Embed presentation
Downloaded 96 times




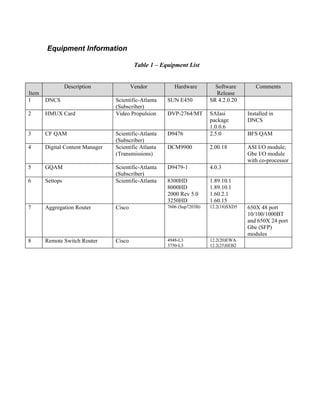

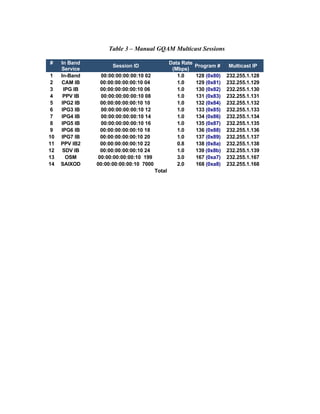



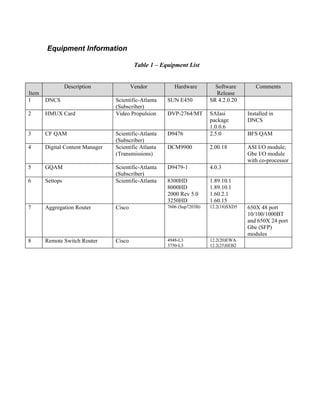
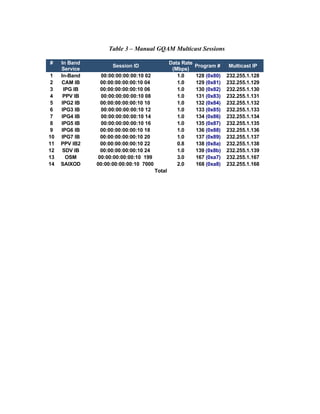
This document provides configuration steps for distributing BFS in-band data over a Gigabit Ethernet network using a Scientific Atlanta DCM 9900 digital content manager. Key steps include configuring the DCM 9900 to output each BFS source as an individual SPTS with a unique multicast IP address. On the DNCS, a multicast session is defined for each BFS source using the GQAM and configured IP address. Routers are configured for IP multicast routing and IGMP. Testing verified guide, PPV, and application data but image downloads failed due to a known defect when using OSM automux across multiple frequencies.