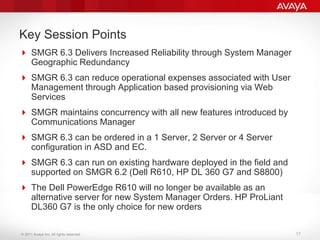
System Manager provides centralized management of Avaya communications solutions. It simplifies operations through a single management interface and reduces costs by automating tasks. System Manager 6.3 introduces geographic redundancy which increases reliability by allowing a secondary System Manager to take over if the primary fails. It also supports application-based provisioning through web services to streamline user management.




![© 2011 Avaya Inc. All rights reserved.
System Manager ASD Offer Help Description
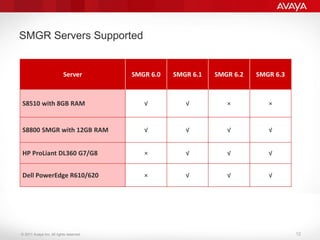
System Manger (SMGR) Order Options :
1. Software & 1 Server - Standalone SMGR running one Avaya supplied server
2. Software & 2 Servers - Standalone SMGR in a High Availability (HA) pair
configuration running on two Avaya supplied servers or a SMGR Geographic
Redundancy (GR) pair configuration running on two Avaya supplied servers.
Either configuration can be supported with the two servers, but not both.
3. Software & 4 Servers – Two SMGR pairs in a High Availability (HA) and a
Geographic Redundancy (GR) configuration running on four Avaya supplied
servers. For example: Two data centers, each with a SMGR HA Pair in a
Geographic Redundant configuration across the two data centers.
4. Software Only – Option if customer already has an Avaya supplied server,
that they will repurpose for SMGR utilization. The Avaya supplied server
hardware used by the customer for the ‘software only’ option, must comply
with the hardware specifications for the release of SMGR software being
ordered. Only Avaya supplied servers are supported by SMGR.
5. None - Only one SMGR domain is required and supported per Enterprise.
Selecting ‘None’ means that the System Manager application in a Standalone,
HA or GR configuration already exists for this customer and no materials
(either software or hardware) will be provided. [DEFAULT SETTING]
Note: When ordering multiple servers for HA or GR, all servers must be identical
15](https://image.slidesharecdn.com/avayasystemmanager-140412190057-phpapp02/85/Avaya-Aura-System-Manager-14-320.jpg)