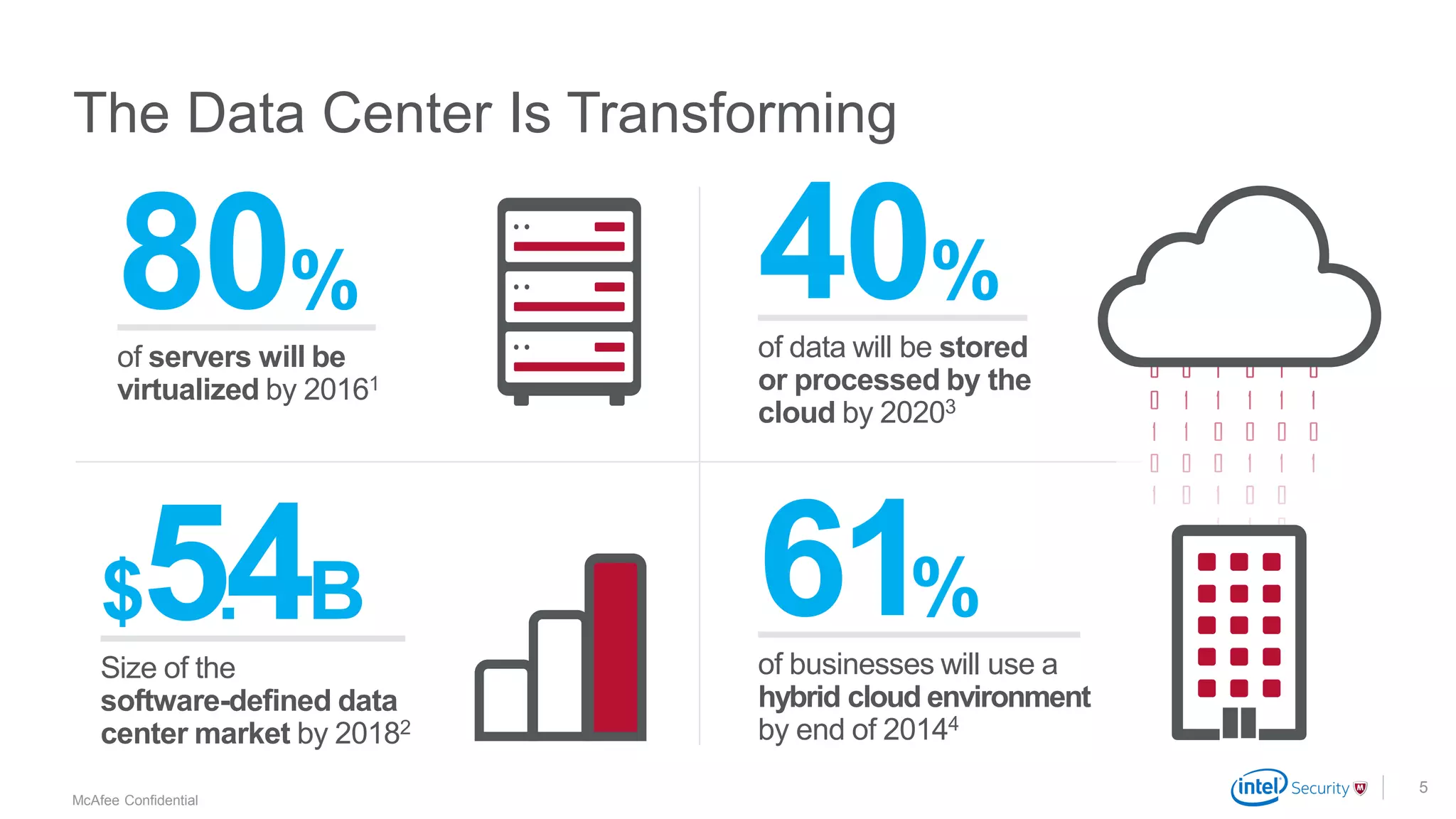
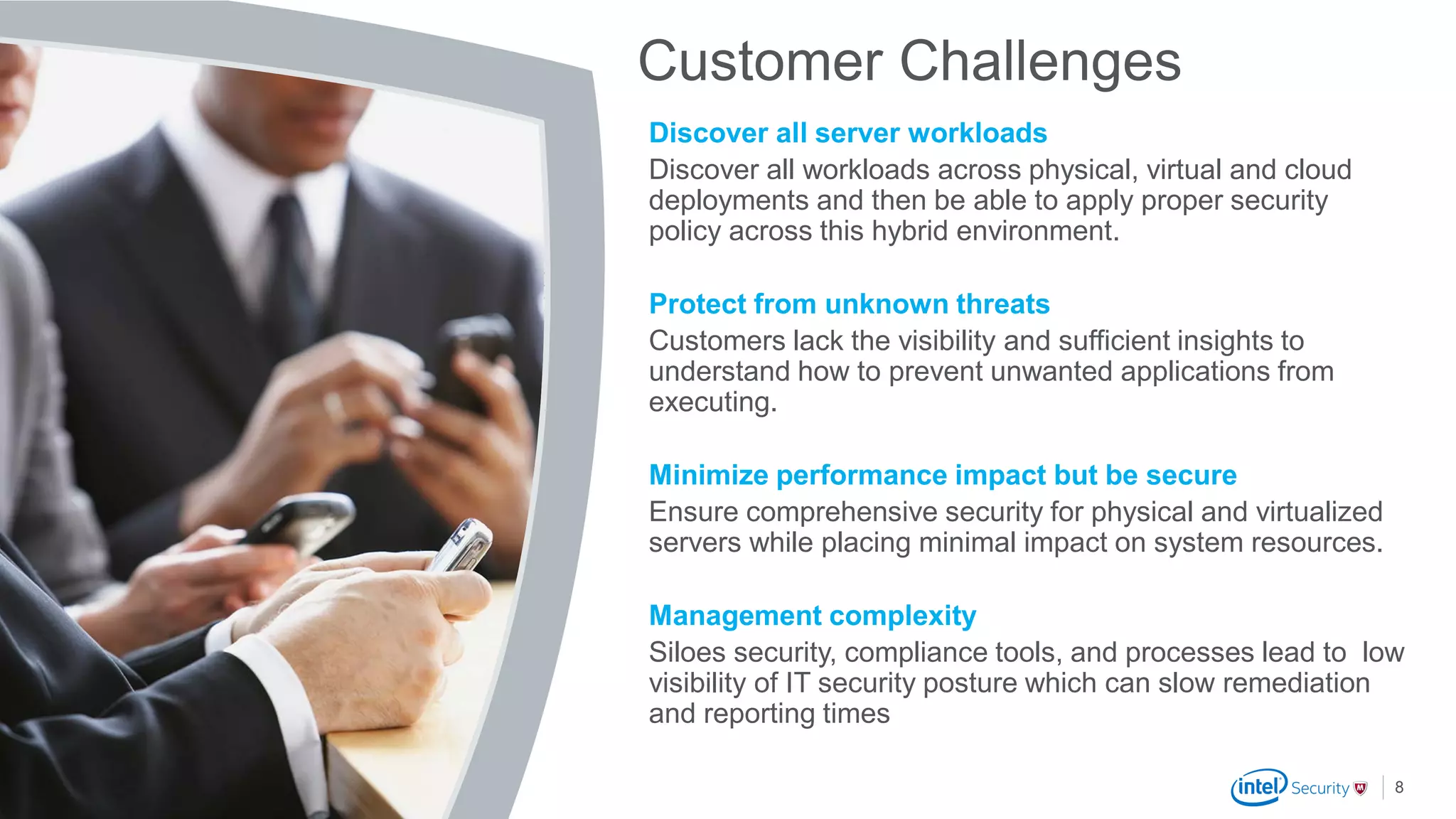
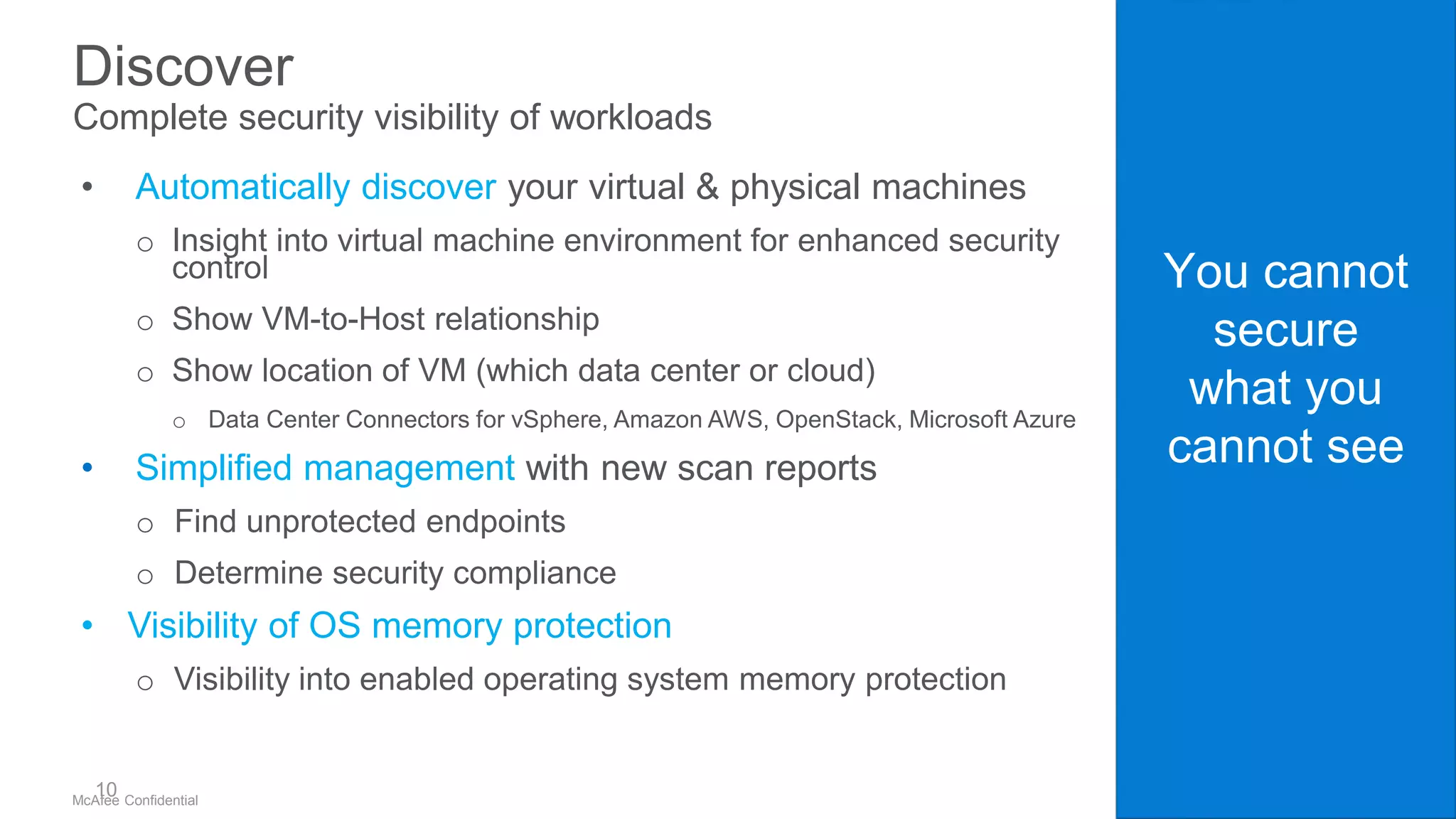
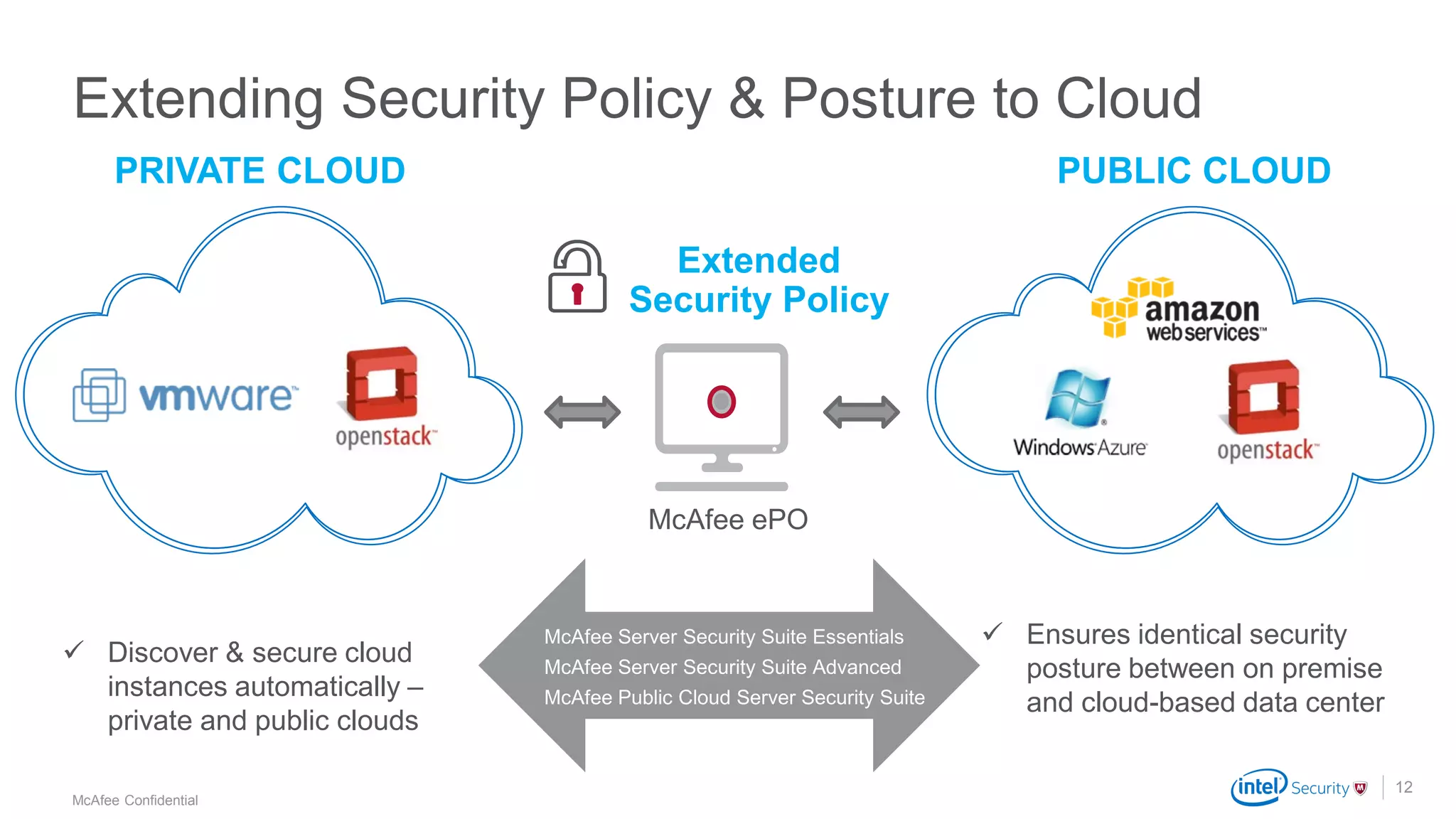
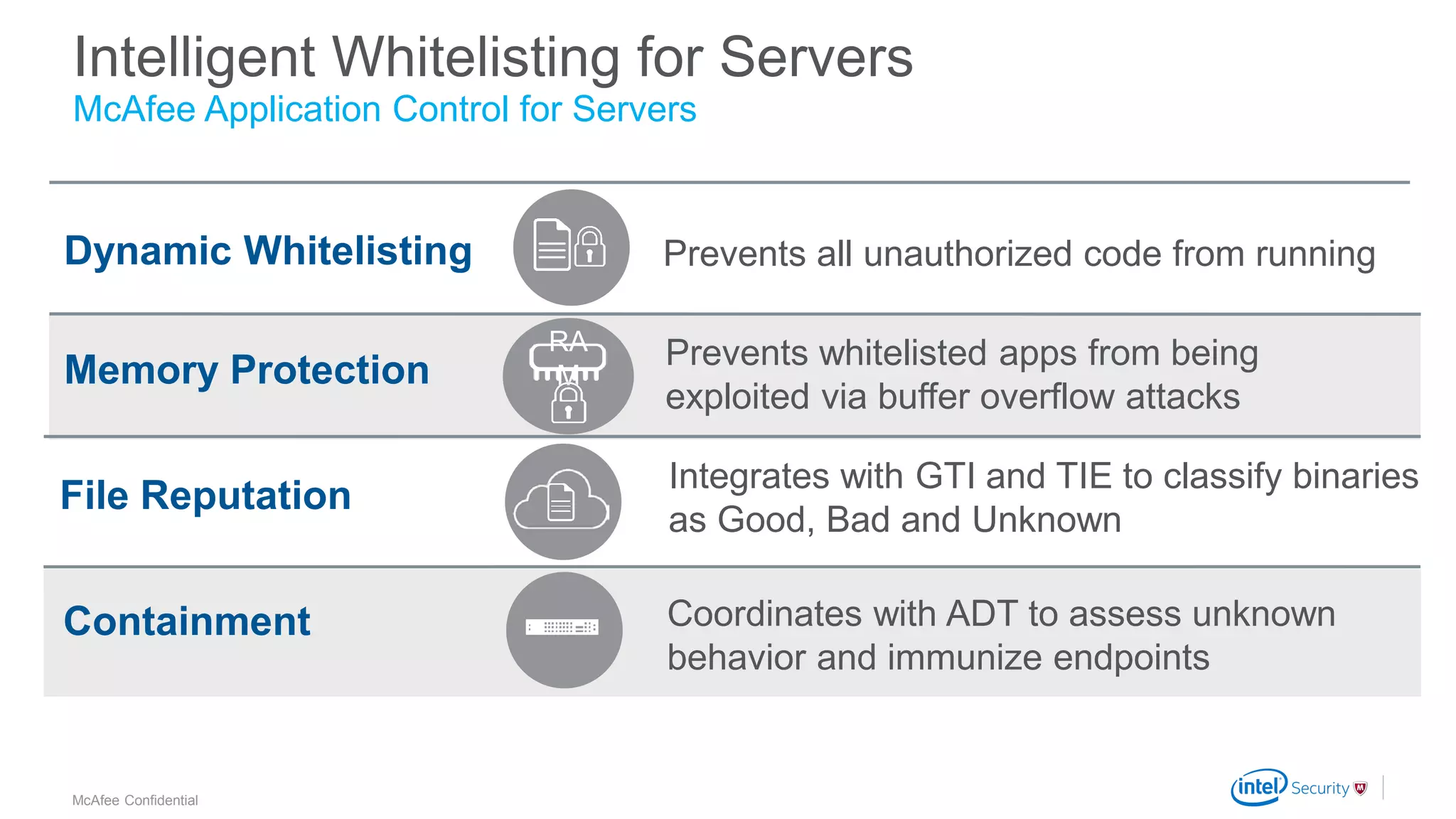
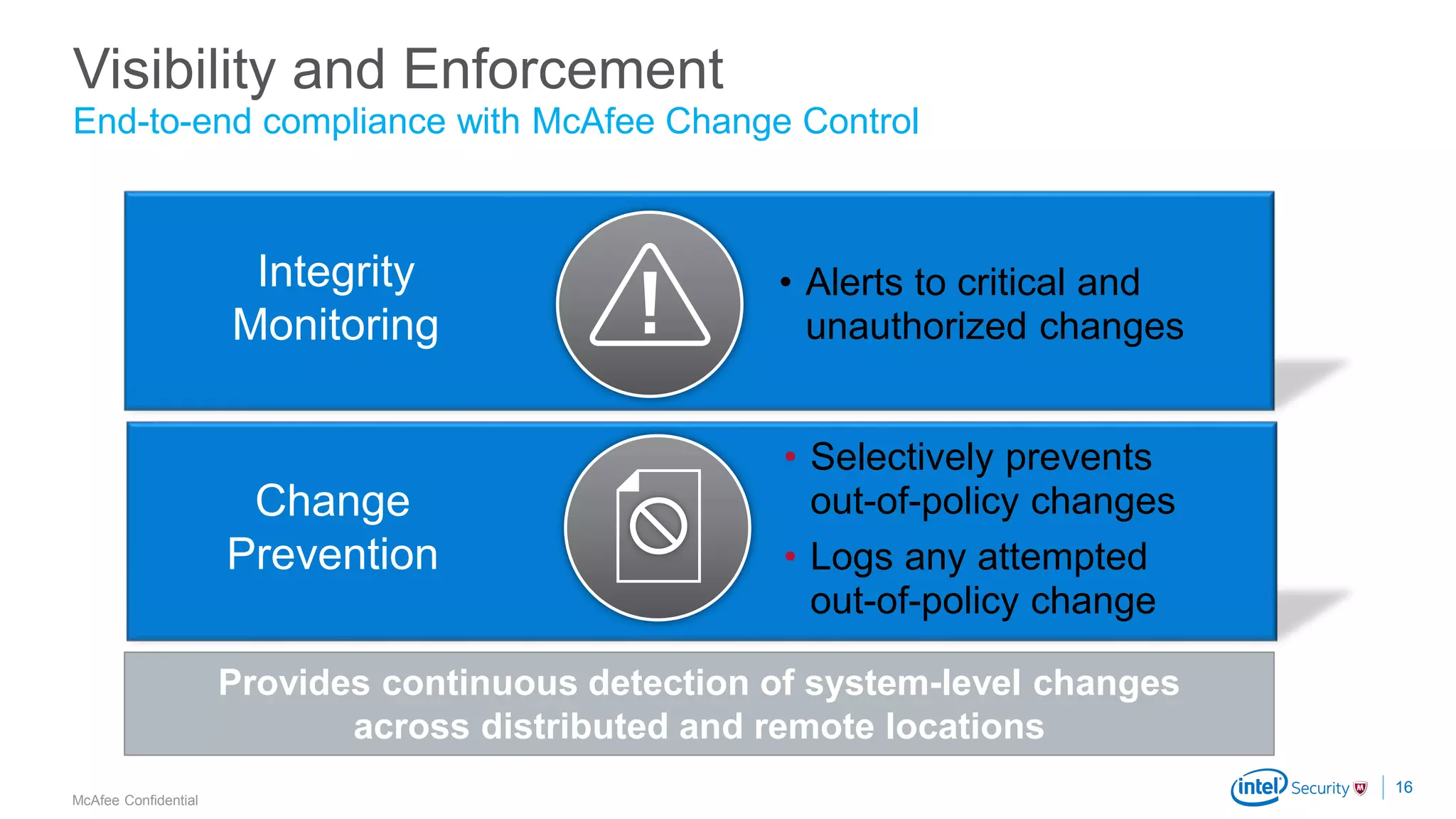
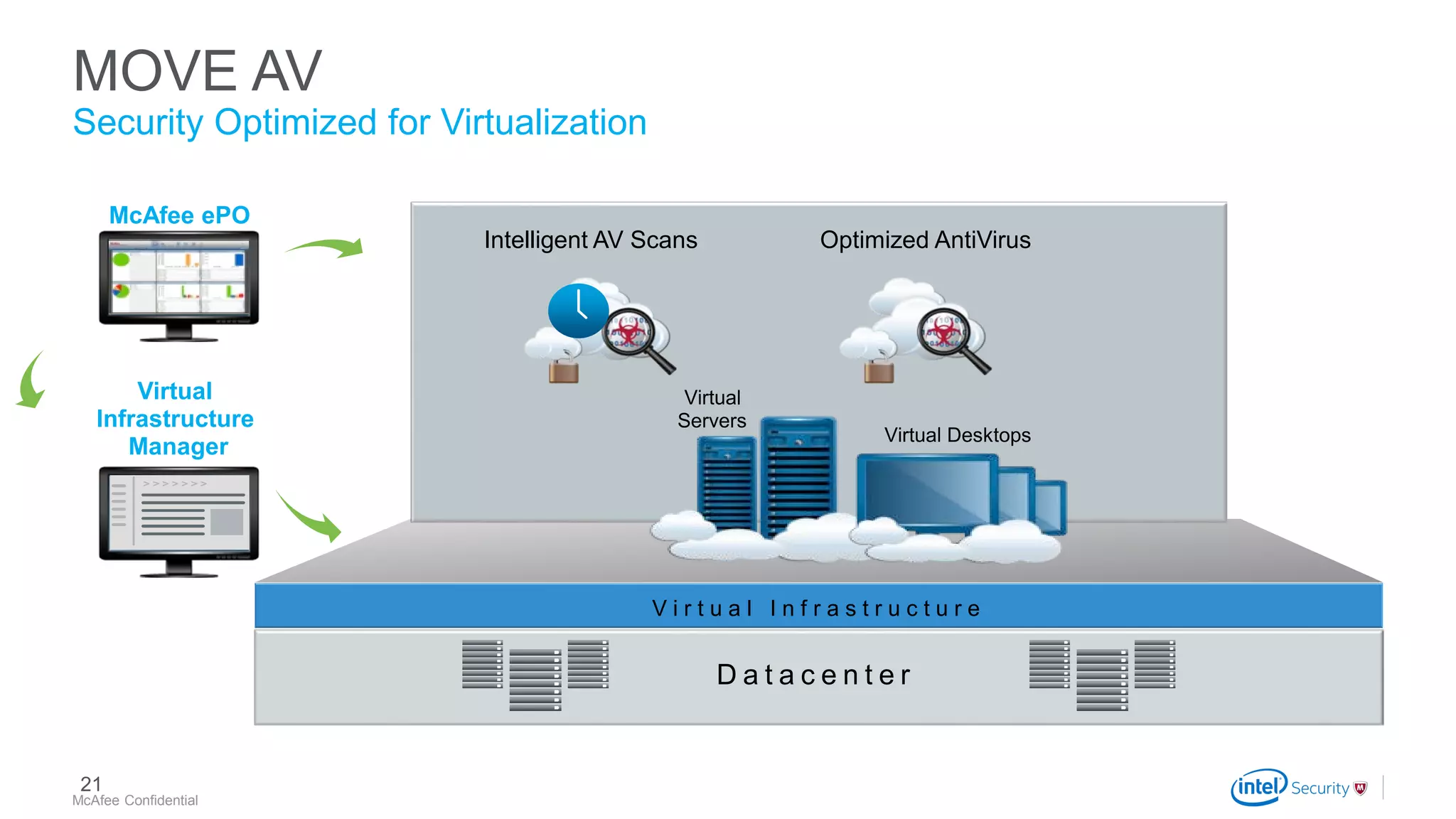
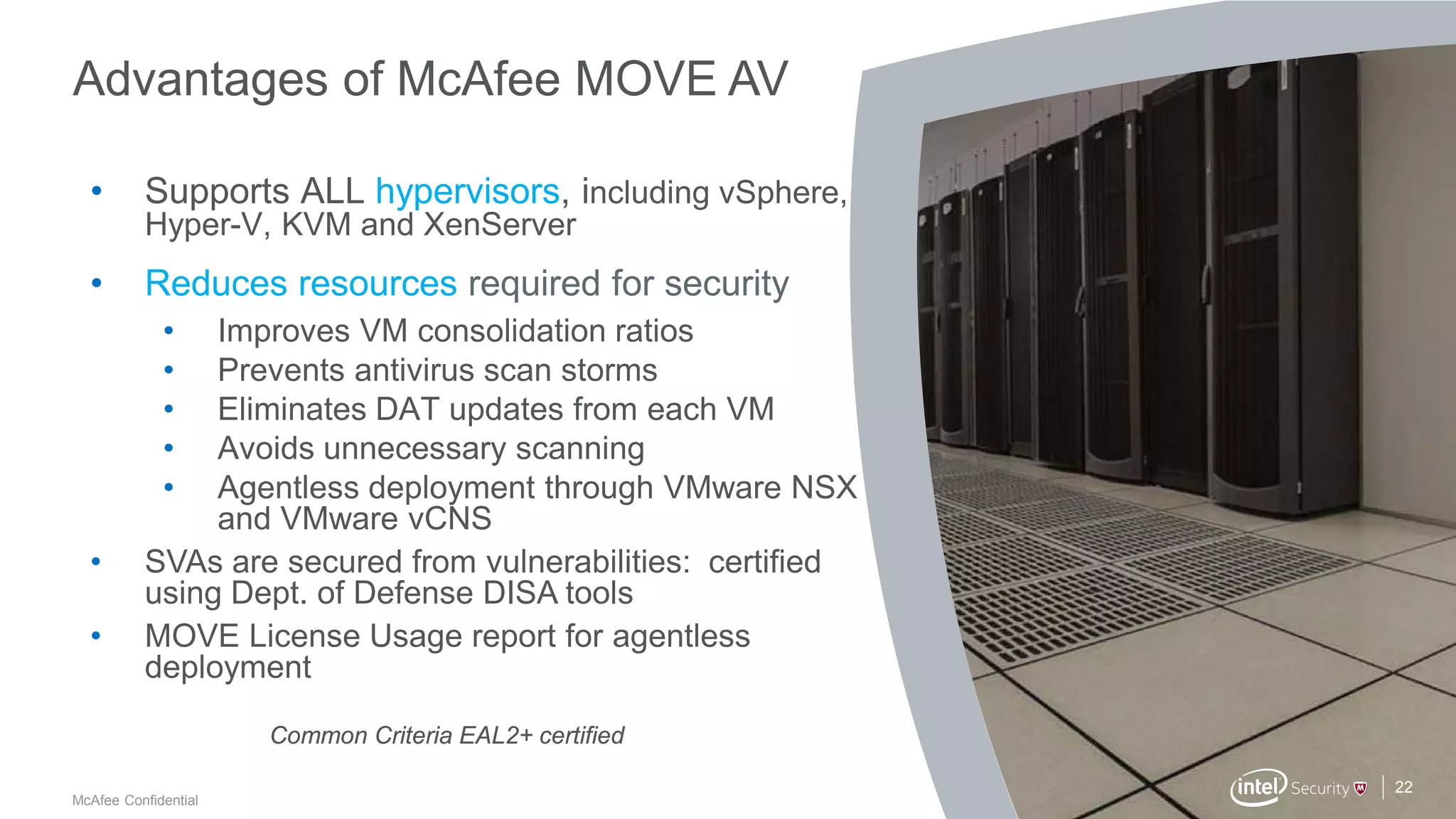
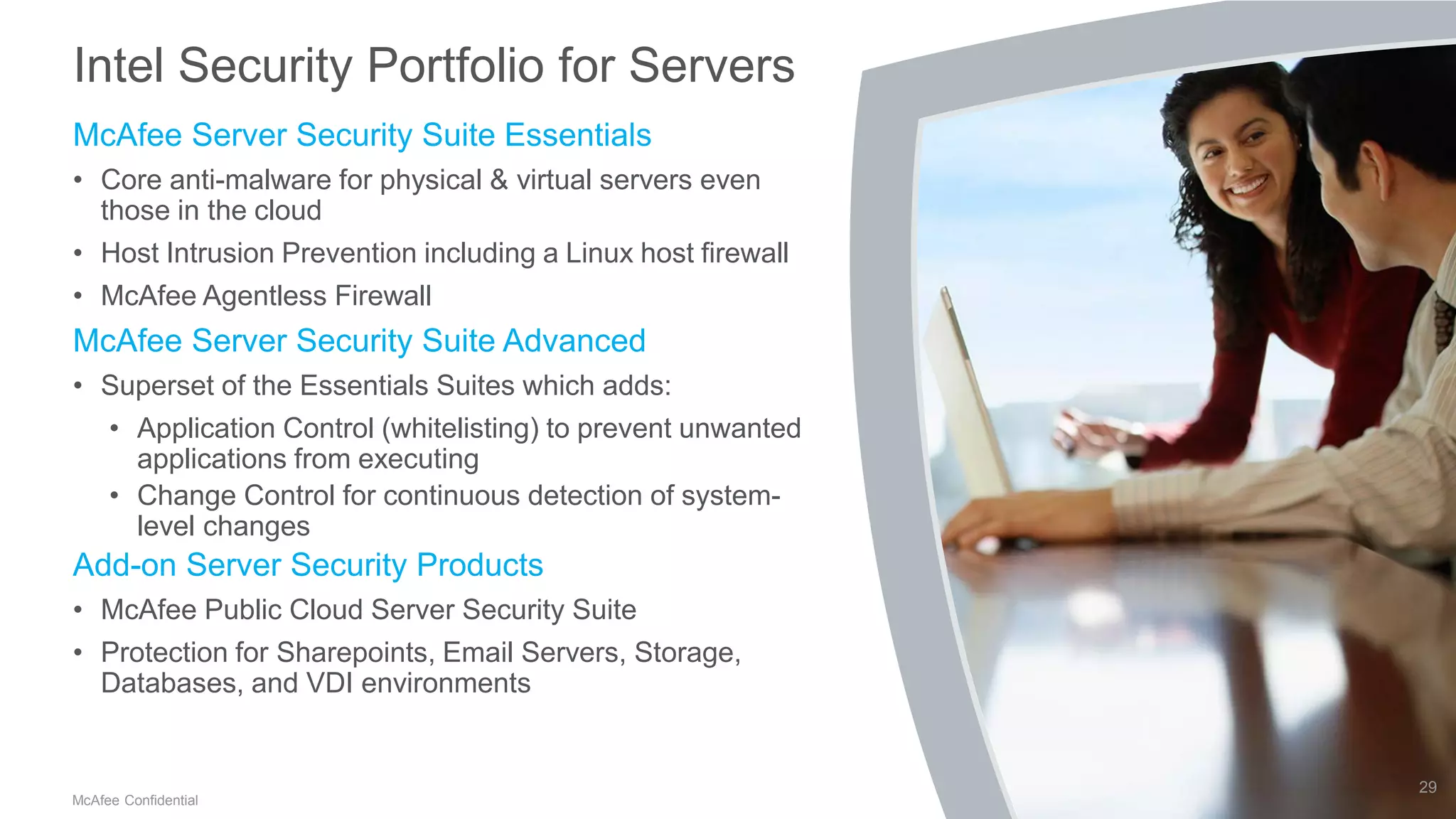
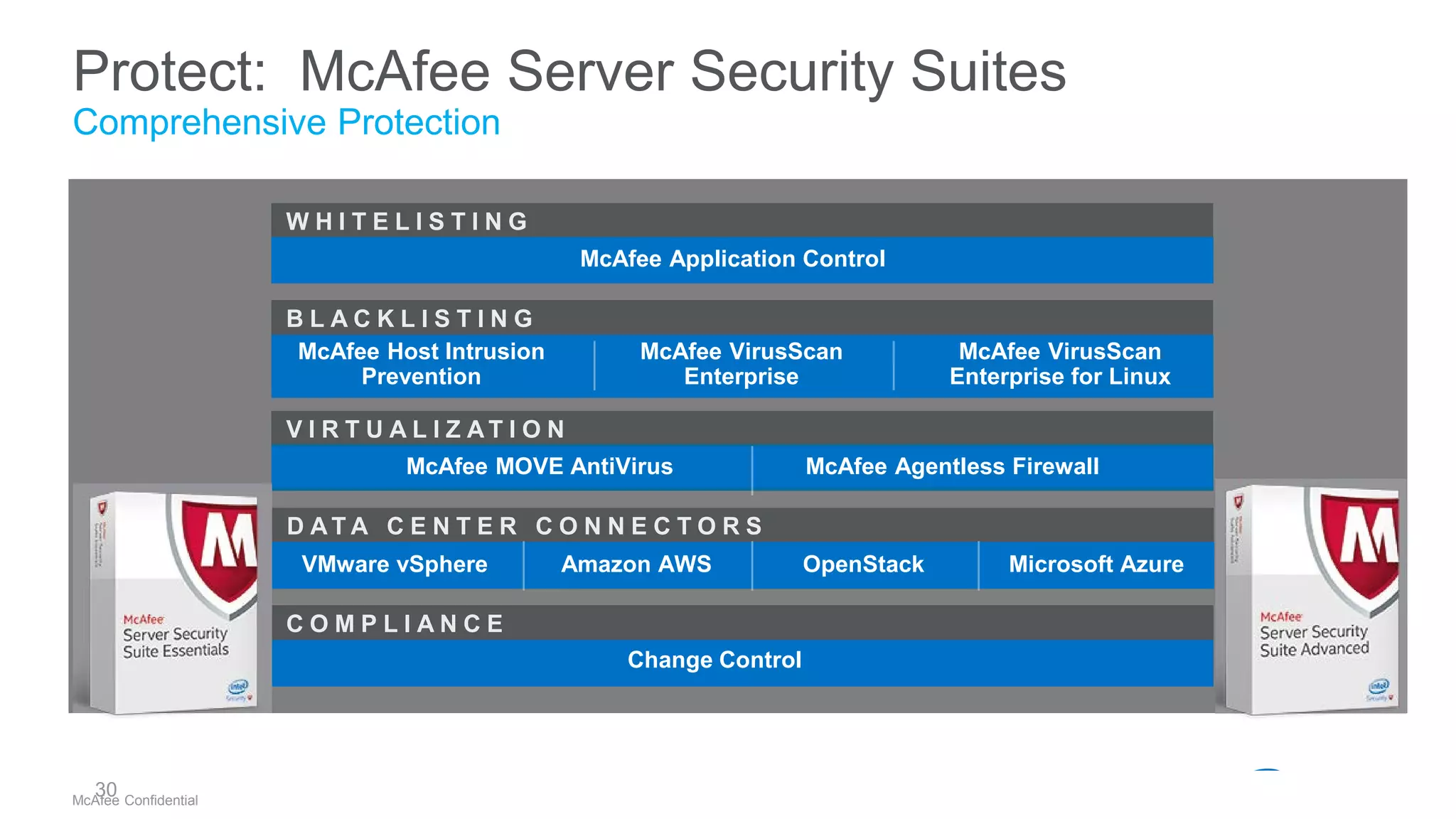
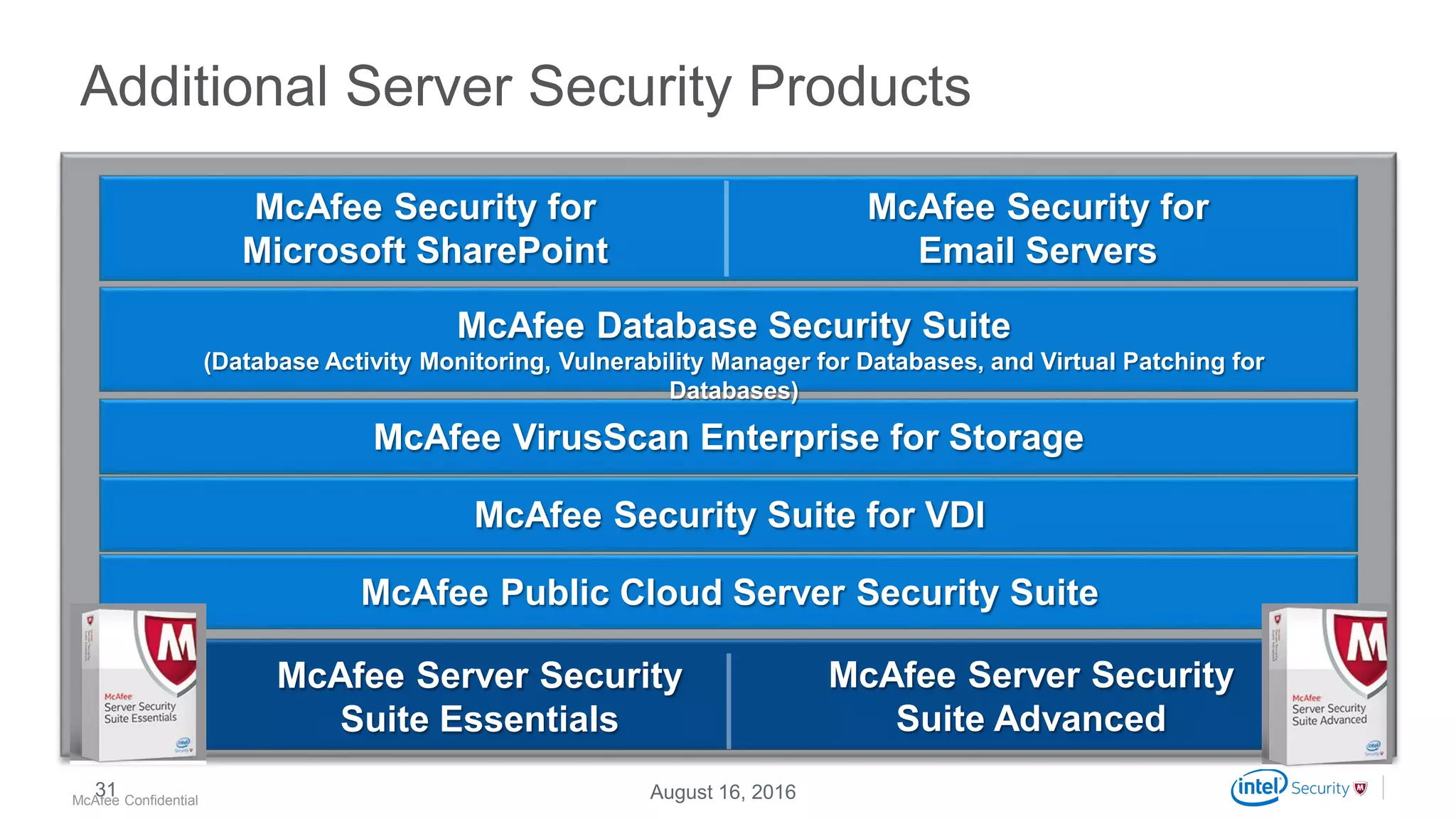
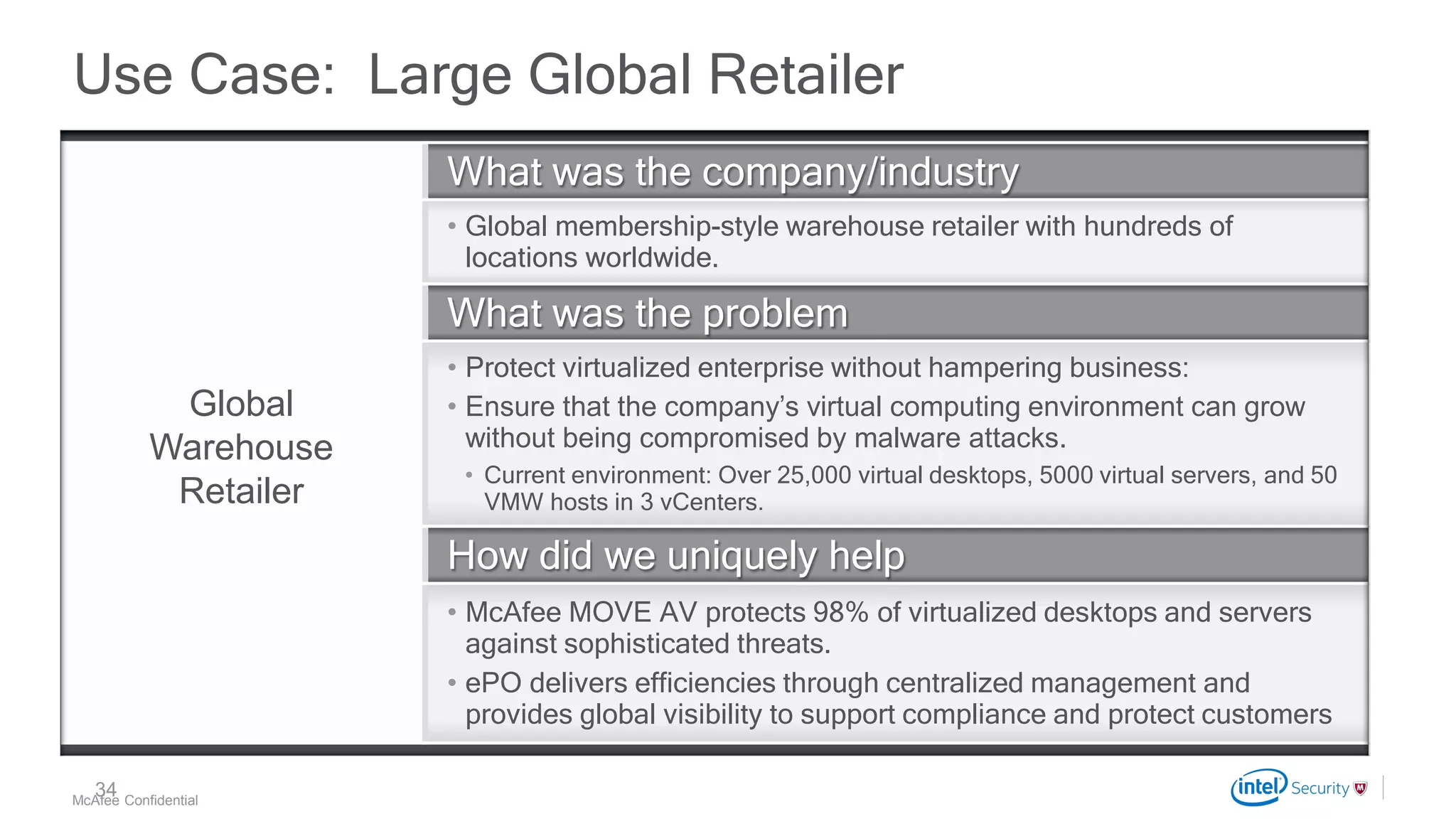
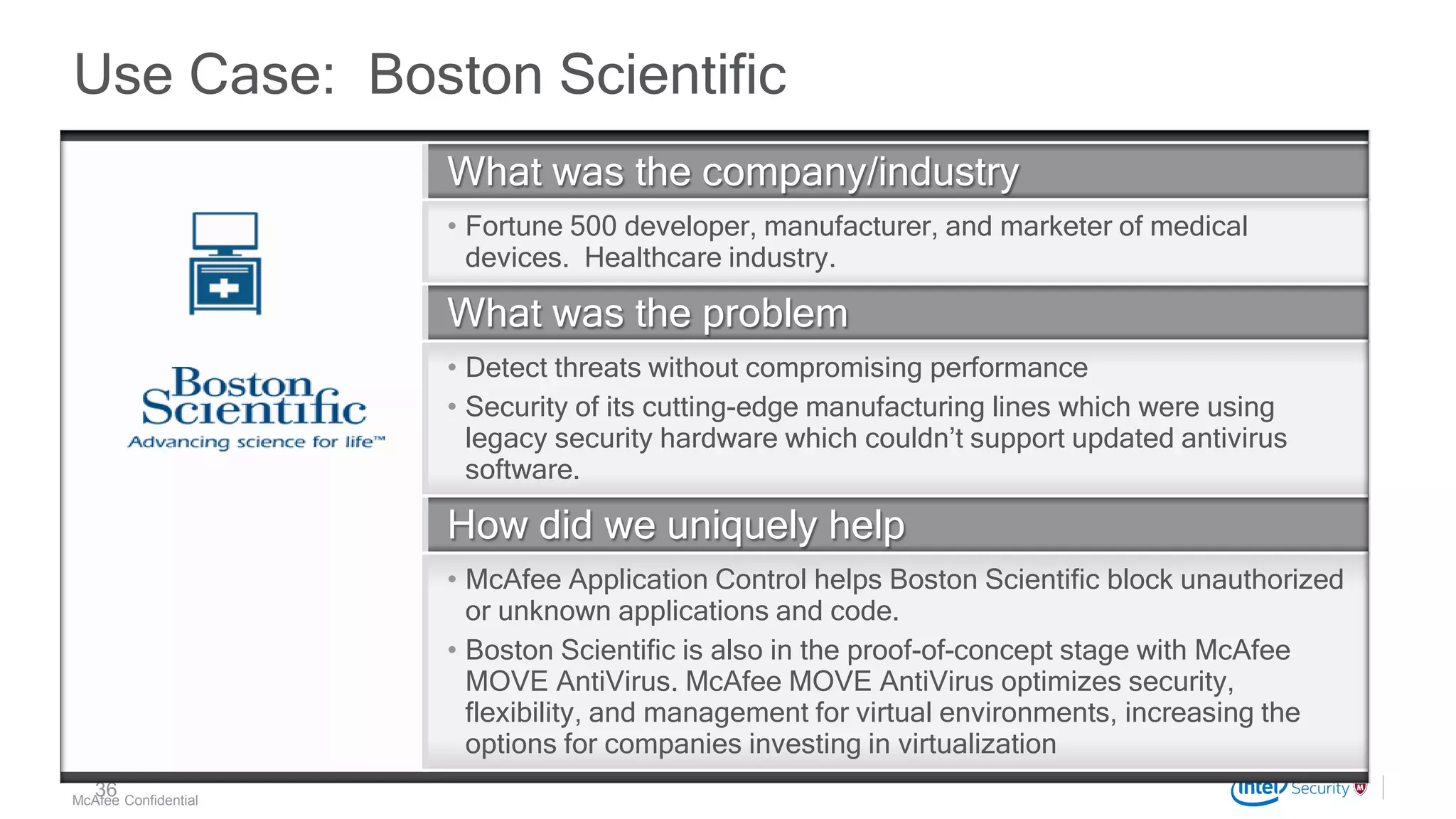
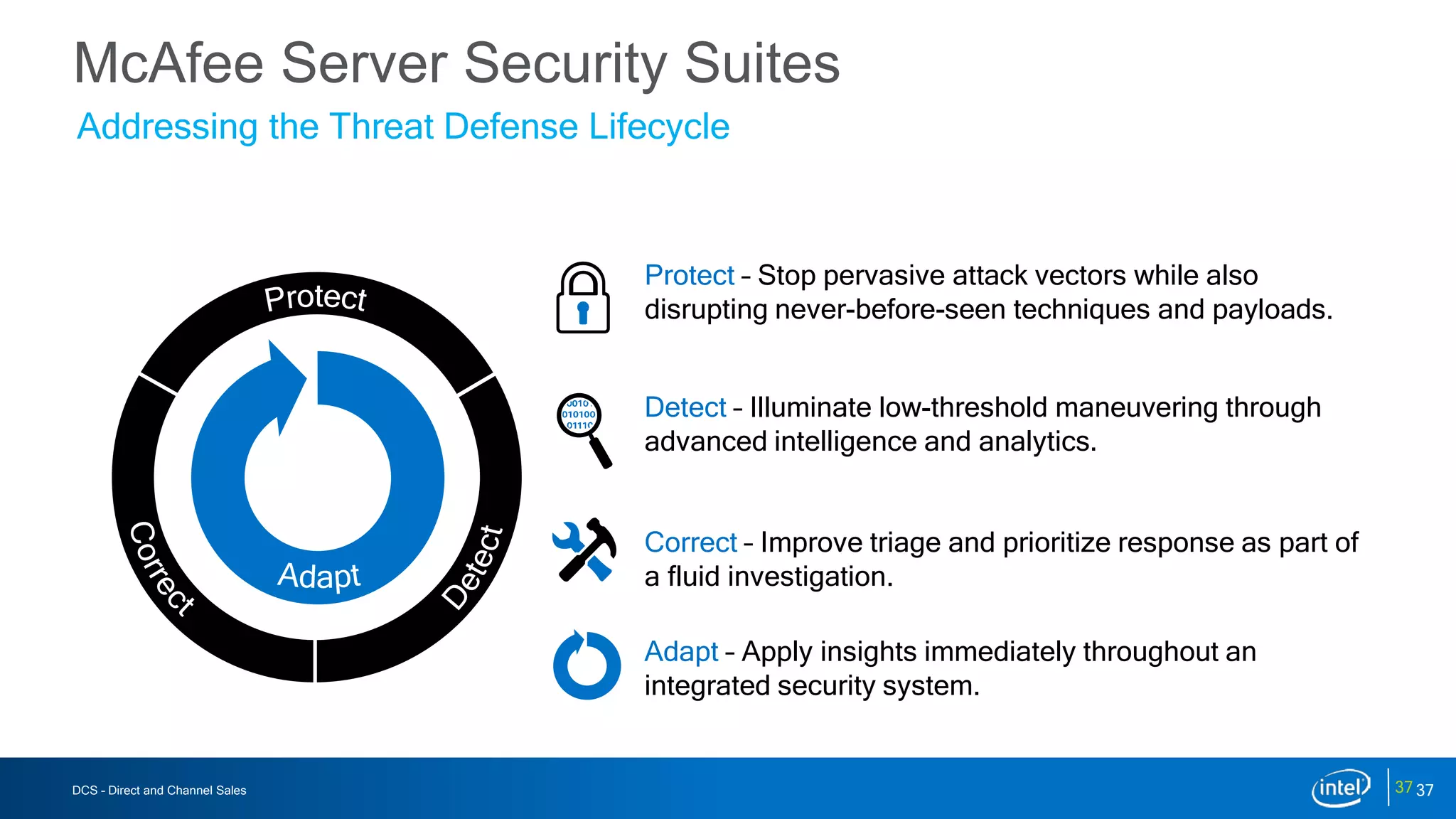
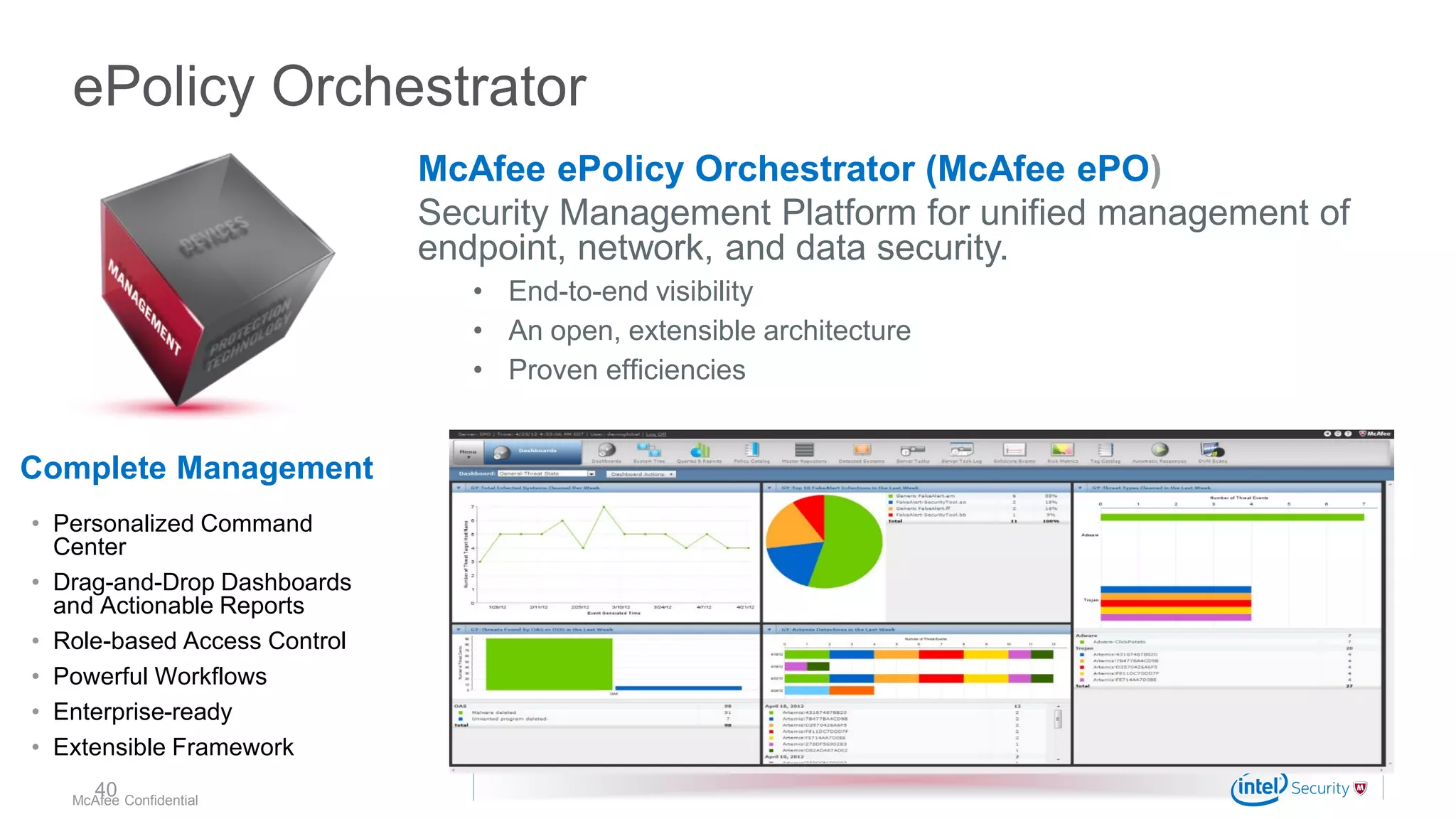
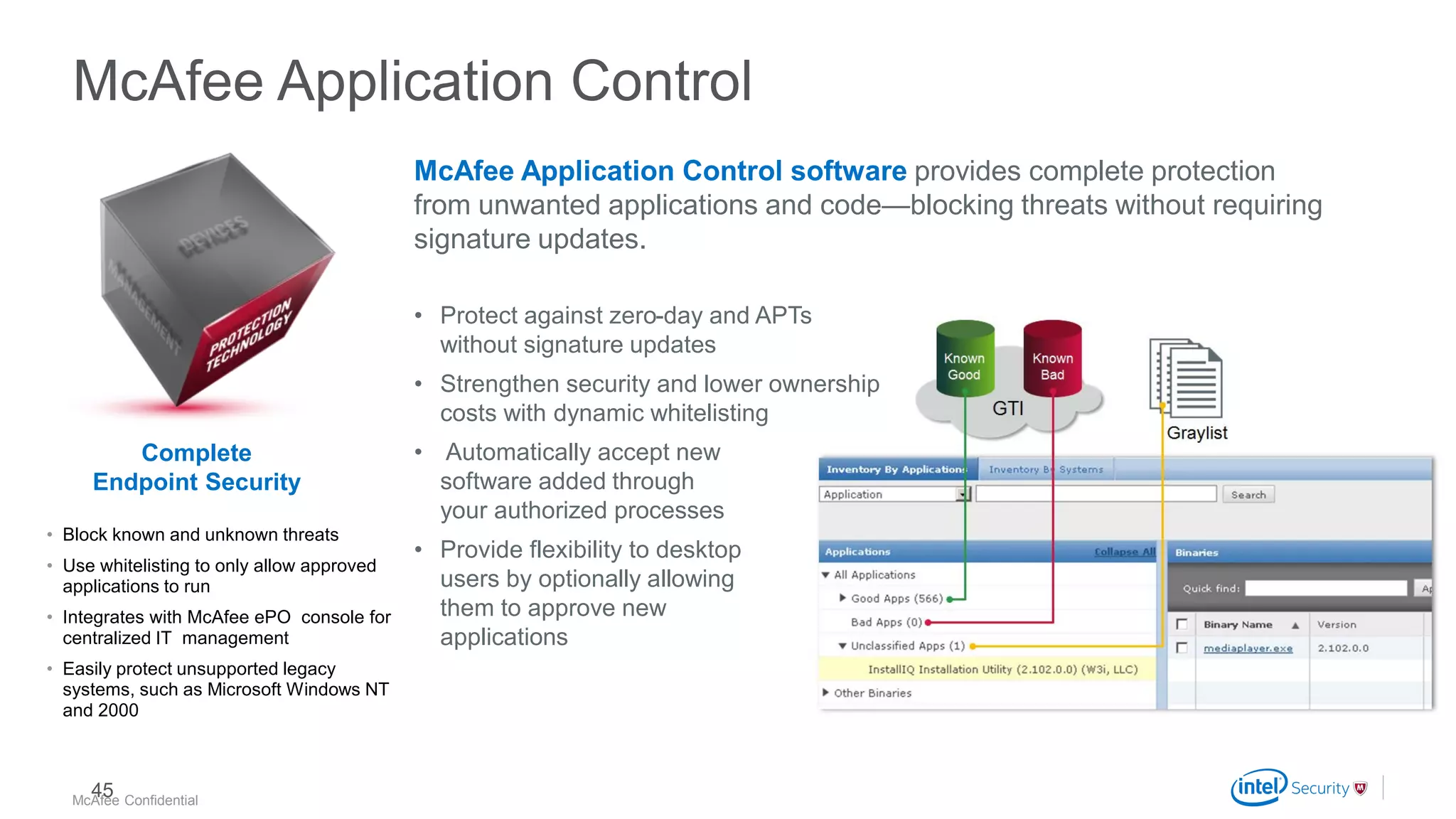
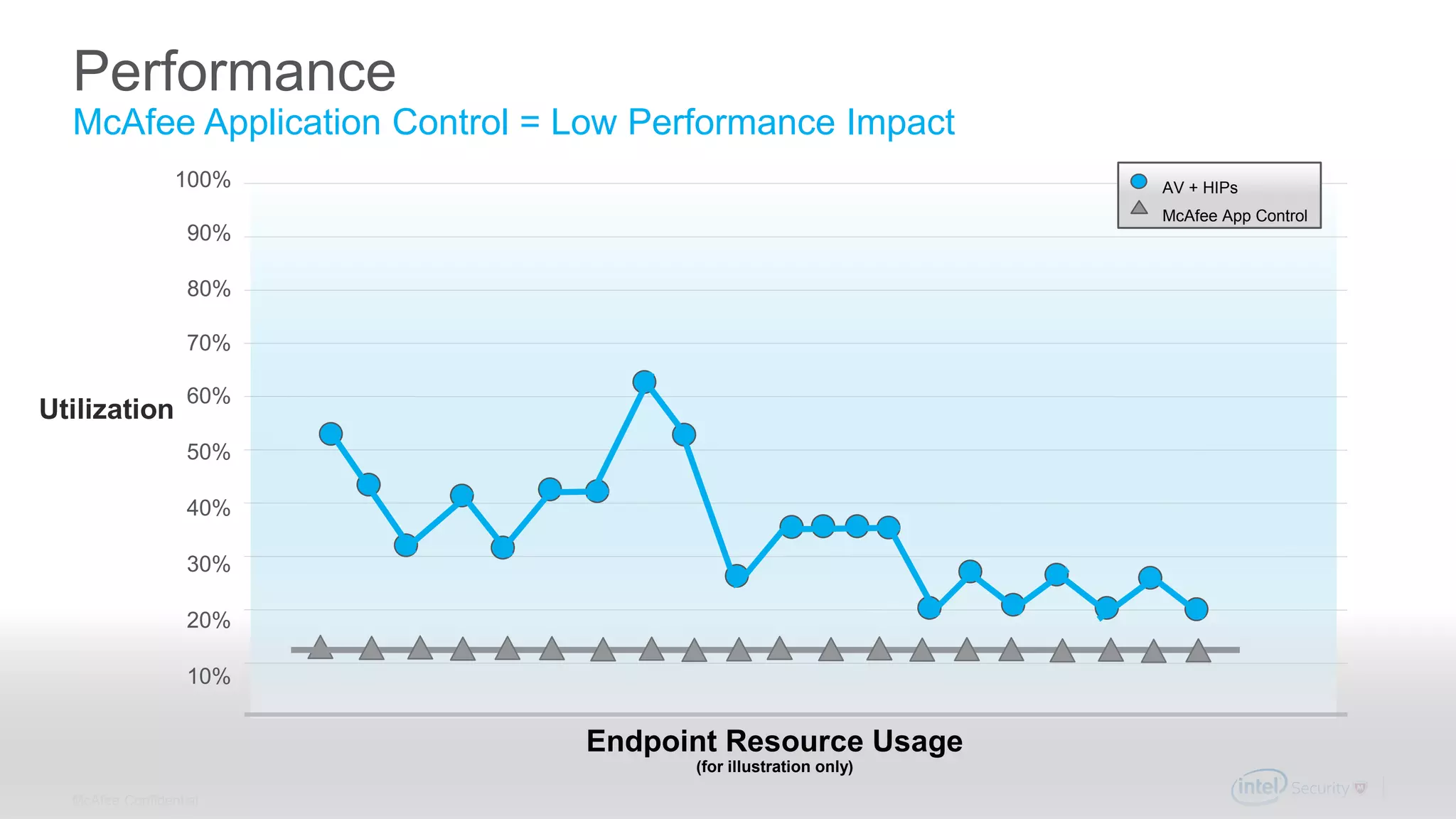
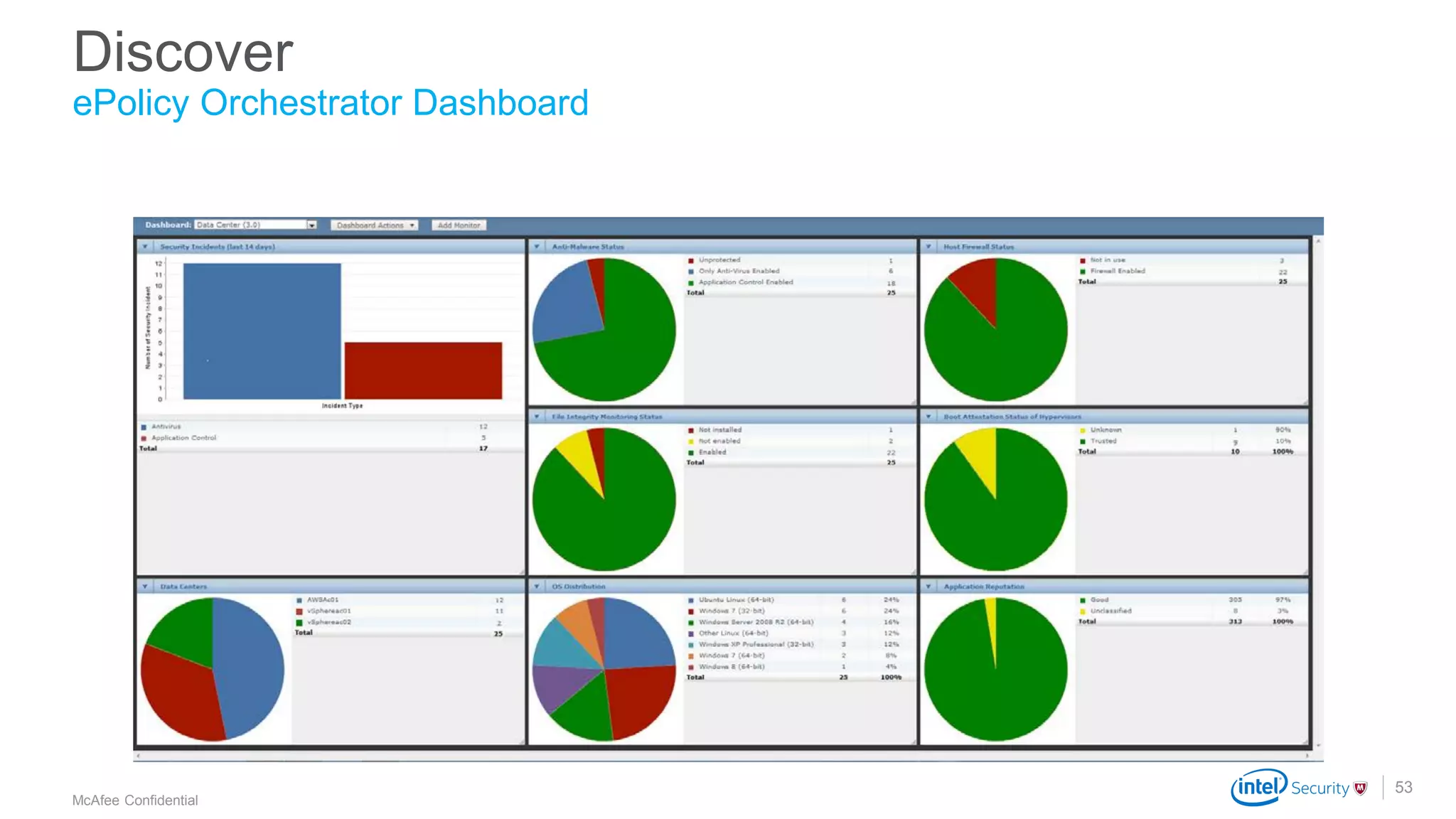
McAfee provides server security solutions to address common customer challenges around securing physical, virtual, and cloud servers. Their solutions help customers discover all server workloads, protect from unknown threats through application control and integrity monitoring, and minimize performance impact while maintaining security. McAfee offers a comprehensive server security portfolio that can be managed from a single console to reduce security management complexity.