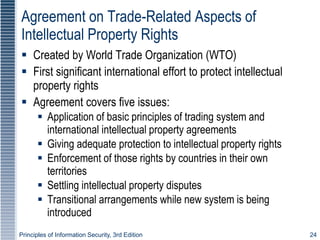
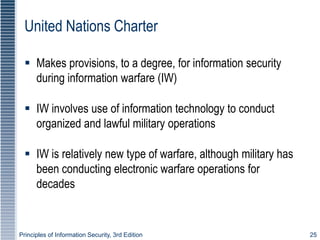
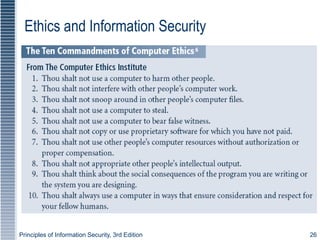
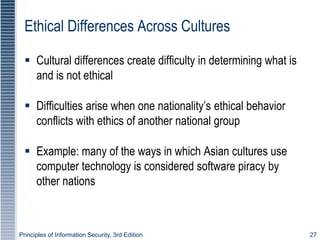
This document discusses laws, regulations, ethics, and professional organizations related to information security. It defines key concepts like laws, ethics, liability, due care and due diligence. Major sections cover relevant US laws, privacy laws, types of laws, and international legal issues. Professional ethics organizations and their codes are also summarized.