This document provides an outline for a Capture the Flag (CTF) event with details on CTF concepts, server setup, and examples of challenges. Some key points:
- It introduces CTFs and the AIS3 final CTF event, which will use a jeopardy style format across categories like Misc, Binary, Pwn, Web, and Crypto.
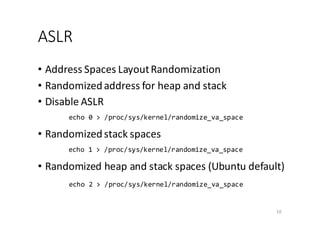
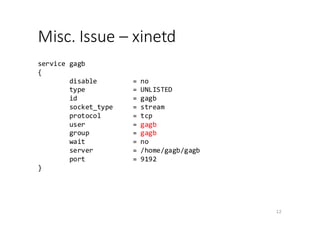
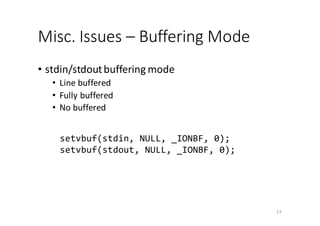
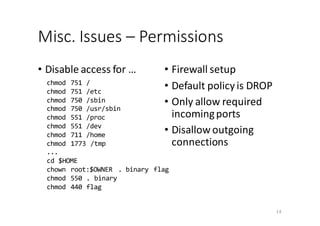
- It provides instructions for setting up a CTF server on Linux with tricks like disabling stack protectors, allowing code execution in the stack, and disabling address space layout randomization (ASLR) to make challenges simpler.
- It outlines some simple initial challenges like a basic buffer overflow example in C, using cryptography, and two pwn
![Simple Buffer Overflow
• Outdated Implementation • Input "A" * 20
7
int func1(int a, int b, int c) {
char buffer[8]; // declare a character array of 8 bytes
gets(buffer); // read user input string
return 0; // return zero
}
buffer[8]
0x00000000
0xffffffff
EBP
ret-addr
a
Stack grows in this way
b
c
Last
Stack Frame Current Stack Frame
......
0x41414141
0x41414141
0x00000000
0xffffffff
0x41414141
0x41414141
0x41414141
Stack grows in this way
b
c
Last
Stack Frame
Current Stack Frame
......](https://image.slidesharecdn.com/ctfhelloworld-151211094614/85/Ctf-hello-world-7-320.jpg)
![Stack Protector
• With Stack Protector • Input "A" * 20
8
buffer[8]
0x00000000
0xffffffff
EBP
ret-addr
a
Stack grows in this way
b
c
Last
Stack Frame
Current Stack Frame
......
Canary (?)
0x41414141
0x41414141
0x00000000
0xffffffff
0x41414141
0x41414141
a
Stack grows in this way
b
c
Last
Stack Frame
Current Stack Frame
......
0x41414141](https://image.slidesharecdn.com/ctfhelloworld-151211094614/85/Ctf-hello-world-8-320.jpg)
![ASLR (Cont’d)
• Without ASLR (0) • With ASLR (1, 2)
11
$ ./a.out
main = 0x80484cd
gets = 0x8048380
buf = 0xffffd3ac
m = 0x804b008
$ ./a.out
main = 0x80484cd
gets = 0x8048380
buf = 0xffffd3ac
m = 0x804b008
$ ./a.out
main = 0x80484cd
gets = 0x8048380
buf = 0xffffd3ac
m = 0x804b008
./a.out
main = 0x80484cd
gets = 0x8048380
buf = 0xffdf6d8c
m = 0x9b03008
$ ./a.out
main = 0x80484cd
gets = 0x8048380
buf = 0xff86930c
m = 0x9b1e008
$ ./a.out
main = 0x80484cd
gets = 0x8048380
buf = 0xfff9b4bc
m = 0x88f3008
char buf[64];
printf("main = %pn", main);
printf("gets = %pn", gets);
printf(" buf = %pn", buf);
printf(" m = %pn", malloc(16));](https://image.slidesharecdn.com/ctfhelloworld-151211094614/85/Ctf-hello-world-11-320.jpg)
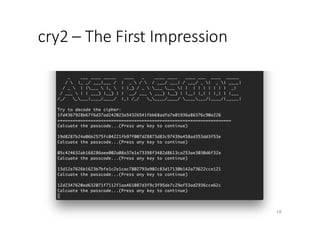
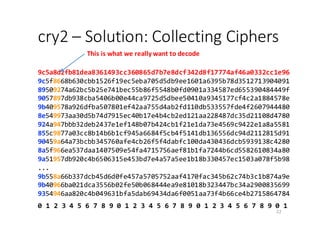
![cry2 – Enumerate All Ciphertexts
24
1: #!/usr/bin/env python
2: from pwn import *
3:
4: #r = remote('54.xxx.yyy.zzz', 5566)
5: r = process("./src.py")
6: ciphers = []
6:
7: while len(ciphers) < 100:
8: s = r.recvline().strip()
9: if len(s) == 64:
10: ciphers.append(s)
11: r.send('n')](https://image.slidesharecdn.com/ctfhelloworld-151211094614/85/Ctf-hello-world-24-320.jpg)
![cry2 – Pseudocodes to Obtain the
XOR-Pad
25
Given c: The list containing n ciphertexts (except the first one)
c = [ c1, c2, c3, …, cn ]
Suppose cu,v represents the vth byte in ciphertext cu, 1 ≤ u ≤ n
pad = "";
for v = 1 to 32:
for x = 0 to 255:
if x XOR cu,v is a lowercase alphabet for all u in [1, n]
pad = pad + x
break
use pad to decrypt the real ciphertext and obtain the flag](https://image.slidesharecdn.com/ctfhelloworld-151211094614/85/Ctf-hello-world-25-320.jpg)
![gagb – The Overflow Part:
Strategy #1 (Cont’d)
35
0x4141...41
0x00000000
0xffffffff
0x41414141
Jump to stack
Stack grows in this way
......
0x90909090
...
...
0x90909090
shellcode
s[24]
0x00000000
0xffffffff
EBP
ret-addr
Stack grows in this way
Last
Stack Frame
Current Stack Frame
......](https://image.slidesharecdn.com/ctfhelloworld-151211094614/85/Ctf-hello-world-35-320.jpg)
![gagb – The Overflow Part:
Strategy #2 (2/3)
• We want the stack to looks like …
37
s[24]
0x00000000
0xffffffff
EBP
addr of gets()
Stack grows in this way
......
ret-addr
argument #1
return addr after gets()
address for gets() to fill
garbage](https://image.slidesharecdn.com/ctfhelloworld-151211094614/85/Ctf-hello-world-37-320.jpg)
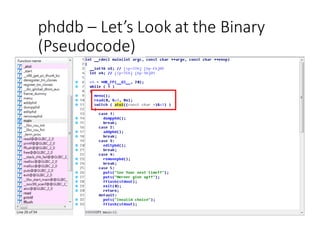
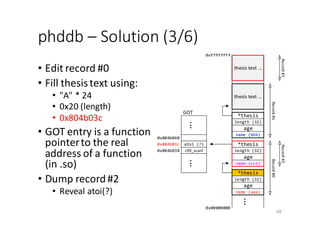
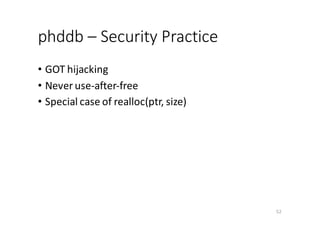
![phddb – Feature Summary
• Data stored in heap – use malloc()
• dump
• add
• Allocate header first (32 bytes)
• Allocate thesis-text according to
the given length
• edit
• Modify header content
• Reallocate thesis-text if necessary
• remove
44
thesis text ...
thesis text ...
......
0x00000000
0xffffffff
name[20]
age
length
*thesis
name[20]
age
length
*thesis
Record #0Record #1](https://image.slidesharecdn.com/ctfhelloworld-151211094614/85/Ctf-hello-world-44-320.jpg)