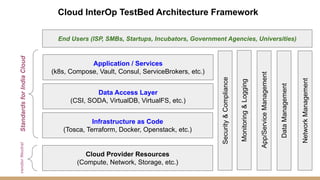
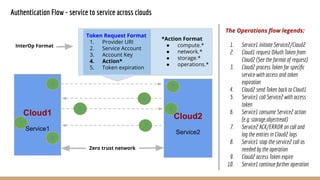
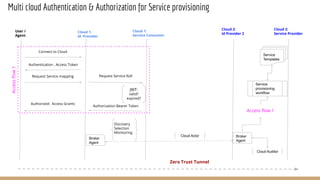
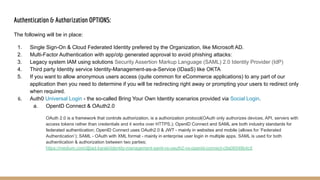
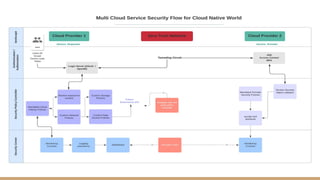
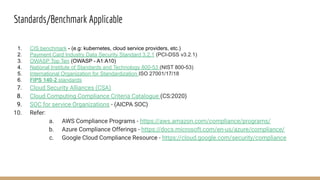
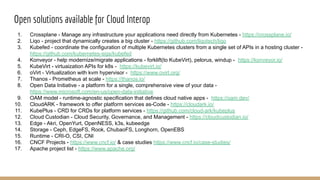
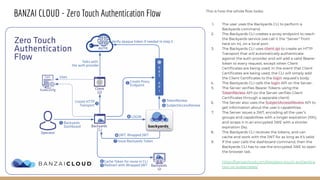
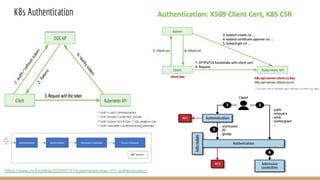
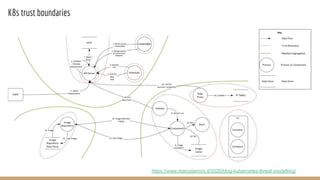
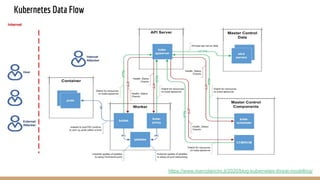
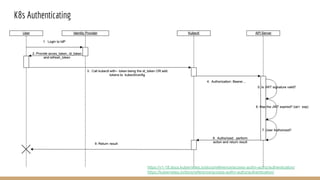
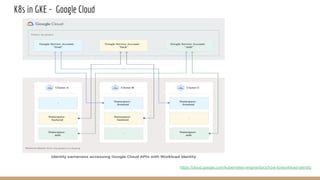
The document details the implementation and security access for the CCICI cloud interoperability testbed, emphasizing multi-cloud authentication, authorization, and security measures. It outlines a framework for securely managing cloud resources and services, integrating standards and best practices for cloud compliance. Additionally, it presents open-source solutions and major cloud vendor announcements relevant to interoperability and hybrid cloud solutions.