The document discusses spectrum leasing through cooperative opportunistic routing in distributed ad hoc networks, exploring both optimal and heuristic routing policies. It formulates the problem as a stochastic routing issue to achieve optimal policies and presents two low-complexity heuristics that provide near-optimal performance. Numerical results suggest that both optimal and heuristic methods enhance primary energy efficiency and throughput.



![Spectrum leasing via
cooperation [Simeone08]
¨ Remuneration is offered by the secondary users in the
form of cooperation (relaying)
¨ Secondary users accept to cooperate if leased
enough spectral resources to satisfy QoS requirements
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-4-320.jpg)
![Opportunistic routing
Po Pd
¨ Leverages broadcast nature of wireless channel
¨ Next hop selected in an adaptive manner, based on:
q current channel conditions (relay availability) [Larsson01]
q distance to destination [Zorzi03, Morris04]
q delay and congestion criteria [Javidi09]
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-5-320.jpg)


![System model
T = RP [ RS [ {Po , Pd }
Po Pd
¨ Primary Network: RP [ {Po , Pd }
¨ Secondary Network: RS
¨ Nodes are static and arbitrarily placed
¨ Nodes work in half-duplex mode, spatial reuse is not allowed
¨ ⇠P = EP /N0 : average received SNR between Po and Pd
¨ RP , RS : primary, secondary transmission rates [bits/s/Hz]
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-8-320.jpg)






![Optimal Routing Policies
¨ Starting state s and final state f
¨ Goal: minimize the total expected discounted cost
"+1 #
def
X
k
J(s) = E⇡ c(x, a, y) x0 = s , 0 < <1
k=0
¨ The problem is an instance of stochastic routing
[Lott06]
¨ The optimal policy is an index policy
¤ global ranking of the nodes
¨ A centralized algorithm and its distributed
implementation is provided in [Lott06]
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-15-320.jpg)
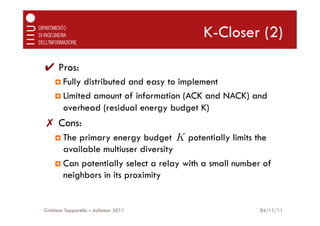
![Heuristic Routing Policies
¨ The algorithm in [Lott06] requires full knowledge of the
network topology and has time complexity O(|T |2 )
¨ We propose two low-complexity heuristic policies that
only require local topology information
¨ Suitable for a distributed implementation
¨ Relay selection is made on-line by the current
transmitter at each hop, based on local interactions
¨ Both policies uses a primary energy budget K to control
the trade-off between the primary energy consumption
and the end-to-end throughput
¤ maximum number of primary relays that can be used
¤ stored within the packet
¤ decremented when a new primary relay is selected
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-16-320.jpg)


![K-OSLA (2)
¨ Expected geographical advancement metrics:
|B(a)| |B(a)|
X Y
¤ ga = ga,ni [1 pout (a, ni )] pout (a, nj )
i=1 j=i+1
|BS (a)| |BS (a)|
X Y
S
¤ ga = ga,mi [1 pout (a, mi )] pout (a, mj )
i=1 j=i+1
¨ At each hop, the possible relays are ranked according to
the metrics:
¤ Ga,n = ga,n + gn when K > 1
¤ Ga,n = ga,n + gn when K = 1 and a 2 RS
¤ GS = ga,n + gn otherwise
a,n
S
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-20-320.jpg)

![Numerical Results:
Optimal vs Heuristics
Optimal
0.6 K-OSLA
α=1 K-Closer
Optimal, No SL
0.5 K-OSLA, No SL
Throughput [bits/s/Hz]
K-Closer, No SL
K=8
0.4
0.3
α=0
0.2
K=0
0.1
0 2 4 6 8 10 12
Primary Energy [dB]
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-22-320.jpg)
![Numerical Results: Impact of
Secondary network density
NS = 12 K-OSLA, K=8
0.6 K-Closer, K=8
Optimal, =1
0.5
Throughput [bits/s/Hz]
0.4
0.3 NS = 0
0.2
0.1
4 5 6 7 8 9 10 11 12
Primary Energy [dB]
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-23-320.jpg)
![Numerical Results: Impact of
budget K on K-Osla
NS = 12 Optimal, = 0
0.6 K=8 Optimal, = 1
K-OSLA
0.5
Throughput [bits/s/Hz]
0.4
NS = 2
K=0
0.3
0.2
0.1
0 2 4 6 8 10 12
Primary Energy [dB]
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-24-320.jpg)

![Refences
¨ [Larsson01]: P. Larsson, “Selection Diversity Forwarding in a Multihop Packet Radio Network with
Fading Channel and Capture,” ACM SIGMOBILE Mob. Comput. Commun. Rev., vol. 5, no. 4, pp. 47–
54, Oct. 2001.
¨ [Zorzi03]: M. Zorzi and R. Rao, “Geographic random forwarding (GeRaF) for ad hoc and sensor
networks: multihop performance,” IEEE Trans. Mobile Comput., vol. 2, no. 4, pp. 337–348, Oct. 2003.
¨ [Morris04]: S. Biswas and R. Morris, “Opportunistic Routing in Multi-Hop Wireless Networks,” ACM
SIGCOMM Comput. Commun. Rev., vol. 34, no. 1, Jan. 2004.
¨ [Javidi09]: M. Naghshvar, H. Zhuang, and T. Javidi, “A General Class of Throughput Optimal Routing
Policies in Multi-hop Wireless Networks,” preprint, http://arxiv.org/pdf/0908.1273.
¨ [Chiarotto10]: D. Chiarotto, O. Simeone, M. Zorzi, ”Throughput and Energy Efficiency of Opportunistic
Routing with type-I HARQ in Linear Multihop Networks”, in Proc. of IEEE GlobeCom, Miami, FL, 6–10
Dec. 2010.
¨ [Simeone08]: O. Simeone, I. Stanojev, S. Savazzi, Y. Bar-Ness, U. Spagnolini, and R. Pickholtz,
“Spectrum Leasing to Cooperating Secondary Ad Hoc Networks,” IEEE J. Select. Areas Commun., vol.
26, no. 1, Jan. 2008.
¨ [Lott06]: C. Lott and D. Teneketzis, “Stochastic routing in ad hoc networks”, IEEE Transactions on
Automatic Control, vol. 51, no.1, Jan. 2006.
¨ [Chiarotto11]: D. Chiarotto, O. Simeone and M. Zorzi, “Spectrum leasing via cooperative
opportunistic routing”, IEEE Transactions on Wireless Communications, Vol. 10, no. 9, Sep. 2011
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-26-320.jpg)

![Optimal Routing Policies:
transition probabilities
8
>0
> (Pd 2 x or x = f ) and y 6= f
>
<1 (Pd 2 x or x = f ) and y = f
pxy (a) =
>0
> Pd 2 x, x 6= f and y = f
/
>
:
Pxy (a) Pd 2 x, x 6= f and y 6= f
/
Y Y
Pxy (a) = [1 pout (a, n)] pout (a, m)
n2T s.t. m2T s.t.
n2y,n2x
/ m2y
/
Cristiano Tapparello – Asilomar 2011 04/11/11](https://image.slidesharecdn.com/asilomar2011slides-121023045822-phpapp02/85/Asilomar-2011-28-320.jpg)
