C:\Fakepath\=Information Management
•
1 like•127 views
Amor Group Information Management Solution
Report
Share
Report
Share
Download to read offline
Recommended
Modern IT Service Management Transformation - ITIL Indonesia

Presented at Online ITIL Indonesia Webinar #5.
Content:
> Setting up the context
> Understanding holistic IT Management point of view
> IT Service Management Transformation
> Key Performance Indicator (KPI)
> IT Service Catalogue
> IT Sourcing
> Agile Incident Management
Approaching Information Management from a Framework Perspective

This presentation provides the reader with a perspective on the use of a framework approach to Enterprise Information Management.
Siam key-facts

Service integration and management (SIAM) is a management methodology that can be applied in an environment that includes services sourced from a number of service providers.
Assembling the Jigsaw: Service Integration and Management in a Multisourced I...

Assembling the Jigsaw: Service Integration and Management in a Multisourced I...Information Services Group (ISG)
SIAM Whitepaper

White paper on The Future ICT Organisation: The Service Integration & Management Model (INPROC)
Recommended
Modern IT Service Management Transformation - ITIL Indonesia

Presented at Online ITIL Indonesia Webinar #5.
Content:
> Setting up the context
> Understanding holistic IT Management point of view
> IT Service Management Transformation
> Key Performance Indicator (KPI)
> IT Service Catalogue
> IT Sourcing
> Agile Incident Management
Approaching Information Management from a Framework Perspective

This presentation provides the reader with a perspective on the use of a framework approach to Enterprise Information Management.
Siam key-facts

Service integration and management (SIAM) is a management methodology that can be applied in an environment that includes services sourced from a number of service providers.
Assembling the Jigsaw: Service Integration and Management in a Multisourced I...

Assembling the Jigsaw: Service Integration and Management in a Multisourced I...Information Services Group (ISG)
SIAM Whitepaper

White paper on The Future ICT Organisation: The Service Integration & Management Model (INPROC)
Service Integration and Management (SIAM)

Presented by Goh Boon Nam, Chief of IT Service Management, Institute of Systems Science, NUS at itSMF Singapore 2015 Annual Conference on 13 Mar 2015.
McHenry whitepaper trc as asp recordkeeping service

Whitepaper describing value of running recordkeeping systems as an ASP.
How to build and operate an effective IT tooling strategy in a SIAM operating...

When operating within an outsourced multi-vendor / Service Integration & Management (SIAM) operating model it is important to have an effective IT tooling strategy.
11 Actions that will make your SIAM Programme successful

Service Integration & Management (SIAM) is a term given to IT Operating Models which cater for multi-vendor strategies. This presentation describes the 11 Actions that you must adopt to make your SIAM programme a success
Service Integration and Management 

Service integration and management (SIAM) is a management methodology that can be applied in an environment that includes services sourced from a number of service providers.
Leveraging IT to create business agility: Why leading IT organisations are re...

CIOs are under pressure. Some analysts are even predicting the end of the CIO role. In the light of digitalisation and an ever-increasing need for business agility, IT is becoming an embedded part of the business. Information technology is no longer just a utility but a deeply integrated driver of products and services within most companies. An ever-changing environment means that old assumptions on how to deliver IT services need to be revisited if the IT organisation is to remain relevant.
Data Center Flexibilty and Efficiency

A consolidated data center has been an attractive alternative for CIOs to protect the IT investment as many of them have realized that centralized infrastructure and processes help optimize the shared resources and in turn bring greater ROI from their IT investments. This whitepaper explains the various benefits of data center consolidation and how CIOs can work collaboratively with service providers to build an outcome based IT framework that can deliver cost efficiencies, savings and innovation in an organization.
SIAM Study - Comparing the Introduction of New IT Services via Simple and Com...

A Study to Compare the Introduction of typical New IT Services within a Single Tower and Multi-Tower SIAM Model using a mature set of ‘Plan-Build-Run’ project tasks
Conlcusion
The conclusions of this study for the introduction of New IT Services via Simple and Complex SIAM Models are:
Single Tower model is more efficient than a Muti-Tower Model
Due to security issues, more Design project tasks are required for New hosted cloud services than On-premise hosted services
Operating Enterprise IT as a Business

Traditionally, Enterprise IT has 'not' been operating as a customer-facing department, and its costs were allocated to business drivers out of bundled costs using an arbitrary driver. But the business aligned ITSM framework enables a company to run its IT operations as a business that aligns to the strategic needs of business to enable its growth.
Making SIAM Work (for you)

Service Integration & Management is all about managing delivery when multi-sourcing your IT services, instead of single sourcing or prime contracting.
Medi pragma documento di progetto della soluzione pf20-10

Documentazione Presentazione Progetto - Medi - Pragma
Resume 2015 sherry m

Assisting with the business case.
Planning and monitoring.
Eliciting requirements.
Requirements organization.
Translating and simplifying requirements.
Requirements management and communication.
Requirements analysis.
More Related Content
What's hot
Service Integration and Management (SIAM)

Presented by Goh Boon Nam, Chief of IT Service Management, Institute of Systems Science, NUS at itSMF Singapore 2015 Annual Conference on 13 Mar 2015.
McHenry whitepaper trc as asp recordkeeping service

Whitepaper describing value of running recordkeeping systems as an ASP.
How to build and operate an effective IT tooling strategy in a SIAM operating...

When operating within an outsourced multi-vendor / Service Integration & Management (SIAM) operating model it is important to have an effective IT tooling strategy.
11 Actions that will make your SIAM Programme successful

Service Integration & Management (SIAM) is a term given to IT Operating Models which cater for multi-vendor strategies. This presentation describes the 11 Actions that you must adopt to make your SIAM programme a success
Service Integration and Management 

Service integration and management (SIAM) is a management methodology that can be applied in an environment that includes services sourced from a number of service providers.
Leveraging IT to create business agility: Why leading IT organisations are re...

CIOs are under pressure. Some analysts are even predicting the end of the CIO role. In the light of digitalisation and an ever-increasing need for business agility, IT is becoming an embedded part of the business. Information technology is no longer just a utility but a deeply integrated driver of products and services within most companies. An ever-changing environment means that old assumptions on how to deliver IT services need to be revisited if the IT organisation is to remain relevant.
Data Center Flexibilty and Efficiency

A consolidated data center has been an attractive alternative for CIOs to protect the IT investment as many of them have realized that centralized infrastructure and processes help optimize the shared resources and in turn bring greater ROI from their IT investments. This whitepaper explains the various benefits of data center consolidation and how CIOs can work collaboratively with service providers to build an outcome based IT framework that can deliver cost efficiencies, savings and innovation in an organization.
SIAM Study - Comparing the Introduction of New IT Services via Simple and Com...

A Study to Compare the Introduction of typical New IT Services within a Single Tower and Multi-Tower SIAM Model using a mature set of ‘Plan-Build-Run’ project tasks
Conlcusion
The conclusions of this study for the introduction of New IT Services via Simple and Complex SIAM Models are:
Single Tower model is more efficient than a Muti-Tower Model
Due to security issues, more Design project tasks are required for New hosted cloud services than On-premise hosted services
Operating Enterprise IT as a Business

Traditionally, Enterprise IT has 'not' been operating as a customer-facing department, and its costs were allocated to business drivers out of bundled costs using an arbitrary driver. But the business aligned ITSM framework enables a company to run its IT operations as a business that aligns to the strategic needs of business to enable its growth.
Making SIAM Work (for you)

Service Integration & Management is all about managing delivery when multi-sourcing your IT services, instead of single sourcing or prime contracting.
What's hot (12)
McHenry whitepaper trc as asp recordkeeping service

McHenry whitepaper trc as asp recordkeeping service
How to build and operate an effective IT tooling strategy in a SIAM operating...

How to build and operate an effective IT tooling strategy in a SIAM operating...
11 Actions that will make your SIAM Programme successful

11 Actions that will make your SIAM Programme successful
Leveraging IT to create business agility: Why leading IT organisations are re...

Leveraging IT to create business agility: Why leading IT organisations are re...
SIAM Study - Comparing the Introduction of New IT Services via Simple and Com...

SIAM Study - Comparing the Introduction of New IT Services via Simple and Com...
AIIM Info360 Conference - What ECM Success Looks Like - 2010 04 21

AIIM Info360 Conference - What ECM Success Looks Like - 2010 04 21
Viewers also liked
Medi pragma documento di progetto della soluzione pf20-10

Documentazione Presentazione Progetto - Medi - Pragma
Resume 2015 sherry m

Assisting with the business case.
Planning and monitoring.
Eliciting requirements.
Requirements organization.
Translating and simplifying requirements.
Requirements management and communication.
Requirements analysis.
Viewers also liked (12)
Medi pragma documento di progetto della soluzione pf20-10

Medi pragma documento di progetto della soluzione pf20-10
Similar to C:\Fakepath\=Information Management
TAC Expertise-as-a-Service 

It is a fact of life that the IT department is a necessary yet costly part of today’s small and midsize businesses (SMBs). Many SMBs have reduced the size of the IT department to the point where costs cannot seemingly be cut any further. The result of these cuts is that service has been severely degraded, customer satisfaction is down, and the real value of IT to the business is being questioned. And still SMB IT leaders are being asked to do much more with much less. How does an IT department cope with these ever increasing demands and diminishing budgets?
Smart SMB CIOs are leveraging the Expertise-as-a-Service® (EaaS™) model to transform their organizations. Legal and finance departments have leveraged outside counsel and accounting firms for decades, with the IT department being one of the last of the major departments within the business to move to this low-fixed-cost model. Taking a page from the legal and finance departments’ “playbooks,” EaaS is used as an extension of the IT department. EaaS brings cost savings by enabling IT to reduce and reallocate in-house resources more effectively, while retaining on-demand access to scalable high quality expertise, information, and performance measurement. EaaS gives IT the ability to quickly adjust to changing business goals and drivers, encourage innovation, and increase productivity while reducing fixed costs.
The Value Of Business Information March 2010

Notes from the Value of Business Information Presentation
Actionable Guidance to Succeed in Enterprise-Class Privileged Access Management

Actionable Guidance to Succeed in Enterprise-Class Privileged Access ManagementEnterprise Management Associates
According to EMA research, 79% of organizations consider privileged access management (PAM) to be very important or critical to their business operations. However, 76% of organizations experience significant privileged access policy violations each year, exposing the most sensitive business information and IT resources to extreme risks of exposure.
These slides—based on the webinar from EMA Research and Remediant—provide actionable guidance on how to advance your PAM implementations regardless of where you are currently in your security management journey.
Enterprise Content Management in Microsoft SharePoint 2007

This is a CIO-level presentation discussing how Microsoft approaches the topic of ECM. SharePoint is discussed as a technical framework and a foundation to build a solution. By the end of the presentation, if you would like more information on SharePoint or related collaboration products from Microsoft, please email viralta@microsoft.com or visit www.microsoft.com/sharepoint
Take Charge of Your Cloud Migrations with Dependency Mapping, Inventory and U...

Take Charge of Your Cloud Migrations with Dependency Mapping, Inventory and U...Enterprise Management Associates
Leveraging extensive research and interviews from leading IT analyst firm Enterprise Management Associates (EMA), these slides based on the webinar will provide you with unique insights into cloud adoption, along with associated trends, such as shadow IT.
These slides also delve into how innovative approaches to dependency mapping, inventory and usage can help to make public and private cloud migrations more effective in optimizing costs and maximizing value.Welcome to Systems Plus

Systems Plus has consistently designed, developed and implemented solutions that have met or exceeded customers expectations over the years.
Salesforce Platform: Governance and the Social Enterprise

The road to the Social Enterpise is transformative, but IT departments need to ensure a smooth transition. Join us to learn first hand from customers who have made the journey, how they defined and managed the change with a well crafted governance strategy.
iMark Company Brochure

iMark is a IT Solutions, Consulting and Services Company. iMark with extensive experiences in Infrastructure, Energy & Utilities, Mining & Metals, FMCG, Pharma, Real Estate, Logistics & Transportation Industries; helps organizations to bring Process Intelligence & Operation Excellence through the effective use of SAP ERP
JRM for communications

JRM is a dynamic industry leader providing technology integrated solutions and converged infrastructure.
JRM serves clients with a leading edge technology solutions, including unified communications,collaboration, servers, storage, switches, routers, data centers, wireless networking, wired networking, passive and active networking.
JRM for communication have more than 21 one partner in Technology solutions, including NEC, Dell EMC, Vmware, Fortinet, polycom, Cisco, Netronics, Extreme, Excel, Axis and more.
Similar to C:\Fakepath\=Information Management (20)
Actionable Guidance to Succeed in Enterprise-Class Privileged Access Management

Actionable Guidance to Succeed in Enterprise-Class Privileged Access Management
Enterprise Content Management in Microsoft SharePoint 2007

Enterprise Content Management in Microsoft SharePoint 2007
Take Charge of Your Cloud Migrations with Dependency Mapping, Inventory and U...

Take Charge of Your Cloud Migrations with Dependency Mapping, Inventory and U...
Salesforce Platform: Governance and the Social Enterprise

Salesforce Platform: Governance and the Social Enterprise
Epgp (one year) 2009-10_isop_group assignment_group 4_24dec09

Epgp (one year) 2009-10_isop_group assignment_group 4_24dec09
Recently uploaded
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

In questo evento online gratuito, organizzato dalla Community Italiana di UiPath, potrai esplorare le nuove funzionalità di Autopilot, il tool che integra l'Intelligenza Artificiale nei processi di sviluppo e utilizzo delle Automazioni.
📕 Vedremo insieme alcuni esempi dell'utilizzo di Autopilot in diversi tool della Suite UiPath:
Autopilot per Studio Web
Autopilot per Studio
Autopilot per Apps
Clipboard AI
GenAI applicata alla Document Understanding
👨🏫👨💻 Speakers:
Stefano Negro, UiPath MVPx3, RPA Tech Lead @ BSP Consultant
Flavio Martinelli, UiPath MVP 2023, Technical Account Manager @UiPath
Andrei Tasca, RPA Solutions Team Lead @NTT Data
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
Recently uploaded (20)
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
C:\Fakepath\=Information Management
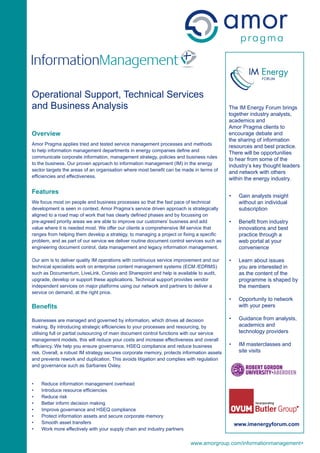
- 1. InformationManagement Operational Support, Technical Services and Business Analysis The IM Energy Forum brings together industry analysts, academics and Amor Pragma clients to Overview encourage debate and the sharing of information Amor Pragma applies tried and tested service management processes and methods resources and best practice. to help information management departments in energy companies define and There will be opportunities communicate corporate information, management strategy, policies and business rules to hear from some of the to the business. Our proven approach to information management (IM) in the energy industry’s key thought leaders sector targets the areas of an organisation where most benefit can be made in terms of and network with others efficiencies and effectiveness. within the energy industry. Features • Gain analysts insight We focus most on people and business processes so that the fast pace of technical without an individual development is seen in context. Amor Pragma’s service driven approach is strategically subscription aligned to a road map of work that has clearly defined phases and by focussing on pre-agreed priority areas we are able to improve our customers’ business and add • Benefit from industry value where it is needed most. We offer our clients a comprehensive IM service that innovations and best ranges from helping them develop a strategy, to managing a project or fixing a specific practice through a problem, and as part of our service we deliver routine document control services such as web portal at your engineering document control, data management and legacy information management. convenience Our aim is to deliver quality IM operations with continuous service improvement and our • Learn about issues technical specialists work on enterprise content management systems (ECM /EDRMS) you are interested in such as Documentum, LiveLink, Conisio and Sharepoint and help is available to audit, as the content of the upgrade, develop or support these applications. Technical support provides vendor programme is shaped by independent services on major platforms using our network and partners to deliver a the members service on demand, at the right price. • Opportunity to network Benefits with your peers Businesses are managed and governed by information, which drives all decision • Guidance from analysts, making. By introducing strategic efficiencies to your processes and resourcing, by academics and utilising full or partial outsourcing of main document control functions with our service technology providers management models, this will reduce your costs and increase effectiveness and overall efficiency. We help you ensure governance, HSEQ compliance and reduce business • IM masterclasses and risk. Overall, a robust IM strategy secures corporate memory, protects information assets site visits and prevents rework and duplication. This avoids litigation and complies with regulation and governance such as Sarbanes Oxley. • Reduce information management overhead • Introduce resource efficiencies • Reduce risk • Better inform decision making • Improve governance and HSEQ compliance • Protect information assets and secure corporate memory • Smooth asset transfers www.imenergyforum.com • Work more effectively with your supply chain and industry partners www.amorgroup.com/informationmanagement+
- 2. tel: +44 (0)141 814 3700 fax: +44 (0)141 814 3701 09.03.10PR/ManagedServices.UK.print email: info@amorgroup.com web: www.amorgroup.com