1) The document discusses the risks associated with the proliferation of unsanctioned cloud application usage in enterprises. Without visibility into all cloud application usage, organizations may increase security risks, leak sensitive data, and reduce efficiency.
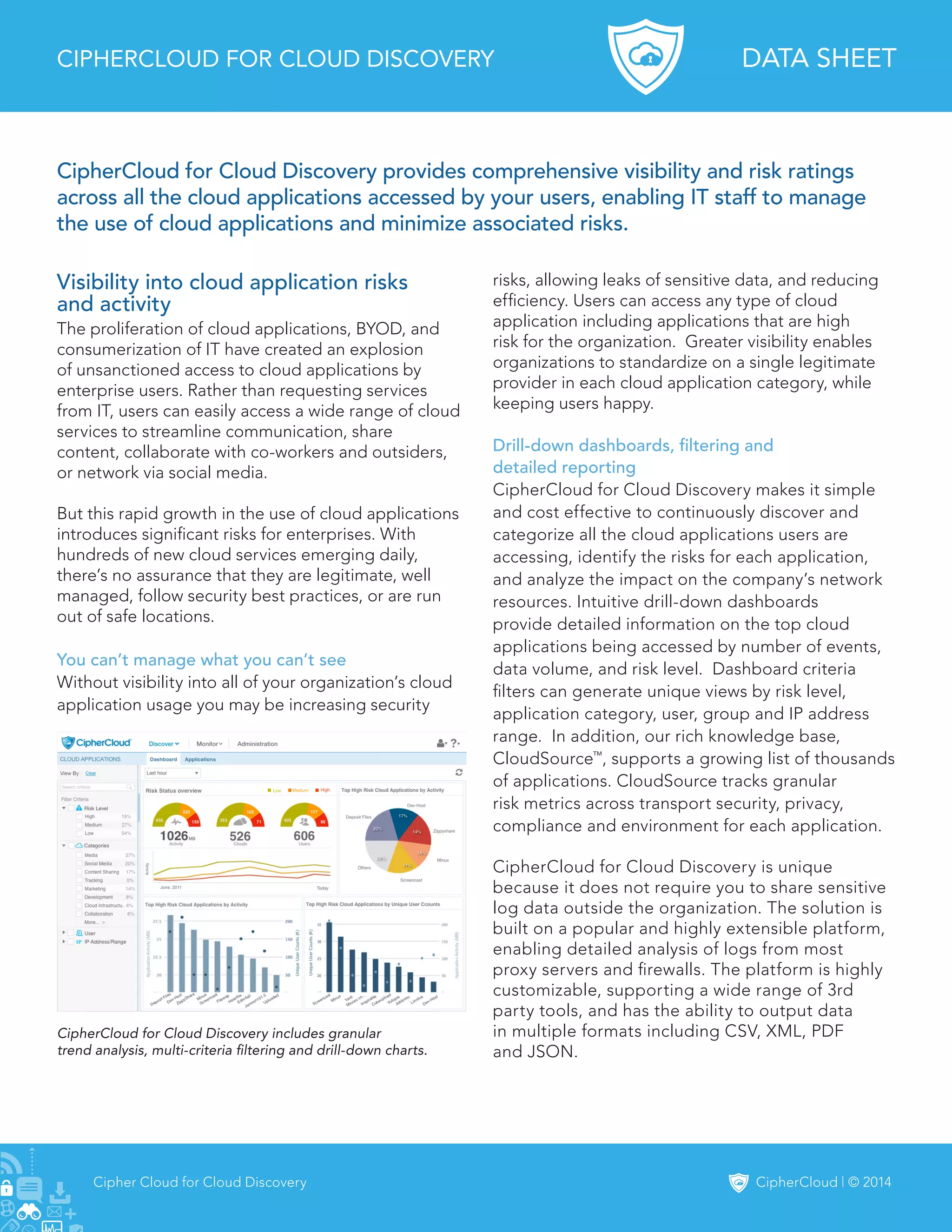
2) CipherCloud for Cloud Discovery provides enterprises visibility and risk ratings for all cloud applications accessed by users. It continuously discovers and categorizes cloud applications, identifies risks for each, and analyzes the impact on network resources.
3) CipherCloud maintains an extensive knowledge base called CloudSource that tracks security metrics and calculates risk scores for thousands of cloud applications based on factors like encryption, location of servers, and data breaches.