Recommended
PPT
PPT
PPT
PPT
Chap 03 underlying technology
PPT
PPT
PPT
PPT
Chap 27 next generation i pv6
PPT
PPT
PPT
PPT
PPT
PPT
PPT
PPT
PPT
PPT
Raj Jain The Ohio State University
PPT
Chap 05 ip addresses classfless
PPTX
Semantech: IT Architecture in the Enterprise
PDF
Computer Security Lecture 4.1: DES Supplementary Material
PPT
PPT
PPT
PPT
Chap 04 ip addresses classful
PPT
PDF
Computer Security Lecture 2: Classical Encryption Techniques 1
PPTX
Congestion control in tcp
PPT
Chap 13 stream control transmission protocol
PPT
More Related Content
PPT
PPT
PPT
PPT
Chap 03 underlying technology
PPT
PPT
PPT
PPT
Chap 27 next generation i pv6
Viewers also liked
PPT
PPT
PPT
PPT
PPT
PPT
PPT
PPT
PPT
PPT
Raj Jain The Ohio State University
PPT
Chap 05 ip addresses classfless
PPTX
Semantech: IT Architecture in the Enterprise
PDF
Computer Security Lecture 4.1: DES Supplementary Material
PPT
PPT
PPT
PPT
Chap 04 ip addresses classful
PPT
PDF
Computer Security Lecture 2: Classical Encryption Techniques 1
PPTX
Congestion control in tcp
More from Noctorous Jamal
PPT
Chap 13 stream control transmission protocol
PPT
PPT
PPT
Chap 06 delivery and routing of ip packets
PPT
Lecture 8 The Communication System Finalterm Slides
PPT
Lecture 7 The Communication System Finalterm Slides
PPT
Lecture 6 The Communication System Finalterm Slides
Chap 26 vpn 1. CChhaapptteerr 2266
VViirrttuuaall PPrriivvaattee NNeettwwoorrkkss aanndd
NNeettwwoorrkk AAddddrreessss TTrraannssllaattiioonn
Objectives
Upon completion you will be able to:
• Understand the difference between an internet and an extranet
• Understand private, hybrid, and virtual private networks
• Understand how VPN can guarantee privacy
• Understand the mechanism of NAT
TCP/IP Protocol Suite 1
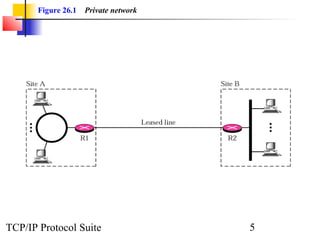
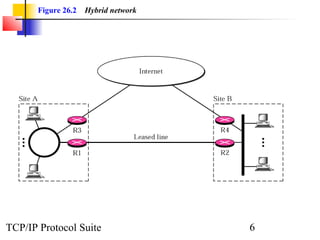
2. 26.1 PRIVATE NETWORKS
A private network is designed to be used only inside aann oorrggaanniizzaattiioonn.. IItt
aalllloowwss aacccceessss ttoo sshhaarreedd rreessoouurrcceess aanndd,, aatt tthhee ssaammee ttiimmee,, pprroovviiddeess
pprriivvaaccyy..
TThhee ttooppiiccss ddiissccuusssseedd iinn tthhiiss sseeccttiioonn iinncclluuddee::
IInnttrraanneett
EExxttrraanneett
AAddddrreessssiinngg
TCP/IP Protocol Suite 2
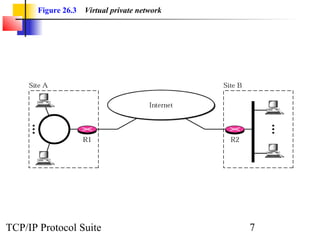
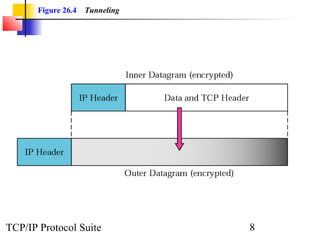
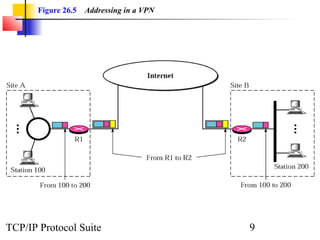
3. 4. 26.2 VIRTUAL PRIVATE
NETWORKS (VPN)
Virtual private network (VPN) is a technology ffoorr llaarrggee oorrggaanniizzaattiioonnss
tthhaatt uussee tthhee gglloobbaall IInntteerrnneett ffoorr bbootthh iinnttrraa-- aanndd iinntteerroorrggaanniizzaattiioonn
ccoommmmuunniiccaattiioonn,, bbuutt rreeqquuiirree pprriivvaaccyy iinn tthheeiirr iinnttrraaoorrggaanniizzaattiioonn
ccoommmmuunniiccaattiioonn..
TThhee ttooppiiccss ddiissccuusssseedd iinn tthhiiss sseeccttiioonn iinncclluuddee::
AAcchhiieevviinngg PPrriivvaaccyy
VVPPNN TTeecchhnnoollooggyy
TCP/IP Protocol Suite 4
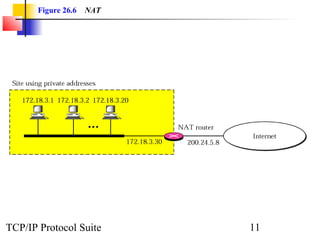
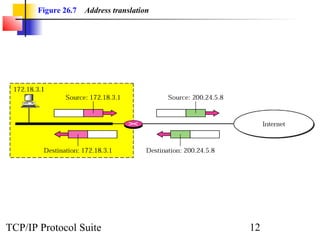
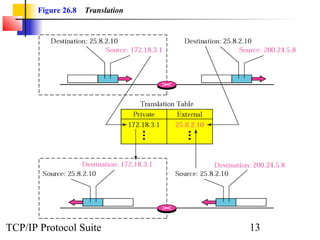
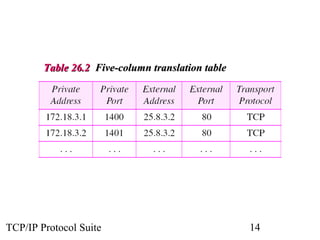
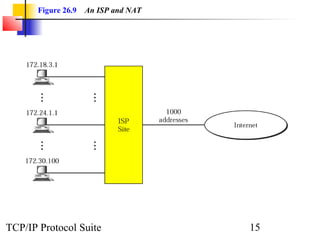
5. 6. 7. 8. 9. 10. 26.3 NETWORK ADDRESS
TRANSLATION (NAT)
Network address translation (NAT) allows a site to uussee aa sseett ooff pprriivvaattee
aaddddrreesssseess ffoorr iinntteerrnnaall ccoommmmuunniiccaattiioonn aanndd aa sseett ooff gglloobbaall IInntteerrnneett
aaddddrreesssseess ffoorr ccoommmmuunniiccaattiioonn wwiitthh aannootthheerr ssiittee.. TThhee ssiittee mmuusstt hhaavvee oonnllyy
oonnee ssiinnggllee ccoonnnneeccttiioonn ttoo tthhee gglloobbaall IInntteerrnneett tthhrroouugghh aa rroouutteerr tthhaatt rruunnss
NNAATT ssooffttwwaarree..
TThhee ttooppiiccss ddiissccuusssseedd iinn tthhiiss sseeccttiioonn iinncclluuddee::
AAddddrreessss TTrraannssllaattiioonn
TTrraannssllaattiioonn TTaabbllee
NNAATT aanndd IISSPP
TCP/IP Protocol Suite 10
11. 12. 13. 14. 15.