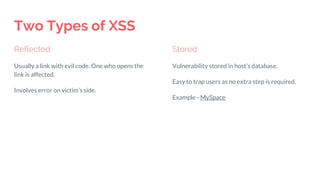
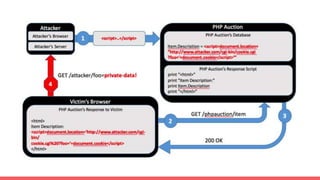
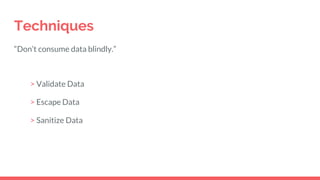
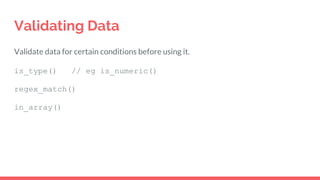
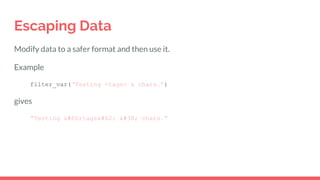
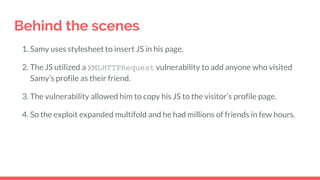
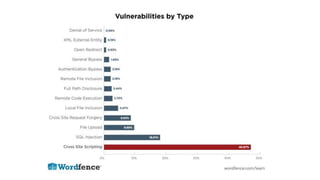
Cross-site scripting (XSS) is a type of computer security vulnerability that enables attackers to inject client-side scripts into web pages viewed by other users. There are two types: reflected XSS involves including malicious code in a URL link, while stored XSS embeds malicious code directly into a website database. To prevent XSS attacks, developers should validate, escape, and sanitize all user input before displaying it. For example, by filtering HTML tags and encoding special characters. An infamous example is a 2005 MySpace XSS worm that spread to millions of users by automatically adding anyone who visited an infected profile as a friend.
![Simple vulnerability
<?php
echo "The value you entered is: " . $_GET['val'];
?>
User: https://example.com/test.php?val=123
Hacker: https://example.com/test.php?val=<script>alert(‘Hacked’)</script>](https://image.slidesharecdn.com/xvqddpyvrxmjtzrsb0fo-signature-1e3daa3c65278befa10fad062b0148d44a91517ecef022145f0a1e4a7140bdc9-poli-170406204800/85/Cross-Site-Scripting-XSS-4-320.jpg)