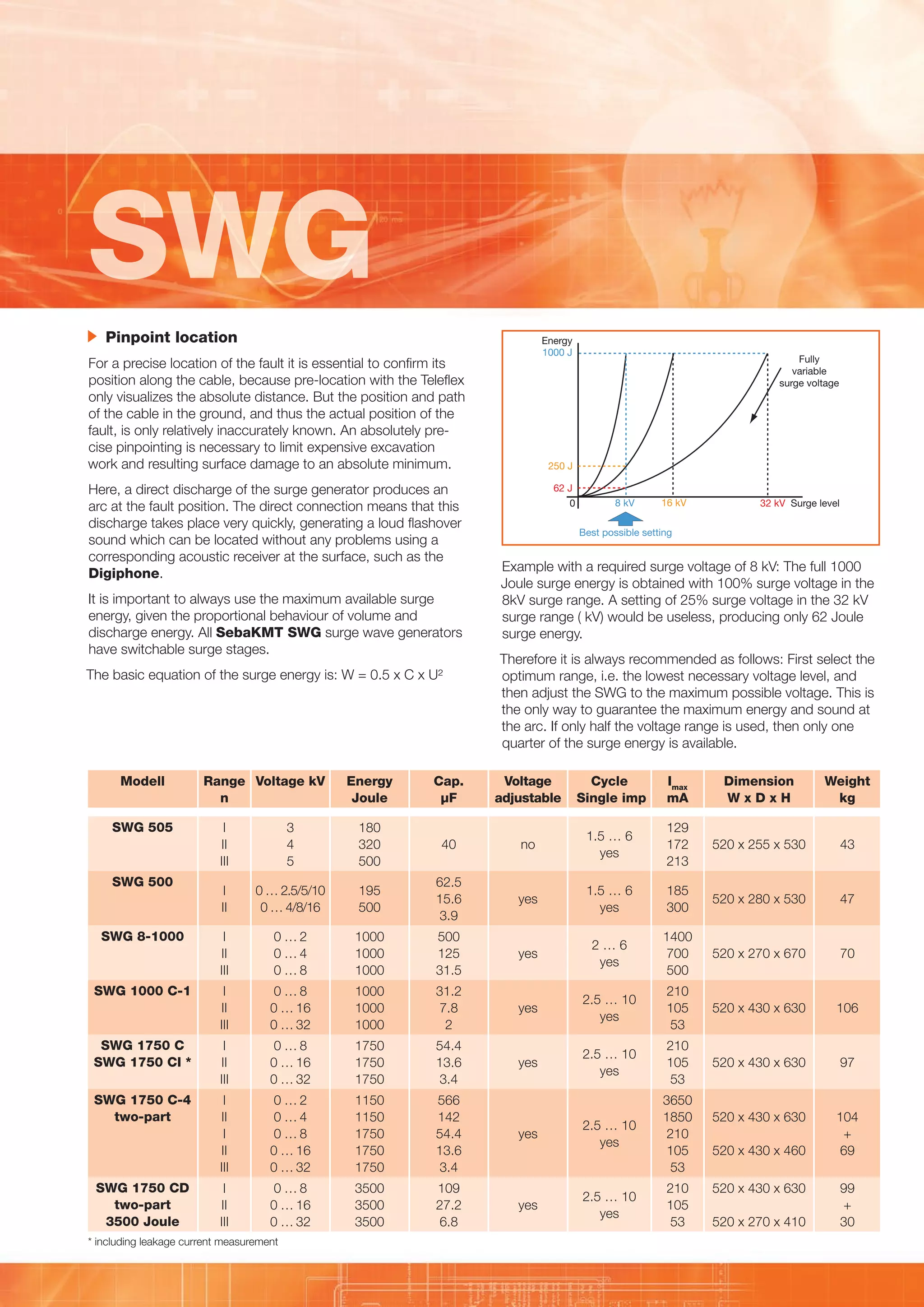
Surge wave generators (SWG) are used with reflectometers for cable fault location. They generate surges that create arcs at faults, allowing transient waves to be recorded and fault distances to be determined. SWGs are available for voltages up to 3500kV and energies up to 3500J. They use switchable capacitors and surge stages to optimize energy for prelocation and pinpointing faults. A Digiphone receiver uses the difference in arrival time between electromagnetic and acoustic signals to precisely locate faults.