The document outlines the creation of a Java project for a lab assignment where users are instructed to build a file writer and reader for different file types (random, binary, and text). It provides detailed instructions on implementing classes for writing and reading files, handling keyboard inputs, and creating a package structure for organizing the code. Additionally, it specifies how to submit the project by zipping the files and emailing them.

![Your job is to complete these three methods.
11)I’ve included the source for the program to read text files
(TextReader.java) and display its contents. It uses two files, so
make sure that your modified TextRead program works with it.
Be careful if you cut and paste this program. The string variable
spaces doesn't cut and paste correctly. You will have to correct
it appropriately. Do not make any other changes to this
program.
12)Answer the synthesis questions in an rtf or doc file
(answers.rtf or answers.doc). Type your name and the lab
number on this file and include the questions with the answers.
13)Zip your Eclipse project along with the synthesis answers
and email to [email protected]
// This program reads the SeqText.dat and seqText2.dat files.
// These files were created by TextWriter.
// They are in sequential text format.
// They contain records of name, age, and salary.
import java.io.*;
import java.text.*;
import cs258.*;
public class TextReader
{ public static final int NAME_SIZE=30;
public static void main(String args[])
{ String name;
int age;
double salary;
if (!new File("seqtext.dat").exists() ||
!new File("seqtext2.dat").exists())](https://image.slidesharecdn.com/description1createalab2folderforthisproject2-221114184932-4a32f6e0/85/Description-1-Create-a-Lab2-folder-for-this-project2-docx-3-320.jpg)

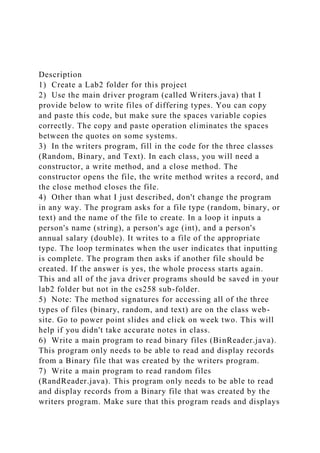
![money.format(salary) );
}
} while (!file1.endOfFile()||!file2.endOfFile());
file1.close();
file2.close();
System.out.println("nTextReader complete; data printed");
}
}
// This program writes different types of files.
// Random, Binary, and Text.
// Created 3/29/2004 for the lab 2 cs258 project.
import java.io.*;
import java.security.*;
public class Writers
{ private final static int RECORDSIZE = 128;
private final static int NAME_SIZE = 30;
private final static String spaces = " ";
// Keyboard input stream.
private final static BufferedReader in =
new BufferedReader(new InputStreamReader(System.in));
public static void main(String args[])
{
// File related variables variables.
Writer out = null;
String fileType = null, fileName = null;
// Data variables.
String name;
int age, recordNumber = 0;
double salary;
String doMore;](https://image.slidesharecdn.com/description1createalab2folderforthisproject2-221114184932-4a32f6e0/85/Description-1-Create-a-Lab2-folder-for-this-project2-docx-5-320.jpg)












