Configuring and installing add in modules for the fi-6010N
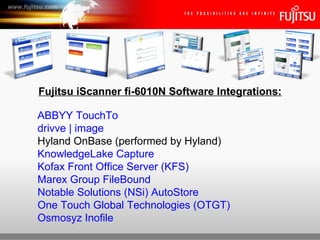
- 1. Fujitsu iScanner fi-6010N Software Integrations: ABBYY TouchTo drivve | image Hyland OnBase (performed by Hyland) KnowledgeLake Capture Kofax Front Office Server (KFS) Marex Group FileBound Notable Solutions (NSi) AutoStore One Touch Global Technologies (OTGT) Osmosyz Inofile Fujitsu iScanner fi-6010N Network Scanner
- 2. TouchTo combines the latest OCR technology with the Fujitsu touchscreen system to simplify the document management process by reducing the multiple steps required to get fields from scanned documents into backend systems. Anyone scanning a document can route data capture and metadata extraction results into applications from the scanning entry point. The technology has been KFSigned so that anyone capable of operating a scanner is able to use this solution to capture paper-bound documents and data fields within those documents straight into archive, document management and accounting systems. Prior to the release, data extraction was performed on a separate PC, requiring one or more operators to input documents and process them in separate steps. Or, if data extraction were to be performed at the scanner, keystroking was required. With TouchTo, data extraction is performed by simply tapping on a word or number as the document is displayed on the scanner’s LCD screen. Fujitsu iScanner fi-6010N Network Scanner
- 3. iScanner Central Admin Console • Launch iScanner Central Admin Console Fujitsu iScanner fi-6010N Network Scanner
- 4. iScanner Central Admin Console • Specify the IP address, host name, or FQDN of the target server Fujitsu iScanner fi-6010N Network Scanner
- 5. iScanner Central Admin Console • iScanner Central Admin Console login screen Fujitsu iScanner fi-6010N Network Scanner
- 6. iScanner Central Admin Console • Enter User Name and Password, then press the Login button Fujitsu iScanner fi-6010N Network Scanner
- 7. Central Admin (Add-in Installs) • iScanner Central Admin Console Main Menu, Select “Add-In Installs” link Fujitsu iScanner fi-6010N Network Scanner
- 8. Central Admin (Add-in Installs) • Select Add-in Group from Add-in Installs Fujitsu iScanner fi-6010N Network Scanner
- 9. Central Admin (Add-in Installs) • Browse to the Add-in Module, highlight then press the Open button Fujitsu iScanner fi-6010N Network Scanner
- 10. Central Admin (Add-in Installs) • Press the Upload button to Upload the Add-in Module to the CAS Fujitsu iScanner fi-6010N Network Scanner
- 11. Central Admin (Add-in Installs) • Uploading… Fujitsu iScanner fi-6010N Network Scanner
- 12. Central Admin (Add-in Installs) • Check the “Issue an Update Call” checkbox then the Register button Fujitsu iScanner fi-6010N Network Scanner
- 13. Central Admin (Add-in Installs) • New Add-in module has been uploaded and is now available Fujitsu iScanner fi-6010N Network Scanner
- 14. ABBYY TouchTo configuration • Press the ABBYY TouchTo button Fujitsu iScanner fi-6010N Network Scanner
- 15. ABBYY TouchTo configuration • ABBYY TouchTo Scan Viewer. Press the Settings… button Fujitsu iScanner fi-6010N Network Scanner
- 16. ABBYY TouchTo configuration • TouchTo/SharePoint configuration. Press the SharePoint settings button Fujitsu iScanner fi-6010N Network Scanner
- 17. ABBYY TouchTo configuration • Enter the Server name or IP of a SharePoint Server and enter credentials v Fujitsu iScanner fi-6010N Network Scanner
- 18. ABBYY TouchTo configuration • ABBYY TouchTo/Network Folder. Press the Network folder settings button Fujitsu iScanner fi-6010N Network Scanner
- 19. ABBYY TouchTo configuration • Enter Path to network folder, Document types and Fields Fujitsu iScanner fi-6010N Network Scanner
- 20. ABBYY TouchTo configuration • Adding a new Field to Document types Fujitsu iScanner fi-6010N Network Scanner
- 21. ABBYY TouchTo configuration • Enter Field Name Fujitsu iScanner fi-6010N Network Scanner
- 22. ABBYY TouchTo configuration • New Field appears Fujitsu iScanner fi-6010N Network Scanner
- 23. ABBYY TouchTo configuration Fujitsu iScanner fi-6010N Network Scanner
- 24. A flexible, customizable suite of tools for the Fujitsu® fi-6010N Network Scanner. drivve | Image is turbocharged scanning software that makes that jump as easy as putting on your blinker. By bringing together seven feature-rich, customizable modules that are highly intelligent and ridiculously user-friendly, D | I turns your Fujitsu fi-6010N network scanner into an exceptionally integrative workflow engine. In fact, D | I transforms your entire network of input devices into a responsive, finely tuned programmable ignition system for these workflows. And with its simple installation and easy configuration, everyone in your organization can accelerate to full-blown office synchronization — to office automation that puts the force back in workforce. Fujitsu iScanner fi-6010N Network Scanner
- 25. iScanner Central Admin Console • Launch iScanner Central Admin Console Fujitsu iScanner fi-6010N Network Scanner
- 26. iScanner Central Admin Console • Specify the IP address, host name, or FQDN of the target server Fujitsu iScanner fi-6010N Network Scanner
- 27. iScanner Central Admin Console • iScanner Central Admin Console login screen Fujitsu iScanner fi-6010N Network Scanner
- 28. iScanner Central Admin Console • Enter User Name and Password, then press the Login button Fujitsu iScanner fi-6010N Network Scanner
- 29. Central Admin (Add-in Installs) • iScanner Central Admin Console Main Menu, Select “Add-In Installs” link Fujitsu iScanner fi-6010N Network Scanner
- 30. Central Admin (Add-in Installs) / drivve | image • Select target Add-In Group Fujitsu iScanner fi-6010N Network Scanner
- 31. Central Admin (Add-in Installs) / drivve | image • Browse to Add-In Module file (i.e. DrivveImage.fi6010n) then Open button Fujitsu iScanner fi-6010N Network Scanner
- 32. Central Admin (Add-in Installs) / drivve | image • Uploading… Fujitsu iScanner fi-6010N Network Scanner
- 33. Central Admin (Add-in Installs) / drivve | image • Issue an Update Call then press Register button Fujitsu iScanner fi-6010N Network Scanner
- 34. Central Admin (Add-in Installs) / drivve | image • New Add-in module is now available for scanners to install Fujitsu iScanner fi-6010N Network Scanner
- 35. Central Admin (Add-in Installs) / drivve | image • Registered Add-in Module, Version and Release Date Fujitsu iScanner fi-6010N Network Scanner
- 36. Central Admin (Add-in Installs) / drivve | image • Add-In Module being installed on fi-6010N’s. Scanner restarts. Fujitsu iScanner fi-6010N Network Scanner
- 37. drivve | image configuration • Start drivve | image applications Fujitsu iScanner fi-6010N Network Scanner
- 38. drivve | image configuration • Choose Tools, then Fujitsu Device Management Fujitsu iScanner fi-6010N Network Scanner
- 39. drivve | image configuration • Enter IP Address of fi-6010N scanner Fujitsu iScanner fi-6010N Network Scanner
- 40. drivve | image configuration • After entering IP Address of scanner then press Connect button Fujitsu iScanner fi-6010N Network Scanner
- 41. drivve | image configuration • MAC address is automatically retrieved, enter Model then press OK Fujitsu iScanner fi-6010N Network Scanner
- 42. drivve | image configuration • Serial Number and Model are now registered with drivve | image Fujitsu iScanner fi-6010N Network Scanner
- 43. fi-6010N/drivve | image configuration • Fujitsu fi-6010N Login screen Fujitsu iScanner fi-6010N Network Scanner
- 44. fi-6010N/drivve | image configuration • Enter User Name Fujitsu iScanner fi-6010N Network Scanner
- 45. fi-6010N/drivve | image configuration • Enter Password Fujitsu iScanner fi-6010N Network Scanner
- 46. fi-6010N/drivve | image configuration • Press drivve | image Add-In button Fujitsu iScanner fi-6010N Network Scanner
- 47. fi-6010N/drivve | image configuration • Enter your Drivve Image server url Fujitsu iScanner fi-6010N Network Scanner
- 48. fi-6010N/drivve | image configuration • drivve | image configuration screen Fujitsu iScanner fi-6010N Network Scanner
- 49. fi-6010N/drivve | image configuration • Enter IP address of drivve | image server, enter port number, then save Fujitsu iScanner fi-6010N Network Scanner
- 50. fi-6010N/drivve | image configuration • Connecting server. Fujitsu iScanner fi-6010N Network Scanner
- 51. fi-6010N/drivve | image configuration • Fujitsu fi-6010N Login screen Fujitsu iScanner fi-6010N Network Scanner
- 52. fi-6010N/drivve | image configuration • Enter User Name Fujitsu iScanner fi-6010N Network Scanner
- 53. fi-6010N/drivve | image configuration • Enter Password Fujitsu iScanner fi-6010N Network Scanner
- 54. fi-6010N/drivve | image configuration • Press drivve | image Add-In button Fujitsu iScanner fi-6010N Network Scanner
- 55. fi-6010N/drivve | image configuration •drivve | image profiles Fujitsu iScanner fi-6010N Network Scanner
- 56. KnowledgeLake Capture for the Fujitsu fi-6010N iScanner enables users to scan directly to Microsoft Office SharePoint Server (MOSS) or Windows SharePoint Services (WSS) with corresponding meta-data for each document. The integration enables users to scan directly to e-mail, to a network folder or to a printer. In addition, the documents can be converted to TIFF, PDF, Searchable PDF or JPEG before stored in SharePoint. The Fujitsu fi-6010N iScanner coupled with KnowledgeLake Capture proviKFS added simplicity, enhanced security and encryption features, a network control utility and an upgraded user interface to further assist collaboration across a global network. The web based centralized control utility allows network administrators to assign scanning profiles to users or groups of users and enables remote delivery of software updates. Fujitsu iScanner fi-6010N Network Scanner
- 57. iScanner Central Admin Console • Launch iScanner Central Admin Console Fujitsu iScanner fi-6010N Network Scanner
- 58. iScanner Central Admin Console • Specify the IP address, host name, or FQDN of the target server Fujitsu iScanner fi-6010N Network Scanner
- 59. iScanner Central Admin Console • iScanner Central Admin Console login screen Fujitsu iScanner fi-6010N Network Scanner
- 60. iScanner Central Admin Console • Enter User Name and Password, then press the Login button Fujitsu iScanner fi-6010N Network Scanner
- 61. Central Admin (Add-in Installs) • iScanner Central Admin Console Main Menu, Select “Add-In Installs” link Fujitsu iScanner fi-6010N Network Scanner
- 62. Central Admin (Add-in Installs) / KnowledgeLake Capture • Select the KFSired Add-in Group from the Add-in Installs list, then Browse Fujitsu iScanner fi-6010N Network Scanner
- 63. Central Admin (Add-in Installs) / KnowledgeLake Capture • Browse to the Add-in Module to Upload to the CAS, then Open Fujitsu iScanner fi-6010N Network Scanner
- 64. Central Admin (Add-in Installs) / KnowledgeLake Capture • Uploading… Fujitsu iScanner fi-6010N Network Scanner
- 65. Central Admin (Add-in Installs) / KnowledgeLake Capture • Check the “Issue an Update Call” checkbox then the Register button Fujitsu iScanner fi-6010N Network Scanner
- 66. Central Admin (Add-in Installs) / KnowledgeLake Capture • New Add-in module has been uploaded and is now available Fujitsu iScanner fi-6010N Network Scanner
- 67. Central Admin (Add-in Installs) / KnowledgeLake Capture • Update is being installed from Central Admin server (fi-6010N screen) Fujitsu iScanner fi-6010N Network Scanner
- 68. KnowledgeLake Capture Add-In Configuration • Fujitsu fi-6010N Login screen Fujitsu iScanner fi-6010N Network Scanner
- 69. KnowledgeLake Capture Add-In Configuration • Enter User Name Fujitsu iScanner fi-6010N Network Scanner
- 70. KnowledgeLake Capture Add-In Configuration • Enter Password Fujitsu iScanner fi-6010N Network Scanner
- 71. KnowledgeLake Capture Add-In Configuration • Press KnowledgeLake Capture button Fujitsu iScanner fi-6010N Network Scanner
- 72. KnowledgeLake Capture Add-In Configuration • Uncheck Auto Folder checkbox unless you want to use this feature Fujitsu iScanner fi-6010N Network Scanner
- 73. KnowledgeLake Capture Add-In Configuration • Select SharePoint, enter URL then press Service Credentials button Fujitsu iScanner fi-6010N Network Scanner
- 74. KnowledgeLake Capture Add-In Configuration • SharePoint Server Credentials Fujitsu iScanner fi-6010N Network Scanner
- 75. KnowledgeLake Capture Add-In Configuration • Enter User Name, Password and Domain for SharePoint Server Fujitsu iScanner fi-6010N Network Scanner
- 76. KnowledgeLake Capture Add-In Configuration • Press OK button Fujitsu iScanner fi-6010N Network Scanner
- 77. KnowledgeLake Capture Add-In Configuration • SharePoint Servers available Fujitsu iScanner fi-6010N Network Scanner
- 78. KnowledgeLake Capture Add-In Configuration • General KnowledgeLake Main Screen Fujitsu iScanner fi-6010N Network Scanner
- 79. KnowledgeLake Capture Add-In Configuration • Select a Location Fujitsu iScanner fi-6010N Network Scanner
- 80. KnowledgeLake Capture Add-In Configuration • Highlight SharePoint Server Fujitsu iScanner fi-6010N Network Scanner
- 81. KnowledgeLake Capture Add-In Configuration • Expand selection Fujitsu iScanner fi-6010N Network Scanner
- 82. KnowledgeLake Capture Add-In Configuration • Select KFSire Location (i.e. Document Center) Fujitsu iScanner fi-6010N Network Scanner
- 83. KnowledgeLake Capture Add-In Configuration • Expand Location Fujitsu iScanner fi-6010N Network Scanner
- 84. KnowledgeLake Capture Add-In Configuration • Select Document Type Fujitsu iScanner fi-6010N Network Scanner
- 85. KnowledgeLake Capture Add-In Configuration • Press Add button to make this Document Type available Fujitsu iScanner fi-6010N Network Scanner
- 86. KnowledgeLake Capture Add-In Configuration • Select additional Document Types to add Fujitsu iScanner fi-6010N Network Scanner
- 87. KnowledgeLake Capture Add-In Configuration • Press Add button to make additional Document Types available Fujitsu iScanner fi-6010N Network Scanner
- 88. KnowledgeLake Capture Add-In Configuration • Select additional Document Types Fujitsu iScanner fi-6010N Network Scanner
- 89. KnowledgeLake Capture Add-In Configuration • Press Add button to make additional Document Types available Fujitsu iScanner fi-6010N Network Scanner
- 90. KnowledgeLake Capture Add-In Configuration • KnowledgeLake Capture – Enter Index Information screen Fujitsu iScanner fi-6010N Network Scanner
- 91. Office Automation Kofax Front Office Server enables customer facing employees to trigger back office, business processes directly from familiar, front office equipment such as digital copiers and KFSktop scanners. Employees start processes with a few clicks at the digital copier or thin client scan application. This office automation solution reduces the days required to ship paper into just minutes via electronic transmission. Time spent shuffling, tracking, and filing that paper is replaced by customer facing activities. This increased responsiveness and front office contact combine to produce superior customer service and reduce operational costs. With Kofax office automation solutions you can: • Speed up document-driven business processes by capturing documents in the front office, where they originate, and quickly deliver them to the systems that automate business processes. • Empower front office employees to scan documents without training and leverage additional functionality to improve user efficiency. • Improve compliance efforts by tracking chain of custody from the point where a document enters a workflow to the final disposition in a back-office application. • Easily deploy a front office based document capture and routing system with centralized management. • Standardize on a single-vendor for document capture, collaboration and routing. • Extend existing Kofax Capture workflows directly to the front office user. Fujitsu iScanner fi-6010N Network Scanner Fujitsu iScanner fi-6010N Network Scanner
- 92. iScanner Central Admin Console • Launch iScanner Central Admin Console Fujitsu iScanner fi-6010N Network Scanner
- 93. iScanner Central Admin Console • Specify the IP address, host name, or FQDN of the target server Fujitsu iScanner fi-6010N Network Scanner
- 94. iScanner Central Admin Console • iScanner Central Admin Console login screen Fujitsu iScanner fi-6010N Network Scanner
- 95. iScanner Central Admin Console • Enter User Name and Password, then press the Login button Fujitsu iScanner fi-6010N Network Scanner
- 96. Central Admin Server (Add-in Installs) • iScanner Central Admin Console Main Menu, Select “Add-In Installs” link Fujitsu iScanner fi-6010N Network Scanner
- 97. fi-6010N / Kofax KFS (Add-In Install) • Central Administration Server - Add-In Installs Fujitsu iScanner fi-6010N Network Scanner
- 98. fi-6010N / Kofax KFS (Add-In Install) • Select Add-in Group from Add-in Installs Fujitsu iScanner fi-6010N Network Scanner
- 99. fi-6010N / Kofax KFS (Add-In Install) • Browse to Add-in Module to Upload Fujitsu iScanner fi-6010N Network Scanner
- 100. fi-6010N / Kofax KFS (Add-In Install) • Press Upload button Fujitsu iScanner fi-6010N Network Scanner
- 101. fi-6010N / Kofax KFS (Add-In Install) • Uploading… Fujitsu iScanner fi-6010N Network Scanner
- 102. fi-6010N / Kofax KFS (Add-In Install) • Check the “Issue an Update Call” checkbox then press Register button Fujitsu iScanner fi-6010N Network Scanner
- 103. fi-6010N / Kofax KFS (Add-In Install) • New Add-in Module has been uploaded and is now available Fujitsu iScanner fi-6010N Network Scanner
- 104. fi-6010N / Kofax KFS (Add-In Install) • Kofax KFS Add-in Module (Released) Fujitsu iScanner fi-6010N Network Scanner
- 105. fi-6010N / Kofax KFS (Add-In Install) • Fujitsu fi-6010N Login screen Fujitsu iScanner fi-6010N Network Scanner
- 106. fi-6010N / Kofax KFS (Add-In Install) • Enter User Name Fujitsu iScanner fi-6010N Network Scanner
- 107. fi-6010N / Kofax KFS (Add-In Install) • Enter Password Fujitsu iScanner fi-6010N Network Scanner
- 108. fi-6010N / Kofax KFS (Add-In Install) • Press the Kofax KFS button Fujitsu iScanner fi-6010N Network Scanner
- 109. fi-6010N / Kofax KFS (Add-In Install) • Launch KFS and Change Server Host Fujitsu iScanner fi-6010N Network Scanner
- 110. fi-6010N / Kofax KFS (Add-In Install) • Press the Change Server Host button Fujitsu iScanner fi-6010N Network Scanner
- 111. fi-6010N / Kofax KFS (Add-In Install) • KFS Server Host Setting Fujitsu iScanner fi-6010N Network Scanner
- 112. fi-6010N / Kofax KFS (Add-In Install) • Enter new KFS host (name or IP), enter Port number and press OK Fujitsu iScanner fi-6010N Network Scanner
- 113. fi-6010N / Kofax KFS (Add-In Install) • Press the Launch Kofax KFS button Fujitsu iScanner fi-6010N Network Scanner
- 114. Kofax Front Office Server (KFS) • Kofax KFS Main Menu Fujitsu iScanner fi-6010N Network Scanner
- 115. Kofax Front Office Server (KFS) • Choose “KDE Inbox” button Fujitsu iScanner fi-6010N Network Scanner
- 116. Kofax Front Office Server (KFS) • Enter User Name of KFS user Inbox Fujitsu iScanner fi-6010N Network Scanner
- 117. Kofax Front Office Server (KFS) • Enter User Name of KFS user Inbox then press “Scan” button Fujitsu iScanner fi-6010N Network Scanner
- 118. Kofax Front Office Server (KFS) • Scanning… Fujitsu iScanner fi-6010N Network Scanner
- 119. Kofax Front Office Server (KFS) • Kofax KFS Scan Viewer Fujitsu iScanner fi-6010N Network Scanner
- 120. The FileBound onboard capture integration allows users to control all the document scanning and indexing processes directly from the scanner panel. Users need only to load their documents into the scanner, select where within FileBound they want to store them, enter the index information, scan the documents and automatically save them into a local or remote FileBound system. The FileBound integrated capture software for the fi-6010N proviKFS a complete, out-of-the-box content management solution without any additional hardware of software requirements. Fujitsu iScanner fi-6010N Network Scanner
- 121. iScanner Central Admin Console • Launch iScanner Central Admin Console Fujitsu iScanner fi-6010N Network Scanner
- 122. iScanner Central Admin Console • Specify the IP address, host name, or FQDN of the target server Fujitsu iScanner fi-6010N Network Scanner
- 123. iScanner Central Admin Console • iScanner Central Admin Console login screen Fujitsu iScanner fi-6010N Network Scanner
- 124. iScanner Central Admin Console • Enter User Name and Password, then press the Login button Fujitsu iScanner fi-6010N Network Scanner
- 125. Central Admin Server (Add-in Installs) • iScanner Central Admin Console Main Menu, Select “Add-In Installs” link Fujitsu iScanner fi-6010N Network Scanner
- 126. fi-6010N / Marex FileBound (Add-In Install) • Central Administration Server - Add-In Installs Fujitsu iScanner fi-6010N Network Scanner
- 127. fi-6010N / Marex FileBound (Add-In Install) • Select the Add-in Group from Add-in Installs Fujitsu iScanner fi-6010N Network Scanner
- 128. fi-6010N / Marex FileBound (Add-In Install) • Browse to the Add-in Module then press the Open button Fujitsu iScanner fi-6010N Network Scanner
- 129. fi-6010N / Marex FileBound (Add-In Install) • Press the Upload button to Upload the Add-in Module to the CAS Fujitsu iScanner fi-6010N Network Scanner
- 130. fi-6010N / Marex FileBound (Add-In Install) • Check the “Issue an Update Call” checkbox then press the Register button Fujitsu iScanner fi-6010N Network Scanner
- 131. fi-6010N / Marex FileBound (Add-In Install) • New Add-in module has been uploaded and is now available Fujitsu iScanner fi-6010N Network Scanner
- 132. fi-6010N / Marex FileBound (Add-In Install) • FileBound Add-in module has been released and is available on the CAS Fujitsu iScanner fi-6010N Network Scanner
- 133. fi-6010N / Marex FileBound (Add-In Install) • Fujitsu fi-6010N Login screen Fujitsu iScanner fi-6010N Network Scanner
- 134. fi-6010N / Marex FileBound (Add-In Install) • Enter User Name Fujitsu iScanner fi-6010N Network Scanner
- 135. fi-6010N / Marex FileBound (Add-In Install) • Enter Password Fujitsu iScanner fi-6010N Network Scanner
- 136. fi-6010N / Marex FileBound (Add-In Install) • Main Menu Fujitsu iScanner fi-6010N Network Scanner
- 137. fi-6010N / Marex FileBound (Add-In Install) • Press the FileBound button Fujitsu iScanner fi-6010N Network Scanner
- 138. fi-6010N / Marex FileBound (Add-In Install) • FileBound iScanner fi-6010N Add-in Module configuration screen Fujitsu iScanner fi-6010N Network Scanner
- 139. fi-6010N / Marex FileBound (Add-In Install) • Enter the FileBound Server URL, User Name and Password. Press Login Fujitsu iScanner fi-6010N Network Scanner
- 140. fi-6010N / Marex FileBound (Add-In Install) • FileBound available Projects Fujitsu iScanner fi-6010N Network Scanner
- 141. fi-6010N / Marex FileBound (Add-In Install) • Select a Project from the FileBound Project list Fujitsu iScanner fi-6010N Network Scanner
- 142. fi-6010N / Marex FileBound (Add-In Install) • Enter index data then press the Scan button Fujitsu iScanner fi-6010N Network Scanner
- 143. fi-6010N / Marex FileBound (Add-In Install) • Scanning… Fujitsu iScanner fi-6010N Network Scanner
- 144. fi-6010N / Marex FileBound (Add-In Install) • FileBound Scan Viewer Fujitsu iScanner fi-6010N Network Scanner
- 145. AutoStore is a full-service document capture software for companies that want to better manage their paper and electronic documents while improving productivity, security and compliance. Capture. Process. Route. Capture print or electronic documents, process them into various digitized formats and then route them to virtually any KFStination. Fujitsu iScanner fi-6010N Network Scanner
- 146. fi-6010N / NSi AutoStore (Add-In Install) • Launch fi Network Scanner Admin Tool Fujitsu iScanner fi-6010N Network Scanner
- 147. fi-6010N / NSi AutoStore (Add-In Install) • Enter IP address, scanner name, or FQDN of target fi-6010N then Connect Fujitsu iScanner fi-6010N Network Scanner
- 148. fi-6010N / NSi AutoStore (Add-In Install) • fi Network Scanner Admin Tool - Login Fujitsu iScanner fi-6010N Network Scanner
- 149. fi-6010N / NSi AutoStore (Add-In Install) • Enter “admin” as the User Name Fujitsu iScanner fi-6010N Network Scanner
- 150. fi-6010N / NSi AutoStore (Add-In Install) • Enter “password” as the Password, unless changed Fujitsu iScanner fi-6010N Network Scanner
- 151. fi-6010N / NSi AutoStore (Add-In Install) • fi Network Scanner Admin Tool – Main Screen Fujitsu iScanner fi-6010N Network Scanner
- 152. fi-6010N / NSi AutoStore (Add-In Install) • Choose the Maintenance tab, then Add-In Manager Fujitsu iScanner fi-6010N Network Scanner
- 153. fi-6010N / NSi AutoStore (Add-In Install) • Browse to the NSi AutoStore Add-In Module Fujitsu iScanner fi-6010N Network Scanner
- 154. fi-6010N / NSi AutoStore (Add-In Install) • Highlight the file (i.e. AddinModule05.00.03.00003.cab), then Open button Fujitsu iScanner fi-6010N Network Scanner
- 155. fi-6010N / NSi AutoStore (Add-In Install) • Press Install button to begin installation Fujitsu iScanner fi-6010N Network Scanner
- 156. fi-6010N / NSi AutoStore (Add-In Install) • Click OK to begin installation. Scanner will need to reboot Fujitsu iScanner fi-6010N Network Scanner
- 157. fi-6010N / NSi AutoStore (Add-In Install) • Installing… Fujitsu iScanner fi-6010N Network Scanner
- 158. fi-6010N / NSi AutoStore (Add-In Install) • Scanner reboots. Disconnect fi Network Scanner Admin Tool. Fujitsu iScanner fi-6010N Network Scanner
- 159. NSi AutoStore Add-In Configuration • fi-6010N Login screen Fujitsu iScanner fi-6010N Network Scanner
- 160. NSi AutoStore Add-In Configuration • Enter “as-maintenance” as User Name Fujitsu iScanner fi-6010N Network Scanner
- 161. NSi AutoStore Add-In Configuration • Enter “as-scanner6-maintenance” as the Password Fujitsu iScanner fi-6010N Network Scanner
- 162. NSi AutoStore Add-In Configuration • Press the “Maintenance” button Fujitsu iScanner fi-6010N Network Scanner
- 163. NSi AutoStore Add-In Configuration • NSi AutoStore Connection Properties Fujitsu iScanner fi-6010N Network Scanner
- 164. NSi AutoStore Add-In Configuration • Enter AutoStore Server Address Fujitsu iScanner fi-6010N Network Scanner
- 165. NSi AutoStore Add-In Configuration • Press Cancel button Fujitsu iScanner fi-6010N Network Scanner
- 166. NSi AutoStore Add-In Configuration • Fujitsu fi-6010N Login screen Fujitsu iScanner fi-6010N Network Scanner
- 167. NSi AutoStore Add-In Configuration • Enter User Name Fujitsu iScanner fi-6010N Network Scanner
- 168. NSi AutoStore Add-In Configuration • Enter Password Fujitsu iScanner fi-6010N Network Scanner
- 169. NSi AutoStore Add-In Configuration • NSi AutoStore Main Menu Fujitsu iScanner fi-6010N Network Scanner
- 170. One Touch Integration Server + Fujitsu fi-6010N = Infinite Opportunities. The Fujitsu fi-6010N integrated with the One Touch Integration Server (OTIS) will empower organization business processes, reduce your total cost of ownership (TCO), improve document communication and delivery between departments, applications, vendors and more. • RightFax enable the Fujitsu fi-6010N. Use native RightFax phone books, cover pages, library documents, customizable topics and billcoKFS. • Leverage existing Windows-based security infrastructure for compliance and network security purposes. • Deliver scanned documents directly to one or more KFStinations simultaneously including: Document Management Systems, Enterprise Content Management Systems (ECM), email, network folder, FTP and fax machine. • Perform Bates Stamping, 1D, 2D bar coKFS stamping, 1D, 2D barcode recognition. • Create intelligent cover pages using 1D/2D bar coKFS. • Incorporate XML metadata creation, delivery and indexing. • Obtain devise Usage Reports for bill back purposes categorized by user, department or document communication method. Fujitsu iScanner fi-6010N Network Scanner
- 171. iScanner Central Admin Console • Launch iScanner Central Admin Console Fujitsu iScanner fi-6010N Network Scanner
- 172. iScanner Central Admin Console • Specify the IP address, host name, or FQDN of the target server Fujitsu iScanner fi-6010N Network Scanner
- 173. iScanner Central Admin Console • iScanner Central Admin Console login screen Fujitsu iScanner fi-6010N Network Scanner
- 174. iScanner Central Admin Console • Enter User Name and Password, then press the Login button Fujitsu iScanner fi-6010N Network Scanner
- 175. Central Admin OTGT (Add-in Installs) • iScanner Central Admin Console Main Menu, Select “Add-In Installs” link Fujitsu iScanner fi-6010N Network Scanner
- 176. Central Admin OTGT (Add-in Installs) • iScanner Central Admin Console, Add-in Installs Fujitsu iScanner fi-6010N Network Scanner
- 177. Central Admin OTGT (Add-in Installs) • Select Add-in Group to Upload Add-In Module Fujitsu iScanner fi-6010N Network Scanner
- 178. Central Admin OTGT (Add-in Installs) • Browse to Add-in Module to Upload Fujitsu iScanner fi-6010N Network Scanner
- 179. Central Admin OTGT (Add-in Installs) • Press Upload button to transfer Add-in Module Fujitsu iScanner fi-6010N Network Scanner
- 180. Central Admin OTGT (Add-in Installs) • Uploading… Fujitsu iScanner fi-6010N Network Scanner
- 181. Central Admin OTGT (Add-in Installs) • Check the Issue an Update Call box then press the Register button Fujitsu iScanner fi-6010N Network Scanner
- 182. Central Admin OTGT (Add-in Installs) • New Add-in module has been uploaded and is now available Fujitsu iScanner fi-6010N Network Scanner
- 183. Central Admin OTGT (Add-in Installs) • Add-in Module has been Released to Add-in Group Fujitsu iScanner fi-6010N Network Scanner
- 184. Central Admin OTGT (Add-in Installs) • Add-In Module being installed on fi-6010N’s. Scanner restarts. Fujitsu iScanner fi-6010N Network Scanner
- 185. One Touch Global Technologies (OTGT) • Login to One Touch Global. Press the “More…” button Fujitsu iScanner fi-6010N Network Scanner
- 186. One Touch Global Technologies (OTGT) • One Touch Global Technologies OTIS configuration Fujitsu iScanner fi-6010N Network Scanner
- 187. One Touch Global Technologies (OTGT) • Enter One Touch Global OTIS information Fujitsu iScanner fi-6010N Network Scanner
- 188. One Touch Global Technologies (OTGT) • Press the “More…” button Fujitsu iScanner fi-6010N Network Scanner
- 189. One Touch Global Technologies (OTGT) • Select from menu of OTGT/OTIS workflows and KFStinations Fujitsu iScanner fi-6010N Network Scanner
- 190. InofileTM Paperless is a pipedream, but Fileless is not. You can remove the paper at the beginning of any workflow process using an Inofile module on Fujitsu’s ScanSnap fi-6010N iScanner. Inofile proviKFS a simple and easy user interface for batch scanning and indexing of documents, reducing the time spent converting files and uploading incoming documents for efficient workflows and business processes in Healthcare, Accounting, Human Resources, Sales, Loan Processing, Project Management and Contracting. Inofile - Complete batch scanning solution Inofile can work in a standalone mode or it can be an integrated appliance, dynamically communicating with any Line of Business (LOB) System, like an electronic medical record (EMR/EHR), document management system, customer relationship management(CRM), enterprise resource planning (ERP) system, human resource system, etc. The standalone mode exports the indexed documents to a searchable directory structure for easy retrieval or uploading into your LOB or document management system. Inofile can be integrated to any LOB, allowing instant data validation on the touch screen and export to the LOB. The touch screen and 101 keyboard makes quality control, batch/document breaking and indexing simple and easy, after which the documents are exported for immediate submission to a workflow or for retrieval. The ScanSnap fi-6010N iScanner is a perfect MFD for any organization; add the Inofile interface and you have distributed a batch scanning and indexing station to enable a customer’s workflow. Inofile – Secure, integrated and branded solution The Inofile platform and graphical user interface(GUI) is built on the SDK from Fujitsu and uses the latest .NET and web technologies. Inofile is a light-weight web-based integration application that allows software manufacturers to create a customized and branded user experience for their software using a variety of methods and Integration Extensions on the Inofile platform including web services, HL7 messaging, database integration and API/SDK smart client integration. The Inofile platform and GUI on the ScanSnap fi-6010N iScanner proviKFS an intuitive end user interface and Inofile services are completely secure and regulatory compliant, using the 6010’s superior security and the images are encrypted during the entire scanning, indexing and export process. Inofile can be linked to any partners document repository effortlessly and immediately. www.inofile.com. Organized by Osmosyz TM. Fujitsu iScanner fi-6010N Network Scanner Fujitsu iScanner fi-6010N Network Scanner
- 191. iScanner Central Admin Console • Launch iScanner Central Admin Console Fujitsu iScanner fi-6010N Network Scanner
- 192. iScanner Central Admin Console • Specify the IP address, host name, or FQDN of the target server Fujitsu iScanner fi-6010N Network Scanner
- 193. iScanner Central Admin Console • iScanner Central Admin Console login screen Fujitsu iScanner fi-6010N Network Scanner
- 194. iScanner Central Admin Console • Enter User Name and Password, then press the Login button Fujitsu iScanner fi-6010N Network Scanner
- 195. Central Admin (Add-in Installs) • iScanner Central Admin Console Main Menu, Select “Add-In Installs” link Fujitsu iScanner fi-6010N Network Scanner
- 196. Central Admin (Add-in Installs)/Inofile • Select target Add-In Group Fujitsu iScanner fi-6010N Network Scanner
- 197. Central Admin (Add-in Installs)/Inofile • Browse to Add-In Module file. (i.e. DeviceModule_Digitech) Fujitsu iScanner fi-6010N Network Scanner
- 198. Central Admin (Add-in Installs)/Inofile • Press the Upload button to save Add-In Module to Central Admin Server Fujitsu iScanner fi-6010N Network Scanner
- 199. Central Admin (Add-in Installs)/Inofile • Uploading… Fujitsu iScanner fi-6010N Network Scanner
- 200. Central Admin (Add-in Installs)/Inofile • Check “Issue an Update Call” then press the Register button Fujitsu iScanner fi-6010N Network Scanner
- 201. Central Admin (Add-in Installs)/Inofile • New Add-in module is now available for scanners to install Fujitsu iScanner fi-6010N Network Scanner
- 202. Central Admin (Add-in Installs)/Inofile • Registered Add-in Module, Version and Release Date Fujitsu iScanner fi-6010N Network Scanner
- 203. Central Admin (Add-in Installs) • Add-In Module being installed on fi-6010N’s. Scanner restarts. Fujitsu iScanner fi-6010N Network Scanner
- 204. Osmosyz Inofile Add-In Configuration • Fujitsu fi-6010N Login screen Fujitsu iScanner fi-6010N Network Scanner
- 205. Osmosyz Inofile Add-In Configuration • Enter User Name Fujitsu iScanner fi-6010N Network Scanner
- 206. Osmosyz Inofile Add-In Configuration • Enter Password Fujitsu iScanner fi-6010N Network Scanner
- 207. Osmosyz Inofile Add-In Configuration • Press Inofile Add-In button Fujitsu iScanner fi-6010N Network Scanner
- 208. Osmosyz Inofile Add-In Configuration • Osmosyz Inofile Add-In Module configuration screen Fujitsu iScanner fi-6010N Network Scanner
- 209. Osmosyz Inofile Add-In Configuration • Enter Entity ID, User Name, Password and PVE Url Fujitsu iScanner fi-6010N Network Scanner
- 210. Osmosyz Inofile Add-In Configuration • Testing connection. Connecting… Fujitsu iScanner fi-6010N Network Scanner
- 211. Osmosyz Inofile Add-In Configuration • Connection Successful! Press the OK button Fujitsu iScanner fi-6010N Network Scanner
- 212. Osmosyz Inofile Add-In Configuration • Save Fujitsu iScanner fi-6010N Network Scanner
- 213. Osmosyz Inofile Add-In Configuration • Osmosyz Inofile Main Menu. Press the Refresh button Fujitsu iScanner fi-6010N Network Scanner
- 214. Osmosyz Inofile Add-In Configuration • Inofile Projects Fujitsu iScanner fi-6010N Network Scanner
