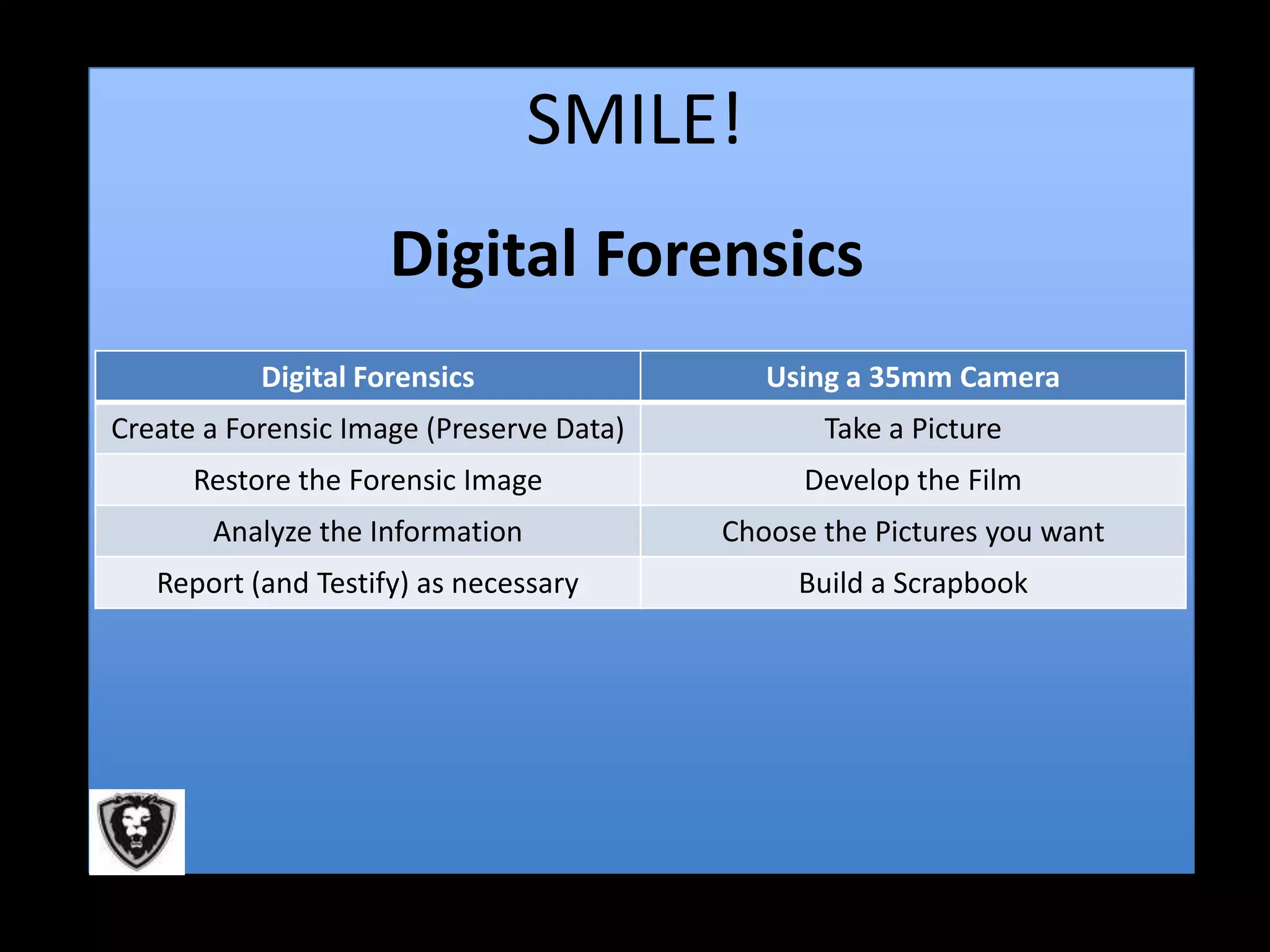
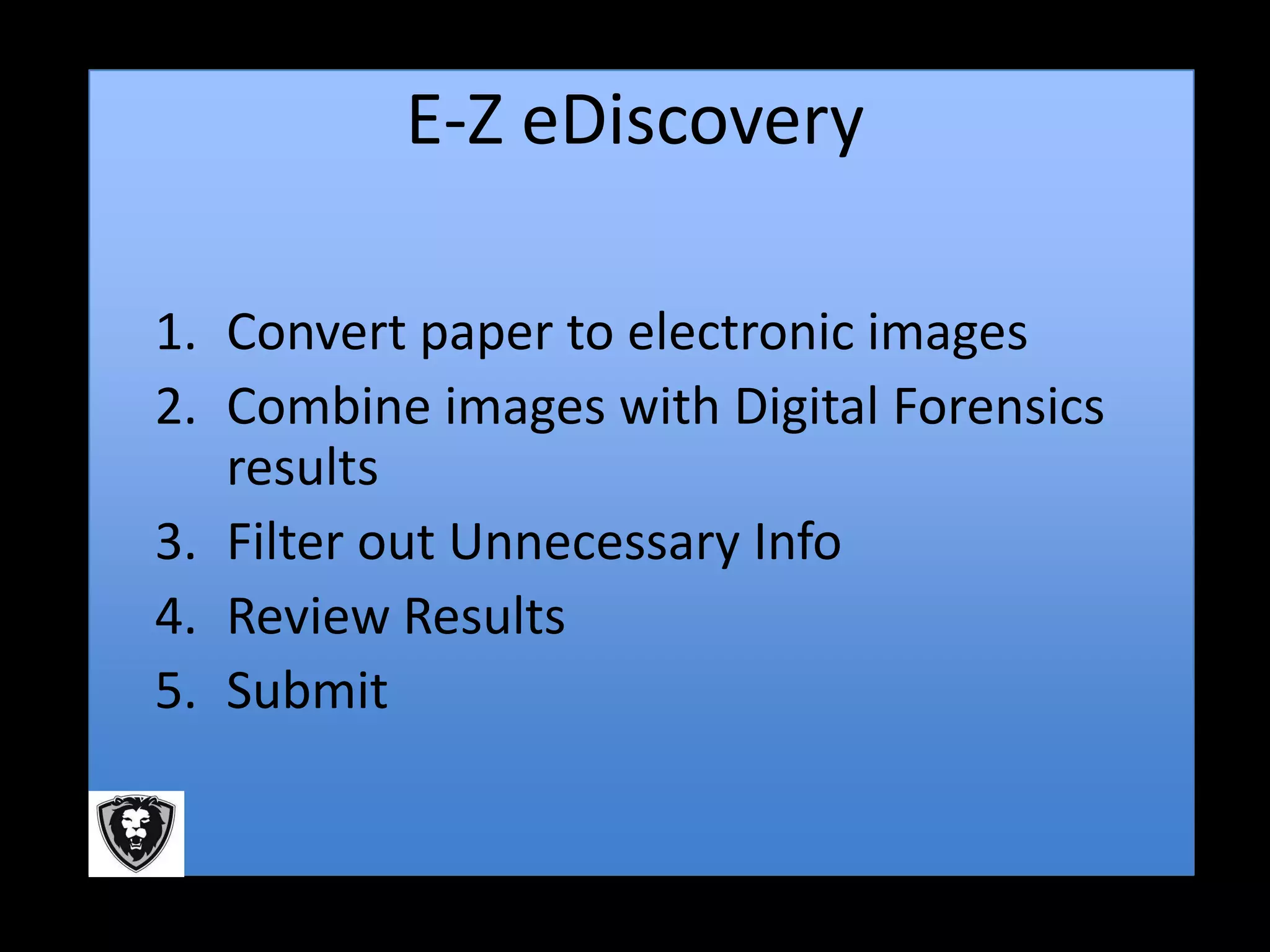
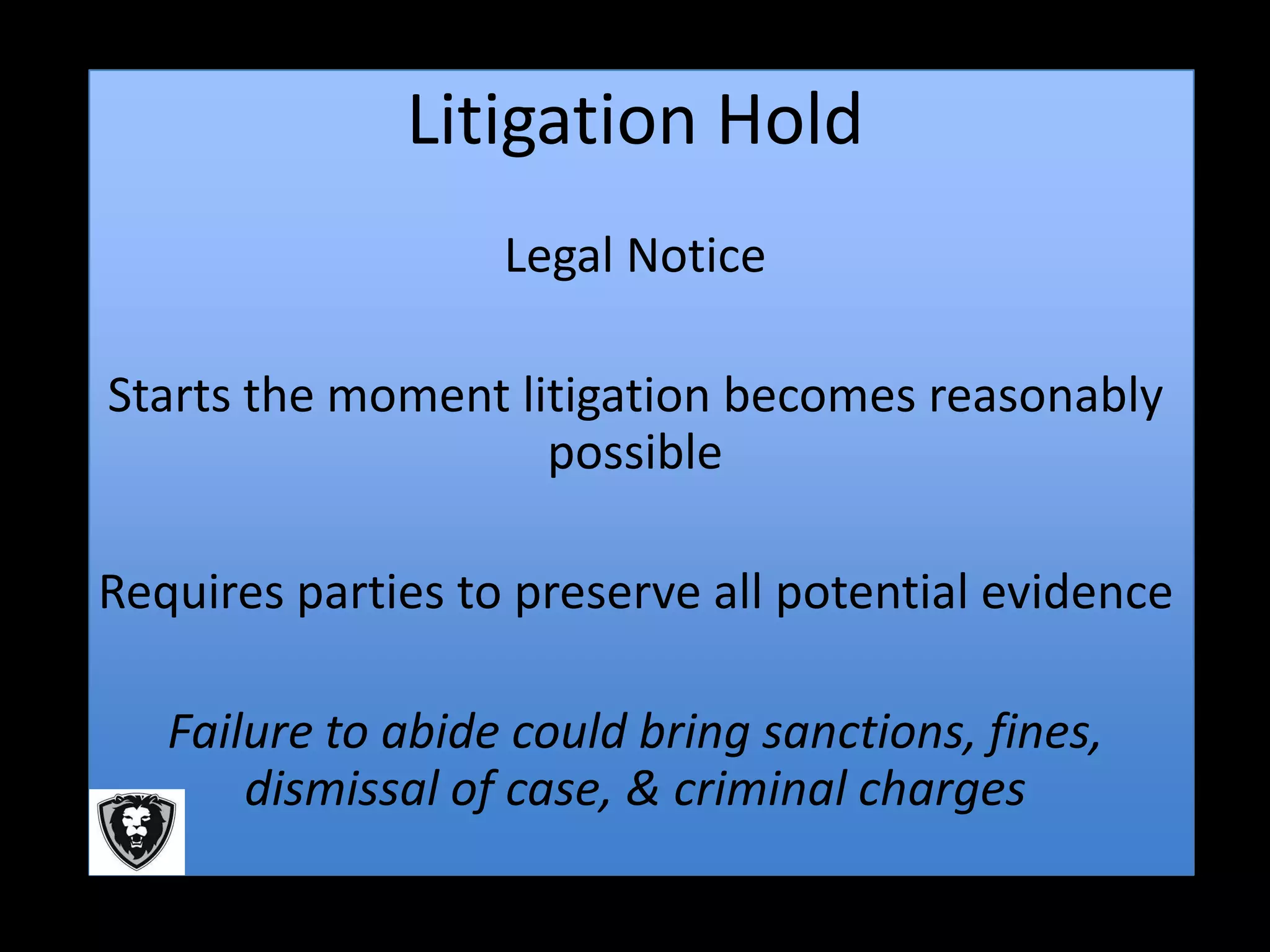
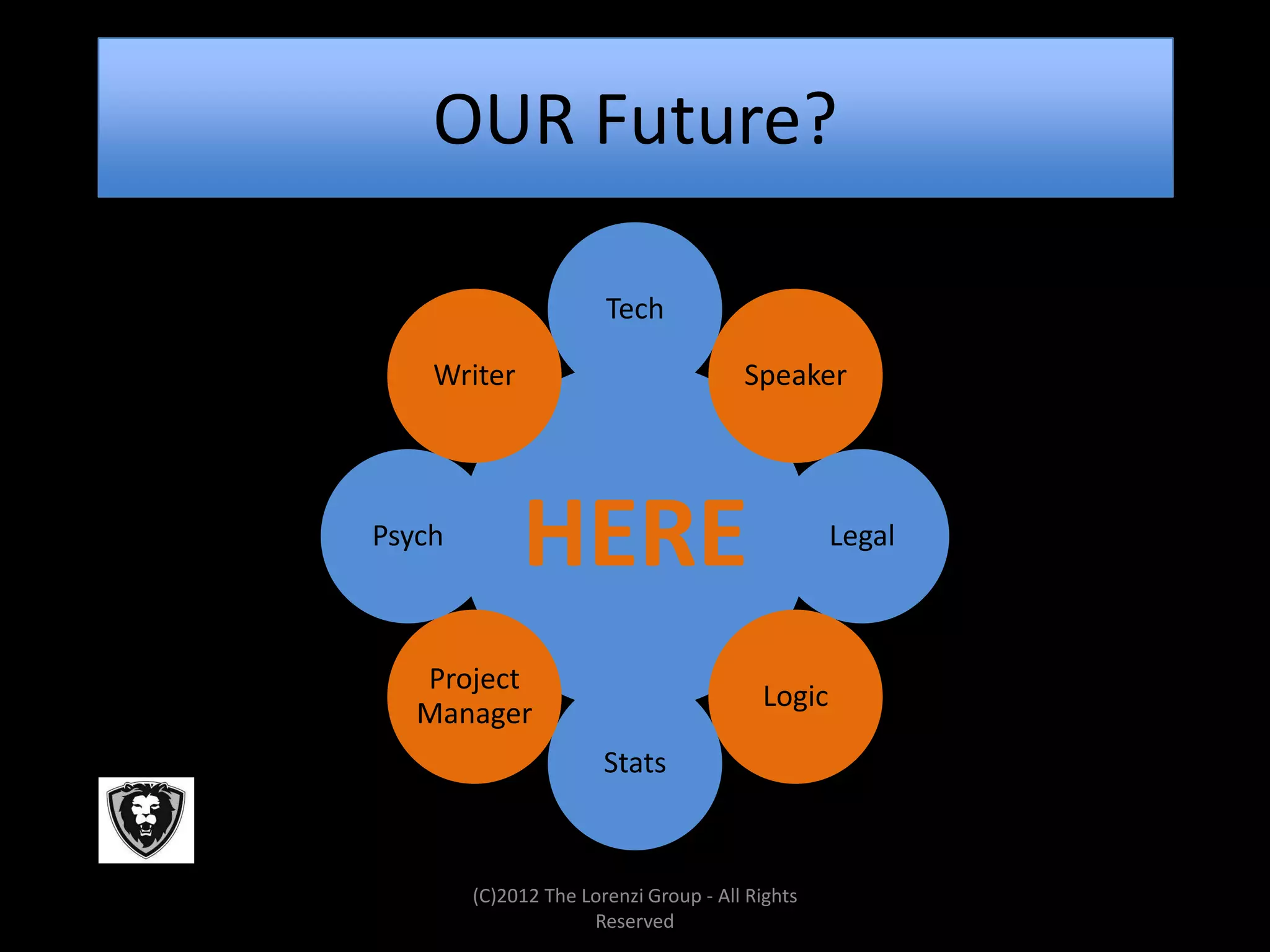
The document discusses the evolving landscape of data security, emphasizing that organizations must shift focus from traditional security measures to protecting data proactively. It highlights the importance of digital forensics and eDiscovery in legal contexts while warning about the risks posed by employees and vendors. Additionally, it addresses the implications of government regulations and the necessity of compliance audits in safeguarding information.