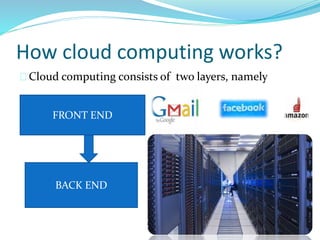
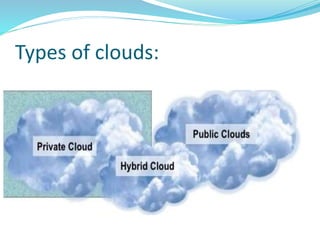
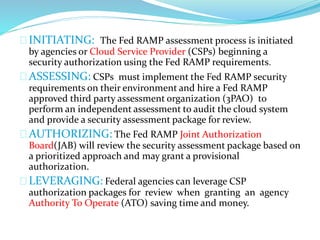
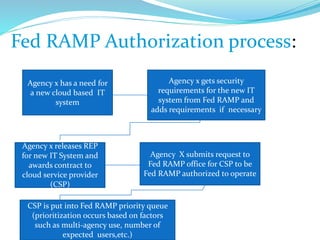
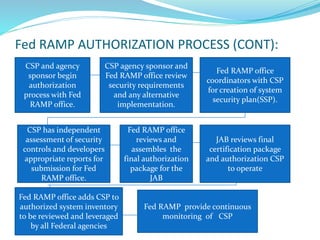
The document provides an overview of cloud computing, describing its definition, how it operates, different types of clouds, and cloud service models such as SaaS, PaaS, and IaaS. It also covers cloud security, the FedRAMP authorization process, and highlights the benefits of cloud computing, emphasizing its cost-effectiveness and efficiency. Overall, it asserts that cloud computing is set to become increasingly popular due to its advantages for businesses.