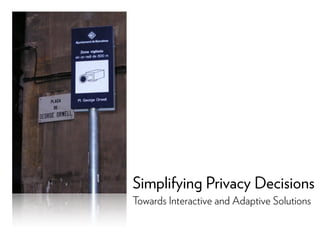
Simplifying Privacy Decisions: Towards Interactive and Adaptive Solutions
- 1. Simplifying Privacy Decisions Towards Interactive and Adaptive Solutions
- 2. INFORMATION AND COMPUTER SCIENCES About me... PhD candidate at UC Irvine Recommender Systems: - Choice overload - Adaptive preference elicitation - User-centric evaluation - Social recommenders Privacy: - Form auto-completion tools - App recommenders - Location-sharing social networks Samsung research intern, Google PhD Fellow @usabart
- 3. INFORMATION AND COMPUTER SCIENCES Outline 1. Transparency and control Privacy calculus, paradoxes, and bounded rationality 2. Privacy nudging and persuasion A solution inspired by decision sciences... with some flaws 3. Privacy Adaptation Procedure Adaptive nudges based on a contextualized understanding of users’ privacy concerns
- 4. Transparency and control Privacy calculus, paradoxes, and bounded rationality
- 5. INFORMATION AND COMPUTER SCIENCES The Privacy Paradox For many participants this behavior stands in sharp contrast to their self-reported privacy attitude - Spiekermann et al., 2001 Seventy percent of US consumers worry about online privacy, but few take protective action - Jupiter research report, 2002 Recent surveys, anecdotal evidence, and experiments have highlighted an apparent dichotomy between privacy attitudes and actual behavior - Acquisti & Grossklags, 2005
- 6. INFORMATION AND COMPUTER SCIENCES The Privacy Paradox
- 7. INFORMATION AND COMPUTER SCIENCES A model by Smith et al. 2011 Why aren’t these more strongly related?
- 11. INFORMATION AND COMPUTER SCIENCES Horror stories “My daughter [is] still in high school, and you’re sending her coupons for baby clothes and cribs? Are you trying to encourage her to get pregnant?” “I had a talk with my daughter. It turns out [...] she’s due in August. I owe you an apology.”
- 12. INFORMATION AND COMPUTER SCIENCES A model by Smith et al. 2011 Why aren’t these more strongly related? Control Transparency
- 13. INFORMATION AND COMPUTER SCIENCES Transparency and control ControlTransparency Informed consent “companies should provide clear descriptions of [...] why they need the data, how they will use it” User empowerment “companies should offer consumers clear and simple choices [...] about personal data collection, use, and disclosure”
- 14. INFORMATION AND COMPUTER SCIENCES Are transparency and control really the key to better privacy decisions?
- 15. INFORMATION AND COMPUTER SCIENCES Example: Website A/B testing
- 16. INFORMATION AND COMPUTER SCIENCES The Transparency Paradox Transparency is useful for concerned users, but bad for others Makes them more fearful Mentions of privacy (even favorable ones) often trigger privacy concerns
- 17. INFORMATION AND COMPUTER SCIENCES 44 Example: John et al.43 Appendix C: Experiment 2A: Screenshots of survey interface manipulation. Frivolous: Baseline: Serious:
- 18. INFORMATION AND COMPUTER SCIENCES Example: John et al. 43 Appendix C: Experiment 2A: Screenshots of survey interface manipulation. Frivolous: Baseline:
- 19. INFORMATION AND COMPUTER SCIENCES 44 Example: John et al.
- 20. INFORMATION AND COMPUTER SCIENCES 44 Example: John et al.43 Appendix C: Experiment 2A: Screenshots of survey interface manipulation. Frivolous: Baseline: Serious:
- 21. INFORMATION AND COMPUTER SCIENCES 37 0.7 0.8 0.9 1 1.1 1.2 1.3 Serious Frivolous AARrelativetooverallaverageAAR withinquestiontype Tame Intrusive Figure 6. The average AAR within each inquiry condition, relative to the overall average AAR for the questions of the given intrusiveness level (Experiment 2B). The value of 1 on the y axis represents the overall average AAR. Example: John et al.
- 22. INFORMATION AND COMPUTER SCIENCES ! ! ! 75% 80% 85% 90% 95% 100% BlogHeroes I♡WRK Codacare Auto ! BlogHeroes R ! ! ! 75% 80% 85% 90% 95% 100% BlogHeroes I♡WRK Codacare Contact info Interests Job skills Health record Control example: Knijnenburg et al. Normally, people are more likely to disclose information when the type of requested information matches the purpose of the website Please tell us more about yourself BlogHeroes will assign a "guild" to you based on the information you provide below. Note that none of the fields are required, but our classification will be better if you provide more information. General info about me Please provide some background info to get our matching process started. Name (first): John (last): Smith E-mail address: john@smith.com Gender: Male Age (years): 23 Address: 123 Main St. City: New York State: NY Zip: 12345 What I do for a living > For employers > For investors > Contact > About us Please enter your information I WRK will find jobs based on the information you enter on this form. None of the items on the form are required, but if you provide more information the jobs will be a better match. GENERAL AND CONTACT INFO General and contact information FIRST NAME John LAST NAME Smith clear AGE 23 clear GENDER Male clear E-MAIL ADDRESS john@smith.com clear ADDRESS 123 Main St. CITY New York STATE NY ZIP 12345 clear Enter your details, please Your personal Codacare health insurance policy will be based on the information you provide. Please note that none of the items are required, but the insurance will be better tailored to your needs if you provide more information. General information Please provide your general information. Name (first): (last): fill Address: fillCity: State: Zip: Gender: fill Age: fill E-‐mail: fill Health
- 23. INFORMATION AND COMPUTER SCIENCES ! ! ! 75% 80% 85% 90% 95% 100% BlogHeroes I♡WRK Codacare Auto ! ! ! BlogHeroes I♡WRK Codacare Remove ! BlogHeroes I♡ A Control example: Knijnenburg et al. Auto-completion tools make it so easy to submit a fully completed form that users may skip weighing the benefits and risk of disclosing a certain piece of information in a specific situation Please tell us more about yourself BlogHeroes will assign a "guild" to you based on the information you provide below. Note that none of the fields are required, but our classification will be better if you provide more information. General info about me Please provide some background info to get our matching process started. Name (first): John (last): Smith E-mail address: john@smith.com Gender: Male Age (years): 23 Address: 123 Main St. City: New York State: NY Zip: 12345 What I do for a living Some guilds write about their jobs. Tell us more about yours, and we can provide a better match. bit.ly/icis2013 ! Codacare ealth record
- 24. INFORMATION AND COMPUTER SCIENCES ! Codacare ! ! ! BlogHeroes I♡WRK Codacare Remove ! ! ! BlogHeroes I♡WRK Codacare Add Control example: Knijnenburg et al. Adding a simple “clear” button reduces overall disclosure and makes it more purpose-specific again Why? Users have more control! > For employers > For investors > Contact > About us Please enter your information I WRK will find jobs based on the information you enter on this form. None of the items on the form are required, but if you provide more information the jobs will be a better match. GENERAL AND CONTACT INFO General and contact information FIRST NAME John LAST NAME Smith clear AGE 23 clear GENDER Male clear E-MAIL ADDRESS john@smith.com clear ADDRESS CITY STATE ZIPbit.ly/icis2013
- 25. INFORMATION AND COMPUTER SCIENCES ! Codacare ! ! ! BlogHeroes I♡WRK Codacare Add Control example: Knijnenburg et al. Using a “fill” button instead does not further reduce disclosure, and actually leads to a higher user satisfaction Why? Even more control! Enter your details, please Your personal Codacare health insurance policy will be based on the information you provide. Please note that none of the items are required, but the insurance will be better tailored to your needs if you provide more information. General information Please provide your general information. Name (first): (last): fill Address: fill City: State: Zip: Gender: fill Age: fill E-‐mail: fill bit.ly/icis2013
- 26. INFORMATION AND COMPUTER SCIENCES Example: Facebook “bewildering tangle of options” (New York Times, 2010) “labyrinthian” controls” (U.S. Consumer Magazine, 2012)
- 27. INFORMATION AND COMPUTER SCIENCES Example: Knijnenburg et al. Introducing an “extreme” sharing option Nothing - City - Block Add the option Exact Expected: Some will choose Exact instead of Block Unexpected: Sharing increases across the board! B N privacy --> benefits--> C E bit.ly/chi2013privacy
- 28. INFORMATION AND COMPUTER SCIENCES The Control Paradox Decisions are too numerous Most Facebook users don’t know implications of their own privacy settings! Decisions are difficult Uncertain and delayed outcomes Result: people just pick the middle option!
- 29. INFORMATION AND COMPUTER SCIENCES Bounded rationality Why do transparency and control not work? People’s decisions are inconsistent and seemingly irrational -Framing effects -Default effects -Order effects
- 30. INFORMATION AND COMPUTER SCIENCES Please send me Vortrex Newsletters and information. Please do not send me Vortrex Newsletters and information. Please send me Vortrex Newsletters and information. Please do not send me Vortrex Newsletters and information. Figure 4: Subjects were assigned one of the following conditions in the registration page. 3.1. Data Analysis and Results The mean levels of participations in each experimental condition are reported in Table 1 below. Table 1: Mean participation levels as a function of frames and 4. In the inher defau onlin The t the s Conn actio nega conv posit Framing and defaults: Lai and Hui 0% 25% 37% 53% D A B C
- 31. INFORMATION AND COMPUTER SCIENCES Default order: Acquisti et al. Foot in the door (innocuous requests first) Door in the face (risqué requests first)
- 32. INFORMATION AND COMPUTER SCIENCES 0 200 400 600 800 1000 1200 1400 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 Question number (Increasing condition) Cumulativeadmissionratesinpercentages Decreasing Increasing Baseline Default order: Acquisti et al.
- 33. INFORMATION AND COMPUTER SCIENCES Bounded rationality Why do transparency and control not work? Transparency: Information overload Control: Choice overload
- 34. INFORMATION AND COMPUTER SCIENCES Bounded rationality Why do transparency and control not work? Transparency: Information overload Control: Choice overload
- 35. INFORMATION AND COMPUTER SCIENCES Summary of part 1 We need to move beyond control and transparency Rational privacy decision- making is bounded Transparency and control increase choice difficulty
- 36. Privacy nudging and persuasion A solution inspired by decision sciences... with some flaws
- 37. INFORMATION AND COMPUTER SCIENCES Starting point... People’s decisions are inconsistent and seemingly irrational, therefore: -People do not always choose what is best for them -There is significant leeway to influence people's decisions -Being objectively neutral is impossible
- 38. INFORMATION AND COMPUTER SCIENCES Privacy Calculus A new model Decision heuristics Benefits Behavioral reactions (including disclosures) Risk/ Costs Nudge Nudge Persuasion PersuasionJustification Default value Default order Justification
- 39. INFORMATION AND COMPUTER SCIENCES A new model Default value Justification A succinct reason to disclose (or not disclose) a piece of information -Make it easier to rationalize the decision -Minimize the potential regret of choosing the wrong option Relieve users from the burden of making decisions -Path of least resistance -Implicit normative cue (what I should do) -Endowment effect (what I have is worth more than what I don’t have)
- 40. INFORMATION AND COMPUTER SCIENCES Example: Knijnenburg & Kobsa 5 justification types None Useful for you Number of others Useful for others Explanation bit.ly/tiis2013
- 41. INFORMATION AND COMPUTER SCIENCES 0%# 10%# 20%# 30%# 40%# 50%# 60%# 70%# 80%# 90%# 100%# Context#first# Demographics#first# Context#first# Demograpics#first# Disclosure*behavior** Demographics*disclosure * *Context*disclosure* Default order: Knijnenburg & Kobsa bit.ly/tiis2013
- 42. INFORMATION AND COMPUTER SCIENCES *" 1" **" *" ***" *" *" 0%" 10%" 20%" 30%" 40%" 50%" 60%" 70%" 80%" 90%" 100%" Context"first" Demographics"first" Context"first" Demograpics"first" Disclosure*behavior** Demographics*disclosure * *Context*disclosure* none" useful"for"you" #"of"others" useful"for"others" explanaDon" Justifications: Knijnenburg & Kobsa bit.ly/tiis2013
- 43. INFORMATION AND COMPUTER SCIENCES **" **" ***" 1" $1,00" $0,75" $0,50" $0,25" 0,00" 0,25" 0,50" 0,75" 1,00" Sa#sfac#on)with)) the)system) Justifications: Knijnenburg & Kobsa Anticipated satisfaction with the system (intention to use): 6 items, e.g. “I would recommend the system to others” Lower for any justification! *" 1" **" *" ***" *" *" 0%" 10%" 20%" 30%" 40%" 50%" 60%" 70%" 80%" 90%" 100%" Context"first" Demographics"first" Context"first" Demograpics"first" Disclosure*behavior** Demographics*disclosure * *Context*disclosure* none" useful"for"you" #"of"others" useful"for"others" explanaDon" bit.ly/tiis2013
- 44. INFORMATION AND COMPUTER SCIENCES Please send me Vortrex Newsletters and information. Please do not send me Vortrex Newsletters and information. Please send me Vortrex Newsletters and information. Please do not send me Vortrex Newsletters and information. Figure 4: Subjects were assigned one of the following conditions in the registration page. 3.1. Data Analysis and Results The mean levels of participations in each experimental condition are reported in Table 1 below. Table 1: Mean participation levels as a function of frames and 4. In the inher defau onlin The t the s Conn actio nega conv posit Framing and Defaults: Lai and Hui 0% 25% 37% 53% D A B C
- 45. INFORMATION AND COMPUTER SCIENCES Problems with Privacy Nudging What should be the purpose of the nudge? “More data collection = better, e.g. for personalization” Techniques to increase disclosure cause reactance in the more privacy-minded users “Privacy is an absolute right“ More difficult for less privacy-minded users to enjoy the benefits that disclosure would provide
- 46. INFORMATION AND COMPUTER SCIENCES Problems with Privacy Nudging Smith, Goldstein & Johnson: “What is best for consumers depends upon characteristics of the consumer: An outcome that maximizes consumer welfare may be suboptimal for some consumers in a context where there is heterogeneity in preferences.”
- 47. INFORMATION AND COMPUTER SCIENCES Summary of part 2 Nudges work Defaults and justifications can influence users’ decisions But we cannot nudge everyone the same way! Users differ in their disclosure preferences Nudges should respect these differences
- 48. Privacy Adaptation Procedure Adaptive nudges based on a contextualized understanding of users’ privacy concerns
- 49. INFORMATION AND COMPUTER SCIENCES What kind of system helps users find what they want in the presence of heterogeneous preferences? A recommender system! (more specifically, a Privacy Adaptation Procedure)
- 50. INFORMATION AND COMPUTER SCIENCES Towards Privacy Adaptation “Figure out what people want, then help them do that.” Explicate the privacy calculus/heuristics What best captures people’s privacy preferences? What are the underlying reasons to disclose or not? Contextualize the privacy calculus/heuristics Who discloses and who doesn’t? What do they disclose and what do they withhold? Under what circumstances do they disclose?
- 51. INFORMATION AND COMPUTER SCIENCES Contextualize Privacy decision different users differentcontext Contextualizing privacy The optimal justification and default may depend on: -type of info (what) -user characteristics (who) -recipient (to whom) -etc...
- 52. INFORMATION AND COMPUTER SCIENCES Example: Knijnenburg et al. Type of data ID Items Facebook activity 1 Wall Facebook activity 2 Status updates Facebook activity 3 Shared linksFacebook activity 4 Notes Facebook activity 5 Photos Location 6 Hometown Location 7 Location (city)Location 8 Location (state/province) Contact info 9 Residence (street address) Contact info 11 Phone numberContact info 12 Email address Life/interests 13 Religious views Life/interests 14 Interests (favorite movies, etc.)Life/interests 15 Facebook groups bit.ly/privdim
- 53. INFORMATION AND COMPUTER SCIENCES Example: Knijnenburg et al. Type of data ID Items Facebook activity 1 Wall Facebook activity 2 Status updates Facebook activity 3 Shared linksFacebook activity 4 Notes Facebook activity 5 Photos Location 6 Hometown Location 7 Location (city)Location 8 Location (state/province) Contact info 9 Residence (street address) Contact info 11 Phone numberContact info 12 Email address Life/interests 13 Religious views Life/interests 14 Interests (favorite movies, etc.)Life/interests 15 Facebook groups “What?” = Four dimensions bit.ly/privdim
- 54. INFORMATION AND COMPUTER SCIENCES Example: Knijnenburg et al. 159 pps tend to share little information overall (LowD) 26 pps tend to share activities and interests (Act+IntD) 50 pps tend to share location and interests (Loc+IntD) 65 pps tend to share everything but contact info (Hi-ConD) 59 pps tend to share everything “Who?” = Five disclosure profiles bit.ly/privdim
- 55. INFORMATION AND COMPUTER SCIENCES Example: Knijnenburg et al. Detect class member- ship bit.ly/privdim
- 56. INFORMATION AND COMPUTER SCIENCES ! ! ! 75% 80% 85% 90% 95% 100% BlogHeroes I♡WRK Codacare Contact info Interests Job skills Health record Example: Knijnenburg et al. Please tell us more about yourself BlogHeroes will assign a "guild" to you based on the information you provide below. Note that none of the fields are required, but our classification will be better if you provide more information. General info about me Please provide some background info to get our matching process started. Name (first): John (last): Smith E-mail address: john@smith.com Gender: Male Age (years): 23 Address: 123 Main St. City: New York State: NY Zip: 12345 What I do for a living > For employers > For investors > Contact > About us Please enter your information I WRK will find jobs based on the information you enter on this form. None of the items on the form are required, but if you provide more information the jobs will be a better match. GENERAL AND CONTACT INFO General and contact information FIRST NAME John LAST NAME Smith clear AGE 23 clear GENDER Male clear E-MAIL ADDRESS john@smith.com clear ADDRESS 123 Main St. CITY New York STATE NY ZIP 12345 clear Enter your details, please Your personal Codacare health insurance policy will be based on the information you provide. Please note that none of the items are required, but the insurance will be better tailored to your needs if you provide more information. General information Please provide your general information. Name (first): (last): fill Address: fillCity: State: Zip: Gender: fill Age: fill E-‐mail: fill Health “To whom?” matters too!
- 57. INFORMATION AND COMPUTER SCIENCES Example: Knijnenburg & Kobsa I do whatever others do I care about the benefits
- 58. INFORMATION AND COMPUTER SCIENCES disclosure tendency, where requesting context data first leads to less threat and more trust. Figure 4 compares for each group the best strategy (marked with an arrow) against all other strategies. Strategies that perform significantly worse than the best strategy are labeled with a p-value. Best Strategy to Achieve High Total Disclosure Since it is best to ask demographics first to increase demographics disclosure, and context first to increase context disclosure, increasing total disclosure asks for a compromise. The best way to attain this compromise is to first choose a preferred request order, and then to select a User type Context first Demographics first Males with low disclosure tendency The ‘useful for you’ justification gives the highest demographics disclosure. Providing no justification gives the highest context disclosure. Females with low disclosure tendency Providing no justification gives the highest demographics disclosure. The ‘explanation’ justification keeps context disclosure on par. Males with high disclosure tendency The ‘useful for others’ justification keeps demographics disclosure almost on par. The ‘useful for you’ justification keeps context disclosure on par. Females with high disclosure tendency Providing no justification gives a high demographics disclosure. The ‘useful for you’ justification gives the highest context disclosure. Table 2: Best strategies to achieve high overall disclosures. User type Best strategy Males with low disclosure tendency Demographics first with ‘useful for you’. Males with high disclosure tendency The ‘useful for you’ justification in any order. Females with low disclosure tendency Context first with ‘useful for you’. Females with high disclosure tendency Context first with no justification, but ‘useful for you’ is second best. Table 3: Best strategies to achieve high user satisfaction. Example: Knijnenburg & Kobsa bit.ly/iui2013
- 59. INFORMATION AND COMPUTER SCIENCES The Adaptive Privacy Procedure pshare = α + βitemtype + βusertype + βrecipienttype • Determine the item-. user-, and recipient-type • Select the default and justification that fits best for this contextINPUT {user, item, recipient} {defaults, justification}OUTPUT
- 60. INFORMATION AND COMPUTER SCIENCES The Adaptive Privacy Procedure Practical use: -Automatic initial defaults in line with “disclosure profile” -Personalized disclosure justifications Relieves some of the burden of the privacy decision: The right privacy-related information The right amount of control “Realistic empowerment”
- 61. INFORMATION AND COMPUTER SCIENCES Summary of part 3 Smith, Goldstein & Johnson: “the idea of an adaptive default preserves considerable consumer autonomy [...] and strikes a balance between providing more choice and providing the right choices.”
- 62. INFORMATION AND COMPUTER SCIENCES Final summary 1. Transparency and control Rational privacy decision-making is bounded, and transparency and control only increase choice difficulty 2. Privacy nudging and persuasion Needs to move beyond the one-size-fits-all approach 3. Privacy Adaptation Procedure The optimal balance between nudges and control
