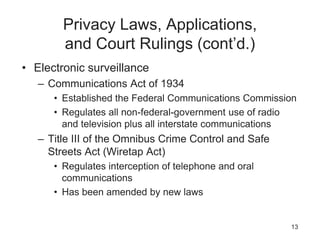
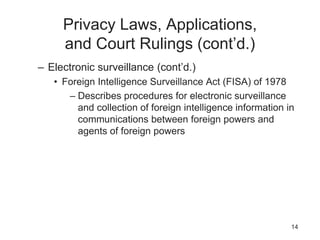
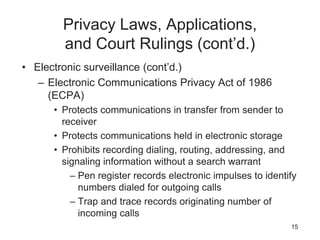
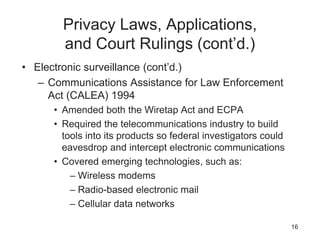
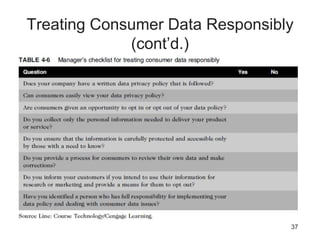
This document discusses privacy issues related to information technology. It covers several topics: laws protecting privacy of personal data; identity theft; electronic discovery; consumer profiling; treating consumer data responsibly; workplace monitoring; and advanced surveillance technologies. The chapter aims to balance the needs of businesses to collect and use data with individuals' rights to privacy.