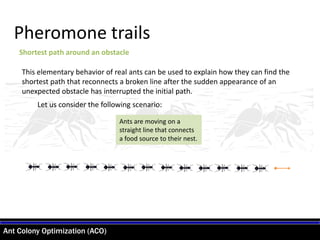
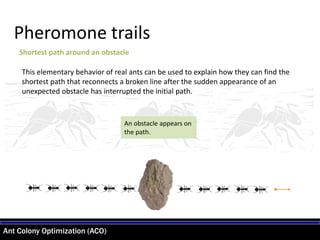
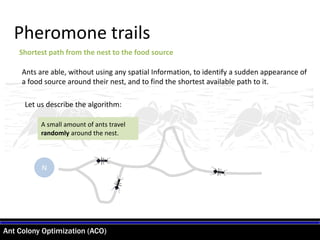
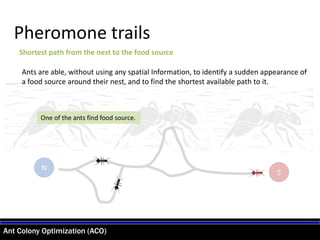
- Ant colony optimization (ACO) is an algorithm inspired by the behavior of real ant colonies. It is used to find solutions to discrete optimization problems.
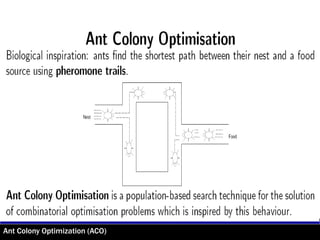
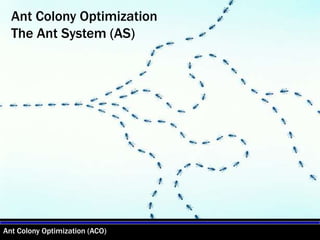
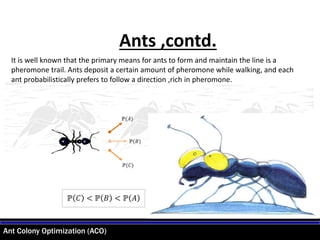
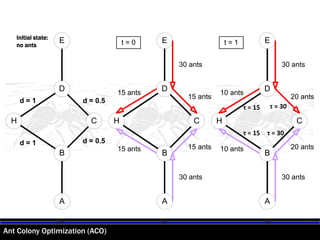
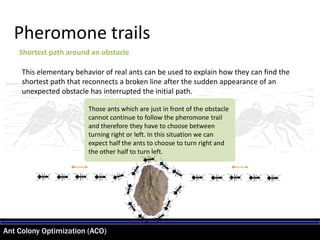
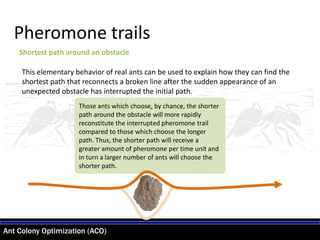
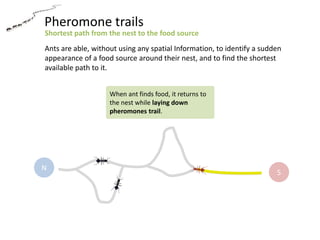
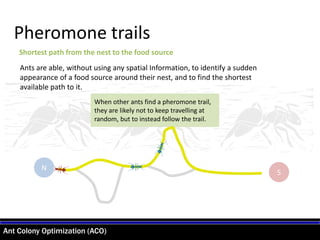
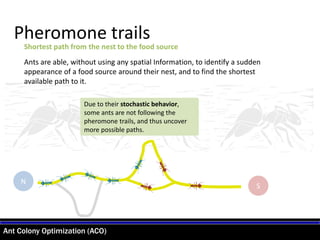
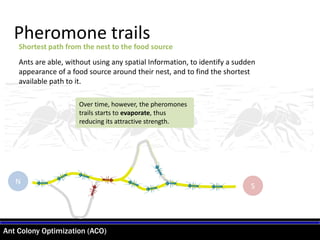
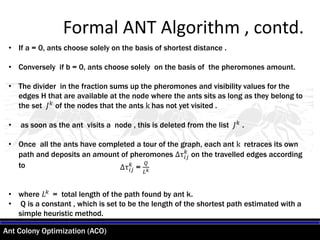
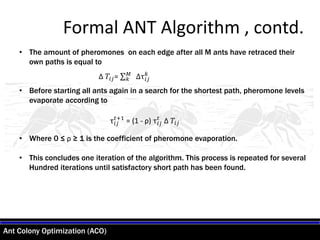
- The algorithm operates by simulating ants walking on the problem graph, depositing and following virtual pheromone trails, with the goal of eventually finding the shortest route. Ants have a higher probability of following paths marked by strong pheromone concentrations.
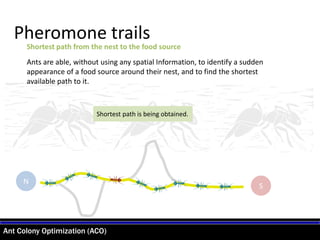
- Over time, the pheromone trails reinforce, guiding more ants toward the best solutions. Pheromone also gradually evaporates, preventing stagnation on locally optimal solutions. After many iterations, the shortest path emerges as the strongest trail.