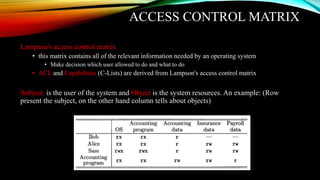
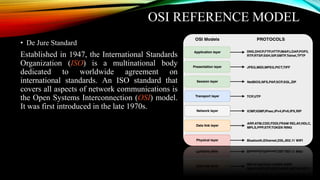
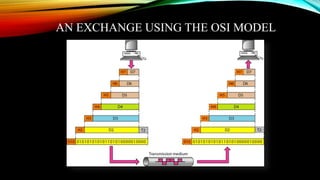
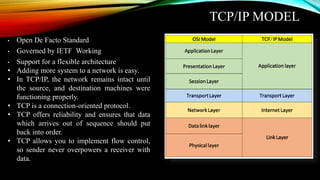
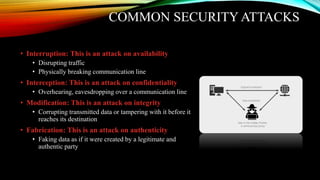
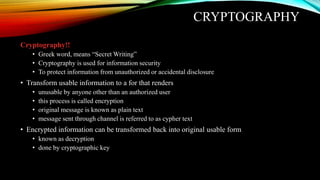
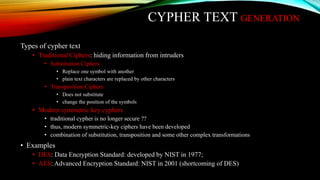
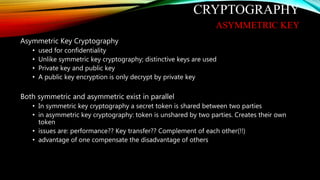
The document outlines an agenda for a cyber security workshop organized by RIGHT Org. It covers topics such as network fundamentals, OSI and TCP/IP models, information security overview and components, common attacks, cryptography, authorization and authentication, firewalls, and hacking tools. The workshop will introduce networking concepts, security threats, cryptography techniques for confidentiality and integrity, and tools for virtual machines, packet tracing, and penetration testing.

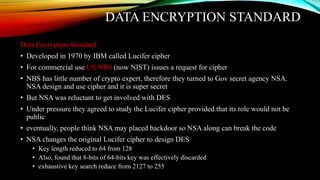
![DES STRUCTURE
• Change was made in Lucifer to involve
substitution box or S-boxes
• 16-round
• 64-bit block length
• 56-bit key
• 48-bit subkey from 56-bit key
• eight S-boxes map 6-bits to
• 4-bits. 48-bits to 32-bits.
• Lookup table
• round function as
• Ri = Li−1⊕[F(Ri−1,Ki) =
P−box(S−boxes(Exapnd(Ri−1)⊕Ki))]
• Li = Ri−1](https://image.slidesharecdn.com/cyber-security-200128133549/85/Cyber-security-25-320.jpg)