This document summarizes the steps taken to copy a CD to an image file and then burn that image file to a new CD. It analyzed the original CD, copied the audio tracks and data to an image file, and prepared the burner and blank disc to write the image in disc-at-once mode. However, the process was aborted by the user before the image could be burned to the new disc.

![Analyzing disc
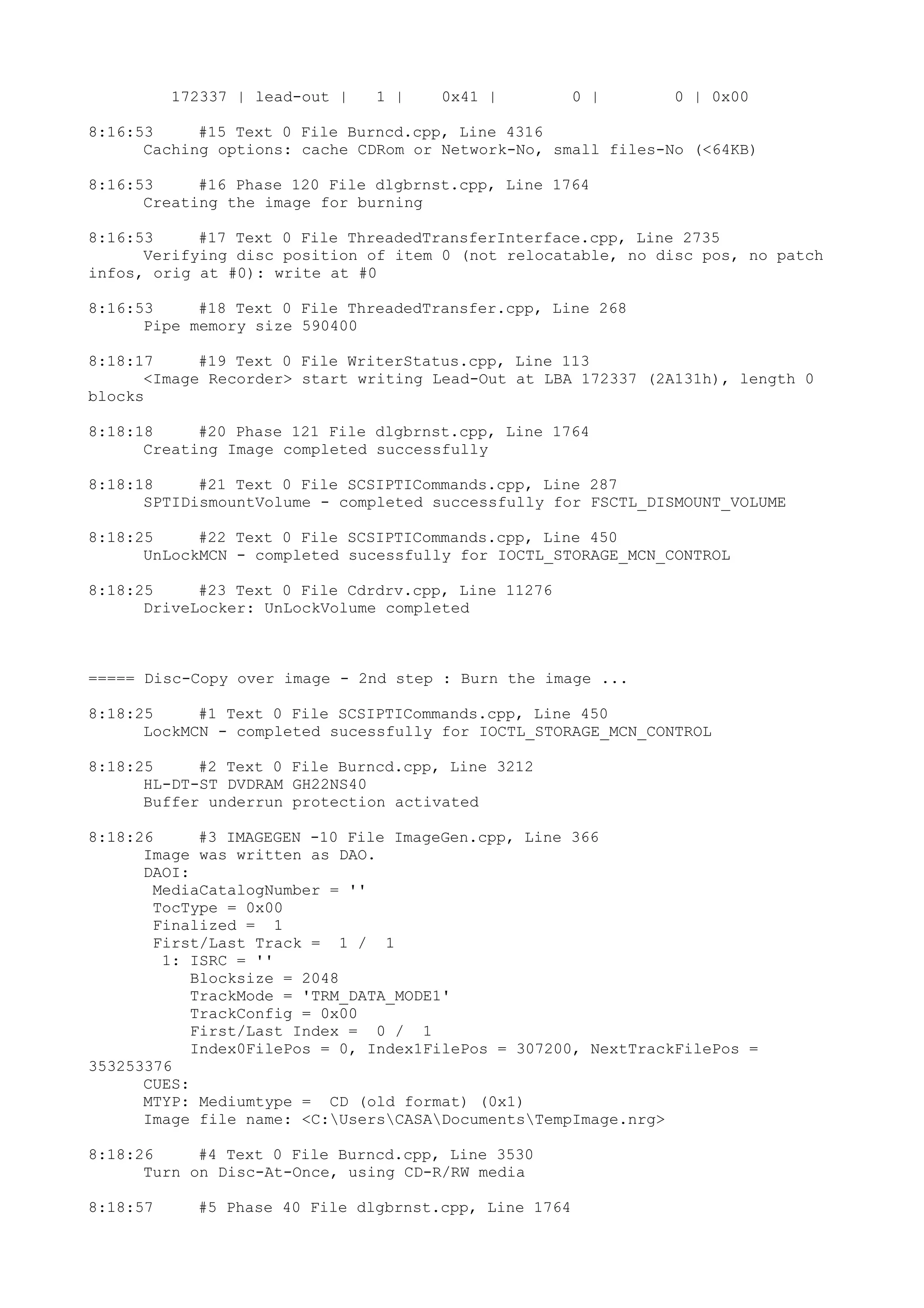
8:16:50 #6 CDCOPY -1 File CDCopy.cpp, Line 1916
The CD is copyrighted
8:16:53 #7 Text 0 File CDCopy.cpp, Line 2132
_Index0_ _______Index1_______ PostPause ___LastBlockOfTrack_
Track 1: 0 0 ( 0:02.00) 172337 172336 ( 38:19.61)
8:16:53 #8 Text 0 File CDCopy.cpp, Line 840
Copy options: copy on-the-fly: ON
read ISRC/MCN: OFF
use jitter correction: OFF
data options
ignore read error: ON write defekt blocks OFF
read raw data: OFF read r-w subchannel data: OFF
audio options
ignore read error: ON
read indexes: OFF read r-w subchannel data: OFF
source disc does not look like CD Extra
01. 0 - 172337 = 172337, data (TRM_DATA_MODE1, block size 2048)
8:16:53 #9 Text 0 File Burncd.cpp, Line 3530
Turn on Disc-At-Once, using CD-R/RW media
8:16:53 #10 Text 0 File DlgWaitCD.cpp, Line 307
Last possible write address on media: 445499 ( 99:01.74)
Last address to be written: 172336 ( 38:19.61)
8:16:53 #11 Text 0 File DlgWaitCD.cpp, Line 319
Write in overburning mode: NO (enabled: CD)
8:16:53 #12 Text 0 File DlgWaitCD.cpp, Line 493
>>> Protocol of DlgWaitCD activities: <<<
=========================================
8:16:53 #13 Text 0 File ThreadedTransferInterface.cpp, Line 785
Setup items (after recorder preparation)
0: TRM_DATA_MODE1 (1 - Data (mode 1))
2 indices, index0 (150) not provided
original disc pos #0 + 172337 (172337) = #172337/38:17.62
not relocatable, disc pos for caching/writing not required/not
required
-> TRM_DATA_MODE1, 2048, config 0, wanted index0 0 blocks, length
172337 blocks [Image Recorder]
--------------------------------------------------------------
8:16:53 #14 Text 0 File ThreadedTransferInterface.cpp, Line 986
Prepare [Image Recorder] for write in CUE-sheet-DAO
DAO infos:
==========
MCN: ""
TOCType: 0x00; Session Closed, disc fixated
Tracks 1 to 1: Idx 0 Idx 1
Next Trk
1: TRM_DATA_MODE1, 2048/0x00, FilePos 0 307200
353253376, ISRC ""
DAO layout:
===========
___Start_|____Track_|_Idx_|_CtrlAdr_|_____Size_|______NWA_|
_RecDep__________
-150 | lead-in | 0 | 0x41 | 0 | 0 | 0x00
-150 | 1 | 0 | 0x41 | 0 | 0 | 0x00
0 | 1 | 1 | 0x41 | 172337 | 172337 | 0x00](https://image.slidesharecdn.com/barioscrosober-140708103105-phpapp01/75/Barios-crosober-2-2048.jpg)