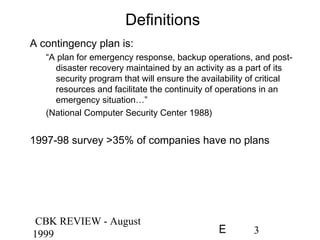
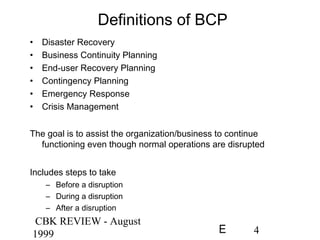
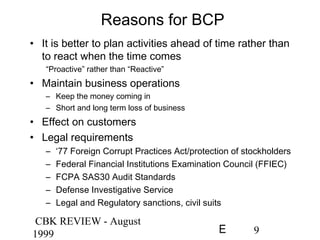
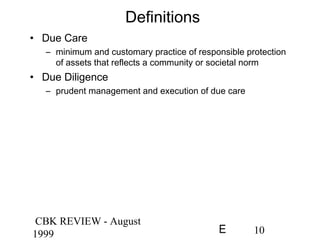
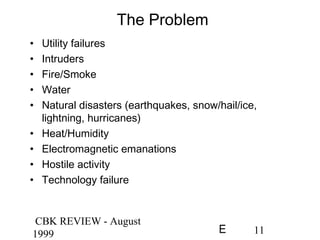
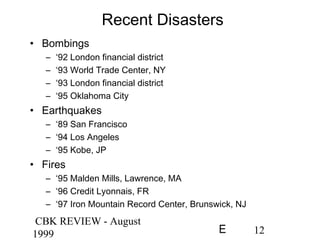
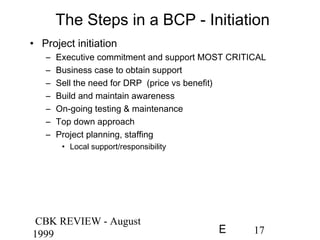
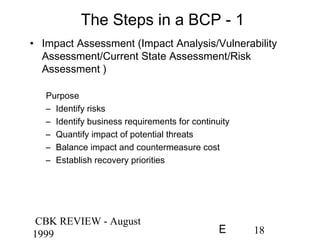
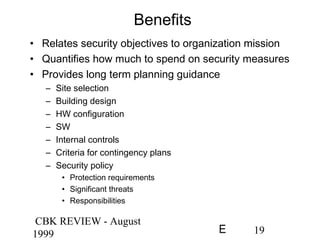
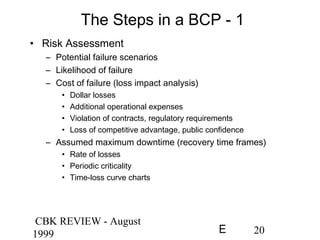
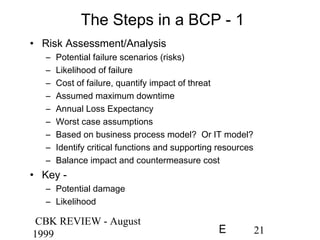
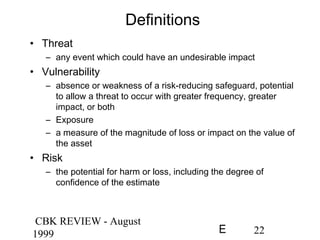
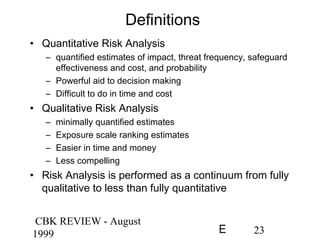
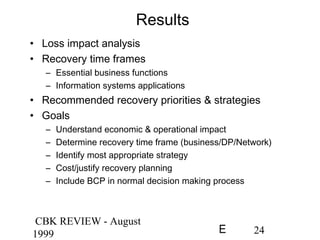
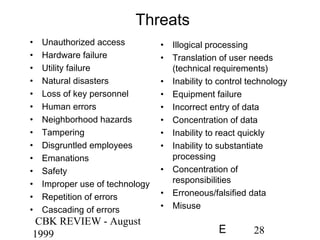
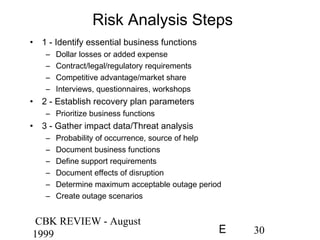
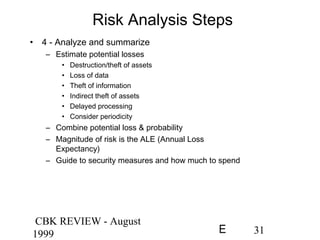
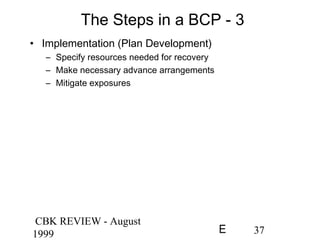
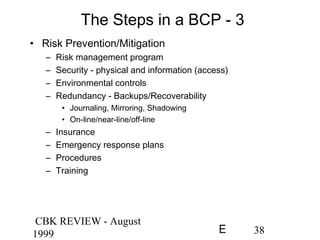
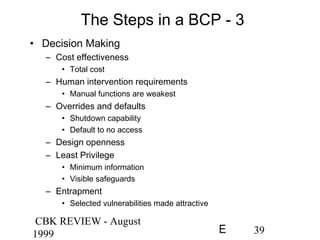
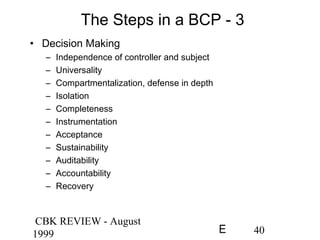
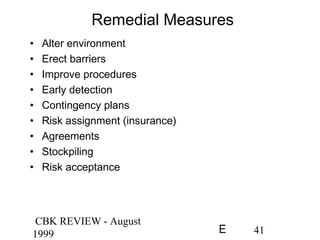
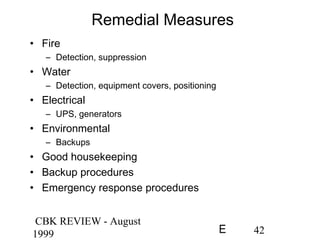
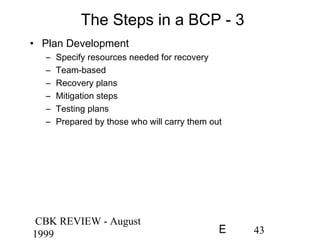
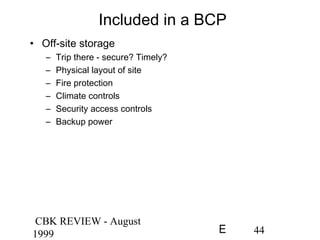
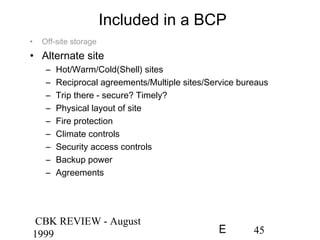
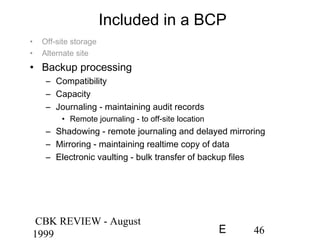
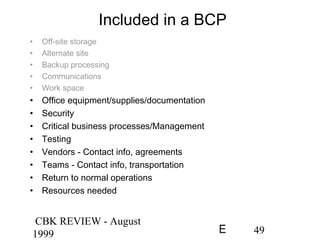
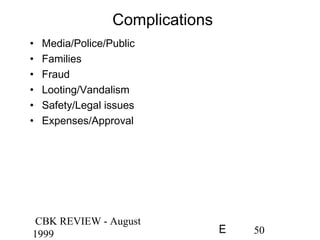
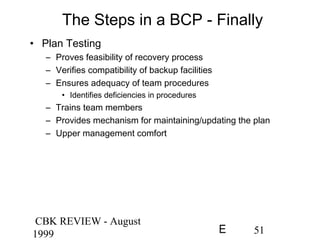
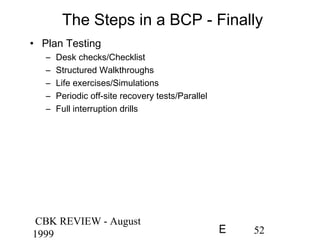
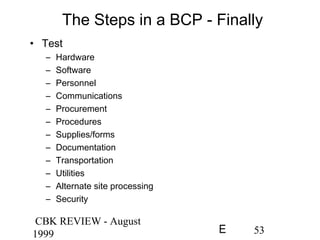
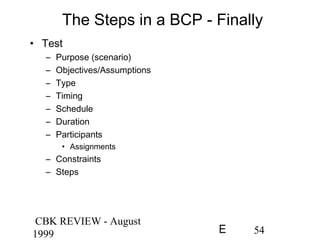
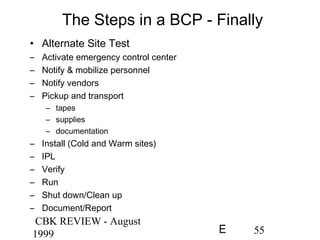
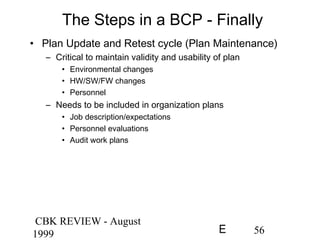
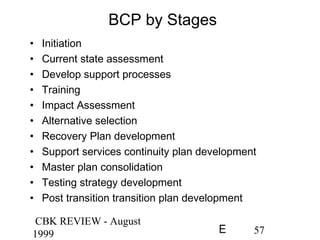
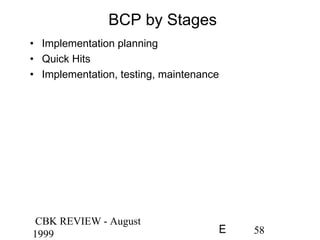
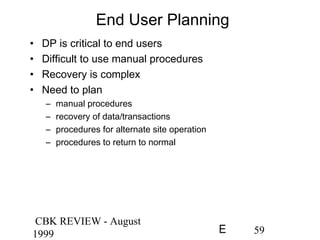
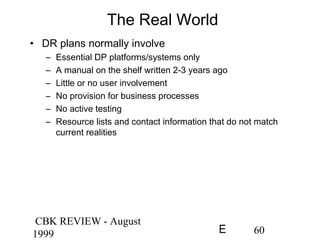
The document provides an overview of business continuity planning (BCP), emphasizing its importance for organizations to maintain operations during disruptions. It outlines key definitions, reasons for BCP, various steps involved in creating a BCP, and the necessity of risk management and testing. Despite being dated, the core principles discussed remain relevant for effective disaster recovery and continuity planning.