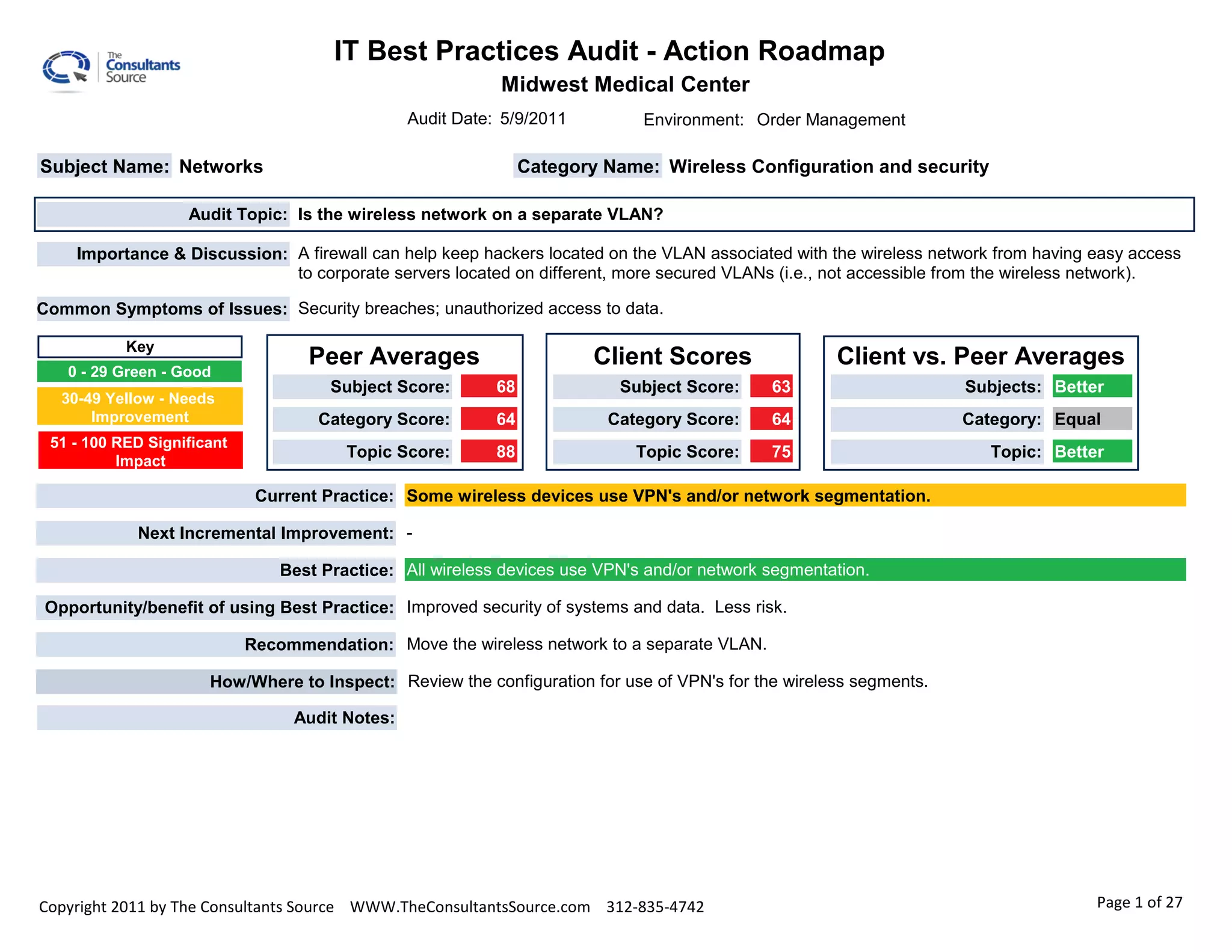
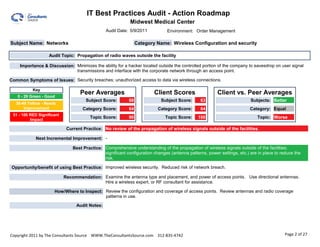
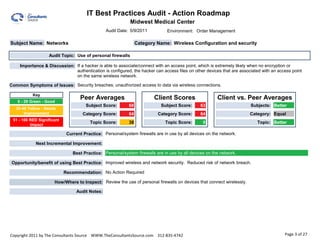
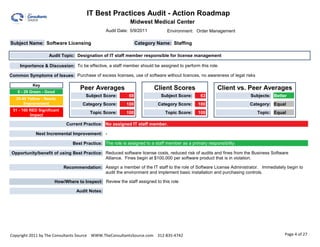
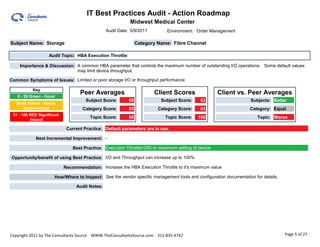
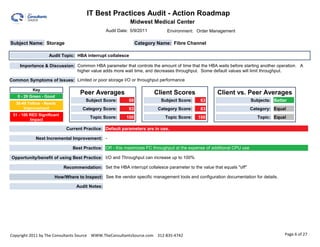
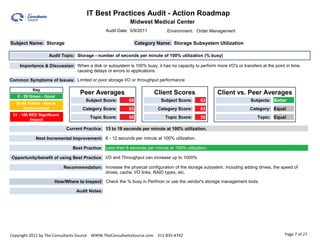
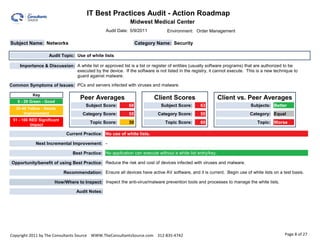
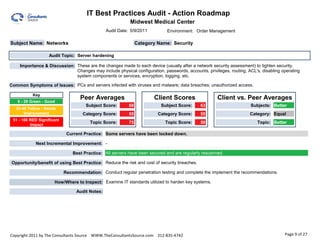
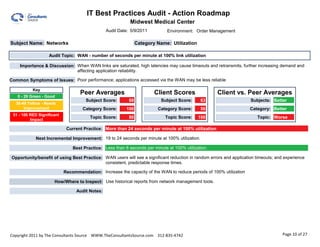
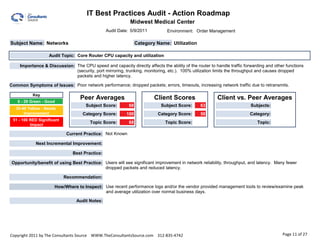
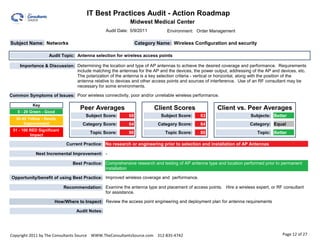
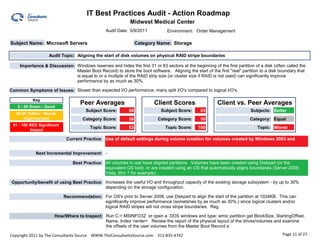
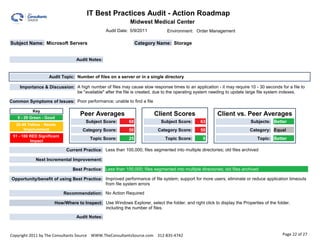
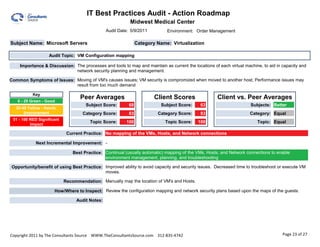
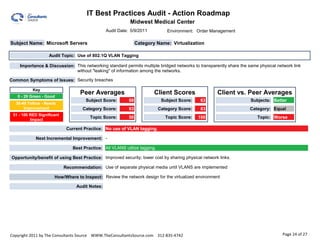
The document outlines an IT best practices audit for Midwest Medical Center conducted on May 9, 2011, focusing on various aspects of wireless network security and configuration, including VLAN separation, signal propagation, personal firewalls, software license management, and storage subsystem performance. Recommendations include moving wireless networks to separate VLANs, utilizing personal firewalls, assigning a dedicated staff member to manage software licenses, and optimizing storage configurations to improve performance and security. Overall, the audit emphasizes the need for several incremental improvements to enhance security and operational efficiency.