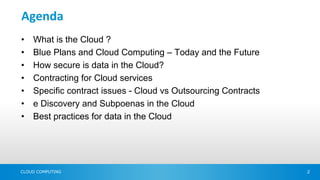
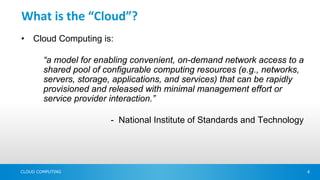
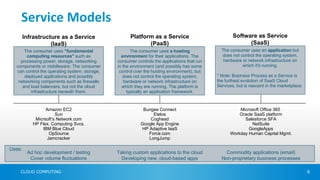
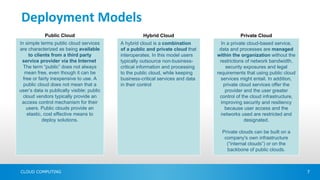
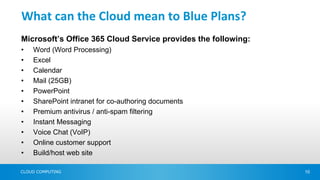
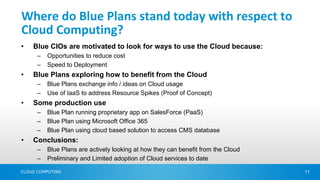
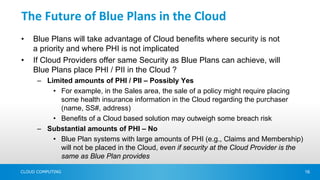
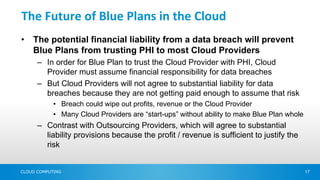
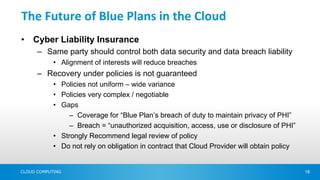
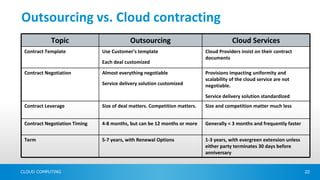
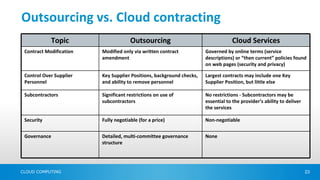
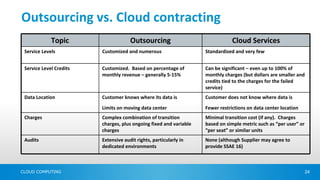
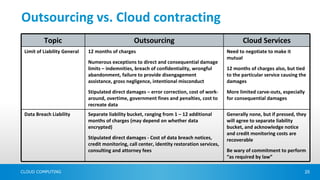
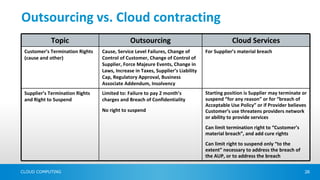
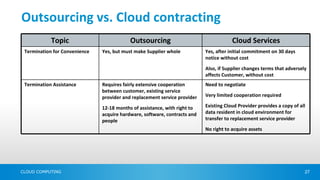
The document discusses critical considerations for healthcare organizations, referred to as 'blue plans,' contemplating the transition to cloud computing. Key topics include the definition of cloud computing, its service models, security concerns regarding data storage and management, and the contrasting contract negotiation processes between traditional outsourcing and cloud services. It concludes that while blue plans are actively exploring cloud benefits, significant hesitance remains around storing sensitive personal health information in the cloud due to potential financial liabilities.




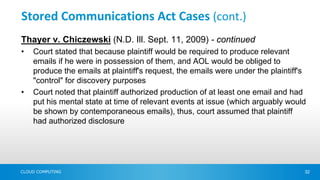
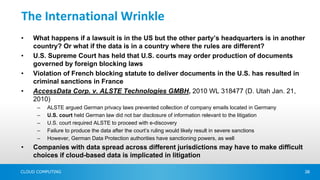
![Stored Communications Act Cases (cont.)
Chasten v. Franklin (No. C10-80205 MISC JW (HRL), 2010 WL
4065606 (N.D. Cal. Oct. 14, 2010))
•Defendant in civil rights case served subpoena on Yahoo seeking plaintiff's
emails
•Plaintiff argued SCA prohibited Yahoo from disclosing his emails
•Court agreed and quashed subpoena stating:
– "Because no exception applies, compliance with the [third-party] subpoena would
be an invasion of the specific interests that the SCA seeks to protect."
•Unlike Thayer, Chasten court did not examine whether plaintiff could/should be
ordered to consent to Yahoo producing emails
•Court's failure to discuss whether account holder could be forced to consent to
disclosure was unique
CLOUD COMPUTING 33](https://image.slidesharecdn.com/bcbsasummitcloudcomputingissues111207-13237086267648-phpapp01-111212111107-phpapp01/85/BCBSA-Summit-Cloud-Computing-Issues-Dec-2012-33-320.jpg)