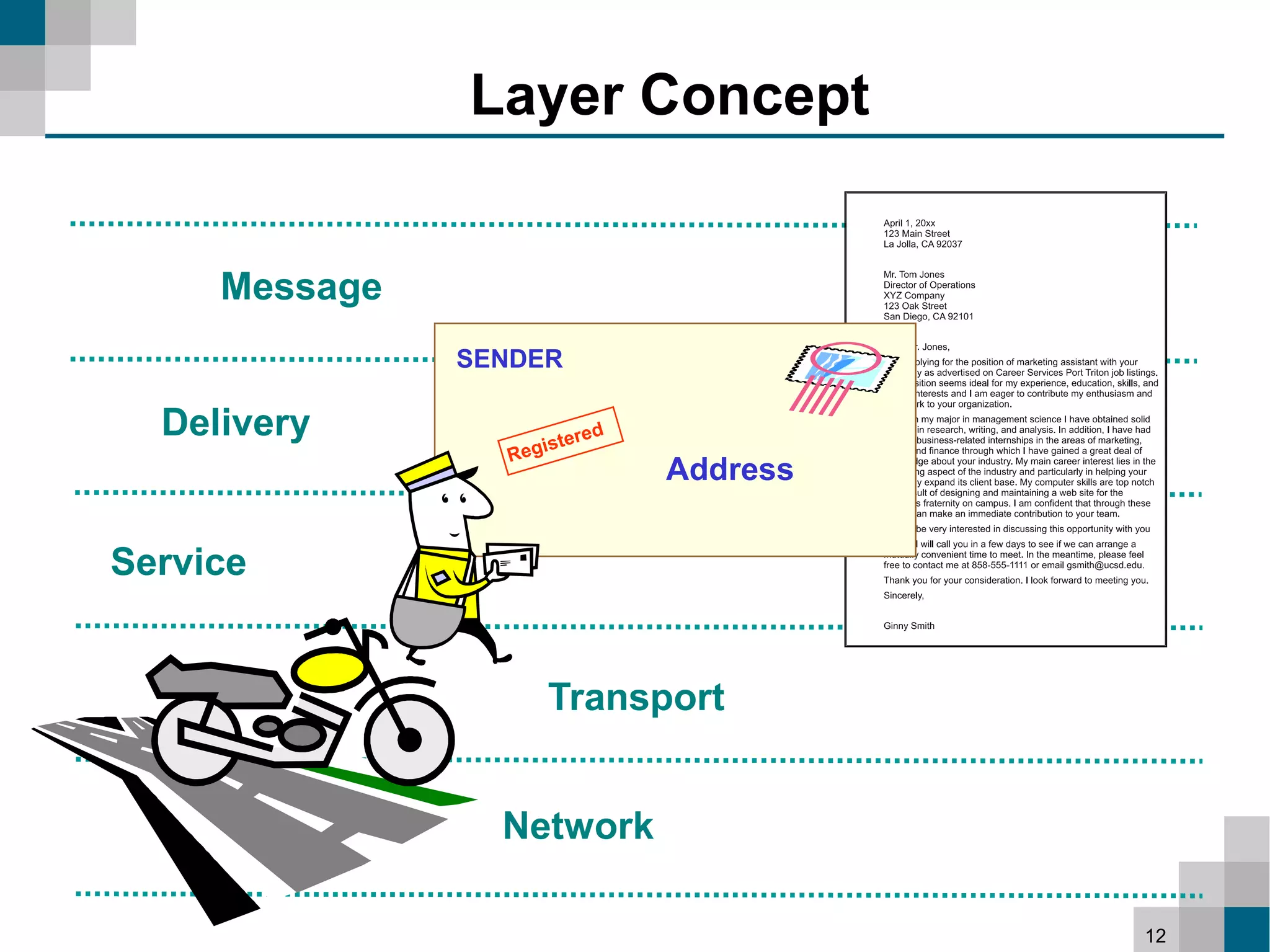
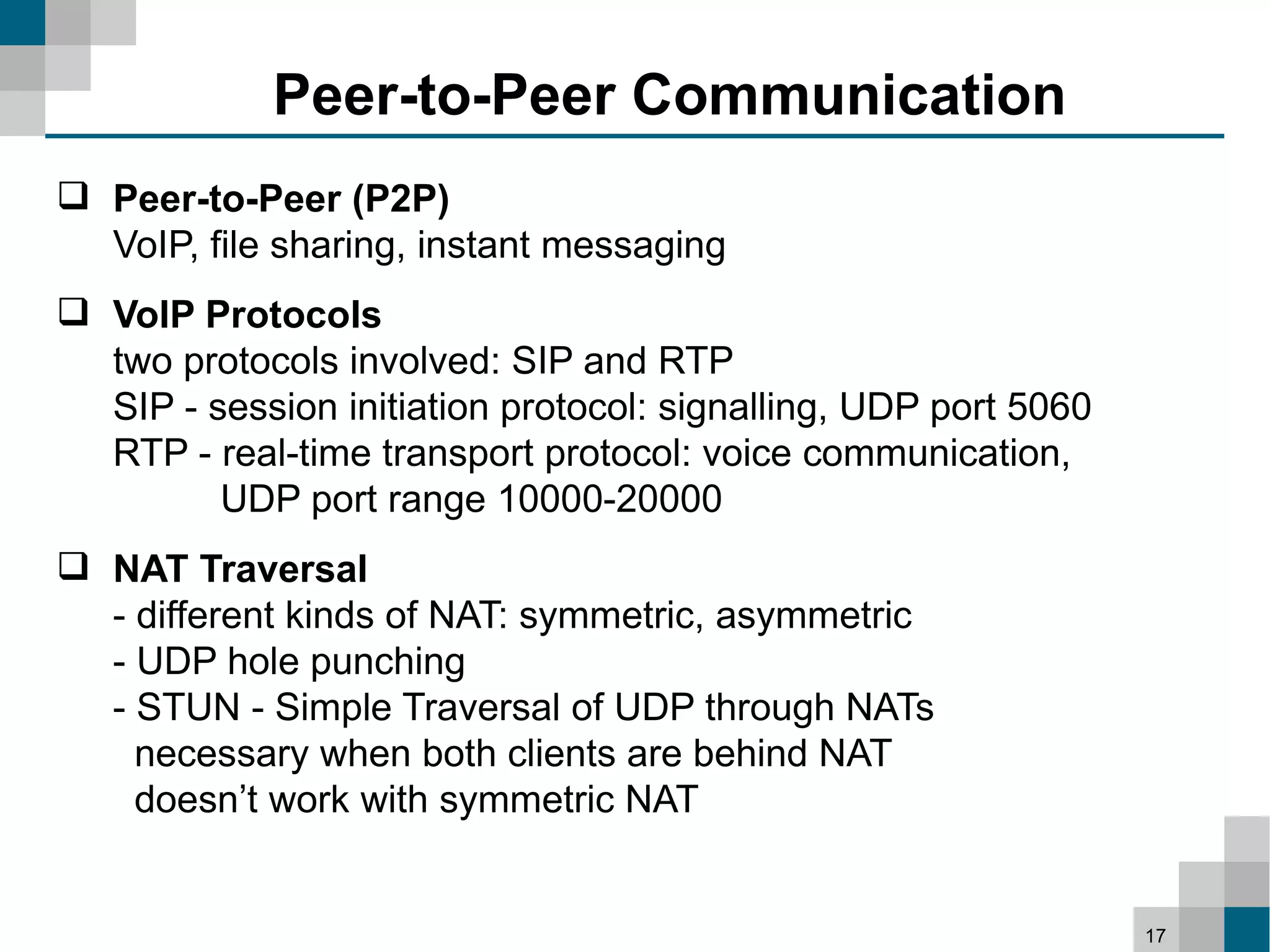
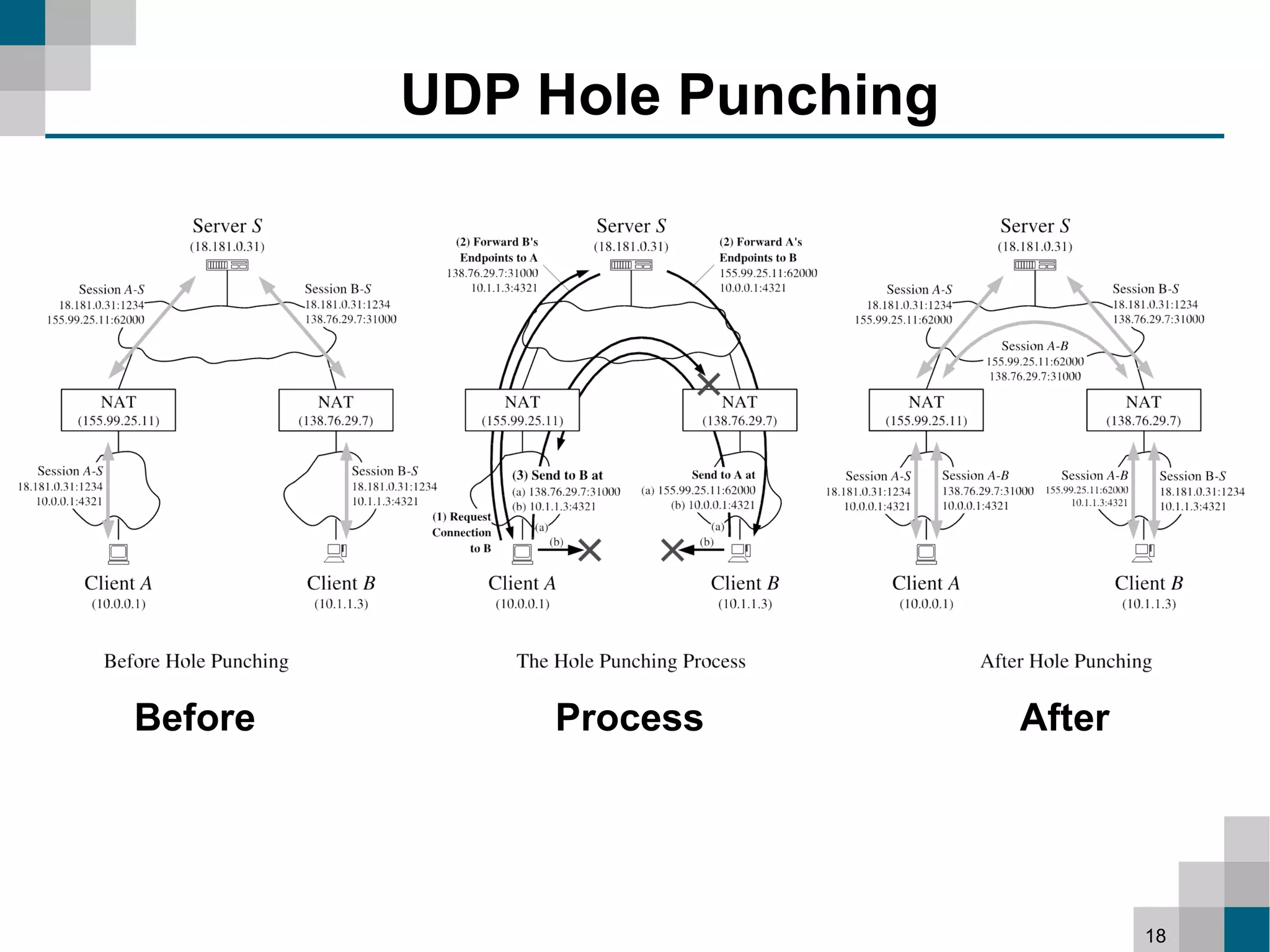
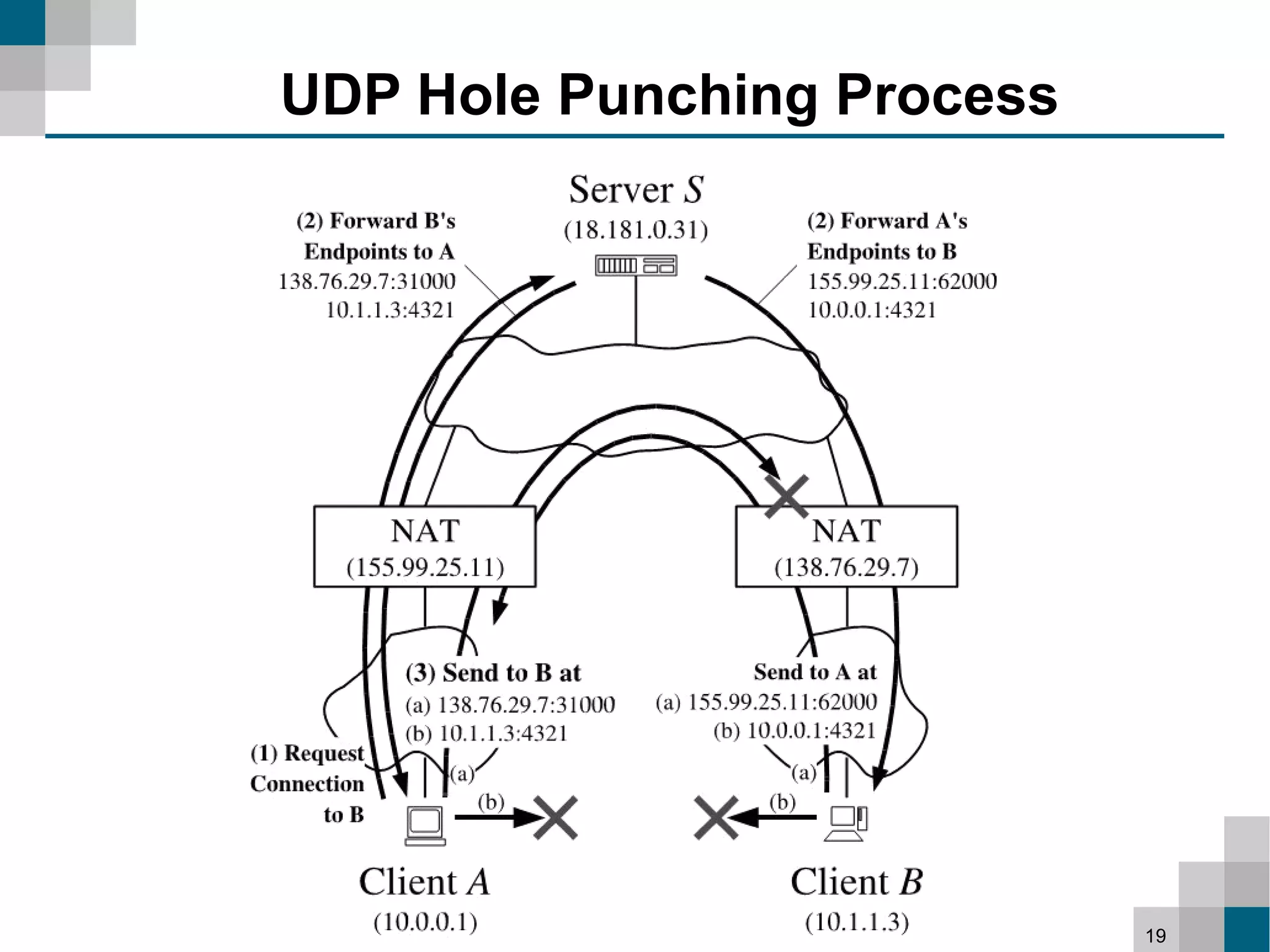
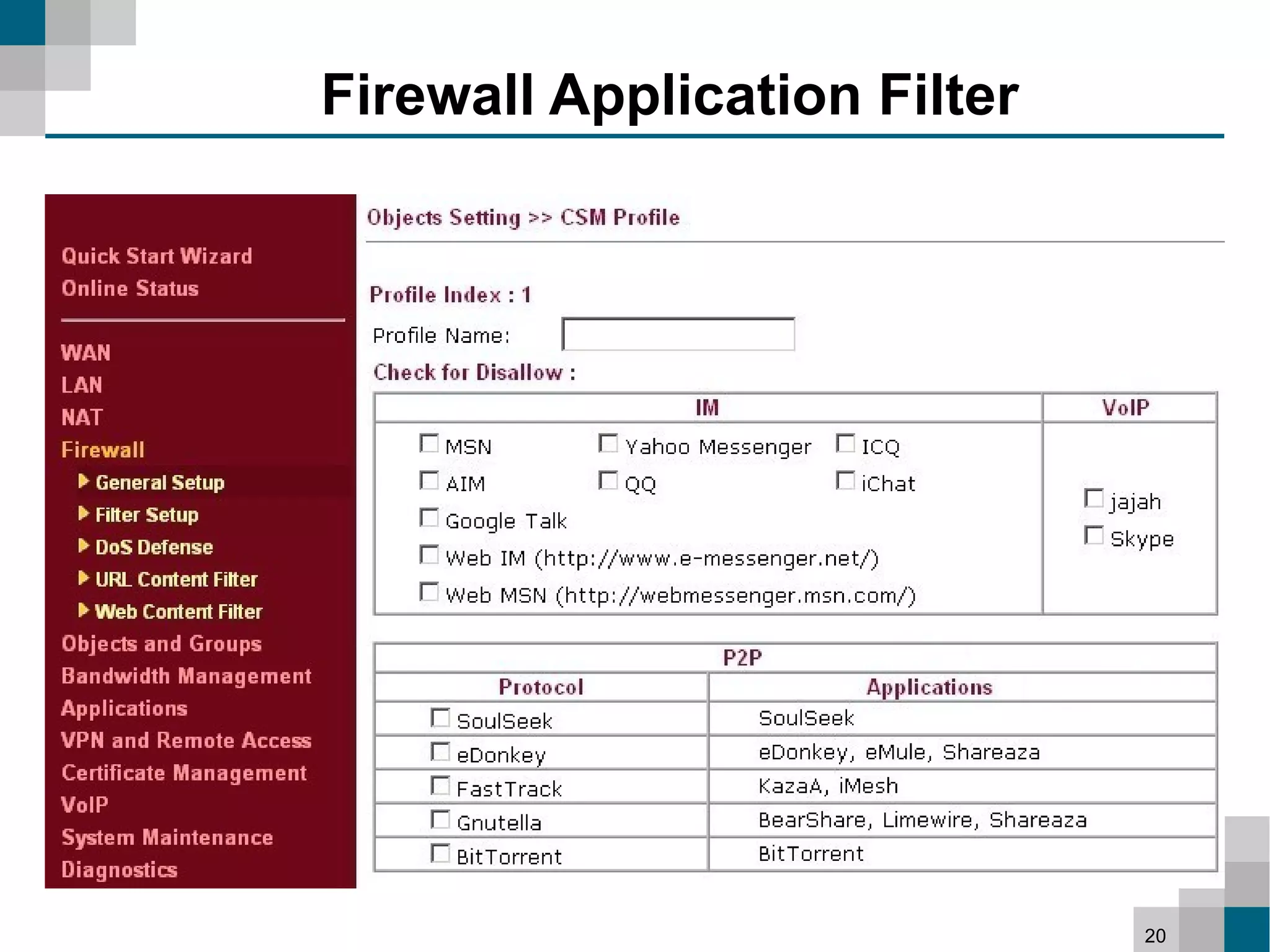
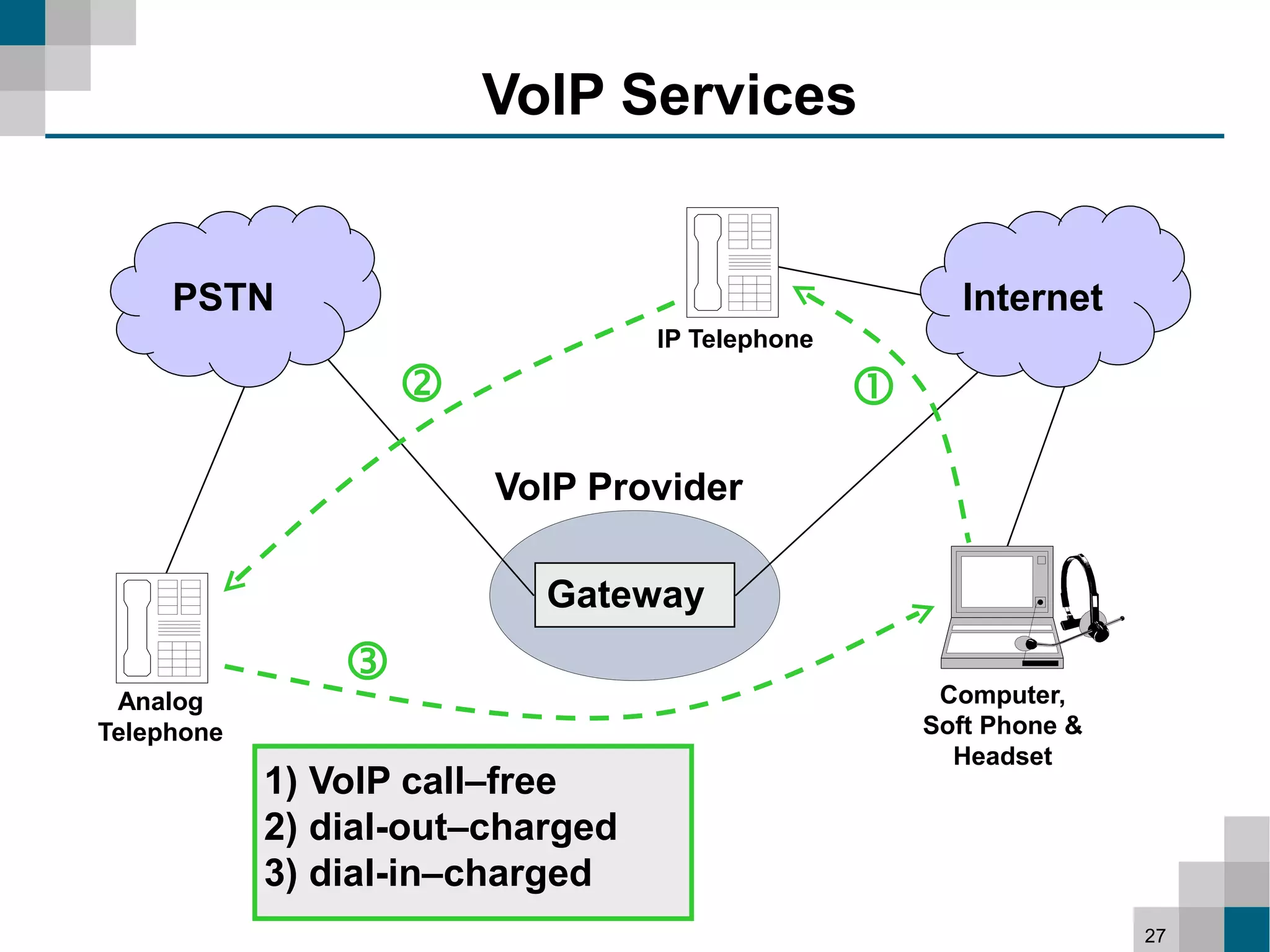
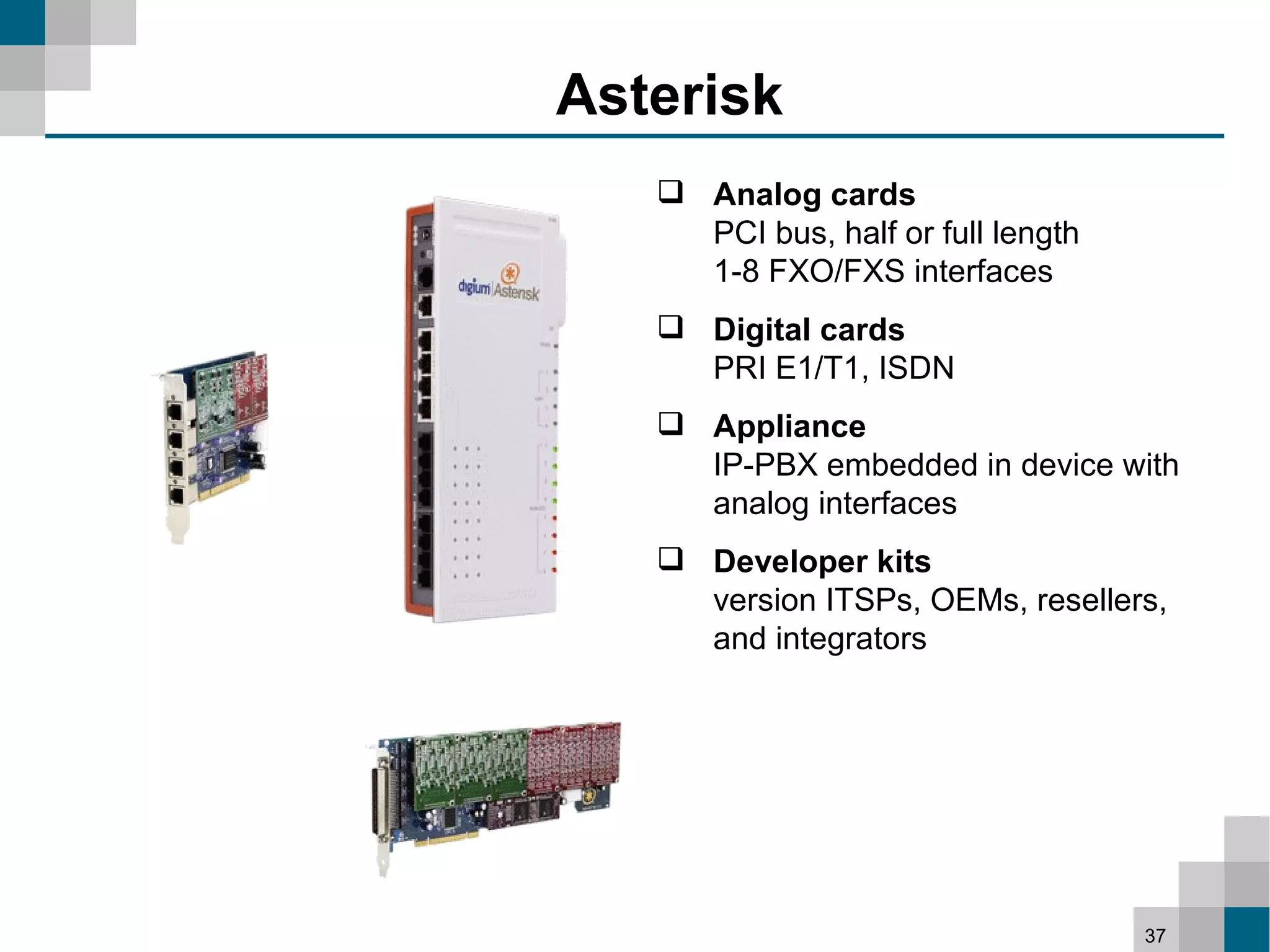
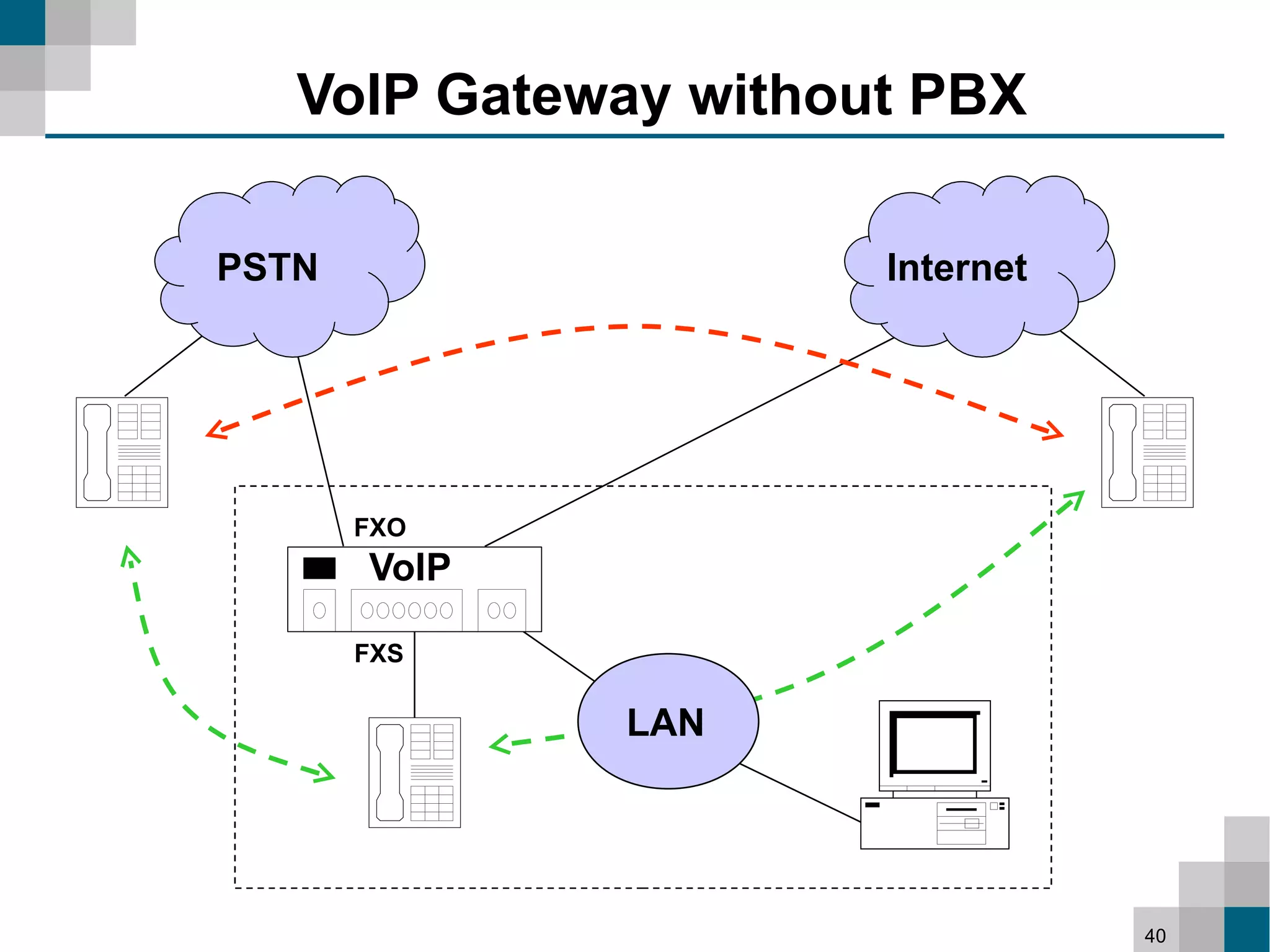
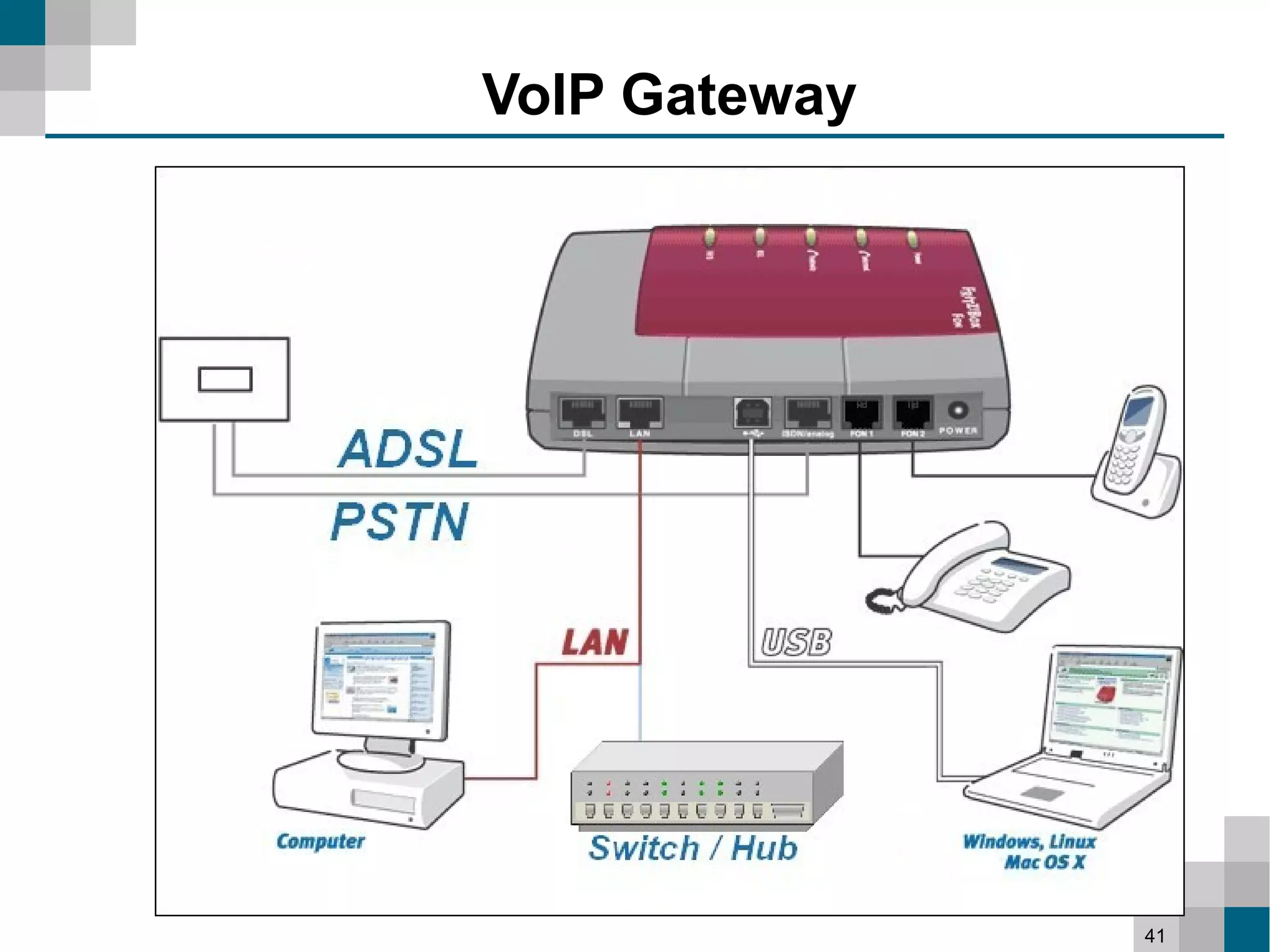
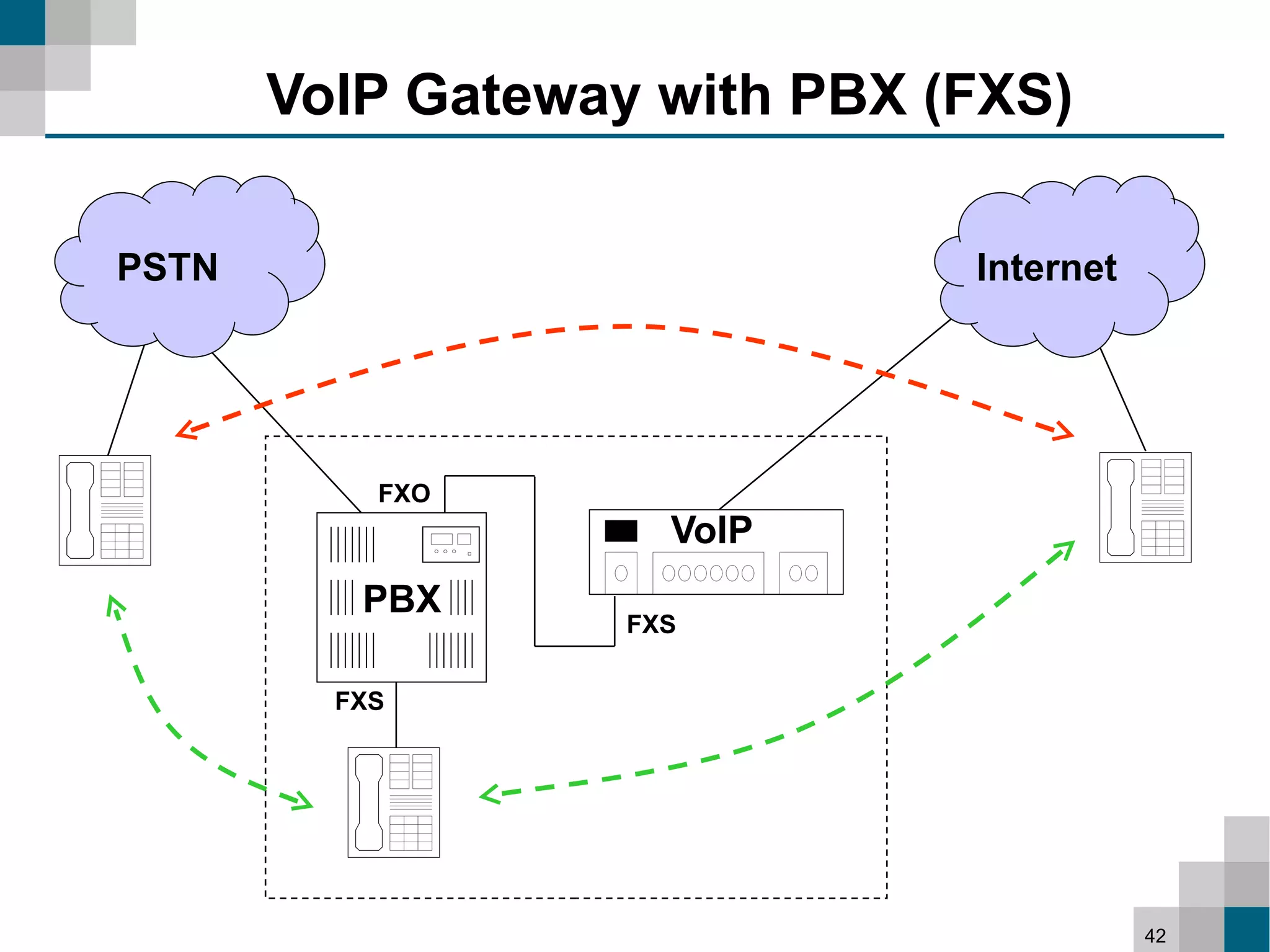
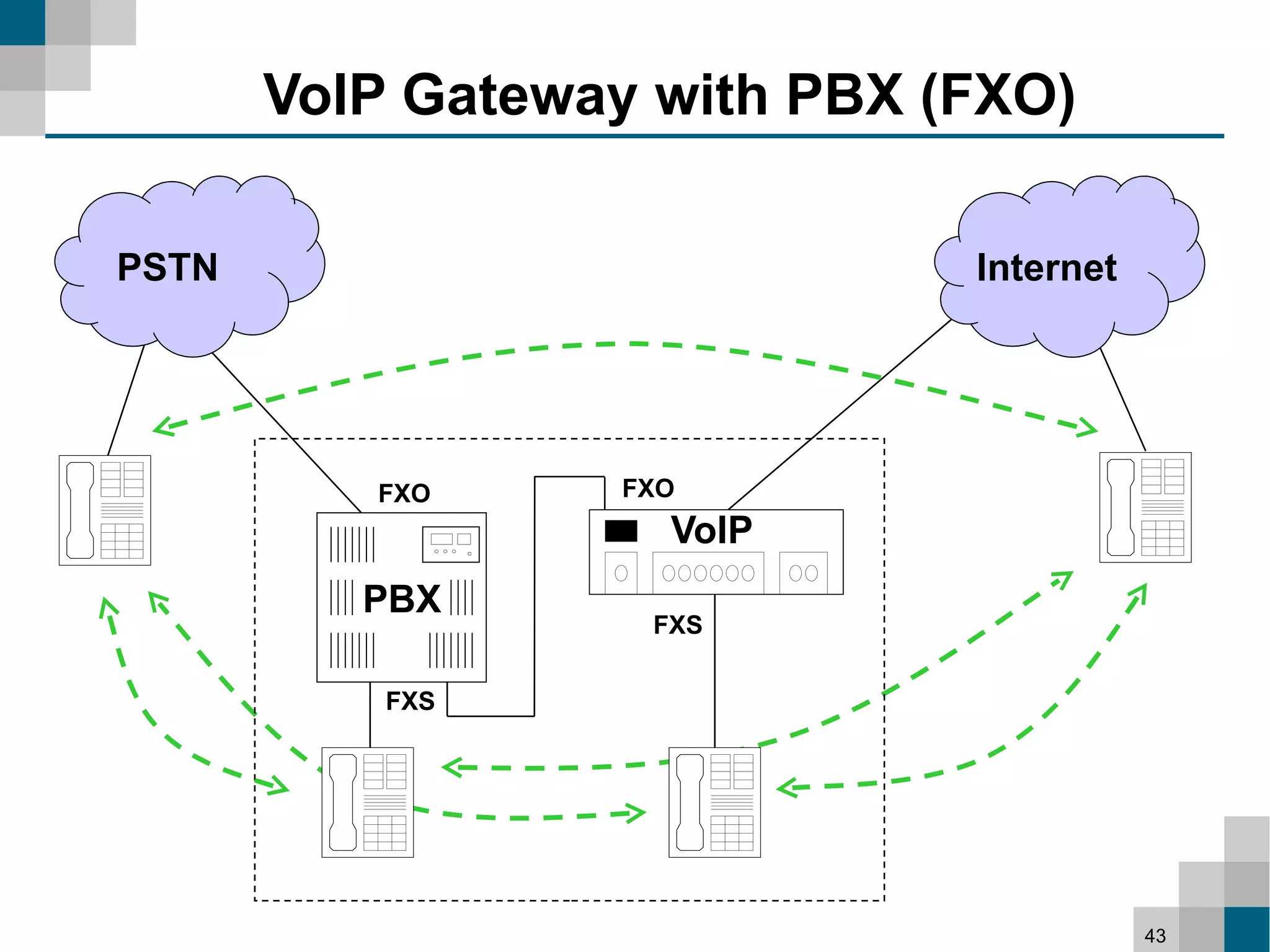
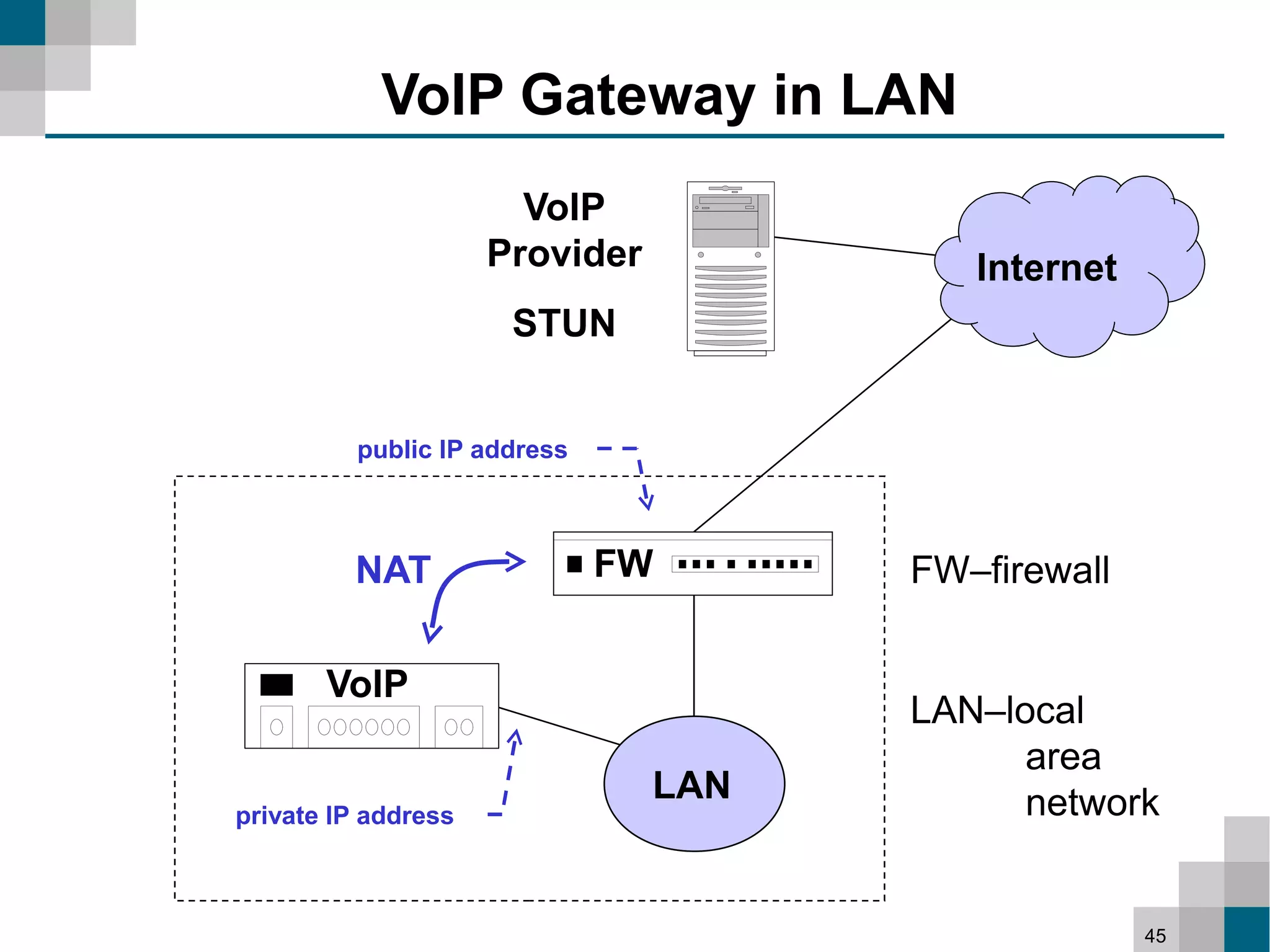
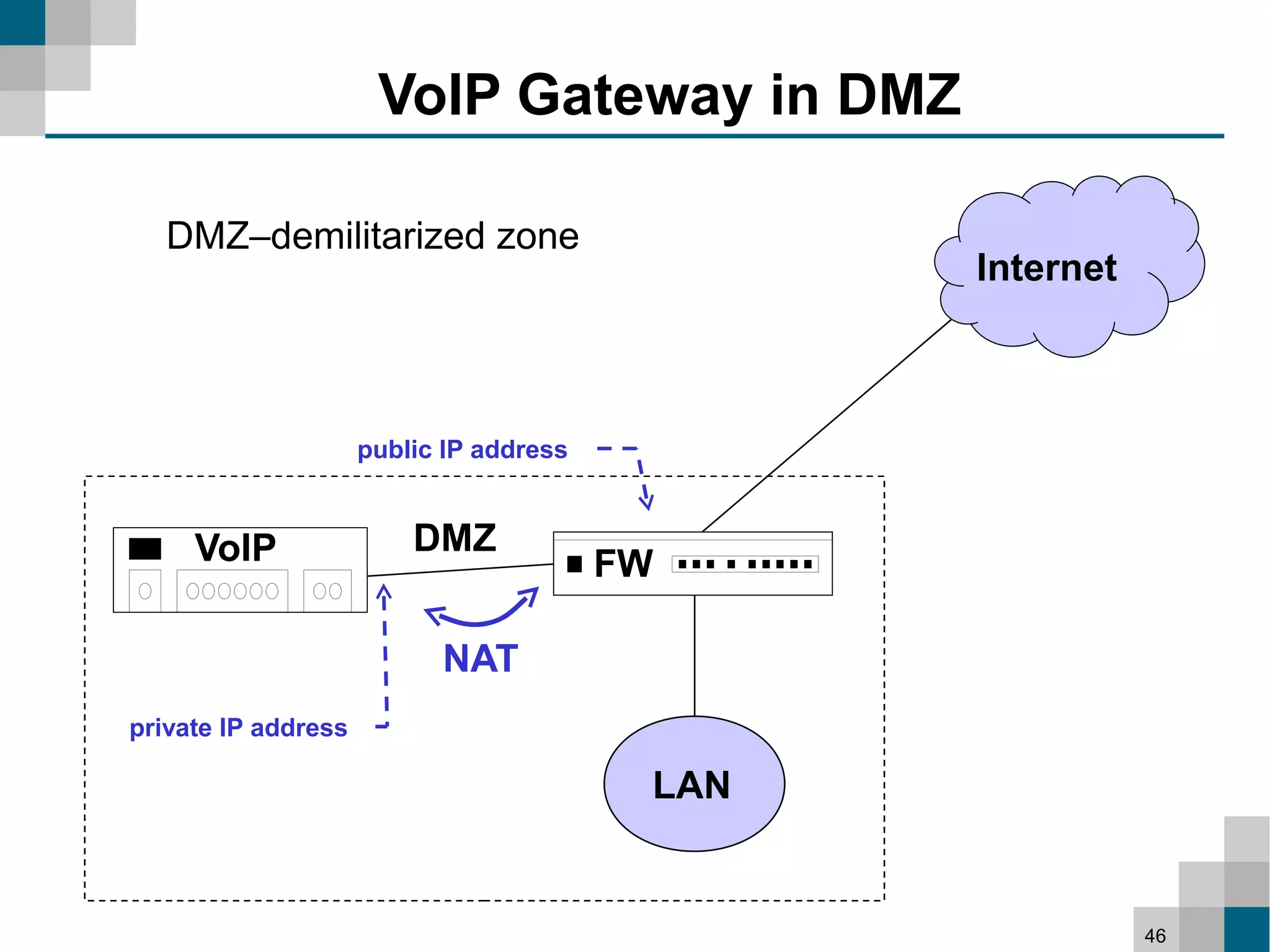
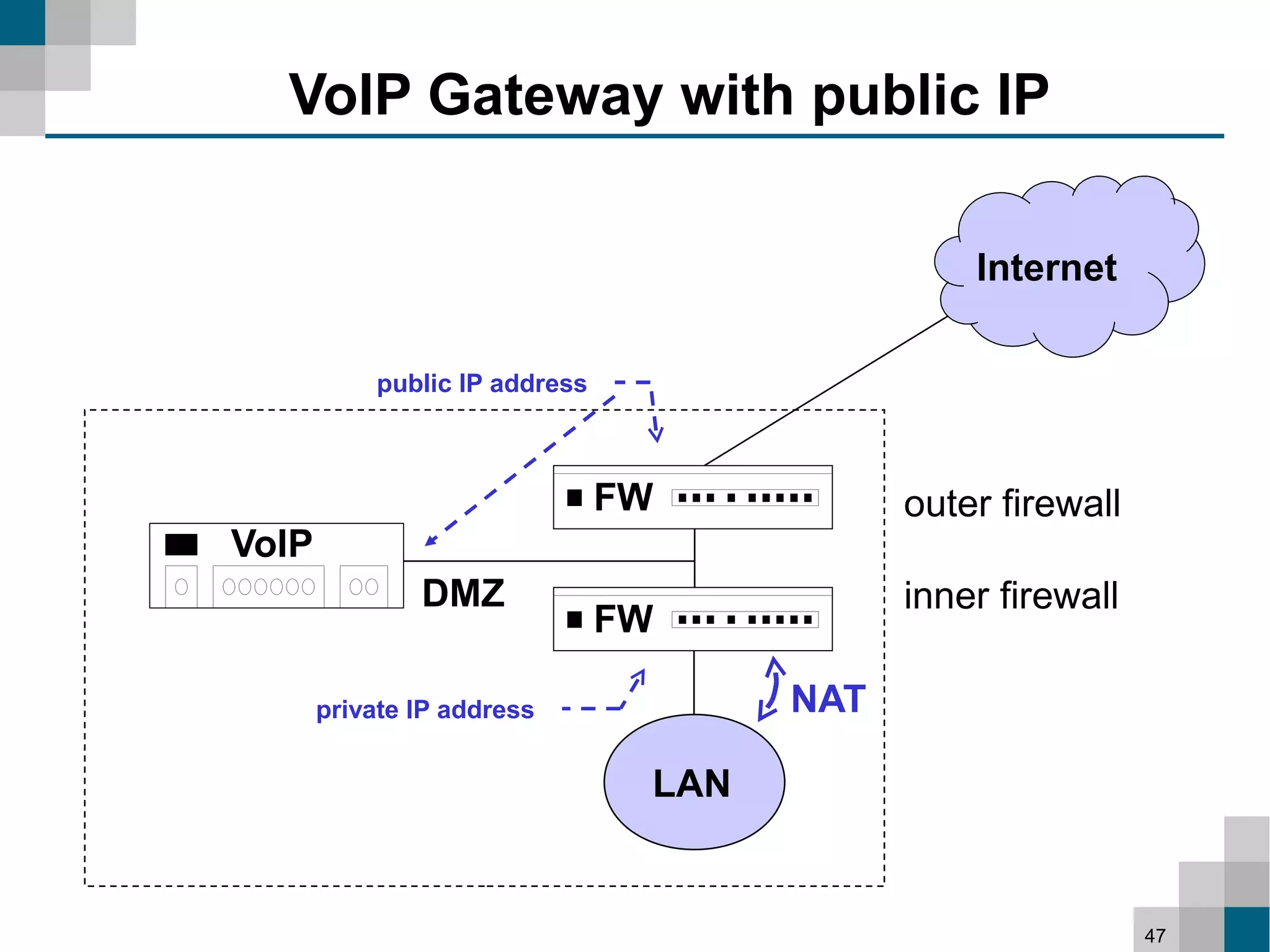
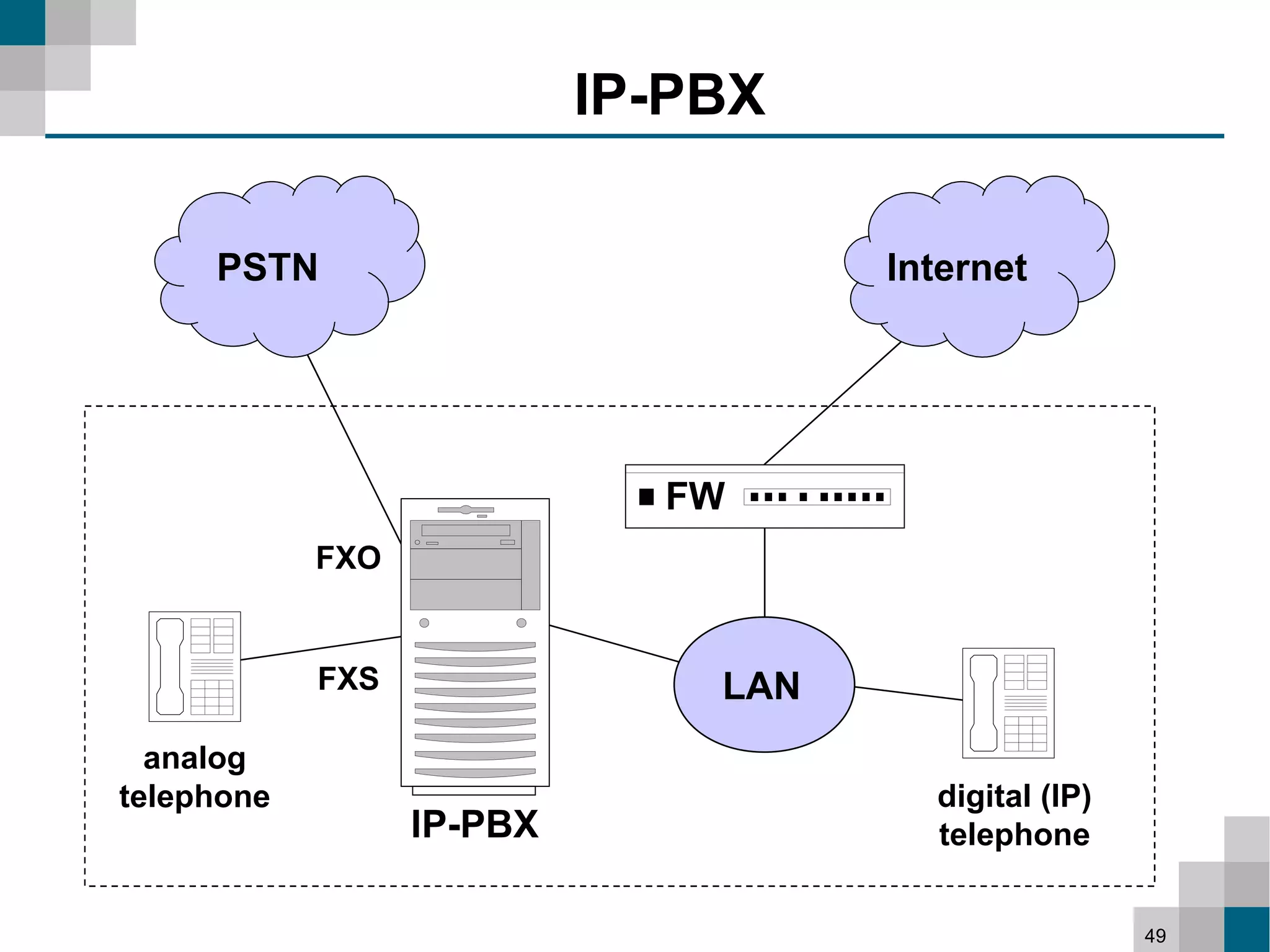
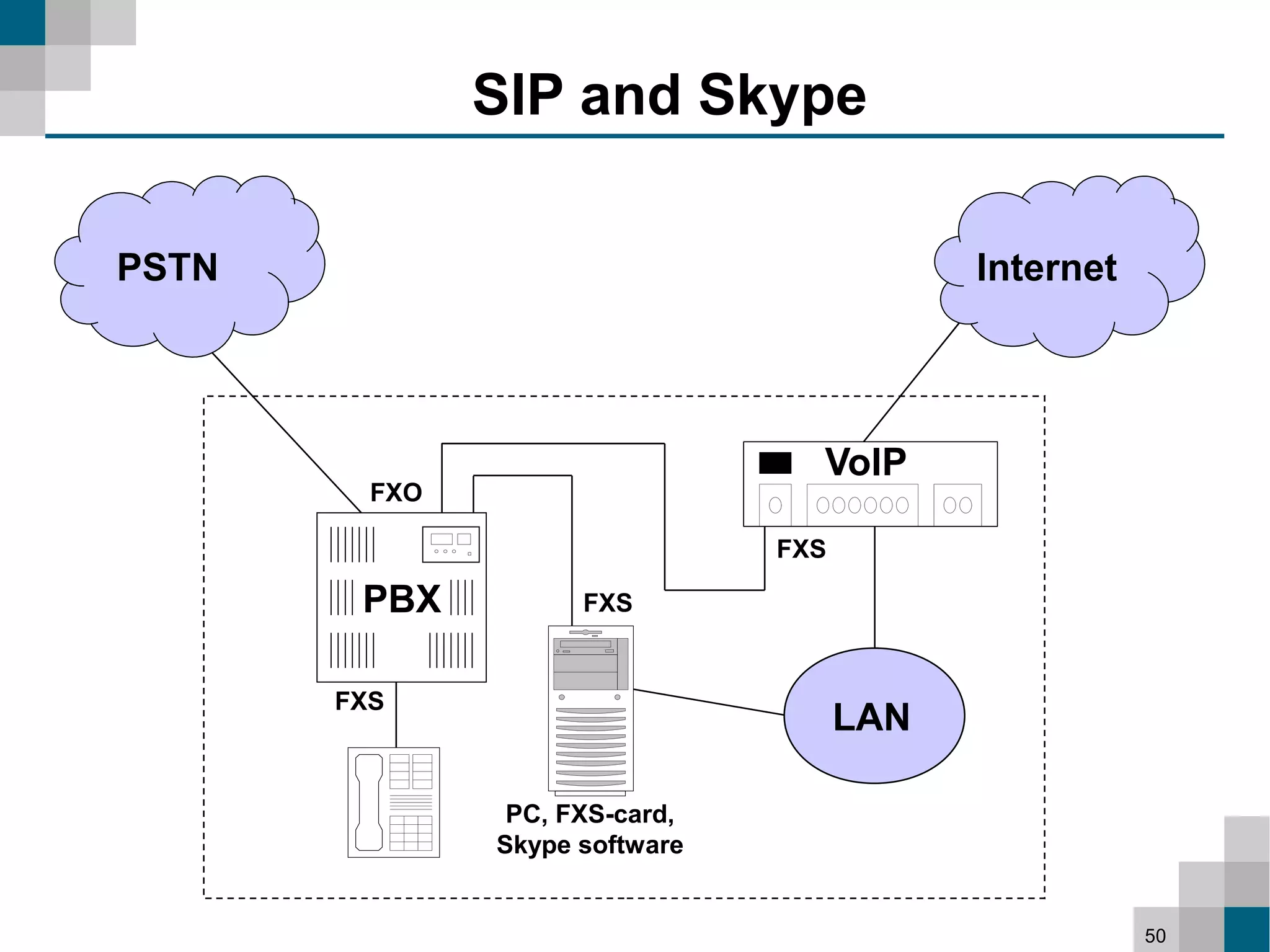
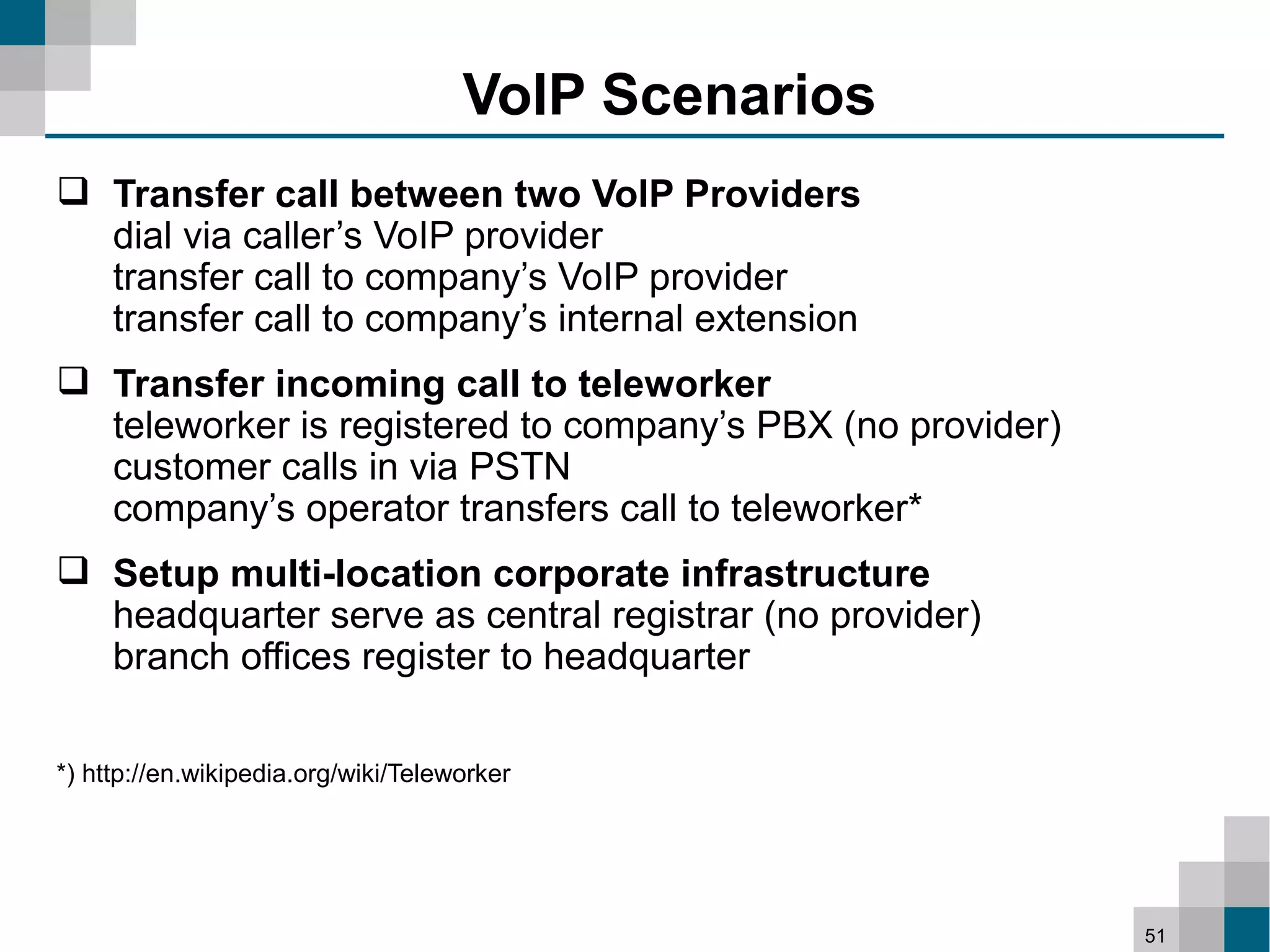
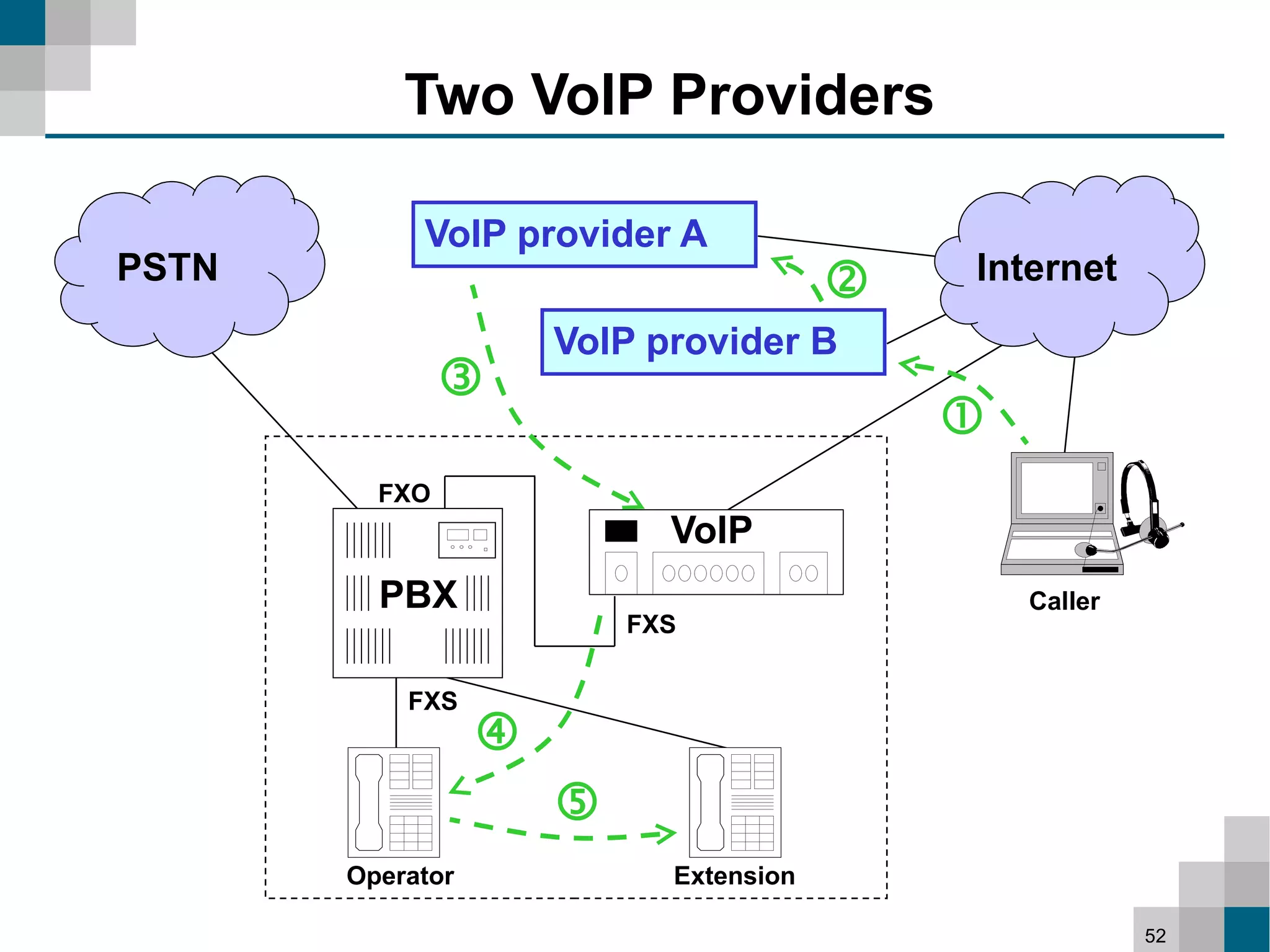
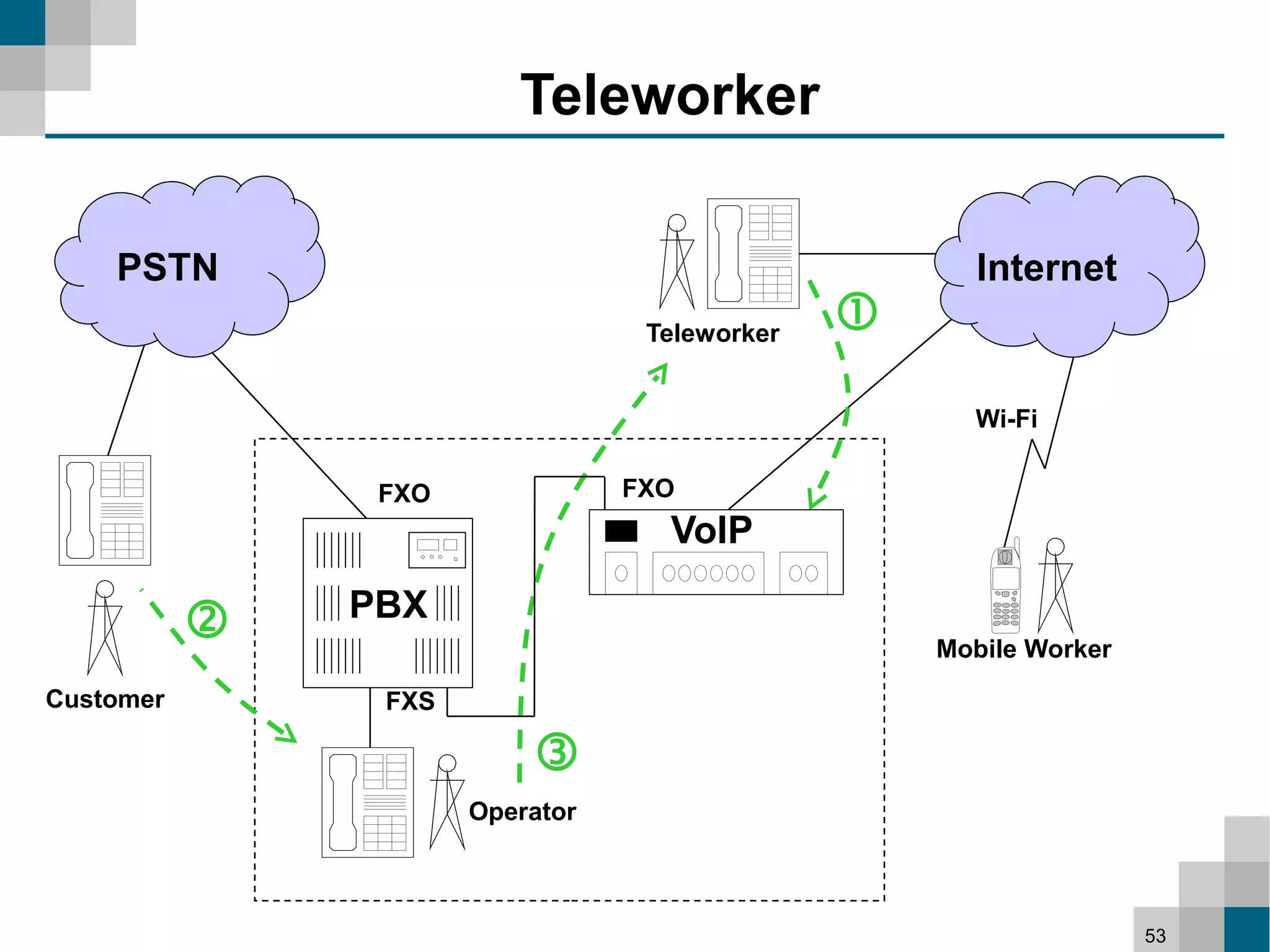
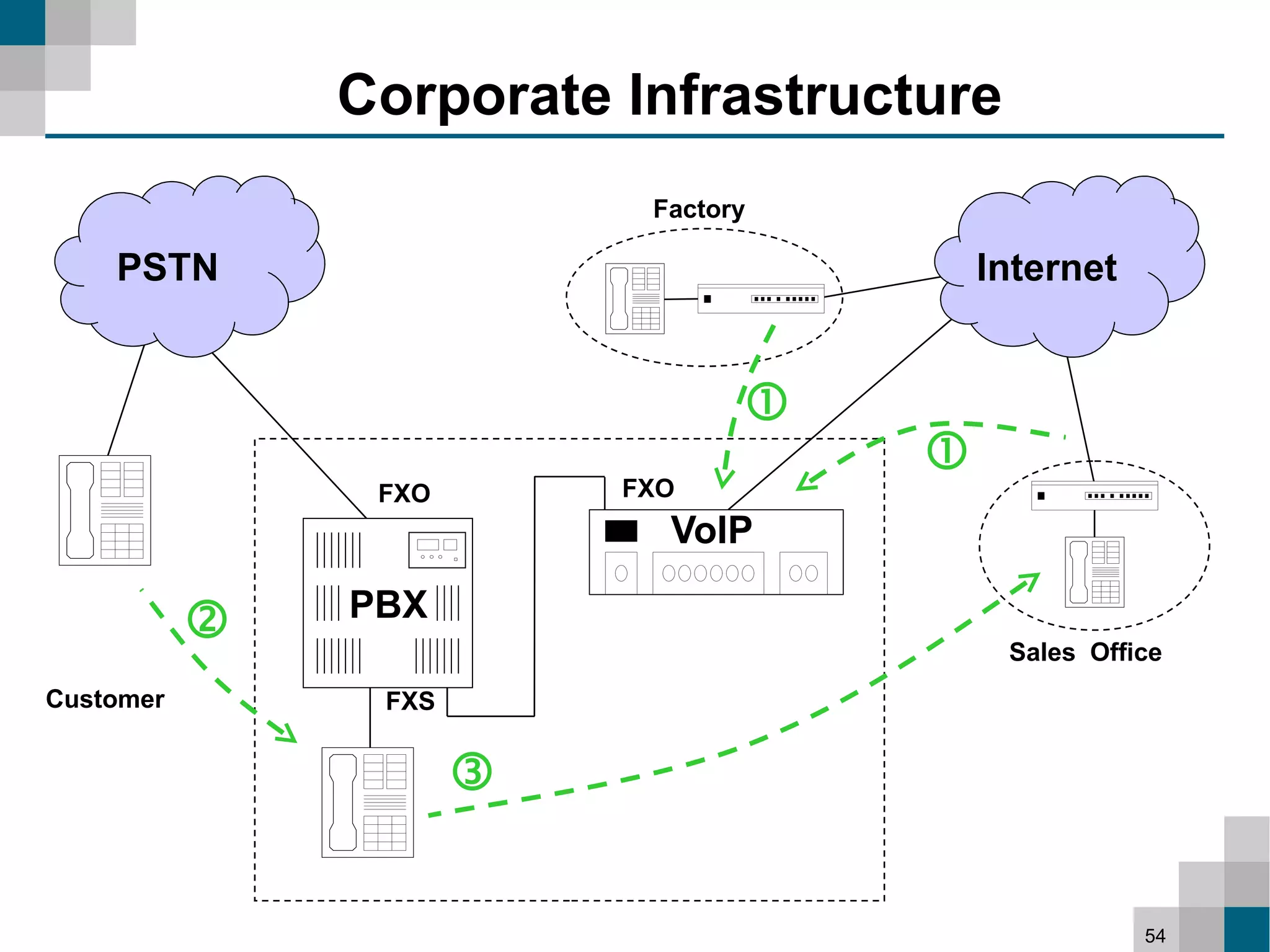
This document provides an overview of efficient telecommunication infrastructure using Internet telephony (VoIP). It discusses basics of telephony and networking, protocols like SIP and RTP, VoIP hardware, service providers, and examples of integrating VoIP into networks and PBX systems. Skype and issues with it are also covered. The presentation aims to explain how VoIP works and scenarios for implementing efficient VoIP solutions.