The document provides instructions for configuring basic settings on Cisco switches and routers, including enabling privileged modes, setting passwords, configuring interfaces, VLANs, routing protocols, ACLs, SNMP, and more. Example commands are given for tasks like configuring device hostnames, IP addresses, routing protocols, trunking, VLANs, DHCP, ACLs, and other common switch and router configurations.
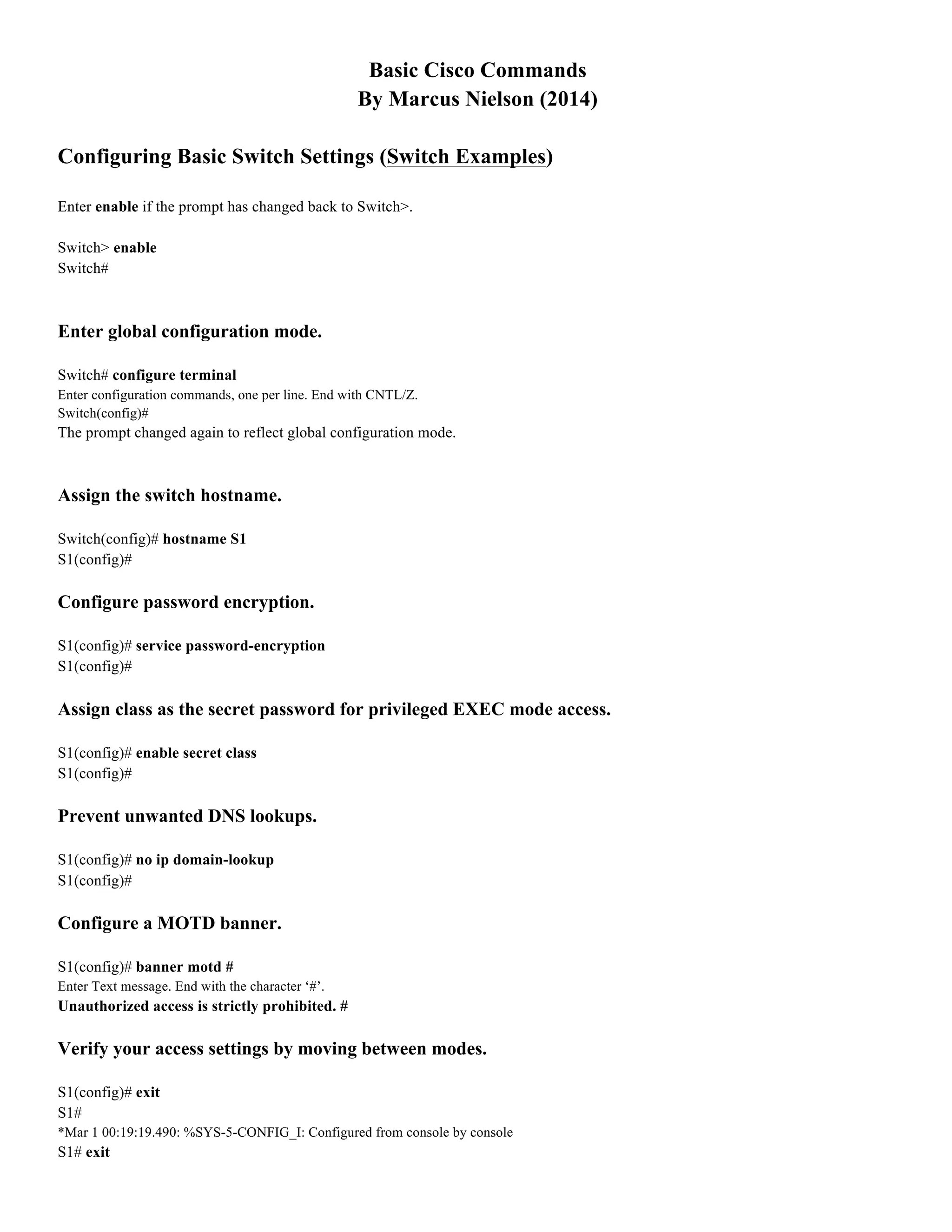
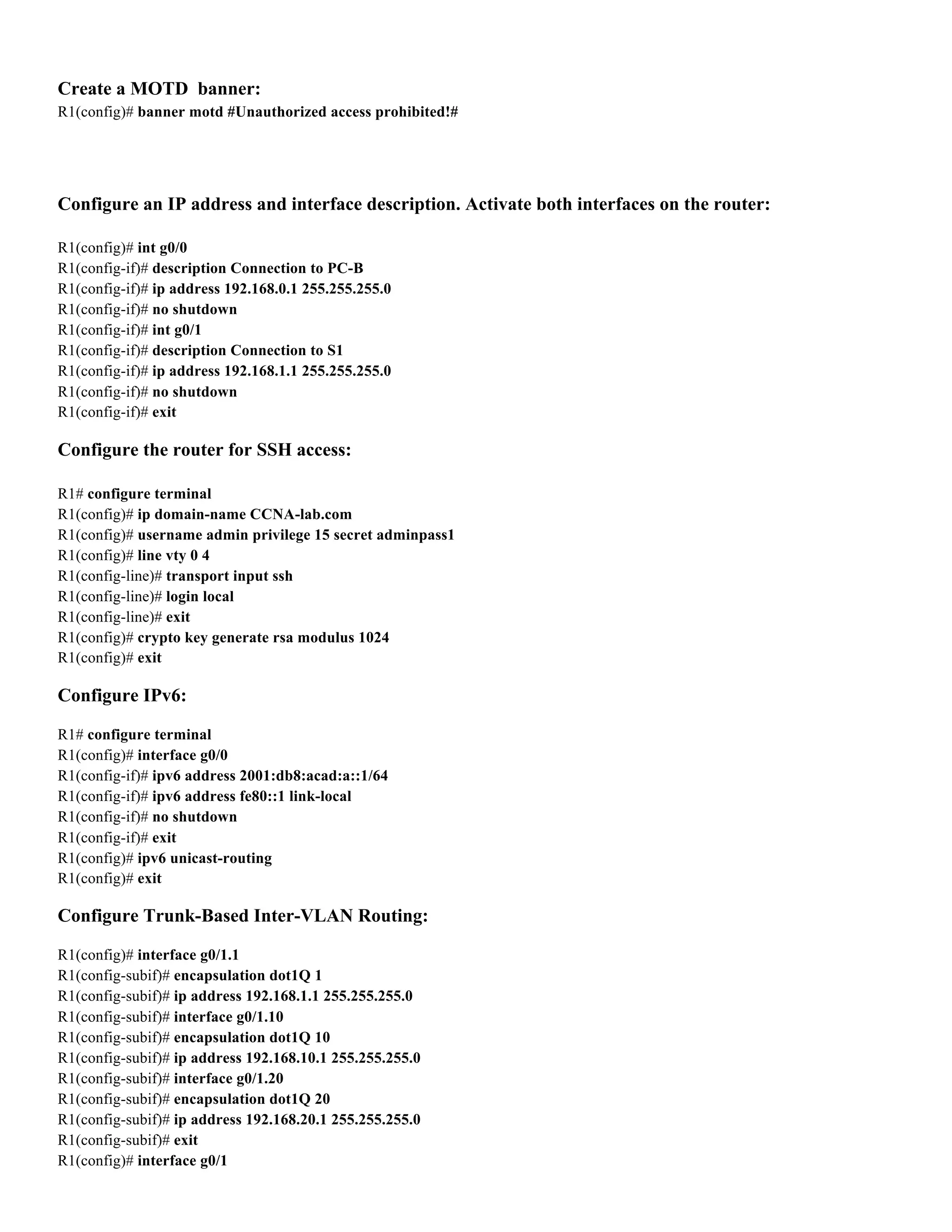
![S1(config)# interface port-channel 1
S1(config-if)# switchport mode trunk
S1(config-if)# switchport trunk native vlan 99
Delete the VLAN database:
S1# delete vlan.dat
Delete filename [vlan.dat]?
Delete flash:/vlan.dat? [confirm]
S1#
Configuring Basic Router Settings (Router Examples) ==========================
Configure the router:
Router> enable
Router#
Router# config terminal
Router(config)#
Router(config)#
hostname
R1.
R1(config)#
no
ip
domain-‐lookup
R1(config)#
security
passwords
min-‐length
10
R1(config)#
enable
secret
cisco12345
Setting a console password on a router:
R1(config)# line con 0
R1(config-line)# password ciscoconpass
R1(config-line)# exec-timeout 5 0
R1(config-line)# login
R1(config-line)# logging synchronous
R1(config-line)# exit
R1(config)#
Assign VTY password:
R1(config)# line vty 0 4
R1(config-line)# password ciscovtypass
R1(config-line)# exec-timeout 5 0
R1(config-line)# login
R1(config-line)# logging synchronous
R1(config-line)# exit
R1(config)#
Encrypt the clear text passwords:
R1(config)# service password-encryption](https://image.slidesharecdn.com/basicciscocommandsbymarcusnielson2-191023183018/75/Basic-cisco-commands_by_marcus_nielson_2-5-2048.jpg)