1. The document is a user manual for the F312A IP camera that provides instructions on setting up and using the camera.
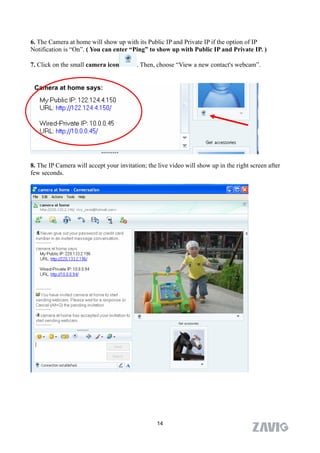
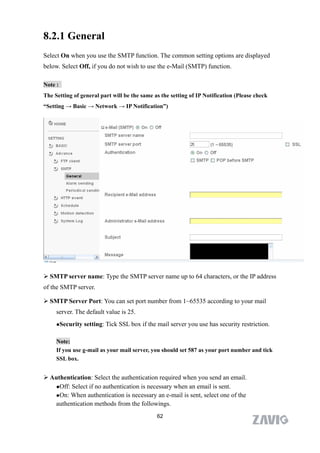
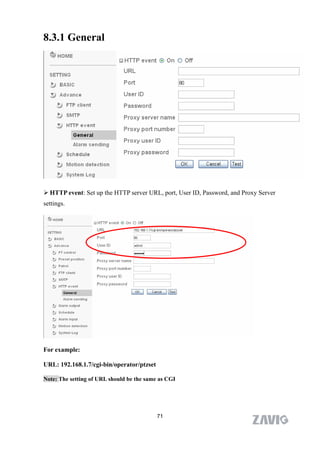
2. It covers connecting to the camera via a web browser on Windows and Mac as well as mobile phones. Settings covered include the network, wireless, motion detection, FTP and more.
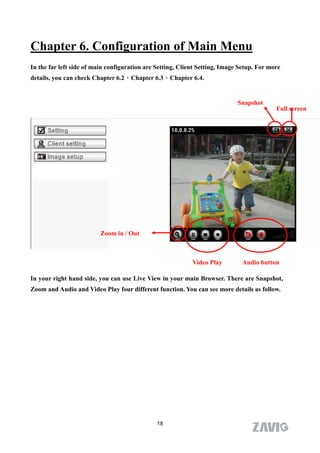
3. Chapters are included on basic camera functions like live view, snapshot, zoom as well as advanced configuration in the settings menu.