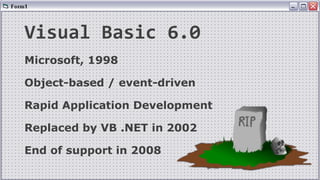
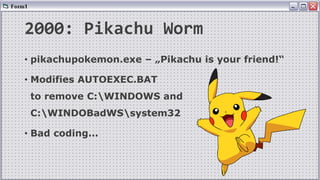
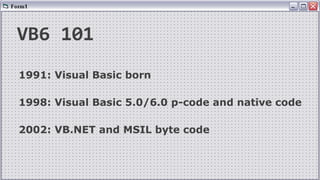
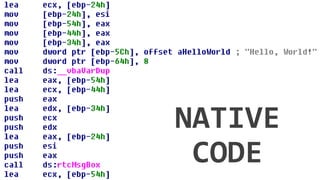
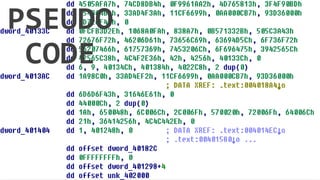
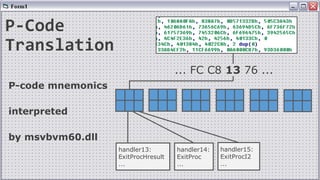
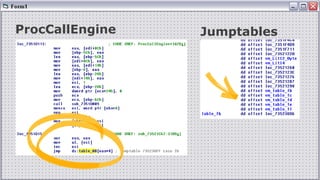
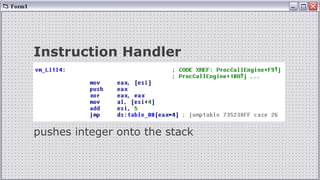
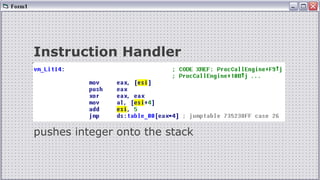
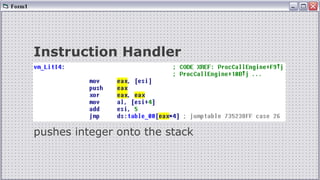
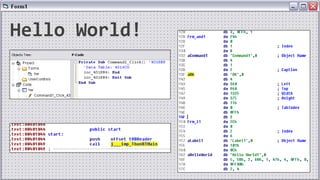
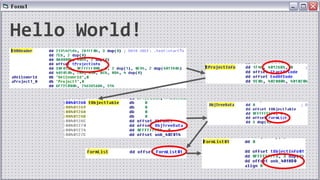
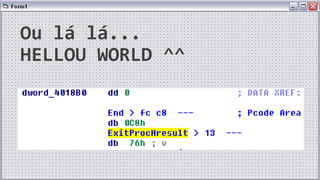
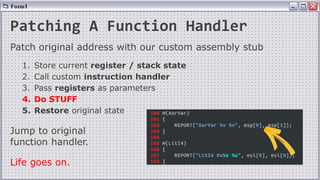
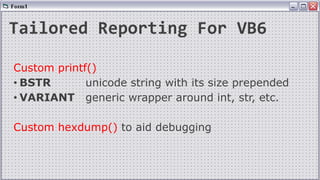
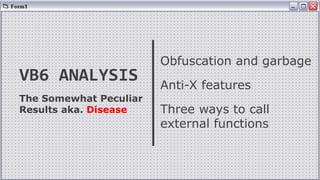
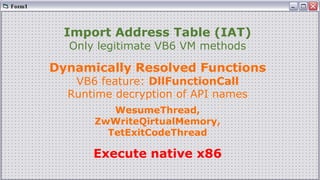
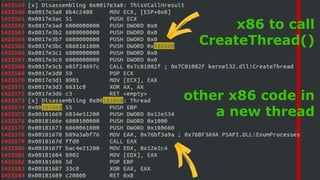
This document discusses analyzing Visual Basic 6 programs. It begins by providing background on VB6 and transitions to discussing challenges with classical analysis approaches. It then outlines approaches for dynamic analysis using instrumentation of the VB6 virtual machine to monitor execution and APIs called. This includes patching jump tables and implementing custom instruction handlers. The goal is to generate tailored reporting and analyze obfuscation techniques in VB6 programs.