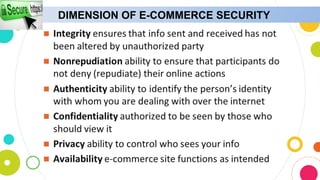
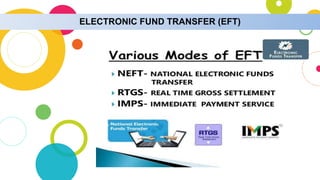
The document provides an overview of e-commerce security, highlighting various threats such as data misuse, hacking, and denial of service, along with potential countermeasures. It outlines essential protective measures for e-commerce sites, including secure platforms, encryption, fraud monitoring, and strong password policies. Additionally, the document discusses different e-commerce payment methods like credit cards, digital cash, and electronic fund transfers.