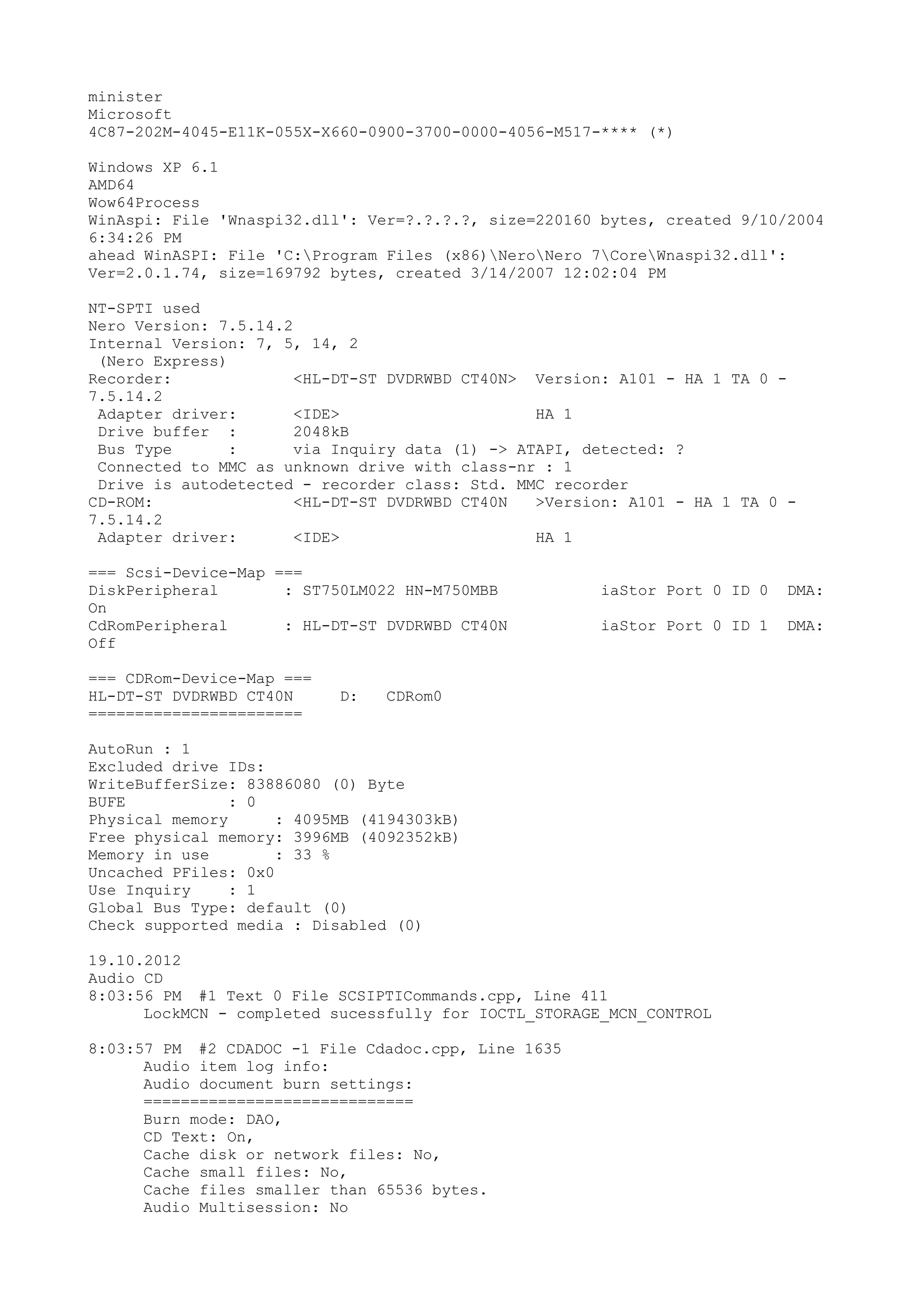
The document provides details from the burning of an audio CD using Nero software. It includes information about the hardware and software used, the audio files being burned, and a log of the burning process. The audio CD contains 10 tracks with a total runtime of 54 minutes and contains .wav files. The burning process uses disc-at-once mode on a HL-DT-ST DVD burner and proceeds without issues according to the log.
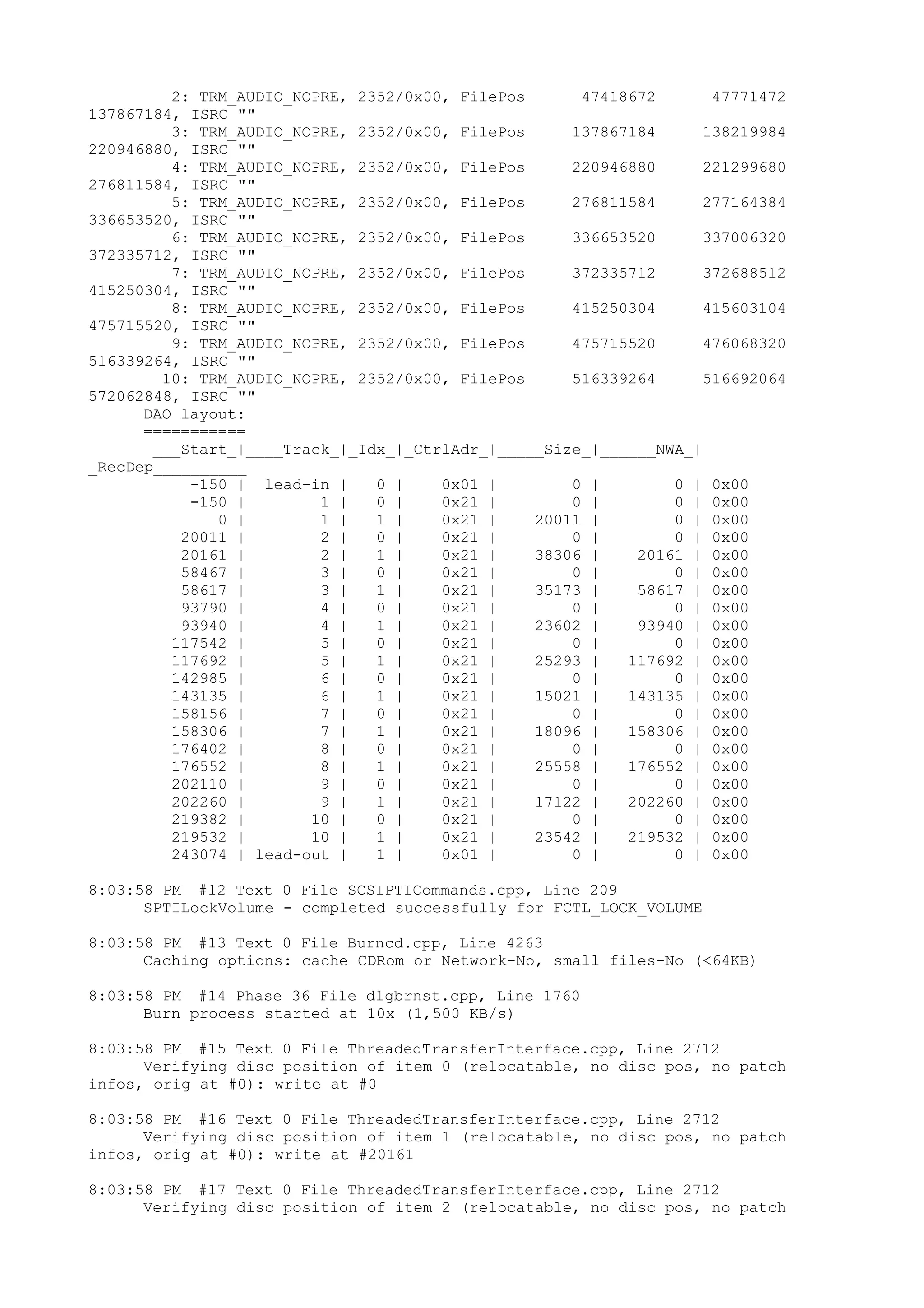
![List of audio tracks:
=====================
Track 01: Length: 04:26.61, Pause frames: 150, Filters: 0, Name: 'bless
like that.wav'.
Track 02: Length: 08:30.56, Pause frames: 150, Filters: 0, Name:
'faith.wav'.
Track 03: Length: 07:48.73, Pause frames: 150, Filters: 0, Name: 'GOD
favor me.wav'.
Track 04: Length: 05:14.52, Pause frames: 150, Filters: 0, Name: 'GOD
GRACE.wav'.
Track 05: Length: 05:37.18, Pause frames: 150, Filters: 0, Name:
'EVERTHING.wav'.
Track 06: Length: 03:20.21, Pause frames: 150, Filters: 0, Name:
'determime_EQ.wav'.
Track 07: Length: 04:01.21, Pause frames: 150, Filters: 0, Name: 'i
understand.wav'.
Track 08: Length: 05:40.58, Pause frames: 150, Filters: 0, Name: 'IN THE
MORNING.wav'.
Track 09: Length: 03:48.22, Pause frames: 150, Filters: 0, Name: 'it not
over.wav'.
Track 10: Length: 05:13.67, Pause frames: 150, Filters: 0, Name:
'forever.wav'.
Total size: 54:02.74
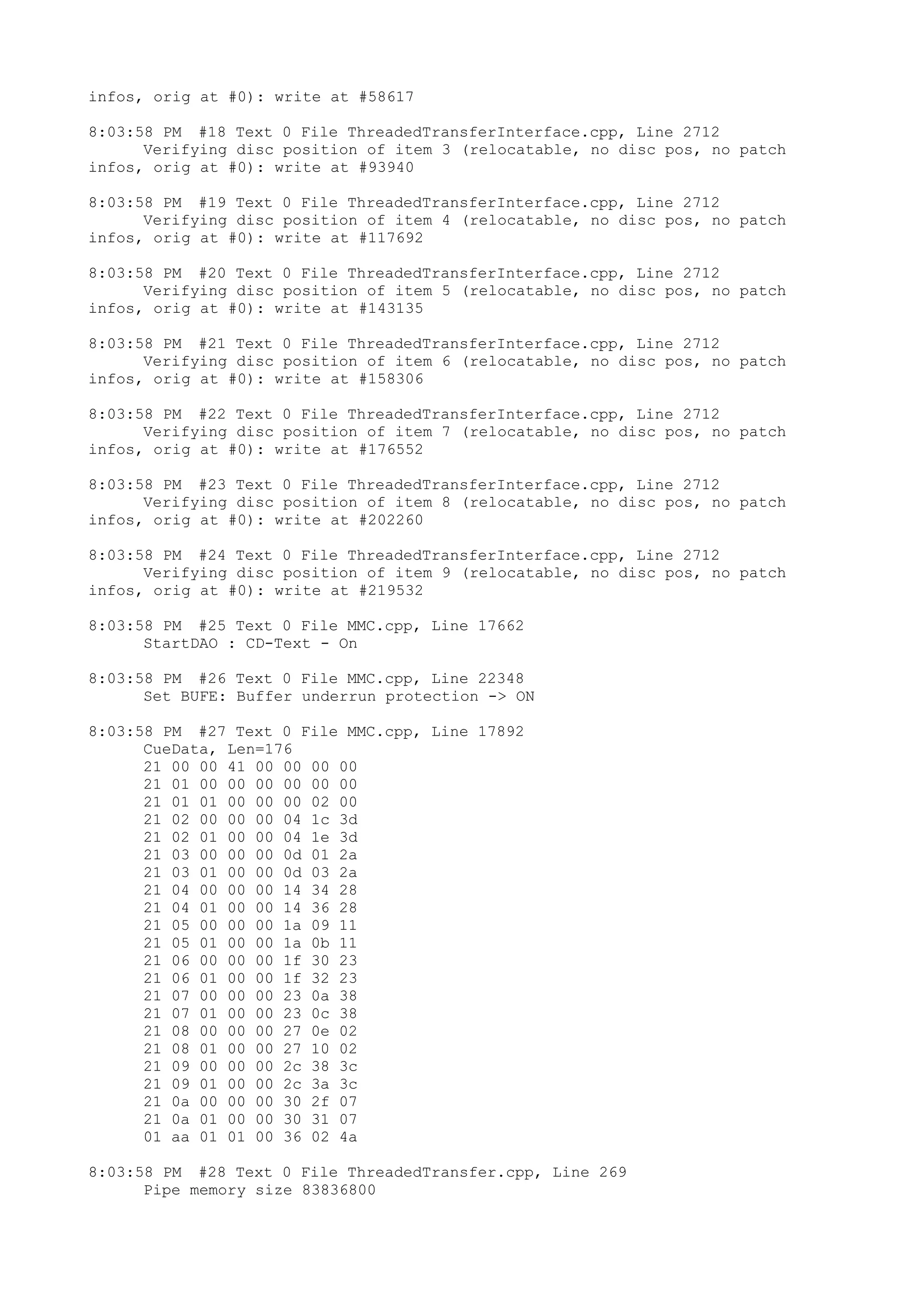
8:03:57 PM #3 Text 0 File Burncd.cpp, Line 3178
HL-DT-ST DVDRWBD CT40N
Buffer underrun protection activated
8:03:57 PM #4 Text 0 File AudioCompilationImpl.cpp, Line 838
DRM: StartDrmRecording(RealRec:1, ImageRec:0, Copies:1)
DRM: Beginning burn process.
8:03:57 PM #5 Text 0 File Burncd.cpp, Line 3490
Turn on Disc-At-Once, using CD-R/RW media
8:03:58 PM #6 Text 0 File DlgWaitCD.cpp, Line 307
Last possible write address on media: 359847 ( 79:59.72)
Last address to be written: 243073 ( 54:02.73)
8:03:58 PM #7 Text 0 File DlgWaitCD.cpp, Line 319
Write in overburning mode: NO (enabled: CD)
8:03:58 PM #8 Text 0 File DlgWaitCD.cpp, Line 2940
Recorder: HL-DT-ST DVDRWBD CT40N;
CDRW code: 00 97 25 30; OSJ entry from: INFODISC Technology Co., Ltd.
ATIP Data:
Special Info [hex] 1: B3 00 CE, 2: 61 19 1E (LI 97:25.30), 3: 4F
3B 49 (LO 79:59.73)
Additional Info [hex] 1: 24 1A D8, 2: 26 B2 4A, 3: 00 80 80 (invalid)
8:03:58 PM #9 Text 0 File DlgWaitCD.cpp, Line 493
>>> Protocol of DlgWaitCD activities: <<<
=========================================
8:03:58 PM #10 Text 0 File ThreadedTransferInterface.cpp, Line 792
Setup items (after recorder preparation)
0: TRM_AUDIO_NOPRE (bless like that.wav)
2 indices, index0 (150) not provided
original disc pos #0 + 20011 (20011) = #20011/4:26.61
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
20011 blocks [D: HL-DT-ST DVDRWBD CT40N]
1: TRM_AUDIO_NOPRE (faith.wav)
2 indices, index0 (150) not provided](https://image.slidesharecdn.com/iunderstand-130121214144-phpapp01/75/I-understand-2-2048.jpg)
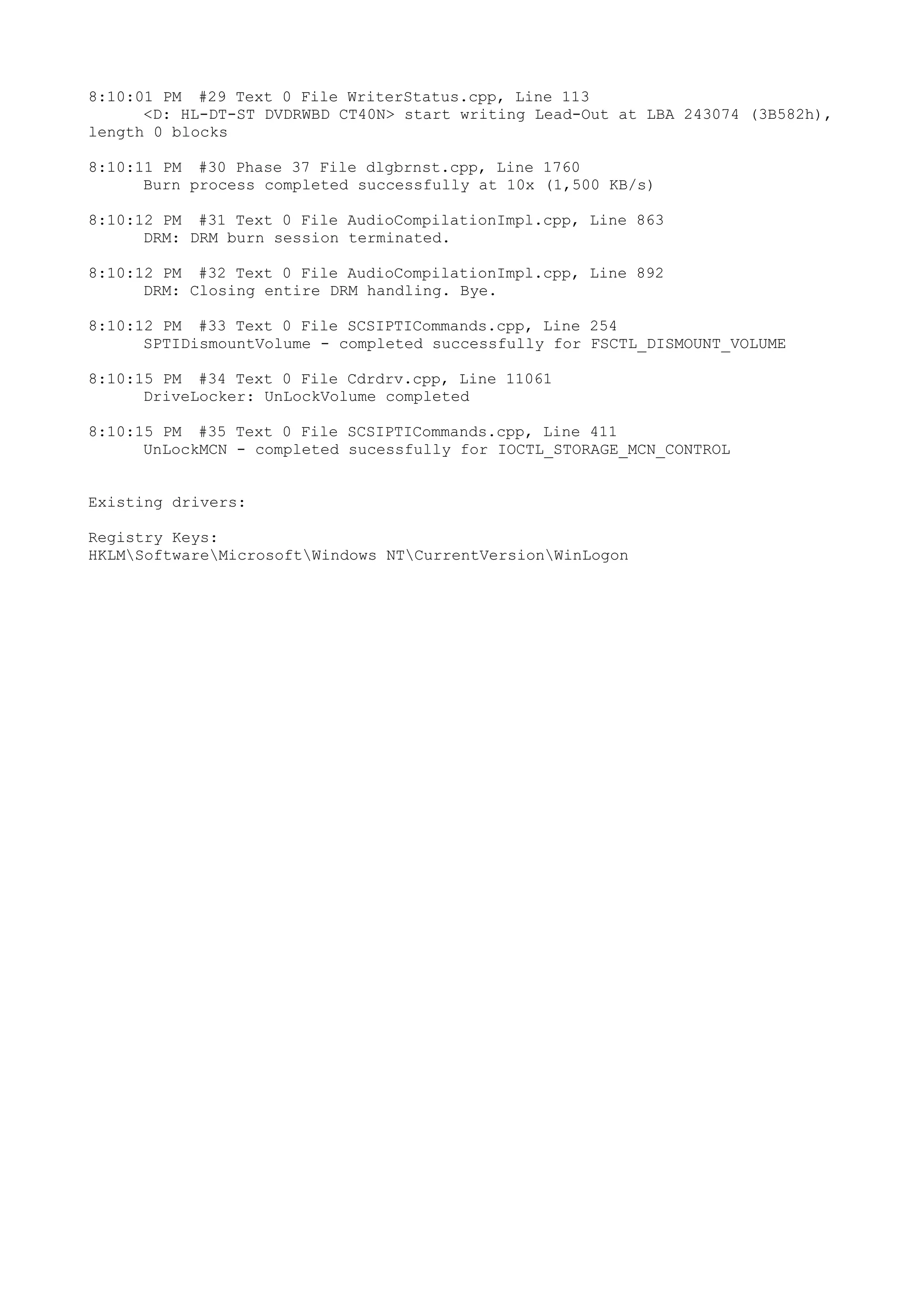
![original disc pos #0 + 38306 (38306) = #38306/8:30.56
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
38306 blocks [D: HL-DT-ST DVDRWBD CT40N]
2: TRM_AUDIO_NOPRE (GOD favor me.wav)
2 indices, index0 (150) not provided
original disc pos #0 + 35173 (35173) = #35173/7:48.73
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
35173 blocks [D: HL-DT-ST DVDRWBD CT40N]
3: TRM_AUDIO_NOPRE (GOD GRACE.wav)
2 indices, index0 (150) not provided
original disc pos #0 + 23602 (23602) = #23602/5:14.52
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
23602 blocks [D: HL-DT-ST DVDRWBD CT40N]
4: TRM_AUDIO_NOPRE (EVERTHING.wav)
2 indices, index0 (150) not provided
original disc pos #0 + 25293 (25293) = #25293/5:37.18
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
25293 blocks [D: HL-DT-ST DVDRWBD CT40N]
5: TRM_AUDIO_NOPRE (determime_EQ.wav)
2 indices, index0 (150) not provided
original disc pos #0 + 15021 (15021) = #15021/3:20.21
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
15021 blocks [D: HL-DT-ST DVDRWBD CT40N]
6: TRM_AUDIO_NOPRE (i understand.wav)
2 indices, index0 (150) not provided
original disc pos #0 + 18096 (18096) = #18096/4:1.21
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
18096 blocks [D: HL-DT-ST DVDRWBD CT40N]
7: TRM_AUDIO_NOPRE (IN THE MORNING.wav)
2 indices, index0 (150) not provided
original disc pos #0 + 25558 (25558) = #25558/5:40.58
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
25558 blocks [D: HL-DT-ST DVDRWBD CT40N]
8: TRM_AUDIO_NOPRE (it not over.wav)
2 indices, index0 (150) not provided
original disc pos #0 + 17122 (17122) = #17122/3:48.22
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
17122 blocks [D: HL-DT-ST DVDRWBD CT40N]
9: TRM_AUDIO_NOPRE (forever.wav)
2 indices, index0 (150) not provided
original disc pos #0 + 23542 (23542) = #23542/5:13.67
relocatable, disc pos for caching/writing not required/not required
-> TRM_AUDIO_NOPRE, 2352, config 0, wanted index0 0 blocks, length
23542 blocks [D: HL-DT-ST DVDRWBD CT40N]
--------------------------------------------------------------
8:03:58 PM #11 Text 0 File ThreadedTransferInterface.cpp, Line 995
Prepare [D: HL-DT-ST DVDRWBD CT40N] for write in CUE-sheet-DAO
DAO infos:
==========
MCN: ""
TOCType: 0x00; Session Closed, disc fixated
Tracks 1 to 10: Idx 0 Idx 1
Next Trk
1: TRM_AUDIO_NOPRE, 2352/0x00, FilePos 0 352800
47418672, ISRC ""](https://image.slidesharecdn.com/iunderstand-130121214144-phpapp01/75/I-understand-3-2048.jpg)