Arrays are data structures that store a collection of data values of the same type in consecutive memory locations that can be individually referenced by their numeric index. Different representations of arrays are possible including using a single block of memory or a collection of elements. Common operations on arrays include retrieving or storing elements by their index and traversing the entire array sequentially.
![Arrays
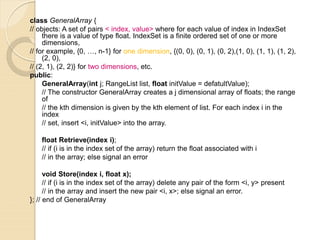
Array: a set of index and value
data structure
For each index, there is a value associated with
that index.
representation (possible)
implemented by using consecutive memory.
Example: int list[5]: list[0], …, list[4] each contains
an integer
0 1 2 3 4
List](https://image.slidesharecdn.com/02-200122092905/85/Array-2-320.jpg)
![Arrays in C
int list[5], *plist[5];
list[5]: five integers
list[0], list[1], list[2], list[3], list[4]
*plist[5]: five pointers to integers
plist[0], plist[1], plist[2], plist[3], plist[4]
0 1 2 3 4
Plist
0 1 2 3 4
List](https://image.slidesharecdn.com/02-200122092905/85/Array-4-320.jpg)
![Arrays in C (cont’d)
implementation of 1-D array
list[0] base address = α
list[1] α + sizeof(int)
list[2] α + 2*sizeof(int)
list[3] α + 3*sizeof(int)
list[4] α + 4*size(int)
Compare int *list1 and int list2[5] in C.
Same: list1 and list2 are pointers.
Difference: list2 reserves five locations.
Notations:
list2 - a pointer to list2[0]
(list2 + i) - a pointer to list2[i] (&list2[i])
*(list2 + i) - list2[i]](https://image.slidesharecdn.com/02-200122092905/85/Array-5-320.jpg)
![Example: 1-dimension array addressing
int one[] = {0, 1, 2, 3, 4};
Goal: print out address and value
void print1(int *ptr, int rows)
{
/* print out a one-dimensional array using a pointer */
int i;
printf(“Address Contentsn”);
for (i=0; i < rows; i++)
printf(“%8u%5dn”, ptr+i, *(ptr+i));
printf(“n”);
}](https://image.slidesharecdn.com/02-200122092905/85/Array-6-320.jpg)
![Address Contents
1228 0
1230 1
1232 2
1234 3
1236 4
call print1(&one[0], 5)](https://image.slidesharecdn.com/02-200122092905/85/Array-7-320.jpg)
![Structures (records)
struct {
char name[10];
int age;
float salary;
} person;
strcpy(person.name, “james”);
person.age=10;
person.salary=35000;](https://image.slidesharecdn.com/02-200122092905/85/Array-8-320.jpg)
![Create structure data type
typedef struct human_being {
char name[10];
int age;
float salary;
};
or
typedef struct {
char name[10];
int age;
float salary
} human_being;
human_being person1, person2;](https://image.slidesharecdn.com/02-200122092905/85/Array-9-320.jpg)
![Unions
Similar to struct, but only one field is active.
Example: Add fields for male and female.
typedef struct sex_type {
enum tag_field {female, male} sex;
union {
int children;
int beard;
} u;
};
typedef struct human_being {
char name[10];
int age;
float salary;
date dob;
sex_type sex_info;
}
human_being person1, person2;
person1.sex_info.sex=male;
person1.sex_info.u.beard=FALSE;](https://image.slidesharecdn.com/02-200122092905/85/Array-10-320.jpg)



![Polynomial Representation 1
0 1 2 3 4
CoeffArray 1 0 3 10 1
x4+10x3+3x2+1
private:
int degree; // degree ≤ MaxDegree
float coef [MaxDegree + 1];](https://image.slidesharecdn.com/02-200122092905/85/Array-15-320.jpg)


![storage requirements: start, finish, 2*(finish-start+1)
nonsparse: twice as much as (1)
when all the items are nonzero
class term {
friend Polynomial;
private:
float coef; // coefficient
int exp; // exponent
};
class Polynomial; // forward delcaration
{ private:
static term termArray[MaxTerms];
static int free;
int Start, Finish;
}
term Polynomial:: termArray[MaxTerms];
int Polynomial::free = 0; // location of next free location in temArray](https://image.slidesharecdn.com/02-200122092905/85/Array-18-320.jpg)
![Polynomial Polynomial:: Add(Polynomial B)
// return the sum of A(x) ( in *this) and B(x)
{
Polynomial C; int a = Start; int b = B.Start; C.Start = free; float c;
while ((a <= Finish) && (b <= B.Finish))
switch (compare(termArray[a].exp, termArray[b].exp)) {
case ‘=‘:
c = termArray[a].coef +termArray[b].coef;
if ( c ) NewTerm(c, termArray[a].exp);
a++; b++;
break;
case ‘<‘:
NewTerm(termArray[b].coef, termArray[b].exp);
b++;
case ‘>’:
NewTerm(termArray[a].coef, termArray[a].exp);
a++;
} // end of switch and while
// add in remaining terms of A(x)
for (; a<= Finish; a++)
NewTerm(termArray[a].coef, termArray[a].exp);
// add in remaining terms of B(x)
for (; b<= B.Finish; b++)
NewTerm(termArray[b].coef, termArray[b].exp);
C.Finish = free – 1;
return C;
} // end of Add
Analysis: O(n+m) where n (m) is
the number of nonzeros in A(B).](https://image.slidesharecdn.com/02-200122092905/85/Array-19-320.jpg)
![Adding a new Term
void Polynomial::NewTerm(float c, int e)
// Add a new term to C(x)
{
if (free >= MaxTerms) {
cerr << “Too many terms in polynomials”<< endl;
exit();
}
termArray[free].coef = c;
termArray[free].exp = e;
free++;
} // end of NewTerm](https://image.slidesharecdn.com/02-200122092905/85/Array-20-320.jpg)



![SparseMatrix Add(SparseMatrix b);
// if the dimensions of a (*this) and b are the same, then the matrix
produced by adding corresponding items, namely those with identical
row and column values is returned
// else error.
SparseMatrix Multiply(SparseMatrix b);
// if number of columns in a (*this) equals number of rows in b then
the matrix d produced by multiplying a by b according to the formula
d[i][j] = Σ(a[i][k] . b[k][j]), where d[i][j] is the (i, j)th element, is returned.
k ranges from 0 to the number of columns in a – 1
// else error](https://image.slidesharecdn.com/02-200122092905/85/Array-24-320.jpg)

![row col value row col value
a[0] 0 0 15 b[0] 0 0 15
[1] 0 3 22 [1] 0 4 91
[2] 0 5 -15 [2] 1 1 11
[3] 1 1 11 [3] 2 1 3
[4] 1 2 3 [4] 2 5 28
[5] 2 3 -6 [5] 3 0 22
[6] 4 0 91 [6] 3 2 -6
[7] 5 2 28 [7] 5 0 -15
(a) (b)
(1) Represented by a two-dimensional array.
Sparse matrix wastes space.
(2) Each element is characterized by <row, col, value>.
row, column in ascending order
transpose](https://image.slidesharecdn.com/02-200122092905/85/Array-26-320.jpg)
![class SparseMatrix; // forward declaration
class MatrixTerm {
friend class SparseMatrix
private:
int row, col, value;
};
In class SparseMatrix:
private:
int Rows, Cols, Terms;
MatrixTerm smArray[MaxTerms];](https://image.slidesharecdn.com/02-200122092905/85/Array-27-320.jpg)

![SparseMatrix SparseMatrix::Transpose()
// return the transpose of a (*this)
{
SparseMatrix b;
b.Rows = Cols; // rows in b = columns in a
b.Cols = Rows; // columns in b = rows in a
b.Terms = Terms; // terms in b = terms in a
if (Terms > 0) // nonzero matrix
{
int CurrentB = 0;
for (int c = 0; c < Cols; c++) // transpose by columns
for (int i = 0; i < Terms; i++)
// find elements in column c
if (smArray[i].col == c) {
b.smArray[CurrentB].row = c;
b.smArray[CurrentB].col = smArray[i].row;
b.smArray[CurrentB].value = smArray[i].value;
CurrentB++;
}
} // end of if (Terms > 0)
return b;
} // end of transpose
Time Complexity O(terms*cols)
column
term element
matrix
0
c = column
b
column assignment](https://image.slidesharecdn.com/02-200122092905/85/Array-29-320.jpg)

![index [0] [1] [2] [3] [4] [5]
RowSize = 3 2 1 0 1 1
RowStart = 0 3 5 6 6 7
row col value row col value
a[0] 0 0 15 b[0] 0 0 15
[1] 0 3 22 [1] 0 4 91
[2] 0 5 -15 [2] 1 1 11
[3] 1 1 11 [3] 2 1 3
[4] 1 2 3 [4] 2 5 28
[5] 2 3 -6 [5] 3 0 22
[6] 4 0 91 [6] 3 2 -6
[7] 5 2 28 [7] 5 0 -15
ba
row
start+size](https://image.slidesharecdn.com/02-200122092905/85/Array-31-320.jpg)
![Fast Matrix Transposing
SparseMatrix SparseMatrix::Transpose()
// The transpose of a(*this) is placed in b and is found in Q(terms + columns) time.
{
int *Rows = new int[Cols];
int *RowStart = new int[Cols];
SparseMatrix b;
b.Rows = Cols; b.Cols = Rows; b.Terms = Terms;
int i;
if (Terms > 0) // nonzero matrix
{
// compute RowSize[i] = number of terms in row i of b
for ( i = 0; i < Cols; i++) RowSize[i] = 0; // Initialize
for ( i = 0; i < Terms; I++) RowSize[smArray[i].col]++;
// RowStart[i] = starting position of row i in b
RowStart[0] = 0;
for (i = 1; i < Cols; i++) RowStart[i] = RowStart[i-1] + RowSize[i-1];
O(columns)
O(terms)
O(columns-1)
row size +1
start size](https://image.slidesharecdn.com/02-200122092905/85/Array-32-320.jpg)
![Fast Matrix Transposing (cont’d)
for (i =0; i < Terms; i++) // move from a to b
{
int j = RowStart[smArray[i].col];
b.smArray[j].row = smArray[i].col;
b.smArray[j].col = smArray[i].row;
b.smArray[j].value = smArray[i].value;
RowStart[smArray[i].col]++;
} // end of for
} // end of if
delete [] RowSize;
delete [] RowStart;
return b;
} // end of FastTranspose
O(terms)
O(row * column)
Text
row
row start
row start](https://image.slidesharecdn.com/02-200122092905/85/Array-33-320.jpg)
![Matrix Multiplication
Definition: Given A and B, where A is mxn and B
is nxp, the product matrix Result has dimension
mxp. Its [i][j] element is
for 0 ≤ i < m and 0 ≤ j < p.
kj
n
k
ikij baresult ∑
−
=
=
1
0](https://image.slidesharecdn.com/02-200122092905/85/Array-34-320.jpg)
![Representation of Arrays
Multidimensional arrays are usually
implemented by one dimensional array via
either row major order or column major
order.
Example: One dimensional array
A[0] A[1] A[2] A[3] A[4] A[5] A[6] A[7] A[8] A[9] A[10] A[11]
α α+1 α+2 α+3 α+4 α+5 α+6 α+7 α+8 α+9 α+10 α+12](https://image.slidesharecdn.com/02-200122092905/85/Array-35-320.jpg)

![Generalizing Array Representation
The address indexing of Array A[i1][i2],…,[in] is
α+ i1 u2 u3 … un
+ i2 u3 u4 … un
+ i3 u4 u5 … un
:
:
+ in-1 un
+ in
=α+
=
≤≤= ∏∑ +=
=
1
1
1
1
n
n
jk
kj
n
j
jj
a
njua
whereai](https://image.slidesharecdn.com/02-200122092905/85/Array-37-320.jpg)




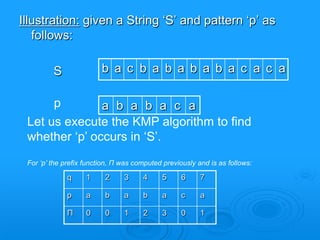
![The prefix (failure) function, Π
Following pseudocode computes the prefix (i.e., failure) fucnction, Π:
Compute-Prefix-Function (p)
1 m length[p] //’p’ pattern to be matched
2 Π[1] 0
3 k 0
4 for q 2 to m
5 do while k > 0 and p[k+1] != p[q]
6 do k Π[k]
7 If p[k+1] = p[q]
8 then k k +1
9 Π[q] k
10 return Π](https://image.slidesharecdn.com/02-200122092905/85/Array-46-320.jpg)
![Example: compute Π for the pattern ‘p’ below:
p a b a b a c a
Initially: m = length[p] = 7
Π[1] = 0
k = 0
Step 1: q = 2, k=0
Π[2] = 0
Step 2: q = 3, k = 0,
Π[3] = 1
Step 3: q = 4, k = 1
Π[4] = 2
q 1 2 3 4 5 6 7
p a b a b a c a
Π 0 0
q 1 2 3 4 5 6 7
p a b a b a c a
Π 0 0 1
q 1 2 3 4 5 6 7
p a b a b a c A
Π 0 0 1 2](https://image.slidesharecdn.com/02-200122092905/85/Array-47-320.jpg)
![Step 4: q = 5, k =2
Π[5] = 3
Step 5: q = 6, k = 3
Π[6] = 1
Step 6: q = 7, k = 1
Π[7] = 1
After iterating 6 times, the prefix
function computation is
complete:
q 1 2 3 4 5 6 7
p a b a b a c a
Π 0 0 1 2 3
q 1 2 3 4 5 6 7
p a b a b a c a
Π 0 0 1 2 3 0
q 1 2 3 4 5 6 7
p a b a b a c a
Π 0 0 1 2 3 0 1
q 1 2 3 4 5 6 7
p a b a b a c a
Π 0 0 1 2 3 0 1
a =](https://image.slidesharecdn.com/02-200122092905/85/Array-48-320.jpg)

![The KMP Matcher
The KMP Matcher, with pattern ‘p’, string ‘S’ and prefix function ‘Π’ as input, finds a match of p in S.
Following pseudocode computes the matching component of KMP algorithm:
KMP-Matcher(S,p)
1 n length[S]
2 m length[p]
3 Π Compute-Prefix-Function(p)
4 q 0 //number of characters matched
5 for i 1 to n //scan S from left to right
6 do while q > 0 and p[q+1] != S[i]
7 do q Π[q] //next character does not match
8 if p[q+1] = S[i]
9 then q q + 1 //next character matches
10 if q = m //is all of p matched?
11 then print “Pattern occurs with shift” i – m
12 q Π[ q] // look for the next match
Note: KMP finds every occurrence of a ‘p’ in ‘S’. That is why KMP does not terminate in step 12,
rather it searches remainder of ‘S’ for any more occurrences of ‘p’.](https://image.slidesharecdn.com/02-200122092905/85/Array-50-320.jpg)
![b a c b a b a b a b a c a a b
b a c b a b a b a b a c a a b
a b a b a c a
Initially: n = size of S = 15;
m = size of p = 7
Step 1: i = 1, q = 0
comparing p[1] with S[1]
S
p
P[1] does not match with S[1]. ‘p’ will be shifted one position to the right.
S
p a b a b a c a
Step 2: i = 2, q = 0
comparing p[1] with S[2]
P[1] matches S[2]. Since there is a match, p is not shifted.](https://image.slidesharecdn.com/02-200122092905/85/Array-52-320.jpg)
![Step 3: i = 3, q = 1
b a c b a b a b a b a c a a b
Comparing p[2] with S[3]
S
a b a b a c a
b a c b a b a b a b a c a a b
b a c b a b a b a b a c a a b
a b a b a c a
a b a b a c ap
S
p
S
p
p[2] does not match with S[3]
Backtracking on p, comparing p[1] and S[3] (q= Π[1]+1=0+1=1)
Step 4: i = 4, q = 0
comparing p[1] with S[4] p[1] does not match with S[4]
Step 5: i = 5, q = 0
comparing p[1] with S[5] p[1] matches with S[5]](https://image.slidesharecdn.com/02-200122092905/85/Array-53-320.jpg)
![b a c b a b a b a b a c a a b
b a c b a b a b a b a c a a b
b a c b a b a b a b a c a a b
a b a b a c a
a b a b a c a
a b a b a c a
Step 6: i = 6, q = 1
S
p
Comparing p[2] with S[6] p[2] matches with S[6]
S
p
Step 7: i = 7, q = 2
Comparing p[3] with S[7] p[3] matches with S[7]
Step 8: i = 8, q = 3
Comparing p[4] with S[8] p[4] matches with S[8]
S
p](https://image.slidesharecdn.com/02-200122092905/85/Array-54-320.jpg)
![Step 9: i = 9, q = 4
Comparing p[5] with S[9]
Comparing p[6] with S[10]
Comparing p[5] with S[11]
Step 10: i = 10, q = 5
Step 11: i = 11, q = 4
S
S
S
p
p
p
b a c b a b a b a b a c a a b
b a c b a b a b a b a c a a b
b a c b a b a b a b a c a a b
a b a b a c a
a b a b a c a
a b a b a c a
p[6] doesn’t match with S[10]
Backtracking on p, comparing p[4] with S[10] because after mismatch q = (Π[5]+1) = 3+1=4
p[5] matches with S[9]
p[5] matches with S[11]
看a fail function = 3
從3+1 開始比](https://image.slidesharecdn.com/02-200122092905/85/Array-55-320.jpg)
![b a c b a b a b a b a c a a b
b a c b a b a b a b a c a a b
a b a b a c a
a b a b a c a
Step 12: i = 12, q = 5
Comparing p[6] with S[12]
Comparing p[7] with S[13]
S
S
p
p
Step 13: i = 13, q = 6
p[6] matches with S[12]
p[7] matches with S[13]
Pattern ‘p’ has been found to completely occur in string ‘S’.](https://image.slidesharecdn.com/02-200122092905/85/Array-56-320.jpg)
