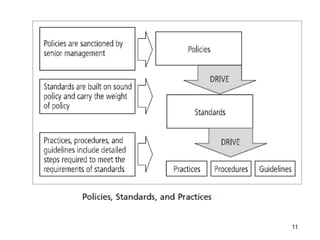
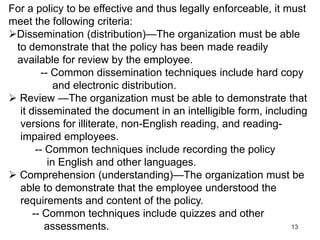
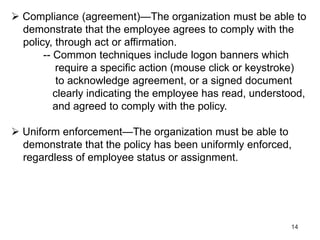
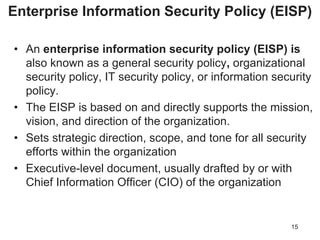
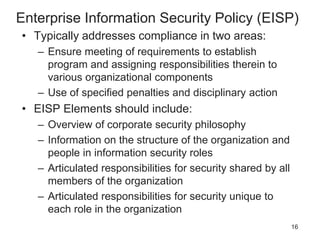
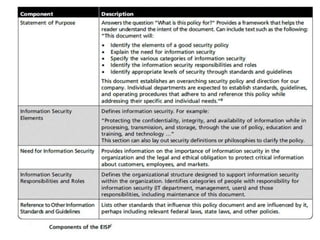
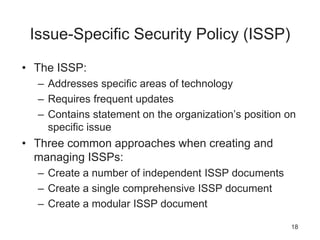
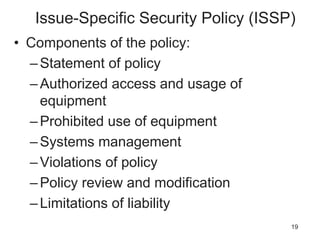
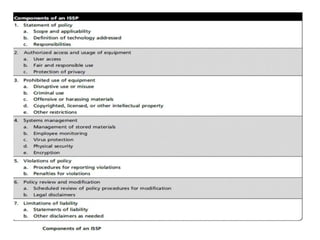
Management plays a key role in developing information security policies, standards, and practices that form the foundation of an organization's security program. These include enterprise policies that set strategic direction, issue-specific policies that address technology areas, and system-specific policies that provide technical guidance. Policies must be properly disseminated, understood, agreed to, and uniformly enforced. They also require ongoing management through regular reviews and updates to remain effective as an organization's needs change over time.