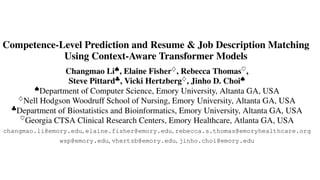
Competence-Level Prediction and Resume & Job Description Matching Using Context-Aware Transformer Models
•
1 like•111 views
EMNLP 2020 Changmao Li, Elaine Fisher, Rebecca Thomas, Steve Pittard, Vicki Hertzberg, Jinho D. Choi https://www.aclweb.org/anthology/2020.emnlp-main.679/
Report
Share
Report
Share
Download to read offline
Recommended
Adaptation of Multilingual Transformer Encoder for Robust Enhanced Universal ...

IWPT 2020
Han He and Jinho D. Choi
https://www.aclweb.org/anthology/2020.iwpt-1.19/
Graph-to-Text Generation and its Applications to Dialogue

Emory NLP Weekly
- Date: 10/15/2020
- Presenter: Sarah Finch (PhD student)
https://www.linkedin.com/events/6711785730856767488/
Hua Shan - 2015 - A Dependency-to-String Model for Chinese-Japanese SMT System

Hua Shan - 2015 - A Dependency-to-String Model for Chinese-Japanese SMT SystemAssociation for Computational Linguistics
WAT - W15-5010 (Poster)Labelled Variables in Logic Programming: A First Prototipe in tuProlog

We present the first prototype of Labelled tuProlog, an extension of tuProlog exploiting labelled variables to enable a sort of multi- paradigm / multi-language programming aimed at pervasive systems.
Relational Calculus

The presentation discusses about the following topics:
DBMS Architecture
Relational Algebra Review
Relational calculus
Relational calculus building blocks
Tuple relational calculus
Tuple relational calculus Formulas
Efficient call path detection for android os size of huge source code

Today most developers utilize source code written by other parties. Because the code is
modified frequently, the developers need to grasp the impact of the modification repeatedly. A
call graph and especially its special type, a call path, help the developers comprehend the
modification. Source code written by other parties, however, becomes too huge to be held in
memory in the form of parsed data for a call graph or path. This paper offers a bidirectional
search algorithm for a call graph of too huge amount of source code to store all parse results of
the code in memory. It refers to a method definition in source code corresponding to the visited
node in the call graph. The significant feature of the algorithm is the referenced information is
used not in order to select a prioritized node to visit next but in order to select a node to
postpone visiting. It reduces path extraction time by 8% for a case in which ordinary path
search algorithms do not reduce the time.
Recommended
Adaptation of Multilingual Transformer Encoder for Robust Enhanced Universal ...

IWPT 2020
Han He and Jinho D. Choi
https://www.aclweb.org/anthology/2020.iwpt-1.19/
Graph-to-Text Generation and its Applications to Dialogue

Emory NLP Weekly
- Date: 10/15/2020
- Presenter: Sarah Finch (PhD student)
https://www.linkedin.com/events/6711785730856767488/
Hua Shan - 2015 - A Dependency-to-String Model for Chinese-Japanese SMT System

Hua Shan - 2015 - A Dependency-to-String Model for Chinese-Japanese SMT SystemAssociation for Computational Linguistics
WAT - W15-5010 (Poster)Labelled Variables in Logic Programming: A First Prototipe in tuProlog

We present the first prototype of Labelled tuProlog, an extension of tuProlog exploiting labelled variables to enable a sort of multi- paradigm / multi-language programming aimed at pervasive systems.
Relational Calculus

The presentation discusses about the following topics:
DBMS Architecture
Relational Algebra Review
Relational calculus
Relational calculus building blocks
Tuple relational calculus
Tuple relational calculus Formulas
Efficient call path detection for android os size of huge source code

Today most developers utilize source code written by other parties. Because the code is
modified frequently, the developers need to grasp the impact of the modification repeatedly. A
call graph and especially its special type, a call path, help the developers comprehend the
modification. Source code written by other parties, however, becomes too huge to be held in
memory in the form of parsed data for a call graph or path. This paper offers a bidirectional
search algorithm for a call graph of too huge amount of source code to store all parse results of
the code in memory. It refers to a method definition in source code corresponding to the visited
node in the call graph. The significant feature of the algorithm is the referenced information is
used not in order to select a prioritized node to visit next but in order to select a node to
postpone visiting. It reduces path extraction time by 8% for a case in which ordinary path
search algorithms do not reduce the time.
The DE-9IM Matrix in Details using ST_Relate: In Picture and SQL

The DE-9IM matrix is the foundation for understanding how spatial relationships are implemented in DBMSs like PostgreSQL, Oracle, and Microsoft SQL Server. This presentation makes a structure walk-through of most of the cases using a very large number of examples.
Ay34306312

International Journal of Engineering Research and Applications (IJERA) is an open access online peer reviewed international journal that publishes research and review articles in the fields of Computer Science, Neural Networks, Electrical Engineering, Software Engineering, Information Technology, Mechanical Engineering, Chemical Engineering, Plastic Engineering, Food Technology, Textile Engineering, Nano Technology & science, Power Electronics, Electronics & Communication Engineering, Computational mathematics, Image processing, Civil Engineering, Structural Engineering, Environmental Engineering, VLSI Testing & Low Power VLSI Design etc.
1984 Article on An Application of AI to Operations Reserach

Introduces an and-or task network and use heuristic search to find an optimal plan and critical path
Mit203 analysis and design of algorithms

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
(Prefer mailing. Call in emergency )
GENERATING PYTHON CODE FROM OBJECT-Z SPECIFICATIONS

ABSTRACT
Object-Z is an object-oriented specification language which extends the Z language with classes, objects, inheritance and polymorphism that can be used to represent the specification of a complex system as collections of objects. There are a number of existing works that mapped Object-Z to C++ and Java programming languages. Since Python and Object-Z share many similarities, both are object-oriented paradigm, support set theory and predicate calculus moreover, Python is a functional programming language which is naturally closer to formal specifications, we propose a mapping from Object-Z specifications to Python code that covers some Object-Z constructs and express its specifications in Python to validate these specifications. The validations are used in the mapping covered preconditions,
post-conditions, and invariants that are bui l t using lambda funct ion and Python's decorator. This work has found Python is an excellent language for developing libraries to map Object-Z specifications to Python.
Spatial Indexing

Spatial indexing using Space-Filling Curves (SFC), R-Trees, and Quadtrees. Examples on spatial indexing on PostgreSQL.
Reference Scope Identification in Citing Sentences

This is material of reading camp (http://www.cl.ecei.tohoku.ac.jp/~y-matsu/snlp4/)
Data compression using python draft

A talk that motivates the idea of text compression using information theory
Regular Expressions -- SAS and Perl

The SAS System provides two declarative syntax languages for regular expressions: SAS and Perl. This presentation compares and contrasts these two complementary choices for SAS application developers.
Knowledg graphs yosi mass

Cognitive Systems Institute Speaker Series Call May 7, 2105 with Yosi Mass, IBM Research Haifa, presenting Knowledge graphs.
End-to-end sequence labeling via bi-directional LSTM-CNNs-CRF

Pytorch Tutorial for End-to-end sequence labeling via bi-directional LSTM-CNN's-CRF
More Related Content
What's hot
The DE-9IM Matrix in Details using ST_Relate: In Picture and SQL

The DE-9IM matrix is the foundation for understanding how spatial relationships are implemented in DBMSs like PostgreSQL, Oracle, and Microsoft SQL Server. This presentation makes a structure walk-through of most of the cases using a very large number of examples.
Ay34306312

International Journal of Engineering Research and Applications (IJERA) is an open access online peer reviewed international journal that publishes research and review articles in the fields of Computer Science, Neural Networks, Electrical Engineering, Software Engineering, Information Technology, Mechanical Engineering, Chemical Engineering, Plastic Engineering, Food Technology, Textile Engineering, Nano Technology & science, Power Electronics, Electronics & Communication Engineering, Computational mathematics, Image processing, Civil Engineering, Structural Engineering, Environmental Engineering, VLSI Testing & Low Power VLSI Design etc.
1984 Article on An Application of AI to Operations Reserach

Introduces an and-or task network and use heuristic search to find an optimal plan and critical path
Mit203 analysis and design of algorithms

Dear students get fully solved assignments
Send your semester & Specialization name to our mail id :
“ help.mbaassignments@gmail.com ”
or
Call us at : 08263069601
(Prefer mailing. Call in emergency )
GENERATING PYTHON CODE FROM OBJECT-Z SPECIFICATIONS

ABSTRACT
Object-Z is an object-oriented specification language which extends the Z language with classes, objects, inheritance and polymorphism that can be used to represent the specification of a complex system as collections of objects. There are a number of existing works that mapped Object-Z to C++ and Java programming languages. Since Python and Object-Z share many similarities, both are object-oriented paradigm, support set theory and predicate calculus moreover, Python is a functional programming language which is naturally closer to formal specifications, we propose a mapping from Object-Z specifications to Python code that covers some Object-Z constructs and express its specifications in Python to validate these specifications. The validations are used in the mapping covered preconditions,
post-conditions, and invariants that are bui l t using lambda funct ion and Python's decorator. This work has found Python is an excellent language for developing libraries to map Object-Z specifications to Python.
Spatial Indexing

Spatial indexing using Space-Filling Curves (SFC), R-Trees, and Quadtrees. Examples on spatial indexing on PostgreSQL.
Reference Scope Identification in Citing Sentences

This is material of reading camp (http://www.cl.ecei.tohoku.ac.jp/~y-matsu/snlp4/)
Data compression using python draft

A talk that motivates the idea of text compression using information theory
Regular Expressions -- SAS and Perl

The SAS System provides two declarative syntax languages for regular expressions: SAS and Perl. This presentation compares and contrasts these two complementary choices for SAS application developers.
Knowledg graphs yosi mass

Cognitive Systems Institute Speaker Series Call May 7, 2105 with Yosi Mass, IBM Research Haifa, presenting Knowledge graphs.
What's hot (20)
Bert pre_training_of_deep_bidirectional_transformers_for_language_understanding

Bert pre_training_of_deep_bidirectional_transformers_for_language_understanding
The DE-9IM Matrix in Details using ST_Relate: In Picture and SQL

The DE-9IM Matrix in Details using ST_Relate: In Picture and SQL
1984 Article on An Application of AI to Operations Reserach

1984 Article on An Application of AI to Operations Reserach
GENERATING PYTHON CODE FROM OBJECT-Z SPECIFICATIONS

GENERATING PYTHON CODE FROM OBJECT-Z SPECIFICATIONS
Reference Scope Identification in Citing Sentences

Reference Scope Identification in Citing Sentences
On the Semantics of Linking and Importing in Modular Ontologies

On the Semantics of Linking and Importing in Modular Ontologies
Similar to Competence-Level Prediction and Resume & Job Description Matching Using Context-Aware Transformer Models
End-to-end sequence labeling via bi-directional LSTM-CNNs-CRF

Pytorch Tutorial for End-to-end sequence labeling via bi-directional LSTM-CNN's-CRF
Predicting Tweet Sentiment

Objective of the Project
Tweet sentiment analysis gives businesses insights into customers and competitors. In this project, we combined several text preprocessing techniques with machine learning algorithms. Neural network, Random Forest and Logistic Regression models were trained on the Sentiment140 twitter data set. We then predicted the sentiment of a hold-out test set of tweets. We used both Python and PySpark (local Spark Context) to program different parts of the pre-processing and modelling.
Concept Detection of Multiple Choice Questions using Transformer Based Models

https://www.irjet.net/archives/V9/i4/IRJET-V9I4178.pdf
Cncwebworld c programming,

programming training courses
programing courses
software training
computer training
programming courses
web programming course
programming training
it programming course
programming course
c programming course
training course
c# training
c courses
c training
A WEB BASED APPLICATION FOR RESUME PARSER USING NATURAL LANGUAGE PROCESSING T...

https://www.irjet.net/archives/V9/i7/IRJET-V9I7493.pdf
Multi-modal sources for predictive modeling using deep learning

Using Vision Language models : Is it possible to prompt them similar to LLMs? when to use out of the box and when to pre-train? General multi-modal models --- deeplearning. Machine learning metrics, feature engineering and setting up an ML problem.
HOPE: A Task-Oriented and Human-Centric Evaluation Framework Using Profession...

Traditional automatic evaluation metrics for machine translation have been widely criticized by linguists due to their low accuracy, lack of transparency, focus on language mechanics rather than semantics, and low agreement with human quality evaluation. Human evaluations in the form of MQM-like scorecards have always been carried out in real industry setting by both clients and translation service providers (TSPs). However, traditional human translation quality evaluations are costly to perform and go into great linguistic detail, raise issues as to
inter-rater reliability (IRR) and are not designed to measure quality of worse than premium quality translations.
In this work, we introduce \textbf{HOPE}, a task-oriented and \textit{\textbf{h}}uman-centric evaluation framework for machine translation output based \textit{\textbf{o}}n professional \textit{\textbf{p}}ost-\textit{\textbf{e}}diting annotations. It contains only a limited number of commonly occurring error types, and uses a scoring model with geometric progression of error penalty points (EPPs) reflecting error severity level to each translation unit.
The initial experimental work carried out on English-Russian language pair MT outputs on marketing content type of text from highly technical domain reveals that our evaluation framework is quite effective in reflecting the MT output quality regarding both overall system-level performance and segment-level transparency, and it increases the IRR for error type interpretation.
The approach has several key advantages, such as ability to measure and compare less than perfect MT output from different systems, ability to indicate human perception of quality, immediate estimation of the labor effort required to bring MT output to premium quality, low-cost and faster application, as well as higher IRR. Our experimental data is available at \url{https://github.com/lHan87/HOPE}
Programming in C [Module One]![Programming in C [Module One]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Programming in C [Module One]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
A step to fulfill the desire of the students who wish to learn Programming from scratch...
Chapter One - Concept of C
Similar to Competence-Level Prediction and Resume & Job Description Matching Using Context-Aware Transformer Models (20)
End-to-end sequence labeling via bi-directional LSTM-CNNs-CRF

End-to-end sequence labeling via bi-directional LSTM-CNNs-CRF
Concept Detection of Multiple Choice Questions using Transformer Based Models

Concept Detection of Multiple Choice Questions using Transformer Based Models
A WEB BASED APPLICATION FOR RESUME PARSER USING NATURAL LANGUAGE PROCESSING T...

A WEB BASED APPLICATION FOR RESUME PARSER USING NATURAL LANGUAGE PROCESSING T...
Multi-modal sources for predictive modeling using deep learning

Multi-modal sources for predictive modeling using deep learning
Large Language Models for Test Case Evolution and Repair

Large Language Models for Test Case Evolution and Repair
HOPE: A Task-Oriented and Human-Centric Evaluation Framework Using Profession...

HOPE: A Task-Oriented and Human-Centric Evaluation Framework Using Profession...
M.tech.(cse) (regular) part i(semester i & ii)

M.tech.(cse) (regular) part i(semester i & ii)
More from Jinho Choi
Analysis of Hierarchical Multi-Content Text Classification Model on B-SHARP D...

AACL 2020
Renxuan Albert Li, Ihab Hajjar, Felicia Goldstein, Jinho D. Choi
https://www.aclweb.org/anthology/2020.aacl-main.38/
Transformers to Learn Hierarchical Contexts in Multiparty Dialogue for Span-b...

ACL 2020
Changmao Li and Jinho D. Choi
https://www.aclweb.org/anthology/2020.acl-main.505/
The Myth of Higher-Order Inference in Coreference Resolution

EMNLP 2020
Liyan Xu, Jinho D. Choi
https://www.aclweb.org/anthology/2020.emnlp-main.686/
Noise Pollution in Hospital Readmission Prediction: Long Document Classificat...

BioNLP 2020
Liyan Xu, Julien Hogan, Rachel E. Patzer, Jinho D. Choi
https://www.aclweb.org/anthology/2020.bionlp-1.10/
CS329 - WordNet Similarities

CS|QTM|LING329: Computational Linguistics
https://github.com/emory-courses/cs329
CS329 - Lexical Relations

CS|QTM|LING329: Computational Linguistics
https://github.com/emory-courses/cs329
Automatic Knowledge Base Expansion for Dialogue Management

Emory NLP Weekly
- Date: 11/4/2020
- Presenter: James Finch (PhD student)
- https://www.linkedin.com/events/6711788100151975936/
Attention is All You Need for AMR Parsing

Emory NLP Weekly
- Date: 10/28/2020
- Presenter: Han He (PhD student)
- https://www.linkedin.com/events/6711787130047217664/
Real-time Coreference Resolution for Dialogue Understanding

Emory NLP Weekly
- Date: 10/21/2020
- Presenter: Liyan Xu (PhD student)
https://www.linkedin.com/events/6711786162941374464/
Multi-modal Embedding Learning for Early Detection of Alzheimer's Disease

Emory NLP Weekly
- Date: 9/23/2020
- Presenter: Ran Xu (BS student)
https://www.linkedin.com/events/6711762540579446784/
Building Widely-Interpretable Semantic Networks for Dialogue Contexts

Emory NLP Weekly
- Date: 9/16/2020
- Presenter: Lydia Feng (BS student)
https://www.linkedin.com/events/6711760000370515968/
How to make Emora talk about Sports Intelligently

Emory NLP Weekly
- Date: 9/2/2020
- Presenter: Sonny Xu (BS/MS student)
https://www.linkedin.com/events/6711696381951770624/
Text-to-SQL with Data-Driven Templates

Emory NLP Weekly
- Date: 8/26/2020
- Presenter: Yusen Zhang (MS student)
https://www.linkedin.com/events/6711695553576747008/
Resume Classification with Term Attention Embeddings

Emory NLP Weekly
- Date: 9/9/2020
- Presenter: Xiangjue Dong (MS student)
https://www.linkedin.com/events/6711755863830466561/
More from Jinho Choi (20)
Analysis of Hierarchical Multi-Content Text Classification Model on B-SHARP D...

Analysis of Hierarchical Multi-Content Text Classification Model on B-SHARP D...
Transformers to Learn Hierarchical Contexts in Multiparty Dialogue for Span-b...

Transformers to Learn Hierarchical Contexts in Multiparty Dialogue for Span-b...
The Myth of Higher-Order Inference in Coreference Resolution

The Myth of Higher-Order Inference in Coreference Resolution
Noise Pollution in Hospital Readmission Prediction: Long Document Classificat...

Noise Pollution in Hospital Readmission Prediction: Long Document Classificat...
Automatic Knowledge Base Expansion for Dialogue Management

Automatic Knowledge Base Expansion for Dialogue Management
Real-time Coreference Resolution for Dialogue Understanding

Real-time Coreference Resolution for Dialogue Understanding
Multi-modal Embedding Learning for Early Detection of Alzheimer's Disease

Multi-modal Embedding Learning for Early Detection of Alzheimer's Disease
Building Widely-Interpretable Semantic Networks for Dialogue Contexts

Building Widely-Interpretable Semantic Networks for Dialogue Contexts
Resume Classification with Term Attention Embeddings

Resume Classification with Term Attention Embeddings
Recently uploaded
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

In questo evento online gratuito, organizzato dalla Community Italiana di UiPath, potrai esplorare le nuove funzionalità di Autopilot, il tool che integra l'Intelligenza Artificiale nei processi di sviluppo e utilizzo delle Automazioni.
📕 Vedremo insieme alcuni esempi dell'utilizzo di Autopilot in diversi tool della Suite UiPath:
Autopilot per Studio Web
Autopilot per Studio
Autopilot per Apps
Clipboard AI
GenAI applicata alla Document Understanding
👨🏫👨💻 Speakers:
Stefano Negro, UiPath MVPx3, RPA Tech Lead @ BSP Consultant
Flavio Martinelli, UiPath MVP 2023, Technical Account Manager @UiPath
Andrei Tasca, RPA Solutions Team Lead @NTT Data
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
By Design, not by Accident - Agile Venture Bolzano 2024

As presented at the Agile Venture Bolzano, 4.06.2024
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

Building better applications for business users with SAP Fiori.
• What is SAP Fiori and why it matters to you
• How a better user experience drives measurable business benefits
• How to get started with SAP Fiori today
• How SAP Fiori elements accelerates application development
• How SAP Build Code includes SAP Fiori tools and other generative artificial intelligence capabilities
• How SAP Fiori paves the way for using AI in SAP apps
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Recently uploaded (20)
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
By Design, not by Accident - Agile Venture Bolzano 2024

By Design, not by Accident - Agile Venture Bolzano 2024
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
Assure Contact Center Experiences for Your Customers With ThousandEyes

Assure Contact Center Experiences for Your Customers With ThousandEyes
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Secstrike : Reverse Engineering & Pwnable tools for CTF.pptx

Secstrike : Reverse Engineering & Pwnable tools for CTF.pptx
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Competence-Level Prediction and Resume & Job Description Matching Using Context-Aware Transformer Models
- 1. Competence-Level Prediction and Resume & Job Description Matching Using Context-Aware Transformer Models Changmao Li, Elaine Fisher, Rebecca S. Thomas, Stephen Pittard, Vicki Hertzberg, and Jinho Choi Emory NLP
- 2. Outline ● Dataset ● Tasks ● Approaches ● Experiments ● Error Analysis ● Contributions
- 3. Dataset Source: Clinical Research Coordinators(CRC) Applicants Resumes Here we have two kinds of annotations: 1. The levels they applied(an applicant can apply multiple levels). 2. The level they should be qualified. This is annotated by human experts with some annotation agreements. There are four levels, CRC1, CRC2, CRC3, CRC4. For the annotation, if the resume cannot match any level it will be annotated with Not Qualified(NQ) Besides, there is a job description for each level.
- 4. Dataset Preprocessing: The original resume files are in DOC or PDF, they are parsed using some tools and splitted into 6 sections and finally put into the json file for the convenient use. The existence ratio of each section in the CRC levels
- 5. Dataset Annotation: Two experts with experience in recruiting applicants for CRC positions of all levels design the annotation guidelines in 5 rounds by labeling each resume. Kappa scores measured for ITA during the five rounds of guideline development
- 6. Tasks Two novel tasks are proposed for this new dataset: 1. (Multiclass classification(5 class))Given a resume, decide which level of CRC positions that the corresponding applicant is suitable for.(Use the resume as input and the annotation 2 as the gold output) 2. (Binary classification)Given a resume and a CRC level job description, decide whether the applicant is suitable for that particular level.(Use both resume and job description for the levels they applied for as input and combine the annotation 1 and annotation 2 to get the binary gold output)
- 7. Approaches Baseline Approaches for both tasks
- 8. Approaches Strategies when applying baseline models ● Section Trimming for baseline models due to input length limitation of transformer encoders Task 1 Task 2
- 9. Approaches Proposed Models for the multiclass classification task The context-aware model using section pruning and section encoding
- 10. Approaches Proposed Models for the multiclass classification task The context-aware model using chunk segmenting and section encoding
- 11. Approaches Proposed Models for the binary classification task Approaches The context-aware models using chunk segmenting + section encoding + job description embedding and multi-head attention between the resume and the job description
- 12. Approaches Strategies when applying models ● Section Pruning for Proposed “encoding by sections” models in case each section exceeds the input length of transformer encoders
- 13. Analysis on Section Pruning (in Appendix) Section lengths before section pruning Section lengths after section pruning
- 14. Experiments Data split for the multiclass classification task(Keep label distributions): Data statistics for the competence-level classification task
- 15. Experiments Data split for binary classification task(keep label and CRC distributions without overlap resumes between training and dev or test set ): Data statistics for the resume-to-job description matching task
- 16. Algorithm to split dataset while avoiding overlaps between training and evaluation dataset(in Appendix) The key idea is 1. Split the data by targeted label distributions but with a smaller initial training set ratio than the original one. 2. If there are overlapping applicants, then the algorithm puts all the overlaps into the training set so that the training set ratio will be large enough to be close to the targeted training set ratio while the label distributions are still kept in a great extent.
- 17. Experiments Experimented Models W!: Whole context model + section trimming P: Context-aware model + section pruning P⊕I:P+ section encoding C: Context-aware model + chunk segmenting C⊕I:C+ section encoding Models for the competence-level classification task W!" : Whole context + sec./job_desc. trimming P⊕I⊕J:P⊕I+ job_desc. embedding P⊕I⊕J⊕A:P⊕I⊕J+ multi-head attention P⊕I⊕J⊕AE:P⊕I⊕J-E# C⊕I⊕J:C⊕I+ job_desc. embedding C⊕I⊕J⊕A:C⊕I⊕J+ multi-head attention C⊕I⊕J⊕AE:C⊕I⊕J- E# Models for the resume-to-job description matching task
- 18. Experiments Results for the competence-level classification task.
- 19. Experiments Results for the resume-to-job description matching task.
- 20. Experiments Analysis for the competence-level classification task. Confusion matrix for the best model of the competence-level classification task
- 21. Experiments Analysis for the resume-to-job description matching task. Confusion matrix for the best model of the resume-to-job description matching task
- 22. Error Analysis • It’s unable to identify clinical research experience. • It can’t identify dates of experience. • It’s hard to distinguish adjacent CRC positions.
- 23. Contributions ● Introduced a new resume classification dataset. ● Proposed two new tasks for this new dataset. ● Proposed novel context-aware transformer approaches for two tasks. ● Conducted experiments with several proposed models. ● Conducted both quantitative and qualitative analysis for future improvements.
- 24. Thank You Q & A
