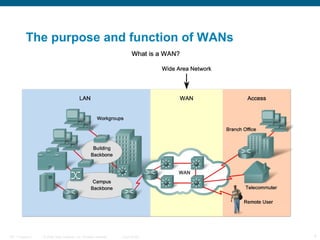
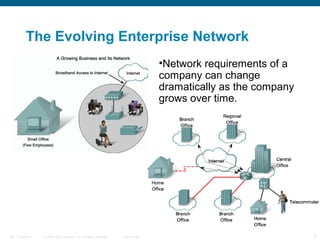
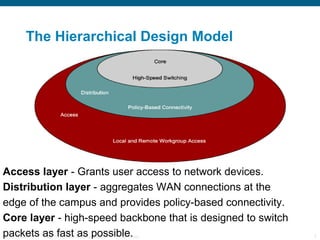
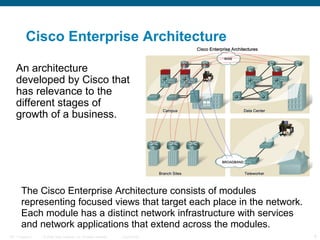
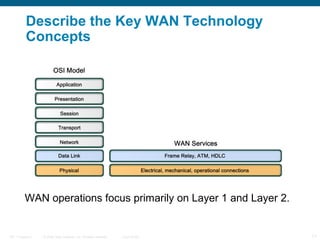
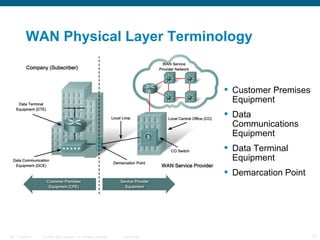
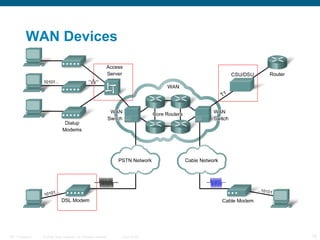
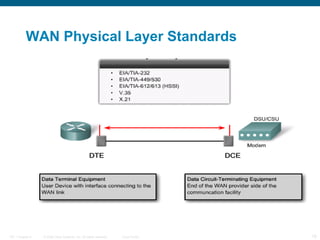
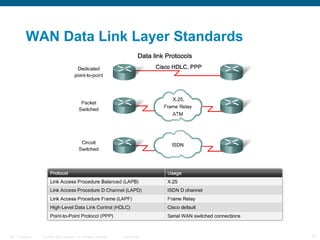
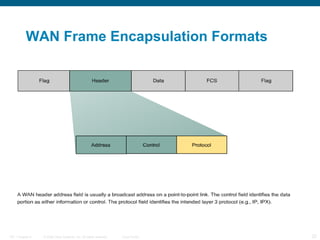
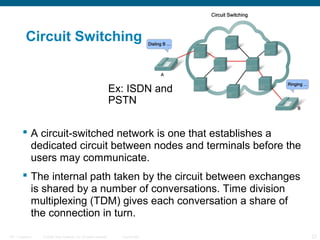
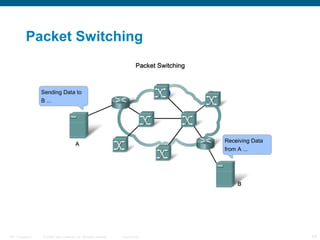
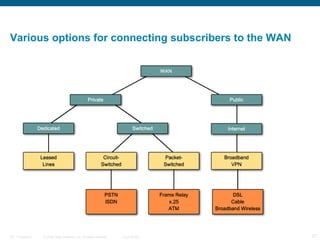
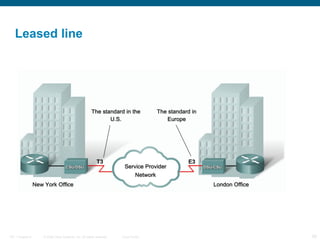
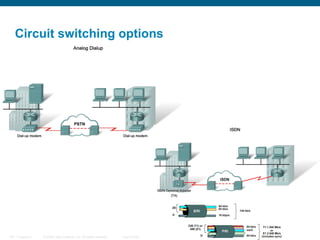
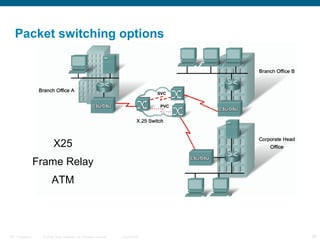
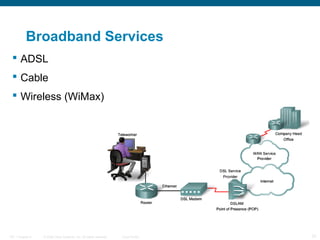
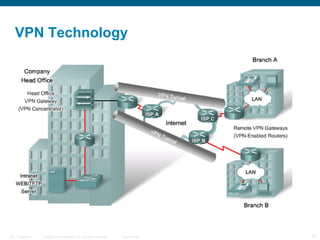
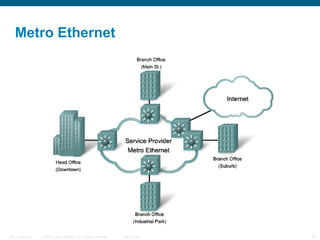
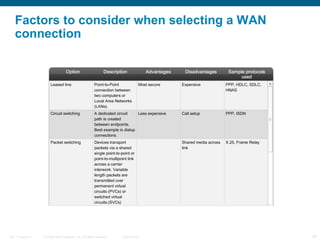
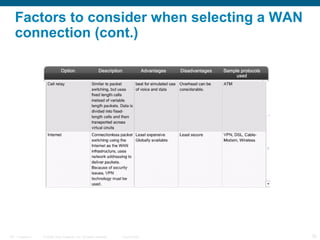
The document discusses wide area network (WAN) technologies. It defines a WAN, describes common WAN devices and standards, and discusses WAN connection options such as leased lines, circuit switching, packet switching, broadband services, and virtual private networks. It also covers Cisco's Enterprise Composite Network Model and factors to consider when selecting a WAN technology such as purpose, geographic scope, traffic needs, and use of public or private infrastructure.